Darktrace has recently observed several targeted intrusions associated with Evil Corp, an advanced cyber-criminal group recently in the headlines after a surge in WastedLocker ransomware cases. The group is believed to have targeted hundreds of organizations in over 40 countries, demanding ransoms of $500,000 to $1m to unlock computer files it seizes. US authorities are now offering a $5m reward for information leading to the arrest of the group’s leaders — understood to be the largest sum of money ever offered for a cyber-criminal.
Thanks to its self-learning nature, Darktrace's AI detected these intrusions without the use of any threat intelligence or static Indicators of Compromise (IoCs). This blog describes the techniques, tools and procedures used in multiple intrusions by Evil Corp – also known as TA505 or SectorJ04.
Key takeaways
- The threat actor was reusing TTPs as well as infrastructure across multiple intrusions
- Some infrastructure was only observed in individual intrusions
- While most WastedLocker reports focus on the ransomware, Darktrace has observed Evil Corp conducting data exfiltration
- The attacker used various ‘Living off the Land’ techniques for lateral movement
- Data exfiltration and ransomware activity took place on weekends, likely to reduce response capabilities of IT teams
- Although clearly an advanced actor, Evil Corp can be detected and stopped before encryption ensues
Evil Corp ransomware attack

Figure 1: The standard attack lifecycle observed in Evil Corp campaigns
Initial intrusion
While Evil Corp is technically sophisticated enough to choose from an array of initial intrusion methods, fake browser updates were the weapon of choice in the observed campaign. These were delivered from legitimate websites and used social engineering to convince users to download these malicious ‘updates’. Evil Corp has actually built a framework around this capability, referred to as SocGholish.
Establishing foothold / Command & Control Traffic
Darktrace detected different C2 domains being contacted after the initial infection. These domains overlap across various victims, showing that the attacker is reusing infrastructure within the same campaign. The C2 communication – comprised of thousands of connections over several days – took place over encrypted channels with valid SSL certificates. No single infected device ever beaconed to more than one C2 domain at a time.
Two example C2 domains are listed below with more details:
techgreeninc[.]com
SSL beacon details:
- Median beacon period: 3 seconds
- Range of periods: 1 seconds - 2.58 minutes
- Data volume sent per connection on average: 921 Bytes
investimentosefinancas[.]com
SSL beacon details:
- Median beacon period: 1.7 minutes
- Range of periods: 1 seconds - 6.68 minutes
- Data volume sent per connection on average: 935 Bytes
Certificate information:
- Subject: CN=investimentosefinancas.com
- Issuer: CN=Thawte RSA CA 2018,OU=www.digicert.com,O=DigiCert Inc,C=US
- Validation status: OK
Note in particular the median beacon period, which indicates that some C2 channels were much more hands-on, whilst others possibly acted as backup channels in case the main C2 was burned or detected. It’s also interesting to see the low amount of data being transferred to the hands-on C2 domains. The actual data exfiltration took place to yet another C2 destination, intentionally separated from the hands-on intrusion C2s. All observed C2 websites were recently registered with Russian providers and are not responsive (see below).

Figure 2: The unresponsive C2 domain
Registrar: reg.ru
Created: 2020-06-29 (6 weeks ago) | Updated: 2020-07-07 (5 weeks ago)
Figure 3: Some key information relating to the C2 domain
Darktrace’s Cyber AI Platform detected this Command & Control activity via various behavioral indicators, including unusual beaconing and unusual usage of TLS (JA3).
