What is VIP impersonation?
VIP impersonation involves a threat actor impersonating a trusted, prominent figure at an organization in an attempt to solicit sensitive information from an employee.
VIP impersonation is a high-priority issue for security teams, but it can be difficult to assess the exact risks, and whether those are more critical than other types of compromise. Looking across a range of Darktrace/Email™ customer deployments, this blog explores the patterns of individuals targeted for impersonation and evaluates if these target priorities correspond with security teams' focus on protecting attack pathways to critical assets.
How do security teams stop VIP Impersonation?
Protecting VIP entities within an organization has long been a traditional focus for security teams. The assumption is that VIPs, due to their prominence, possess the greatest access to critical assets, making them prime targets for cyber threats.
Email remains the predominant vector for attacks, with over 90% of breaches originating from malicious emails. However, the dynamics of email-based attacks are shifting, as the widespread use of generative AI is lowering the barrier to entry by allowing adversaries to create hyper-realistic emails with minimal errors.
Given these developments, it's worth asking the question – which entities (VIP/non-VIP) are most targeted by threat actors via email? And, more importantly – which entities (VIP/non-VIP) are more valuable if they are successfully compromised?
There are two types of VIPs:
1. When referring to emails and phishing, VIPs are the users in an organization who are well known publicly.
2. When referring to attack paths, VIPs are users in an organization that are known publicly and have access to highly privileged assets.
Not every prominent user has access to critical assets, and not every user that has access to critical assets is prominent.
Darktrace analysis of VIP impersonation
We analyzed patterns of attack pathways and phishing attempts across 20 customer deployments from a large, randomized pool encompassing a diverse range of organizations.
Understanding Attack Pathways
Our observations revealed that 57% of low-difficulty attack paths originated from VIP entities, while 43% of observed low-difficulty attack paths towards critical assets or entities began through non-VIP users. This means that targeting VIPs is not the only way attackers can reach critical assets, and that non-VIP users must be considered as well.
While the sample size prevents us from establishing statistical significance across all customers, the randomized selection lends credence to the generalizability of these findings to other environments.
Phishing Attempts
On average, 1.35% of total emails sent to these customers exhibited significantly malicious properties associated with phishing or some form of impersonation. Strikingly, nearly half of these malicious emails (49.6%) were directed towards VIPs, while the rest were sent to non-VIPs. This near-equal split is worth noting, as attack paths show that non-VIPs also serve as potential entry points for targeting critical assets.

For example, a recent phishing campaign targeted multiple customers across deployments, with five out of 13 emails specifically aimed at VIP users. Darktrace/Email actioned the malicious emails by double locking the links, holding the messages, and stripping the attachments.
Given that non-VIP users receive nearly half of the phishing or impersonation emails, it underscores the critical importance for security teams to recognize their blind spots in protecting critical assets. Overlooking the potential threat originating from non-VIP entities could lead to severe consequences. For instance, if a non-VIP user falls victim to a phishing attack or gets compromised, their credentials could be exploited to move laterally within the organization, potentially reaching critical assets.
This highlights the necessity for a sophisticated security tool that can identify targeted users, without the need for extensive customization and regardless of VIP status. By deploying a solution capable of promptly responding to email threats – including solicitation, phishing attempts, and impersonation – regardless of the status of the targeted user, security teams can significantly enhance their defense postures.
Darktrace vs Traditional Email Detection Methods
Traditional rules and signatures-based detection mechanisms fall short in identifying the evolving threats we’ve observed, due to their reliance on knowledge of past attacks to categorize emails.
Secure Email Gateway (SEG) or Integrated Cloud Email Security (ICES) tools categorize emails based on previous or known attacks, operating on a known-good or known-bad model. Even if tools use AI to automate this process, the approach is still fundamentally looking to the past and therefore vulnerable to unknown and zero-day threats.
Darktrace uses AI to understand each unique organization and how its email environment interoperates with each user and device on the network. Consequently, it is able to identify the subtle deviations from normal behavior that qualify as suspicious. This approach goes beyond simplistic categorizations, considering factors such as the sender’s history and recipient’s exposure score.
This nuanced analysis enables Darktrace to differentiate between genuine communications and malicious impersonation attempts. It automatically understands who is a VIP, without the need for manual input, and will action more strongly on incoming malicious emails based on a user’s status.
Email does determine who is a VIP, without a need of manual input, and will action more strongly on incoming malicious emails.
Darktrace/Email also feeds into Darktrace’s preventative security tools, giving the interconnected AI engines further context for assessing the high-value targets and pathways to vital internal systems and assets that start via the inbox.
Leveraging AI for Enhanced Protection Across the Enterprise
The efficacy of AI-driven security solutions lies in their ability to make informed decisions and recommendations based on real-time business data. By leveraging this data, AI driven solutions can identify exploitable attack pathways and an organizations most critical assets. Darktrace uniquely uses several forms of AI to equip security teams with the insights needed to make informed decisions about which pathways to secure, reducing human bias around the importance of protecting VIPs.
