Cloud-Native AI Email Security

Complete Email Threat Protection
Stop the 38% of advanced threats that evade all other email security solutions
(Darktrace Threat Report 2023)Catch unknown threats 13 days earlier with proactive defense
(Darktrace Press Release, April 3, 2023)Achieve 60% improvement in quality of end-user phishing reports and detection of sophisticated malicious weblinks
“Block 25% more threats than traditional Secure Email Gateways”
(Darktrace customer quote, Manufacturing)A Self-Learning AI Approach for Novel Threats
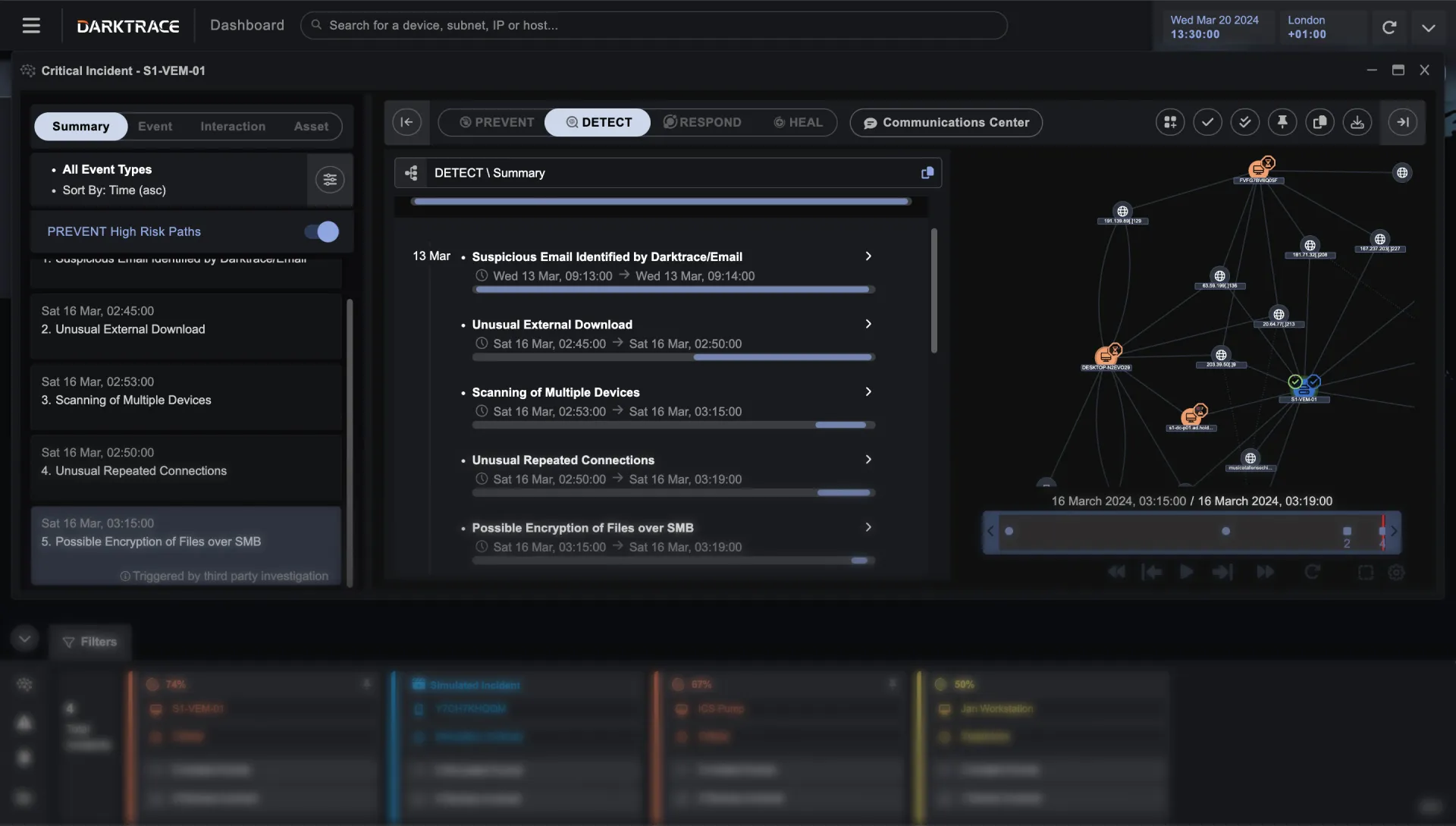
Spotting targeted or unknown threats requires an understanding of ‘normal’. Darktrace’s AI-based email security offers protection against zero-day and multi-vector attacks which isn’t limited to historical attack rules and data. As attacks evolve, so will your security.
- Attack-centric data
- Payload focused

- Business-centric data
- User/behavior focused

Best-in-class email threat protection
Uniquely combines behavioral and content analysis across inbound, outbound and lateral mail plus Microsoft Teams messaging
Detects the earliest signs of phishing and account compromise by analyzing account based behavioral signals
Blocks the entire spectrum of outbound mail threats with advanced data loss prevention – from human error to insider threat
Gain complete brand protection while enhancing your existing security investments
Builds on your existing Microsoft and Google mail solution, creating defense in depth by uniting threat intelligence and business-centric approaches
Offers the easiest path to brand protection and compliance with a AI-assisted deployment of DMARC
Harnesses AI email security insights across your entire security operations workflows to reduce detection and containment times – leveraging context from the Darktrace platform


Augment your end-users and SOC workflows to improve security
Reduces phishing investigations by 60% and increase the quality of end user reports by providing unique feedback to each employee as they interact with their mail
Detects and remediates 70% more malicious sophisticated links with advanced link analysis
Speeds mean time to respond and eliminates console hopping with streamlined SOC workflows, Cyber AI Analyst reports and the Darktrace Mobile App
Look beyond traditional Secure Email Gateways to AI email security
Combines API and journaling access from your native email cyber security provider to eliminate latency – for protection without disrupting mailflow
SEGs detect only known threats and require expensive workarounds to see internal mail – Darktrace has unlimited visibility into all communications
Adaptive AI removes weekly maintenance and configuration tuning, replacing the need for static block lists

Installs in seconds through API

Read about the latest innovations to our email security platform, including AI-augmented data loss prevention, industry-leading domain protection, major enhancements to streamline SOC workflows and advanced prevention for Microsoft Teams.


Better Together
Darktrace/Email

Darktrace ActiveAI Security Platform
The Active AI Security Platform correlates threats across your entire organization, delivering proactive cyber resilience with real-time detection and autonomous response to known and novel threats.
Learn more