Internal reconnaissance
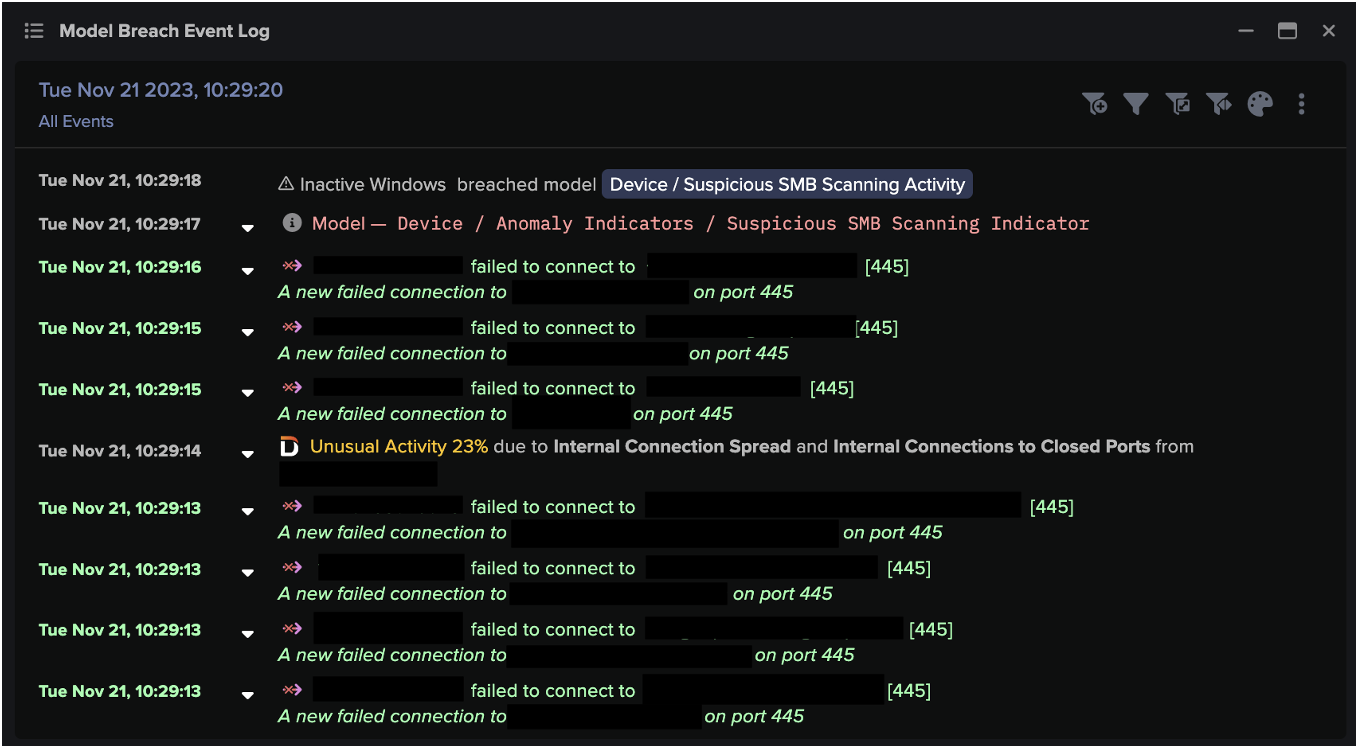
In some cases, Darktrace witnessed several days of inactivity between establishing C2 and internal reconnaissance. The attackers used Advanced Port Scanner, a common IT tool, in a clear attempt to blend in with regular network activity. Several hundred IPs and dozens of popular ports were scanned at once, with tens of thousands of connections made in a short period of time.
Some key ports scanned were: 21, 22, 23, 80, 135, 139, 389, 443, 445, 1433, 3128, 3306, 3389, 4444, 4899, 5985, 5986, 8080. Darktrace detected this anomalous behavior easily as the infected devices don’t usually scan the network.
