One of the greatest issues in security is how to deal with high-stress scenarios when there is a significant breach, and there is too much to do in too little time. The nightmare scenario for any CISO is when this happens during a critical moment for the organization: an important acquisition, a crucial news announcement, or in this case, a global sporting event attracting an audience of millions.
Threat actors often exploit the pressure of these events to cause disruption or extract hefty sums. Sporting occasions, especially Formula 1 races, the Super Bowl, and the Olympics, attract a great deal of criminal interest.
The games begin
There have been several recorded attacks and data breaches at the Olympics this year, including an incident when a volleyball commentator asked his colleague for his computer password – not realizing he was still on air.
In a more nefarious case discovered by Darktrace, a Raspberry Pi device was covertly implanted into a national sporting body directly involved in the Olympics, in an attempt to exfiltrate sensitive data. The events took place one week before the start of the Games, and a data breach at this time would have had significant ramifications for the reputation of the organization, the confidentiality of their plans, and potentially the safety of their athletes.
Darktrace AI recognized this activity as malicious given its evolving understanding of ‘self’ for the organization, and Antigena – Darktrace’s autonomous response capability – took action at machine speed to interrupt the threat, affording the human security team the critical time they needed to catch up and neutralize the attack.
In what follows, we break down the attack.

Figure 1: The overall dwell time was three days.
Breaking down the attack
July 15, 14:09 — Initial intrusion
An unauthorized Raspberry Pi device connected to the organization’s digital environment – disguised and named in a way which mimicked the corporate naming convention. As a small IoT device, Raspberry Pis can be easily hidden and are difficult to locate physically in large environments. They have been used in various high-profile hacks in the past including the 2018 NASA breach.