With the emergence of tools like AutoGPT, identifying potential targets for phishing attacks has become increasingly simplified. However, the real challenge lies in gaining a comprehensive understanding of all possible and low-difficulty attack paths leading to critical assets and identities within the organization.
At the same time, organizations need email tools that can leverage the understanding of users to prevent email threats from succeeding in the first instance. For every email and user, Darktrace/Email takes into consideration changes in behavior from the sender, recipient, content, and language, and many other factors.
Integrating Darktrace/Email with Darktrace’s attack path modeling capabilities enables comprehensive threat contextualization and facilitates a deeper understanding of attack pathways. This holistic approach ensures that all potential vulnerabilities, irrespective of the user's status, are addressed, strengthening the overall security posture.
Conclusion
Contrary to conventional wisdom, our analysis suggests that the distinction between VIPs and non-VIPs in terms of susceptibility to impersonation and low-difficulty attack paths is not as pronounced as presumed. Therefore, security teams must adopt a proactive stance in safeguarding all pathways, rather than solely focusing on VIPs.
Attack path modeling enhances Darktrace/Email's capabilities by providing crucial metrics on potential impact, damage, exposure, and weakness, enabling more targeted and effective threat mitigation strategies. For example, stronger email actions can be enforced for users who are known to have a high potential impact in case of compromise.