Lateral movement
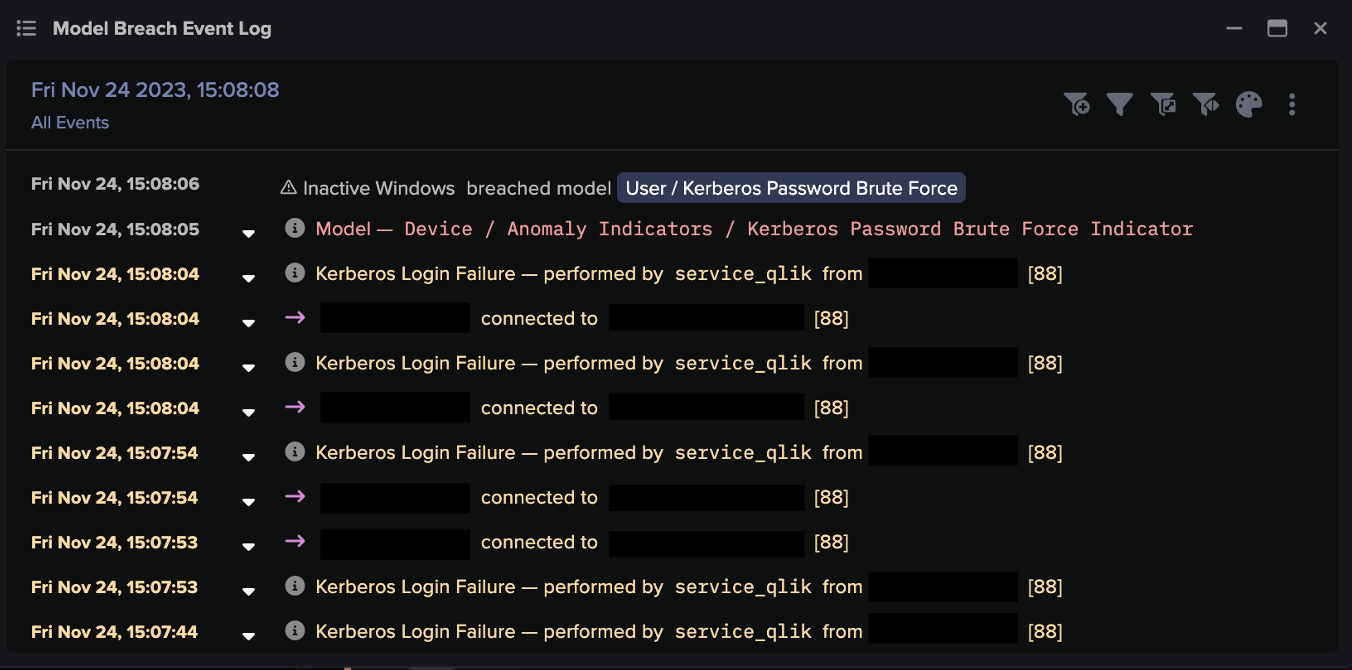
Different methods of lateral movement were observed across intrusions, but also within the same intrusion, with WMI used to move between devices. Darktrace detected this by identifying when WMI usage was unusual or new for a device. An example of the lateral movement is