Empowers security teams to reduce cyber risk by prioritizing vulnerabilities and hardening defenses proactively.
Learn more
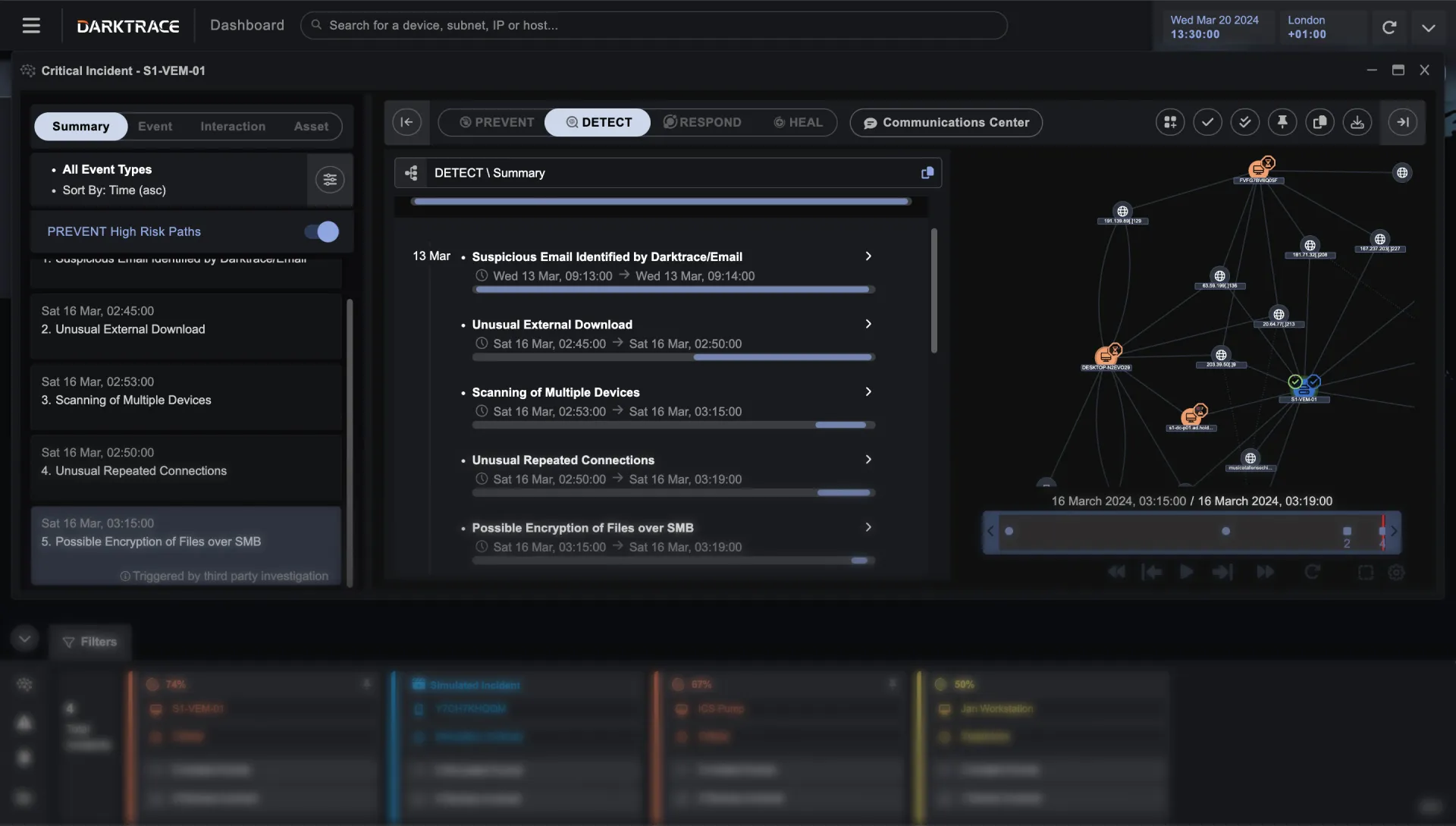
Delivers instant visibility of known and novel threats, powered by a continuously evolving understanding of your business.
Learn more
Acts autonomously to interrupt cyber-attacks with precise and targeted actions, without disrupting regular business operations.
Learn more
Automates incident recovery processes, allowing organizations to return systems to a trusted operational state in the event of a cyber-attack.
Learn moreIntegrages with existing tools

















/Cloud


CISO’s Guide to Cyber AI




Powered by Our Unique AI

/Network


/OT
More coverage areas


Darktrace LIVE is coming to a city near you

"Darktrace/Network helped reduce risk by around 30%. Cyber AI Analyst automates the role of a human security analyst – saving on average 50 hours of work a month. Compared to its previous solution, Darktrace/Email successfully blocked 20-25% more suspicious emails."

"The autonomous side of Darktrace knocks everything else out of the park. AI takes away 90% of the overhead in terms of time spent in the tool, alongside the stress of missing an alert."

"Darktrace has given us a lot of confidence, spotting things we wouldn’t normally as humans. Darktrace analyzes emails in context, containing novel and sophisticated attacks while allowing normal business to continue without disruption."
Darktrace ActiveAI Security Platform
The Active AI Security Platform correlates threats across your entire organization, delivering proactive cyber resilience with real-time detection and autonomous response to known and novel threats.
Learn more