DARKTRACE APP SECURITY
Integrated Cloud Application Protection
Darktrace/Apps learns your unique business, along with every cloud user and application they use, to identify potential threats based on login behavior, administration activity, file transfers, and more.









Darktrace Self-Learning AI asks millions of questions around every cloud app user to determine:
Is this normal?
Covering every major cloud app platform







App security WITH CONTEXT
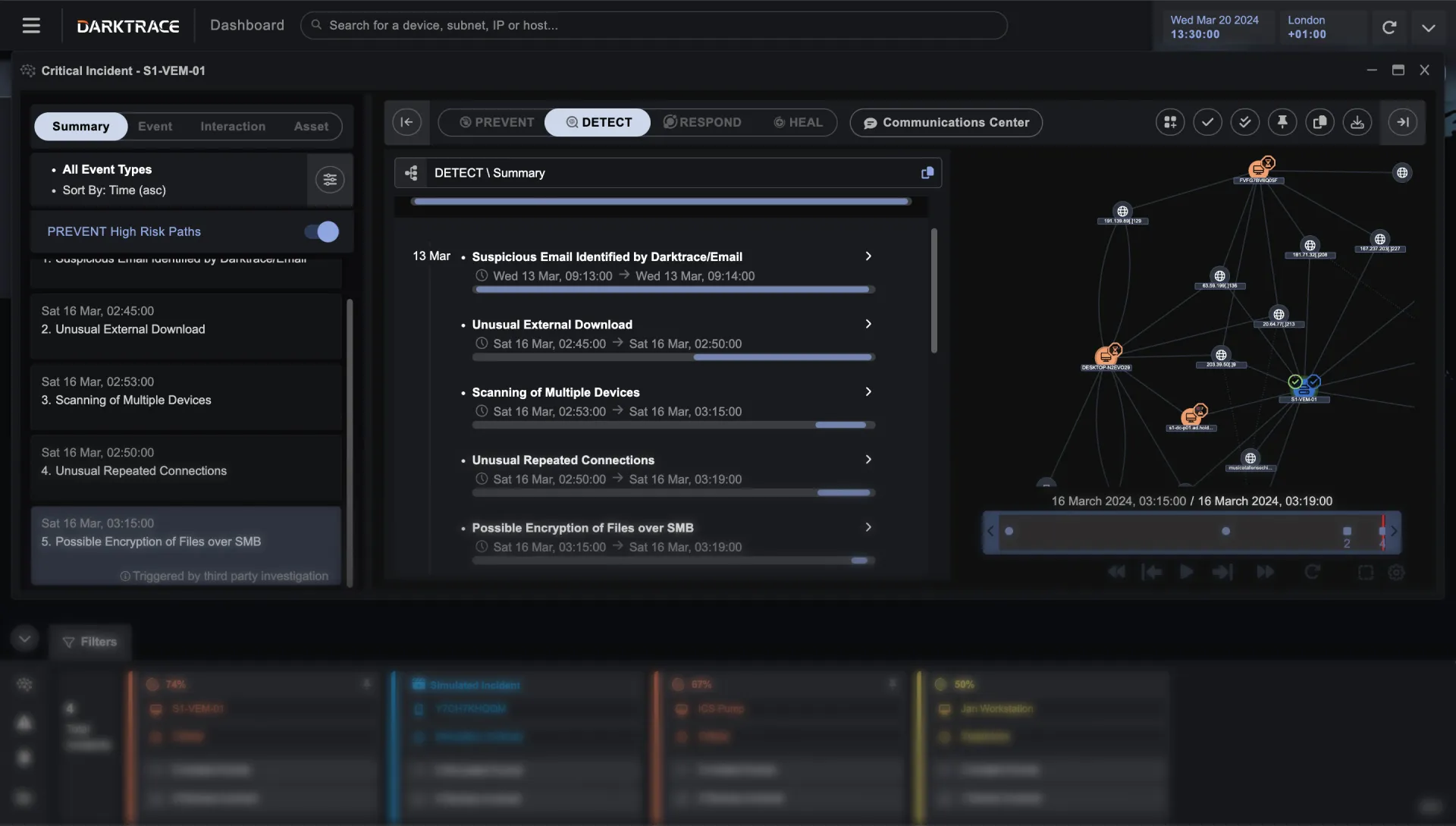
Break down security silos
Modern cyber attacks traverse multiple fields of operation. Data from cloud applications is often just one piece of the puzzle, which is why Darktrace/Apps provides context derived from your entire digital ecosystem.


Self-Learning AI
Cloud app security that learnsyou
Darktrace/Apps learns your unique business, along with every application it uses, to spot behavior that doesn’t belong.
TAKING ACTION
Faster than the fastest threats
Darktrace/Apps takes a targeted and appropriate response to account takeover, data loss and other cloud application-based threats.