In an era where cyber threats continue to evolve in complexity, an adaptive and non-siloed approach to securing inboxes, high-priority individuals, and critical assets is indispensable.











































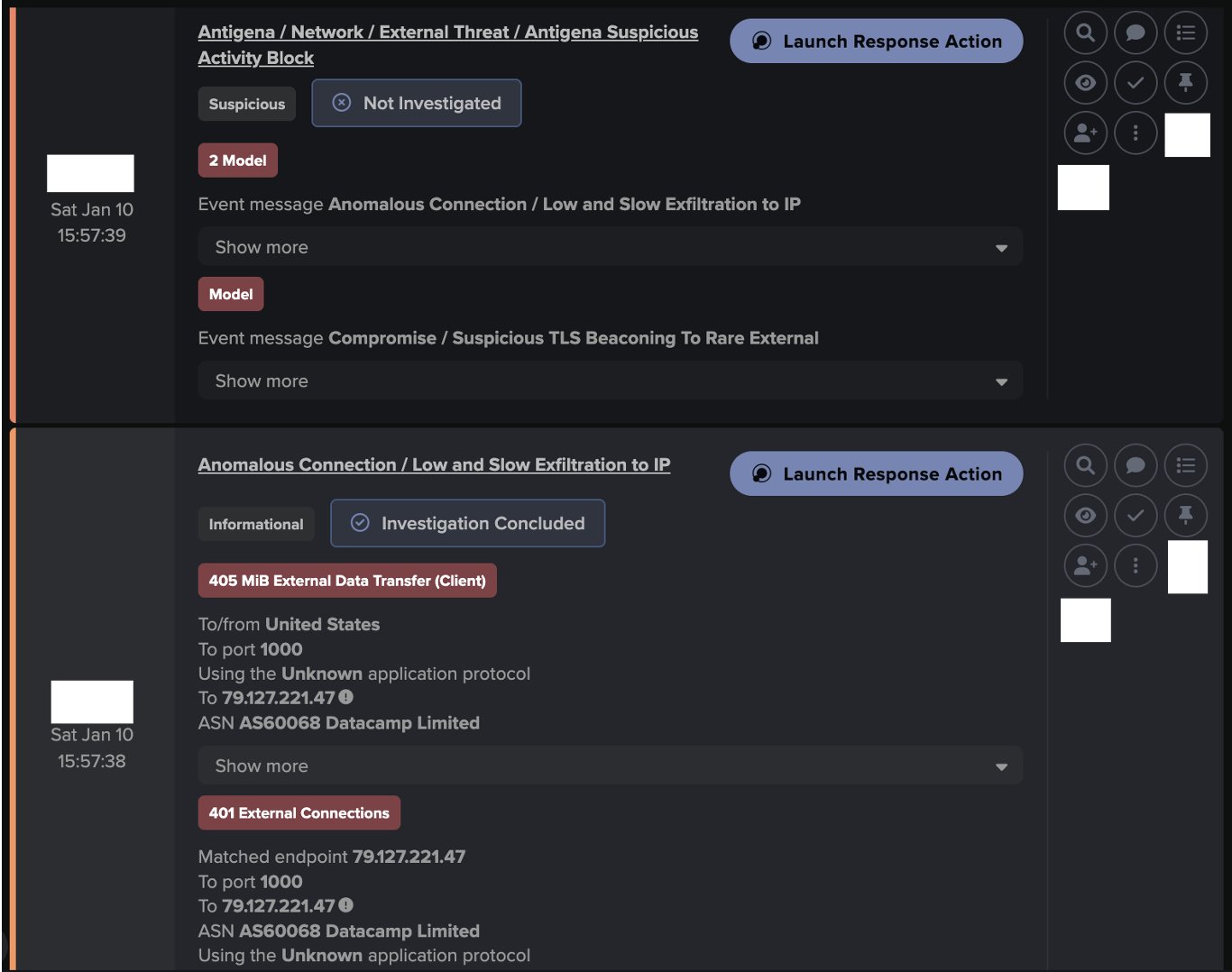
![Initial Beaconing to Young Endpoint alert behavior, involving the known tunnel/proxy endpoint ‘79.127.221[.]47’.](https://cdn.prod.website-files.com/626ff4d25aca2edf4325ff97/6a0b527a7ecc78423d4fdbc6_Screenshot%202026-05-18%20at%2010.55.03%E2%80%AFAM.png)
![Darktrace observed TLS beaconing alerts to the known trojanized installer, update[.]7zip[.]com · 98.96.229[.]19, over port 443 on January 7th.](https://cdn.prod.website-files.com/626ff4d25aca2edf4325ff97/6a0b529557224d073e49becd_Screenshot%202026-05-18%20at%2010.55.29%E2%80%AFAM.png)
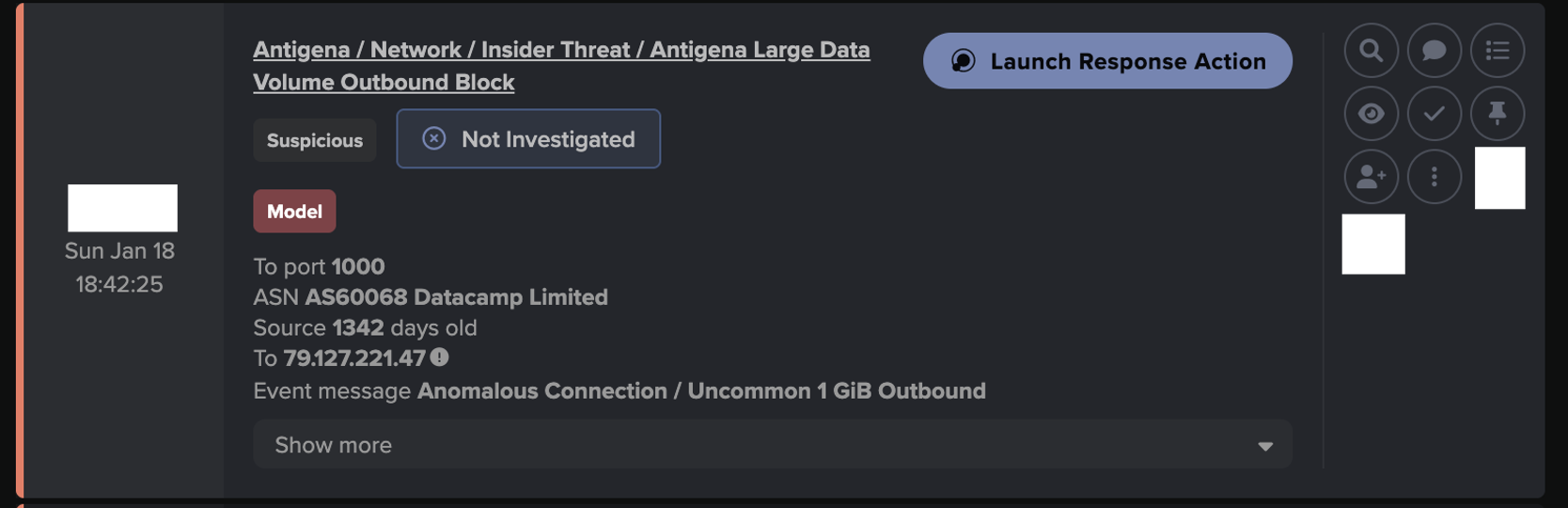
![On January 8th, Darktrace observed SSL beaconing to a rare destination which was attributed to a known ‘config/control domain’, nova[.]smshero[.]ai.](https://cdn.prod.website-files.com/626ff4d25aca2edf4325ff97/6a0b52ca6bdc2e2e6451446a_Screenshot%202026-05-18%20at%2010.56.22%E2%80%AFAM.png)
![Darktrace later observed continued beaconing alerts over a 4-day interval to additional rare destinations attributed to a known ‘config/control domain’, zest[.]hero-sms[.]ai & glide[.]smshero[.]cc.](https://cdn.prod.website-files.com/626ff4d25aca2edf4325ff97/6a0b52eed2e7185a03c382e7_Screenshot%202026-05-18%20at%2010.56.59%E2%80%AFAM.png)