より深刻な被害を及ぼしますます高額な標的を狙うようになったランサムウェアは、世界中のさまざまな組織に対して引き続きカオスと破壊をもたらしています。今年初め、‘Maze’ と呼ばれる種類のランサムウェアが急激に拡大しました。これは大手光学製品メーカーであるキヤノンの操業を中断させ、Cognizant社などのFortune 500企業に大損害をもたらしました。
ヘルスケア業界を標的とするランサムウェア
つい先月も、ドイツでデュッセルドルフ大学病院にランサムウェアが侵入し、女性が死亡したというニュースが話題になったばかりで、人命への脅威はもはや理論上だけのものではないことが確認されました。
ランサムウェアはあらゆる産業に影響を及ぼしますが、2020年においてはサイバー犯罪者達はますますヘルスケア、地方自治体、重要インフラなどの生活に不可欠なサービスに被害を及ぼすようになっています。これには意図的なものも巻き添え被害もあります。リスクが高まる中、これらの壊滅的かつ蔓延する攻撃をどう防止するかを理解する必要性も高まっています。
ランサムウェアは、いったん侵入すると、組織のデジタルインフラを通って数秒で水平方向に広がり、数分でシステム全体をオフラインにすることも可能です。攻撃者はしばしば夜間や週末を狙って攻撃します。その時間はセキュリティチームの対応が遅くなることを知っているからです。マシンスピードの攻撃にはマシンスピードの防御、すなわち人間の指示を必要とせずにこの脅威に対応し、脅威を自律的に阻止できる防御が必要です。
本稿ではEメール、SaaSアプリケーション、ネットワーク、クラウド、IoT、産業用制御システムまでのデジタルエステート全体において「正常」を学習することによりランサムウェアをどのように検知し阻止するのかについて、Darktraceにより顧客環境で検知されたMazeランサムウェアの例を使って説明します。
Darktraceの自己学習型AIは脅威が発生すると即座にそれを検知しましたが、自動対処機能はPassiveモードに設定されていたため、脅威を無害化するには人間によるアクションが必要でした。つまり、攻撃者達は組織内を素早く水平移動し、セキュリティチームが介入する前にファイルの暗号化を開始することができたのです。Activeモードに設定されていれば、Antigena Networkは最も早い段階でこのアクティビティを封じ込めていたでしょう。
DarktraceはMazeのようなランサムウェアをどのように検知するか?
Darktraceは(仮想的にまたはオンプレミスで)導入されるとすぐに、AIが組織全体のあらゆるユーザーとデバイスの「生活パターン」の学習を始めます。これによりサイバー脅威の兆候かもしれない異常なアクティビティを検知することができるのです。これはハードコードされたルールやシグネチャに頼ることなく行われます。ルールやシグネチャを使用するアプローチでは、これらのリストを更新してその後の同様の脅威を封じ込めるために「第一号患者」が必要です。新種のランサムウェアが組織全体に広がり何百台ものデバイスを数秒で感染させるような状況では、そのようなアプローチは役に立ちません。
組織の「生活パターン」の理解を持つことにより、DarktraceのAIは通常と異なるアクティビティをリアルタイムに認識することができます。そうしたアクティビティには次のようなものがあります:
ActivityDarktrace detectionsUnusual downloads from C2 serversEXE from Rare Destination / Masqueraded File TransferBrute forcing publicly accessible RDP serversIncoming RDP brute force modelsBrute forcing access to web portal user accounts with weak passwords or lacking MFAVarious brute force modelsC2 via Cobalt Strike / Empire PowershellSSL Beaconing to Rare Endpoint / Empire Powershell and Cobalt Strike modelsNetwork scanning for reconnaissance & EternalBlue exploitSuspicious Network Scan model known to download Advanced IP Scanner after successful exploitMimikatz usage for privilege escalationUnusual Admin SMB Session / Unusual RDP Admin Session (Procdump, PingCastle, and Bloodhound)Psexec / ‘Living off the Land’ for lateral movementUnusual Remote Command Execution / Unusual PSexec / Unusual DCE RPCData exfiltration to C2 serversData Sent to Rare Domain / Unusual Internal Download / Unusual External UploadEncryptionSuspicious SMB Activity / Additional File Extensions AppendedExfiltration of passwords through various cloud storage servicesData Sent to New External DomainRDP tunnels using NgrokOutbound RDP / Various beaconing models
さらに、Darktraceはインターネットに接続されたサーバーに対するブルートフォースアクセスの試みも識別することができます。また、プレーンテキスト形式で保存されたパスワード、およびさまざまなパスワード管理データベースを狙った検索を検知することができます。
実際の感染事例からの考察

