Darktrace regularly observes an increase in cyber-attacks carried out during holidays, weekends, and outside of working hours. It is clear that such ‘off peak’ attacks allow easy exploitation of standard organizational practices and human vulnerabilities.
As reduced staff wind down and employees mentally and physically log off from the workplace, there is a decline in the speed of detection and triage within an enterprise. This allows threat actors to sneak in unnoticed. Without real-time autonomous systems, when executed these unexpected attacks have a much greater impact on response and recovery.
Ransomware: An unwanted present
One of the most frequent threats detected out of hours is ransomware. In 76% of infections, the encryption process begins either after hours or during the weekend. Darktrace was alerted to a ransomware incident which was executed in the early hours of a client’s network on Christmas Day, when most employees were offline.

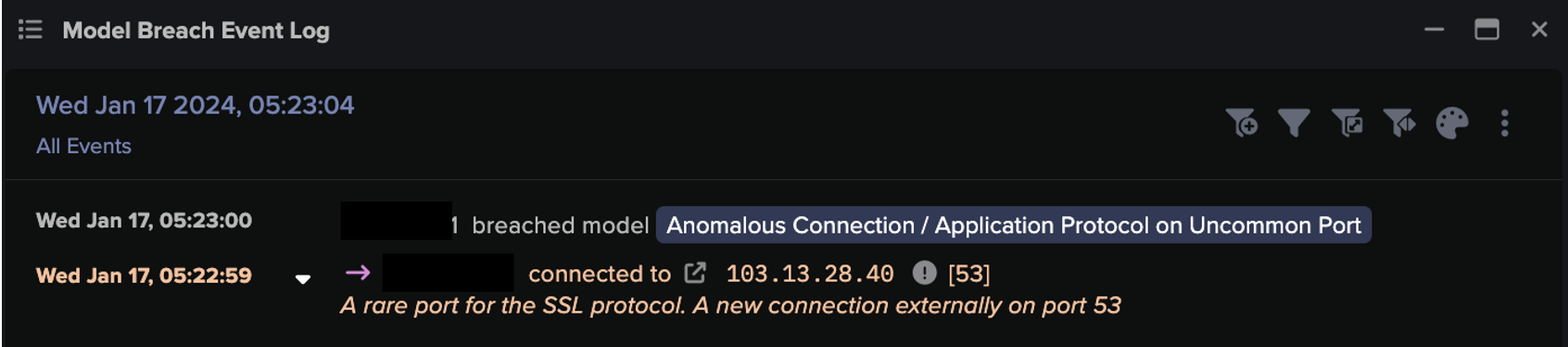
Over a week before the encryption began, an initial foothold was established on an unassuming desktop. Using this vector, the threat actor was able to move laterally and gain access to two domain controllers – servers used to verify users and authenticate requests. The two servers then made unusual command and control (C2) connections to a rare endpoint linked to ransomware. Next, the threat went into hiding. Although Darktrace had alerted to this activity at every stage, the security team was under great stress during the December period and did not manage to action even these highly critical alerts. Without Antigena Network or Proactive Threat Notifications (PTNs), the threat remained uninterrupted.
It suddenly re-emerged after hours on December 24 and utilized its additional privileges to write suspicious executable files to a range of internal devices. A pre-determined set of company data was exfiltrated and a ransomware payload downloaded from the same cloud destination.
A cyber-attack striking on a public holiday is likely to destabilize communication – who is responsible for dealing with it? Are they hard to reach? Are there different protocols for an out-of-hours breach? When unexpected during the holidays, these questions may be surprisingly hard to answer. When answers finally arrive, it is often too late – the damage has already been done.
Once dealt with, there are also repercussions for evaluation: security personnel will be needed to investigate what happened and the future consequences of the attack. If internal staff are hard to mobilize, and external security services come at a premium, this process can be arduous and key evidence may be lost. In turn, the company will be left open to similar attacks in the future.
Saturday night fearware
Holidays clearly pose a human and logistical vulnerability. However, it is often overlooked that these same down periods occur on a small scale throughout the year – at the end of every week. Darktrace has observed a huge surge in weekend attacks in recent months.

This includes another ransomware incident, which struck a hospitality organization based in the UK. A company device was compromised when a user unintentionally accessed a harmful email. The infection exploited cleartext password files to laterally move to four other devices, including critical servers which it then used to host outbound spam and further disseminate. For several following weekends, compromised devices made a large volume of open or Tor-hosted C2 connections to endpoints associated with the XINOF ransomware.
This example shows that out-of-hours infections can come from any vector, and human compliance errors can be exploited to quickly propagate malware and hide before the security team returns to work on Monday. With many data breaches already taking months to discover, threat actors are looking to extend their concealment by implementing the initial compromise at times with decreased monitoring.
Improving detection of these first compromises and adapting to smaller out-of-hours periods may lead to improved response and adjustment for larger holidays as well. But for a permanent fix, enterprises need a proactive approach.
The solution which never sleeps
In the case study above, Autonomous Response was possible at every attack stage, had it been switched on in active mode. Antigena Email would have stopped the initial compromise by identifying the anomalous attachment and quarantining the infection before it could enter the network. Once inside, the critical servers exploited would not have been compromised, as the malicious login activity using gathered passwords would have been halted until verified. Finally, connections to the malicious sites containing the XINOF payload could have been blocked, stopping further damages from occurring.
Unlike a human, AI never sleeps, and never takes a holiday. Instead, the AI stays active around the clock, containing all types of threats in their earliest stages. This prevents malicious activity from escalating while giving human security teams valuable airtime to react and remediate the root cause of any incidents.
If a security team requires an extra set of eyes to augment their investigation, incidents can also be mitigated with Proactive Threat Notifications (PTNs). This service funnels high-severity detections straight into Darktrace’s customer-dedicated SOC to be investigated by expert cyber analysts. The Darktrace PTN SOC has a follow-the-sun approach to monitoring customer environments, meaning that organizations are protected from attacks around the clock.
Timing is everything
The case studies in this blog should serve as a reminder of the need for 24/7 attentiveness. As security professionals increase their skills and creativity in combating threats, malicious actors continue to adapt themselves and are using timing to their advantage during attacks. Now more than ever, it is clear that autonomous AI-based detection is the only means to remove the advantage of timing from threat actors so that even when the office is closed or the laptop is switched off, your security remains on.
Thanks to Darktrace analyst Gabriel Few-Wiegratz for his insights.