A COmprehensive Set of capabilities
Architectural Awareness
Real-time visibility into asset utilization, cloud architecture, and access rights.
Cost insights give a better understanding of resource allocation, helping teams contextualize resources.
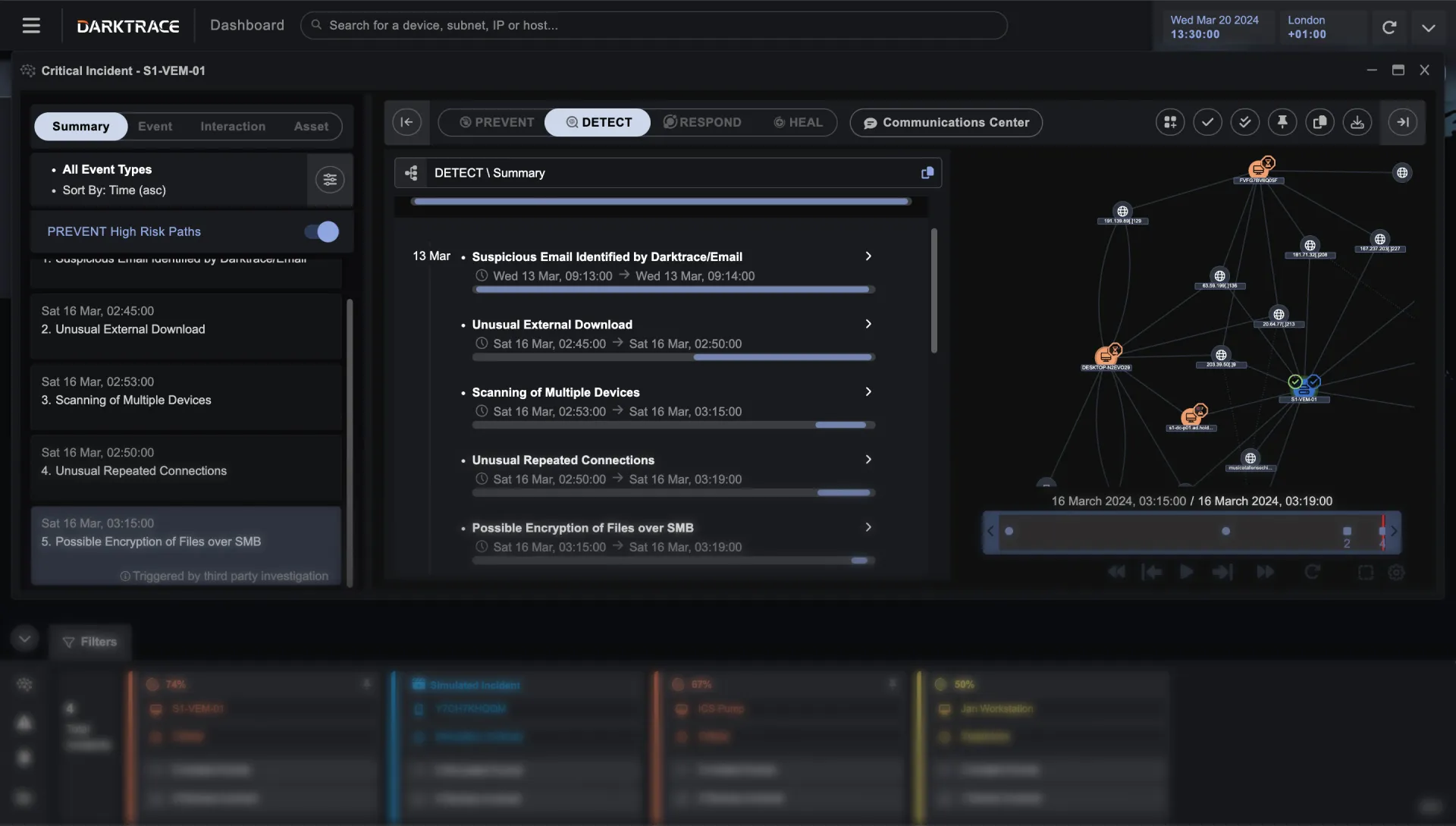
Cloud-Native Detection & Response
Understands ‘normal’ for your unique business; reveals anomalous activity and potential threats.
Platform-native response capabilities to contain threats and minimize business disruption.
Cloud Protection & Compliance
Real-time attack path modeling considers attack vectors on the control plane and beyond.
Identify compliance issues and potential misconfigurations, with prioritized remediation steps.
The cloud is an extremely dynamic environment. Workloads come and go. Developers change direction. Resources are fluid and hard to pinpoint.
Cloud security must also be dynamic.
It needs to be real-time, all the time.
Darktrace's Cyber AI understands your cloud environment, continuously learning ‘normal’ across your network, architectural and management layers.
This allows it to prioritize risks and correlate threats, giving you insight into what is going on in your cloud architecture right now.
AUTONOMOUS RESPONSE
Real-Time Response to Emerging Incidents
Because Darktrace AI knows what’s normal for your cloud environment, it can take surgical action to shut down anomalous, threatening activity – all through platform-native controls.



Compatible with all major cloud providers
Scales to organizations large and small, in any industry
Darktrace/Cloud™ customers come in all shapes and sizes, and operate a range of cloud platforms and services. Built for SMB, Enterprise, Government, and Critical Infrastructure.

The Right Approach Can Handle Anything
See Use Cases

Data Exfiltration

Critical Misconfigurations

Insider Threats

Vulnerabilities that matter to you
capabilities
Combined Cloud Security
Architectural Awareness

Get a comprehensive understanding into your cloud architecture, including users and permissions, in real time.
Learn moreCloud-Native Detection & Response

Detect cloud threats with AI behavioral modeling of devices, containers, and users, and unlock truly autonomous response in the cloud.
Learn moreCloud Protection & Compliance

Uncover misconfigurations, vulnerabilities, and compliance issues, and prioritize on true cyber risk with attack surface management and attack path modeling.
Learn more
white paper
CISO’s Guide to Cloud Security
Demystify the cloud and discover your security blind spots.
Download now


Darktrace ActiveAI Security Platform
The Active AI Security Platform correlates threats across your entire organization, delivering proactive cyber resilience with real-time detection and autonomous response to known and novel threats.
Learn more