The number of cyber security incidents reported worldwide is increasing year-on-year. No surprise. This increase in reported incidents is driven by a growing sophistication of attacks with the adoption of new tools like generative AI, which allow malicious actors to roll out novel and targeted cyber-attacks at scale.
In this landscape, it’s important for CISOs and security teams to consider incident response and understand their readiness to handle cyber-attacks – from both a personnel and a technology perspective.
One major method for defenders to test their incident response readiness is through drills which help identify gaps in response plans and ensure that security teams are prepared to respond to real-world incidents.
Commonly, teams rely on tabletop exercises, in which a hypothetical incident response scenario is conducted in a conference room setting. The exercise typically involves a group of people who are responsible for responding to cyber security incidents, such as IT professionals, security analysts, management, and even employees from legal and corporate affairs teams.
The goal of a tabletop exercise is to test the team's ability to respond to a cyber security incident in a “realistic” scenario. But this takes considerable time to plan and execute or can be expensive if outsourced, which can be a challenge for organizations short on resources. Tabletop exercises are based on hypothetical scenarios that are high level, not time-bound like real incidents, and not necessarily applicable to an organization’s unique environment. As a result, these drills lack real-world application and do not help employees train with a sense of urgency and stress that comes with a real high stakes scenario.
Running realistic training simulations until incident response is second nature
Practical incident preparation requires a deep understanding of an organization. Only with a nuanced understanding of an organization can you put the simulation in the most realistic setting possible. For the average organization, with limited security resources, this level of granularity is unobtainable; something purely theoretical.
But thanks to recent advances in AI, this is becoming a reality. Self-Learning AI is a unique form of artificial intelligence that learns from real devices, real communication paths, and real user behaviors – custom to your environment. And this understanding of ‘self’ allows it to run a simulation that effectively maps onto your environment and the assets within it – in other words, real training, for a real incident.
Incident simulations with Darktrace HEAL
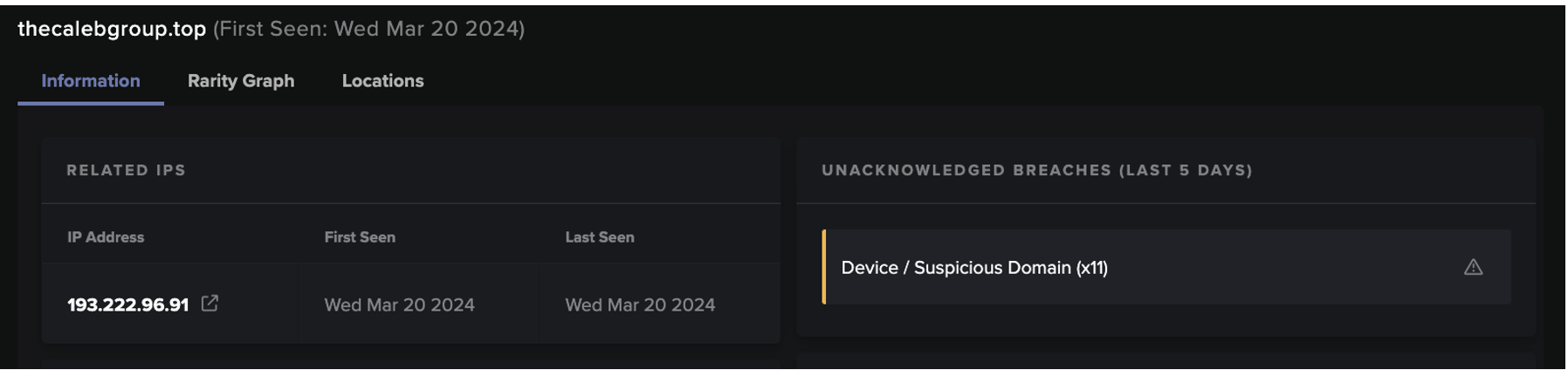
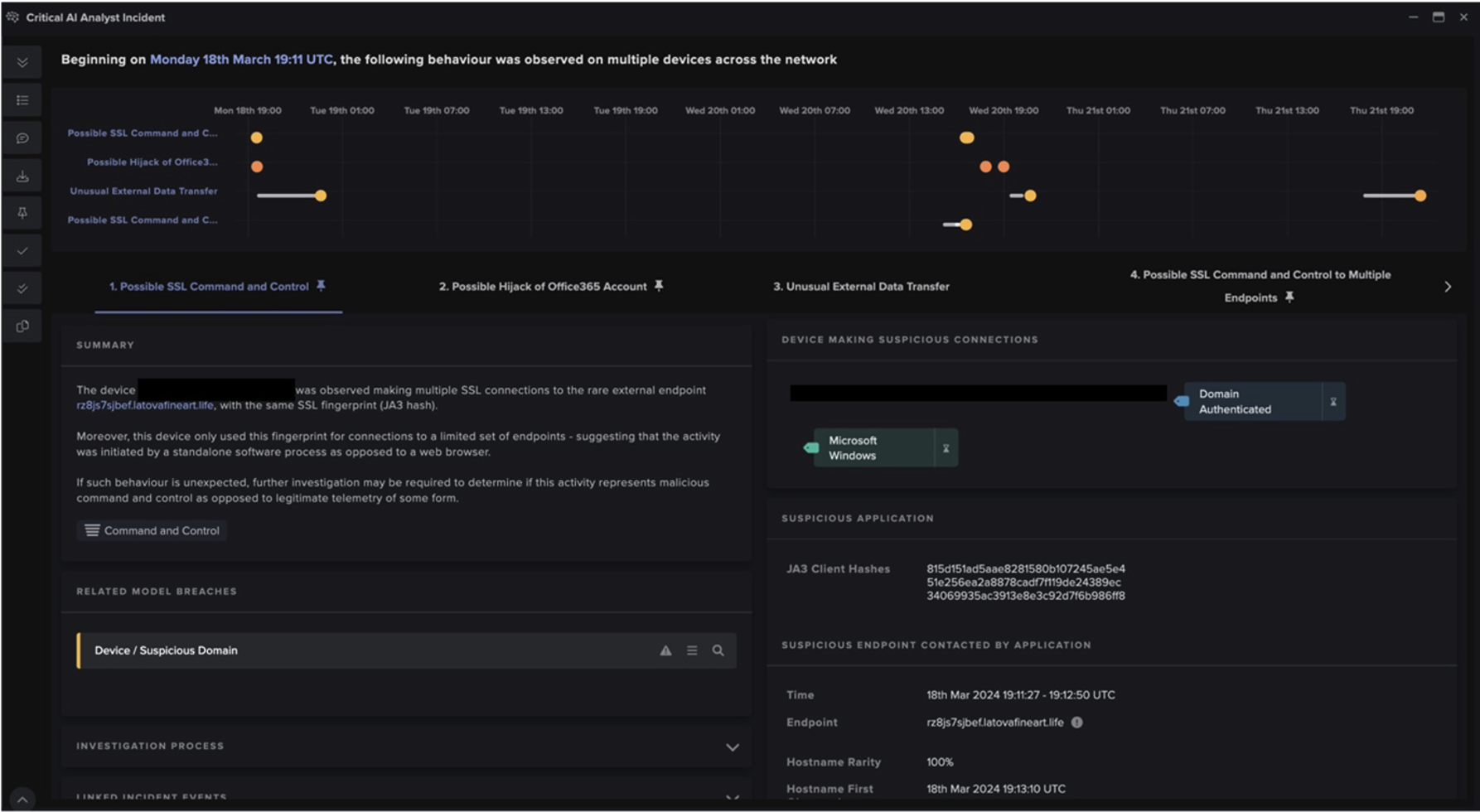
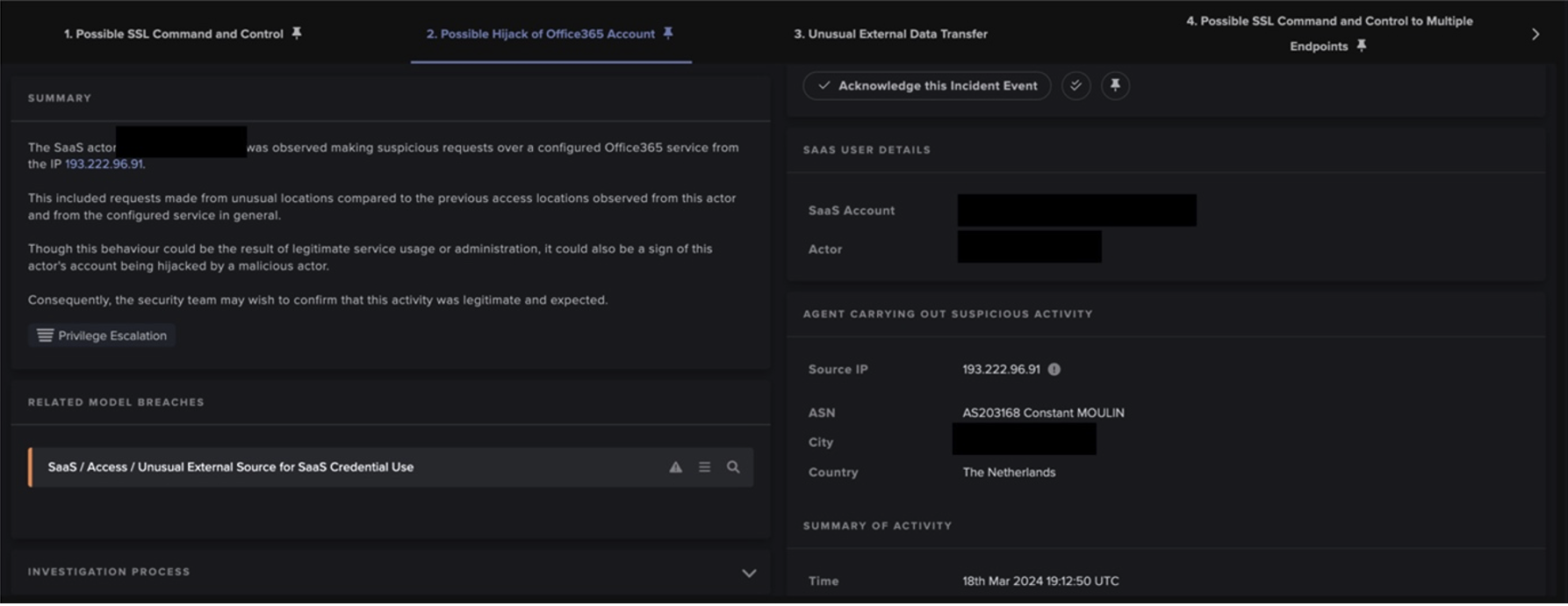
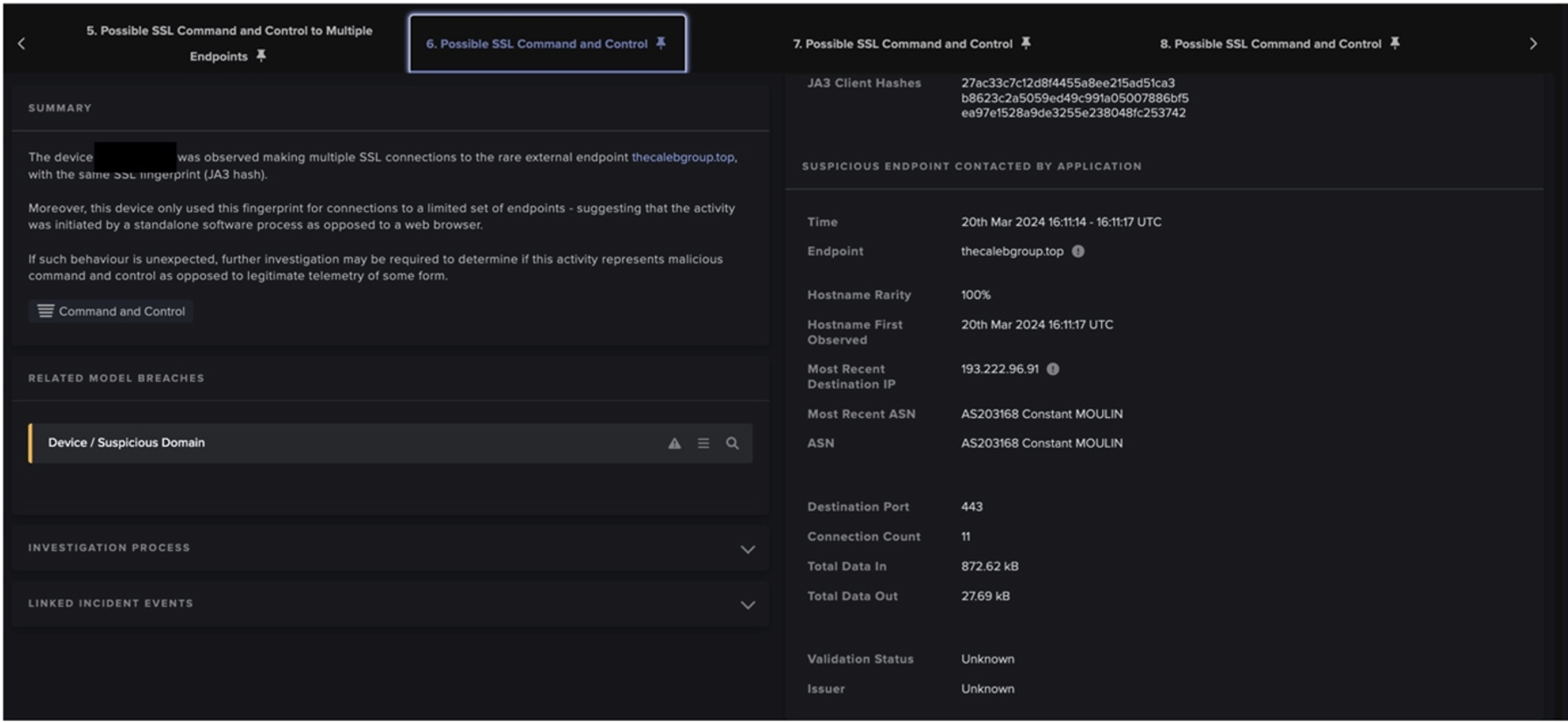
Darktrace HEAL™ enhances an organization’s cyber resilience by allowing defenders to be ready for cyber incidents, engage incidents early, and establish the quickest paths to recovery. As part of this, its simulations allow businesses to