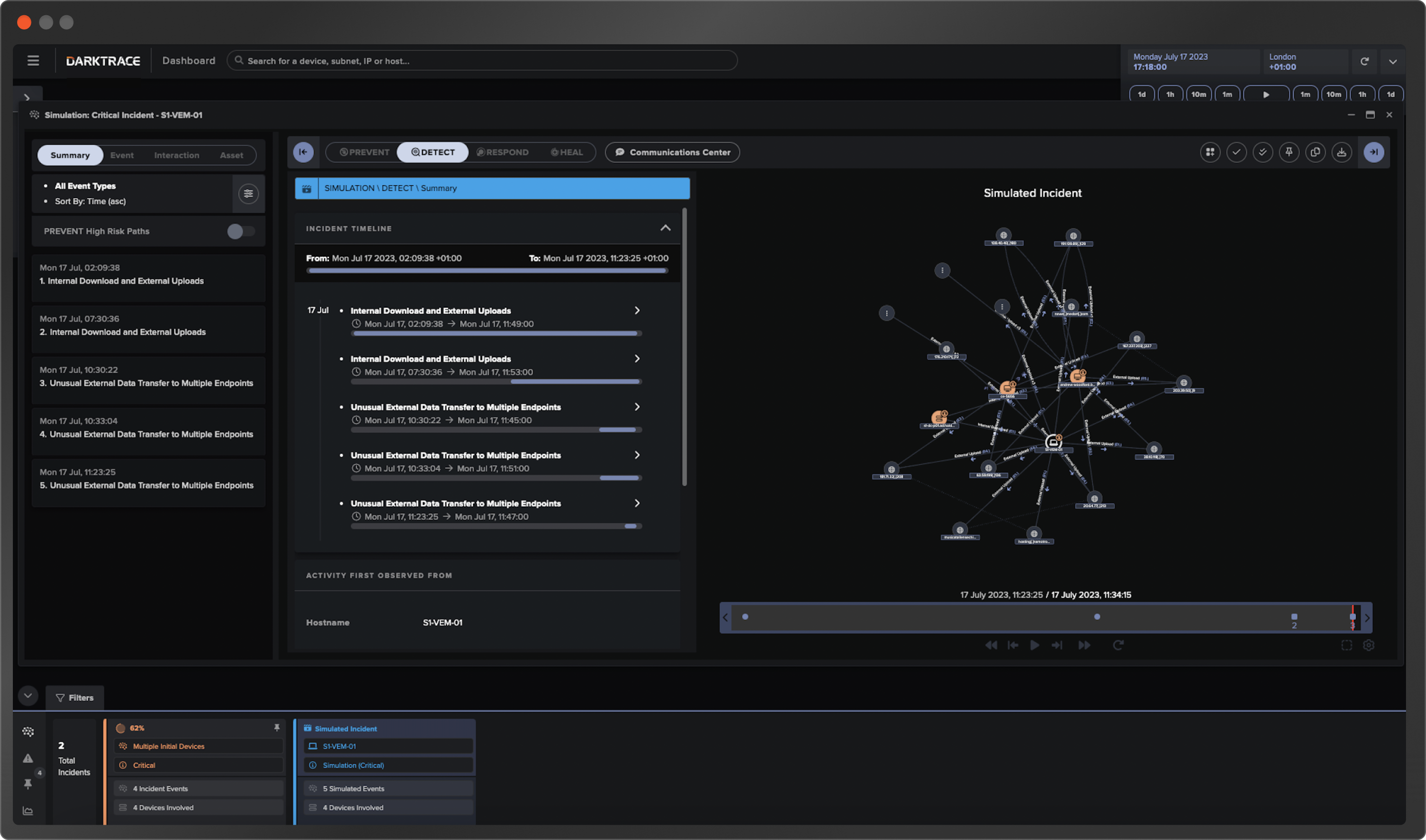
AI ANALYST
Understand what happened, instantly
Cyber AI Analyst investigates every anomaly and stitches together individual events, generating digestible incident summaries.
DETECT + RESPOND/Apps
A unique solution to keep you secure from future attacks.
Perfectly tuned response. Proportionate action for every threat.


Scales to organizations large and small, in any industry
Darktrace/Apps customers come in all shapes and sizes - each with their own lineup of favorite & essential applications. Built for Enterprise, Government, Critical Infrastructure, and SMB. Integrates into your workflow including SIEMs, SOARs, and access via SSO.


Productivity, Protected
Darktrace and Microsoft have partnered to help organizations close the security gaps in their multi-cloud and multi-platform environments. Darktrace complements Microsoft security with Self-Learning AI that detects and autonomously responds to novel cyber-threats that evade other defenses.
One click is all it takes.
Deploys in minutes
Supports cloud or on-premise delivery. Hardware optional
Sits passively, monitoring cloud collaboration apps
Provides protection with autonomous response to blind spots
Darktrace ActiveAI Security Platform
The Active AI Security Platform correlates threats across your entire organization, delivering proactive cyber resilience with real-time detection and autonomous response to known and novel threats.
Learn more