shown below, with Darktrace detecting this as ‘New Activity’.

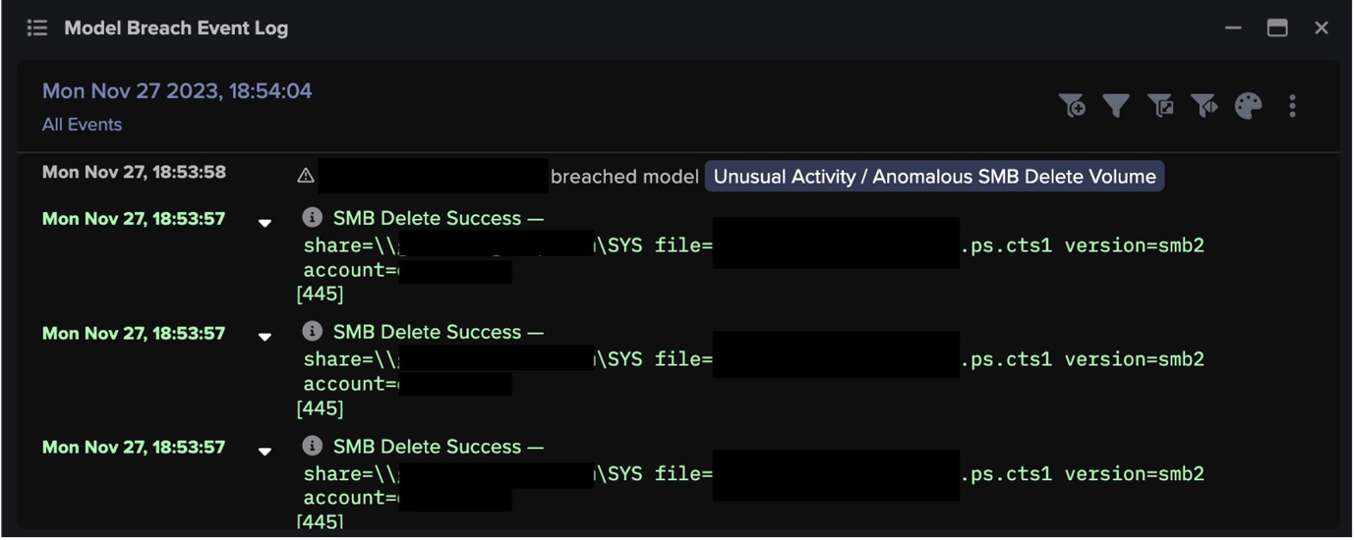
Figure 4: The model breach event log
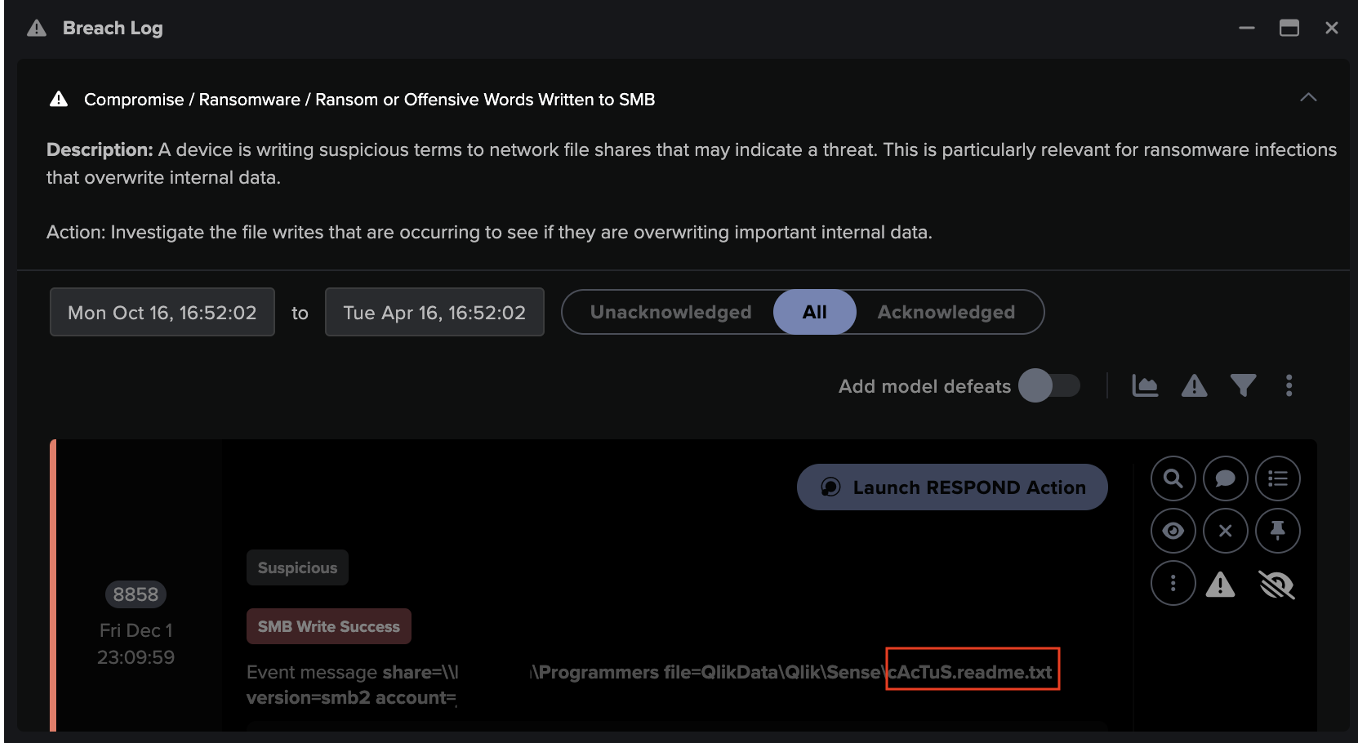
PsExec was used where it already existed in the environment and Darktrace also witnessed SMB drive writes to hidden shares to copy malware, e.g.