図1: 攻撃のタイムライン
最近では、DarktraceのAIが、医療機関を標的としたMazeランサムウェアのケースを検知しました。DarktraceのCyber AI Analystは直ちにインシデント全体の自動調査を開始し、セキュリティチームに対して自然言語で書かれた実用的な要約を即座に提示しました。
最初の感染ベクトルはスピアフィッシングでした。Mazeはパンデミックをテーマにしたフィッシングメールを使って医療機関に頻繁に配信されています。DarktraceはMicrosoft 365のユーザー毎の正常な行動を学習・理解し、フィッシングの兆候となる異常を自律的に発見するAI搭載のEメールセキュリティも提供していますが、この保護機能を導入していなかったため、Eメールは従来のゲートウェイをすり抜けていました。
攻撃者はネットワークスキャニングアクティビティと列挙を開始し、研究開発部門のサブネット内でアクセスをエスカレートさせました。DarktraceのAIはadminレベルの認証情報の侵害、珍しいRDPアクティビティおよびKerberos認証の試みを検知しました。
Darktraceは攻撃者がドメインコントローラをアップロードしていることを検知しましたが、次いでバッチファイルが複数のファイル共有に書き込まれ、それが暗号化プロセスに使用されました。
感染したデバイスはその後Maze mazedecrypt[.]topに関連した不審なドメインに接続され、TORブラウザバンドルがおそらくC2目的でダウンロードされました。その後、研究開発部門のサブネットから大量の機密データが未知のドメインにアップロードされました。これはMazeランサムウェアに特徴的な動作であり、重要なファイルを暗号化しようとするばかりか、そのコピーを攻撃者に送信するという点で「二重の脅威」と言われる所以です。
このdoxwareとも言われる攻撃形態は、身代金の支払いが拒否されたときにも攻撃者が力を持てるようにするものです。たとえばこのデータをダークウェブに売ったり、知的財産を競合他社にリークすると脅したりすることができるからです。
Cyber AI Analystを使ったリアルタイムの自動化された調査
攻撃ライフサイクル全体を通じて、複数の高確度のアラートがDarktraceのAIによって生成され、これによりCyber AI Analystが自動的にバックグラウンドで調査を開始し、さまざまなイベントをつなぎ合わせて1つの包括的なセキュリティインシデントにまとめ、セキュリティチームがレビューできるよう単一の画面に表示しました。

図2:未知の外部ドメインに対するデータ流出

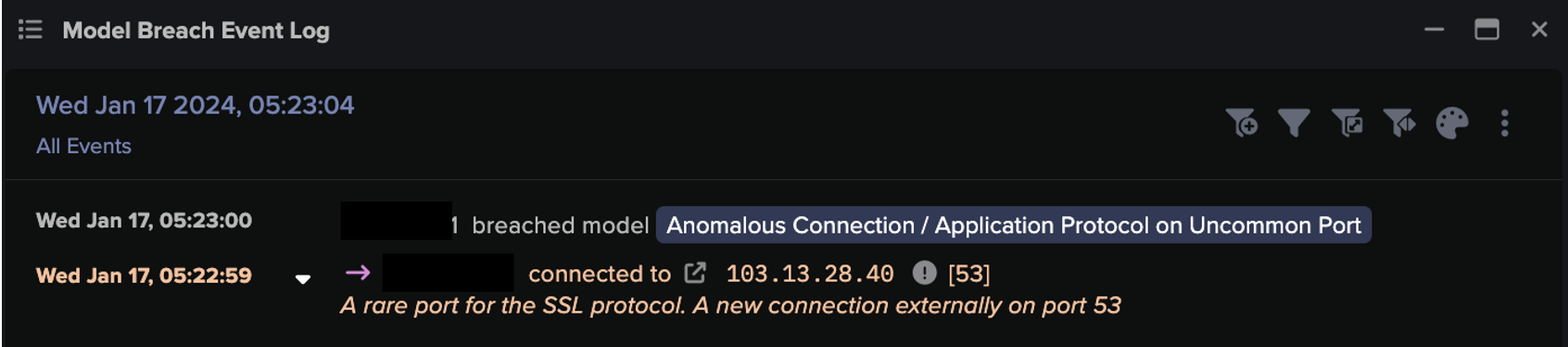
図3:Darktraceのユーザーインターフェイスはランサムウェア攻撃に直接関係したドメインコントローラ上の異常なアクティビティおよびModel Breachを明確に表示
Mazeのような標的型の二重脅威攻撃は増えつつあり、きわめて危険です。それらはますますリスクの高い環境を標的にするようになっています。数千社の組織が、上記のようなランサムウェアの侵入を検知し調査するためだけではなく、イベント発生時に自律的に対応させるためにAIを選択しています。このようなランサムウェア攻撃は、アクティブモードに設定された自動対処機能が単に「あると助かる」ものではなく「ぜひとも必要な」ものであることを証明しています。動きの速い脅威に対してはマシンスピードの対応が要求されるからです。
前回のブログでは、新種のゼロデイ攻撃が従来型のセキュリティツールをすり抜けたものの、Antigena Networkがアクティブモードに設定されていたため脅威の進行が自律的に阻止された事例を紹介しました。この独自の機能は、ますます巧妙化する攻撃手法の標的となっているあらゆる業界の組織にとってきわめて重要なものとなりつつあります。
この脅威検知についての考察はDarktraceアナリストAdam Stevens が協力しました。
Darktraceによるモデル検知
- Device / Suspicious Network Scan Activity
- Device / Network Scan
- Device / ICMP Address Scan
- Unusual Activity / Unusual Internal Connections
- Device / Multiple Lateral Movement Model Breaches
- Experimental / Executable Uploaded to DC
- Compromise / Ransomware::Suspicious SMB Activity
- Compromise / Ransomware::Ransom or Offensive Words Written to SMB
- Compliance / SMB Drive Write
- Compliance / High Priority Compliance Model Breach
- Anomalous Connection / SMB Enumeration
- Device / Suspicious File Writes to Multiple Hidden SMB Shares
- Device / New or Unusual Remote Command Execution
- Anomalous Connection / New or Uncommon Service Control
- Anomalous Connection / SMB Enumeration
- Compromise / Ransomware::Ransom or Offensive Words Written to SMB
- Anomalous Connection / High Volume of New or Uncommon Service Control
- Experimental / Possible Ransom Note
- Anomalous File / Internal::Additional Extension Appended to SMB File
- Compliance / Tor Package Download
- Device / Suspicious Domain
- Device / Long Agent Connection to New Endpoint
- Anomalous Connection / Data Sent to Rare Domain