DARKTRACE OPERATIONAL TECHNOLOGY CYBERSECURITY
Revolutionizing OT Risk Management
New innovations to Darktrace/OT makes it the industry’s first OT cybersecurity solution to move beyond CVE scores and redefine vulnerability management for critical infrastructure, tackling the full breadth of risks not limited by traditional controls.

Darktrace/OT understands your infrastructure's unique risks by building a comprehensive and contextualized picture that goes beyond isolated CVE scoring, combining attack path modelling with MITRE techniques to provide hardening recommendations regardless of patching availability, and opening a window into the potential impact of an attack from APT groups.
Unparalleled visibility across IT & OT
Identify IT and OT Convergence
AI augmented workflows ensures OT cybersecurity analysts and operation engineers can manage IT and OT environments, leveraging a live asset inventory and tailored dashboards to optimize security workflows and minimize operator workload.


Bespoke OT Cyber Risk Management
Move beyond CVE Prioritization
The only OT cybersecurity solution to provide bespoke risk management that combines attack path modelling with MITRE techniques to harden systems regardless of patching availability.
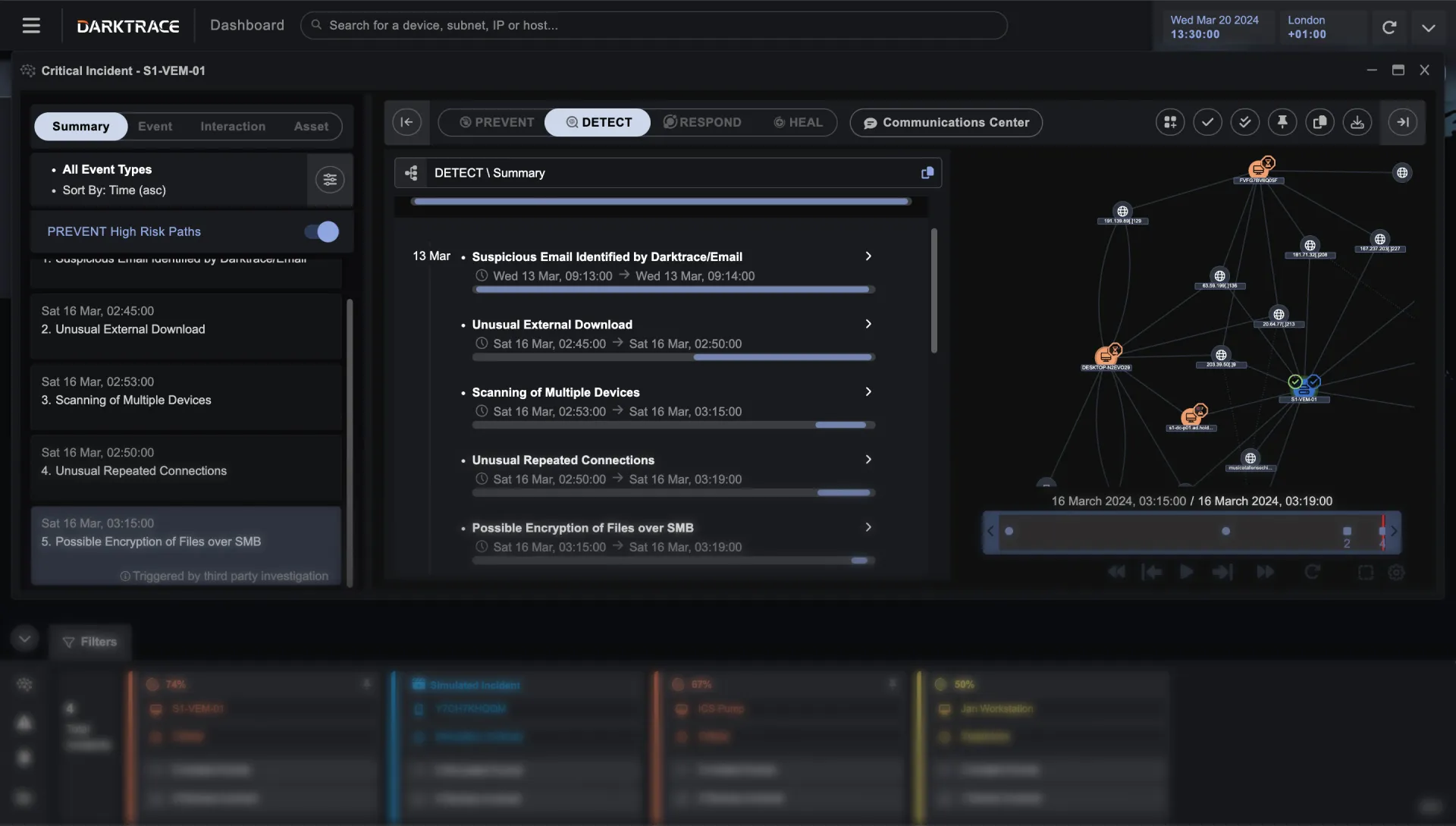
AI-Led Detection, Response, & Investigation
90% reduction in total triage time
Darktrace/OT leverages Self-Learning AI to understand activity across your unique infrastructure, detecting and containing all known and unknown threats while ensuring operations continue.

Providing OT Cybersecurity to 9000+ customers across every industry

Electric Power


Water Treatment


Telecommunications


Transportation


Maritime


Manufacturing


Healthcare


Building Management


Oil & Gas

Pharmaceuticals

Mining

“With its ability to self-learn what’s normal for our organization and take action autonomously, Darktrace’s Cyber AI has fast proven to be our team’s most valuable assistant. ”
CIO, Manufacturing and Supply
“Just like with our IT environments, Darktrace/OT leverages AI to understand ‘normal’ behavior for all our bespoke OT and IT/OT ecosystems, identifying and stopping threats at the earliest stages. ”
Vice President of IT, Financial Services
“Darktrace’s machine learning approach provides unprecedented awareness across both our IT and OT networks, making it uniquely capable of fighting the battle before it has truly begun.”
CIO, Government/Municipality
Maps to major frameworks
SOLUTION BRIEF
Darktrace/OT
Get more insight into the business and operational benefits of unified OT protection


Darktrace ActiveAI Security Platform
The Active AI Security Platform correlates threats across your entire organization, delivering proactive cyber resilience with real-time detection and autonomous response to known and novel threats.
Learn more