C$ file=Programdata\[REDACTED]4rgsfdbf[REDACTED]
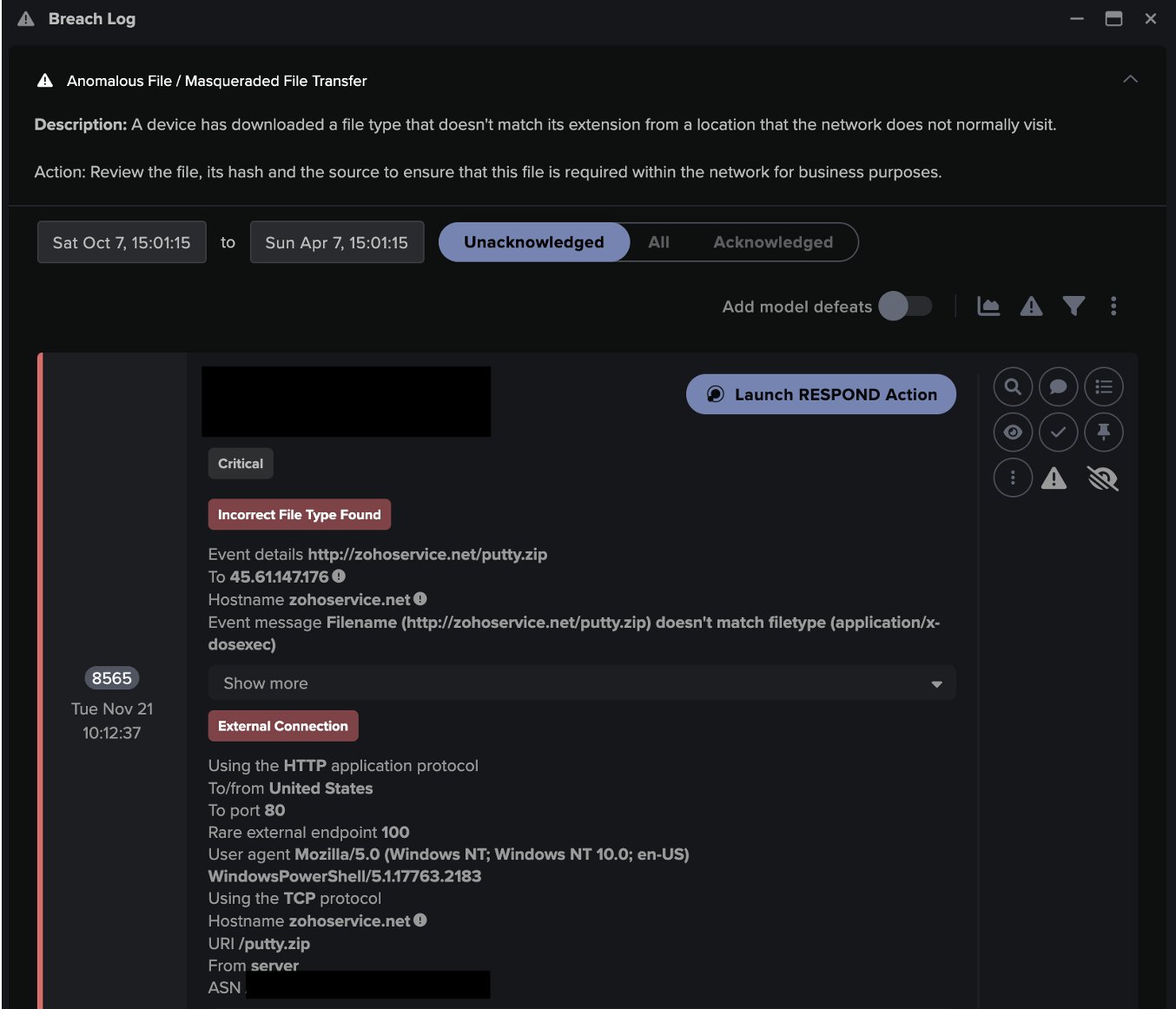
A malicious Powershell file was downloaded – partly shown in the screenshot below.