test and improve their incident response readiness by addressing process and knowledge gaps while gaining real experience. Since HEAL understands the specific digital landscape and normal activity within each organization, it can use real assets that could plausibly be part of an incident of that type. For example, if two devices communicate with each other or they communicate with the internet, they could be an entry point.
These simulated incidents can be tracked and followed from initial compromise through to payload execution, response, and eventual recovery. As HEAL creates these simulations, they do not require time and resources from the human security team to plan. As a result, they can be run frequently and at varying levels of complexity so teams can gain experience and test a variety of scenarios to build a better understanding of how they would respond to a real-world incident.
Evaluating technology readiness
In addition to testing cyber security incident response with simulations, HEAL can also help organizations assess their technology’s readiness to help answer the question “When we’re up against an attack and time is of the essence, will my technology stack work as we need it to?”
HEAL tests and assesses third-party integrations and the configuration and scope of the third-party products to ensure they’ll work when needed. This provides the security team with visibility into coverage, configuration, and effectiveness of product deployments that affect recovery but aren’t necessarily under security’s purview.
For example, HEAL’s readiness report can surface warning signs such as an unresponsive integration, a solution that has a smaller scope of coverage than expected, or the failure of common functionality in a product.
These reports – which can be pulled at any time – can be used to verify tech is all working as expected as well as deployed following best practice or as a means to show that things aren’t as they should be and need to be resolved ahead of an incident occurring.
Incident preparation made simple
Cyber security incident drills and technology readiness are essential components of any comprehensive cyber security strategy.
Preparation and practice, paired with an accurate understanding of technology readiness, are crucial for efficient incident response. These pieces help CISOs and their teams build confidence, make strong incident response into habit, and identify process gaps. Today, with ever-changing threats and ever-evolving organizations, the only way for cyber security teams to have a true indication of their readiness is through simulated real-world incidents and up-to-date information on the functionality of their incident response tools.
HEAL can help improve these areas, which further contributes to optimizing incident response to conserve resources. By using HEAL, teams can test their incident response plans in realistic scenarios and identify gaps in their security tools or processes to improve their overall cyber resilience.