Figure 5: The malicious Powershell file
Accomplish mission – Data exfiltration or ransomware deployment
Evil Corp is currently best known for its WastedLocker ransomware. Whilst some of its recent intrusions have seen ransomware deployments, others have been classic cases of data exfiltration. Darktrace has not yet observed a double-threat – a case of exfiltration followed by ransomware.
The data exfiltration took place over HTTP to generic .php endpoints under the attacker’s control.
How Cyber AI Analyst reported on WastedLocker
When the first signs of anomalous activity were picked up by Darktrace’s Enterprise Immune System, Cyber AI Analyst automatically launched a full investigation and quickly provided a full overview of the overall incident. The AI Analyst continued to add more details to the ongoing incident as it evolved. There were a total of six AI Analyst incidents for the week spanning an example Evil Corp intrusion – and two of them directly covered the Evil Corp attack. In stitching together disparate security events and presenting a single narrative, Cyber AI Analyst did all the heavy lifting for human security staff, who could look at just a handful of fully-investigated incidents, instead of having to triage countless individual model breaches.

Figure 6: Cyber AI Analyst’s overview of the incident
Note how AI Analyst covers five phases of the attack lifecycle in a single incident report:
- Unusual Repeated Connections – Initial C2
- Possible HTTP Command & Control Traffic – Further C2
- Possible SSL Command & Control Traffic – Further C2
- Scanning of Multiple Devices – Internal reconnaissance with Advanced IP Scanner
- SMB Writes of Suspicious Files – Lateral Movement
Evil Corp rising
Every indicator suggests that this was not a case of indiscriminate ransomware, but rather highly sophisticated and targeted attacks by an advanced threat actor. With the ultimate goal of ransoming operations, the attacker moved towards the crown jewels of the organization: file servers and databases.
The organizations involved in the above analysis did not have Darktrace Antigena – Darktrace’s Autonomous Response technology – in active mode, and the threat was therefore allowed to escalate beyond its initial stages. With Antigena in full operation, the activity would have been contained at its early stages with a precise and surgical response which would have stopped the malicious behavior whilst allowing the business to operate as normal.
Despite the targeted and advanced nature of the threat, security teams are perfectly capable of detecting, investigating, and stopping the threat with Cyber AI. Darktrace was able to not only detect WastedLocker ransomware based on a series of anomalies in network traffic, but also stitch together those anomalies and investigate the incident in real time, presenting an actionable summary of the different attack stages without flooding the security team with meaningless alerts.
Learn more about Autonomous Response
Network IoCs:
IoCCommenttechgreeninc[.]comC2 domaininvestimentosefinancas[.]comC2 domain
Selected associated Darktrace model breaches:
- Compromise / Beaconing Activity To External Rare
- Compromise / Agent Beacon (Medium Period)
- Compromise / Slow Beaconing Activity To External Rare
- Compromise / Suspicious Beaconing Behaviour
- Device / New or Unusual Remote Command Execution
- Compromise / Beaconing Activity To External Rare
- Compromise / Agent Beacon (Medium Period)
- Compromise / Slow Beaconing Activity To External Rare
- Device / New User Agent
- Unusual Activity / Unusual Internal Connections
- Device / Suspicious Network Scan Activity
- Device / Network Scan
- Device / Network Scan - Low Anomaly Score
- Device / ICMP Address Scan
- Anomalous Server Activity / Anomalous External Activity from Critical Network Device
- Compromise / SSL Beaconing to Rare Destination
- Anomalous Connection / SMB Enumeration
- Compliance / SMB Drive Write
- Anomalous File / Internal / Unusual SMB Script Write































![Cyber AI Analyst Incident Log showing the offending device making over 1,000 connections to the suspicious hostname “zohoservice[.]net” over port 8383, within a specific period.](https://assets-global.website-files.com/626ff4d25aca2edf4325ff97/662971c1cf09890fd46729a1_Screenshot%202024-04-24%20at%201.55.10%20PM.png)