IoT devices – from printers to fish tanks – pose a serious risk to security, as they can be exploited to gather information, move laterally, and escalate privileges.
July 15, 15:25 — External VPN activity
Anomalous UDP connections were made to an external endpoint over port 1194 (Open VPN activity). URIs showed that the device downloaded data potentially associated with Open VPN configuration files. This could represent an attempt to establish a secure channel for malicious activity such as data exfiltration.
By establishing an outgoing VPN, the attacker obfuscated their activity and bypassed the organization’s signature-based security, which could not detect the encrypted traffic. Antigena immediately blocked the suspicious connectivity, regardless of the encryption, identifying that the activity was a deviation from the ‘pattern of life’ for new devices.
July 15, 16:04 — Possible C2 activity
The Raspberry Pi soon began making repeated HTTP connections to a new external endpoint and downloaded octet streams — arbitrary binary data. It seems the activity was initiated by a standalone software process as opposed to a web browser.
Darktrace revealed that the device was performing an unusual external data transfer to the same endpoint, uploading 7.5 MB which likely contained call home data about the new location and name of the device.
July 15, 16:41 — Internal reconnaissance
The device engaged in TCP scanning across three unique internal IP addresses over a wide range of ports. Although the network scan only targeted three internal servers, the activity was identified by Darktrace as a suspicious increase in internal connections and failed internal connections.
Antigena instantly stopped the Raspberry Pi from making internal connections over the ports involved in the scanning activity, as well as enforcing the device’s ‘pattern of life’.

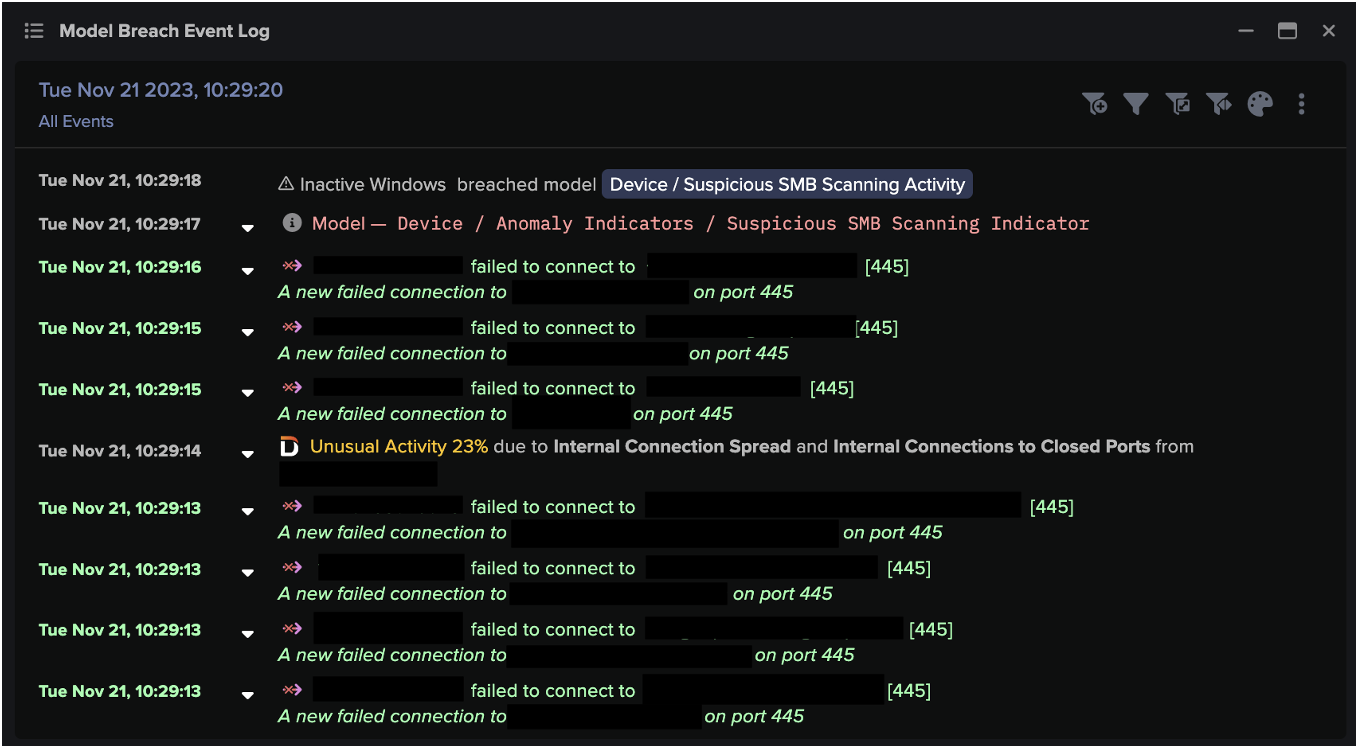
Figure 2: Device event log showing the components which enable Darktrace to detect network scanning.
July 15, 18:14 — Multiple internal reconnaissance tactics
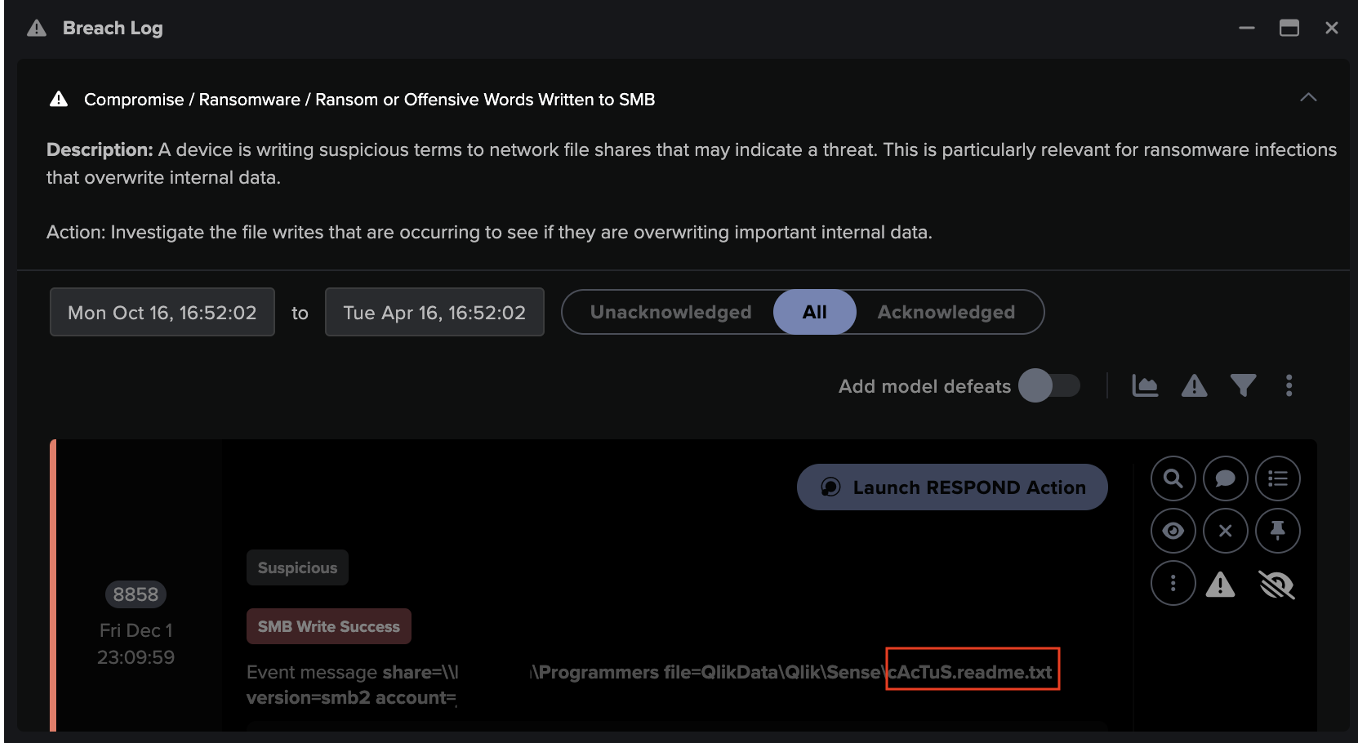
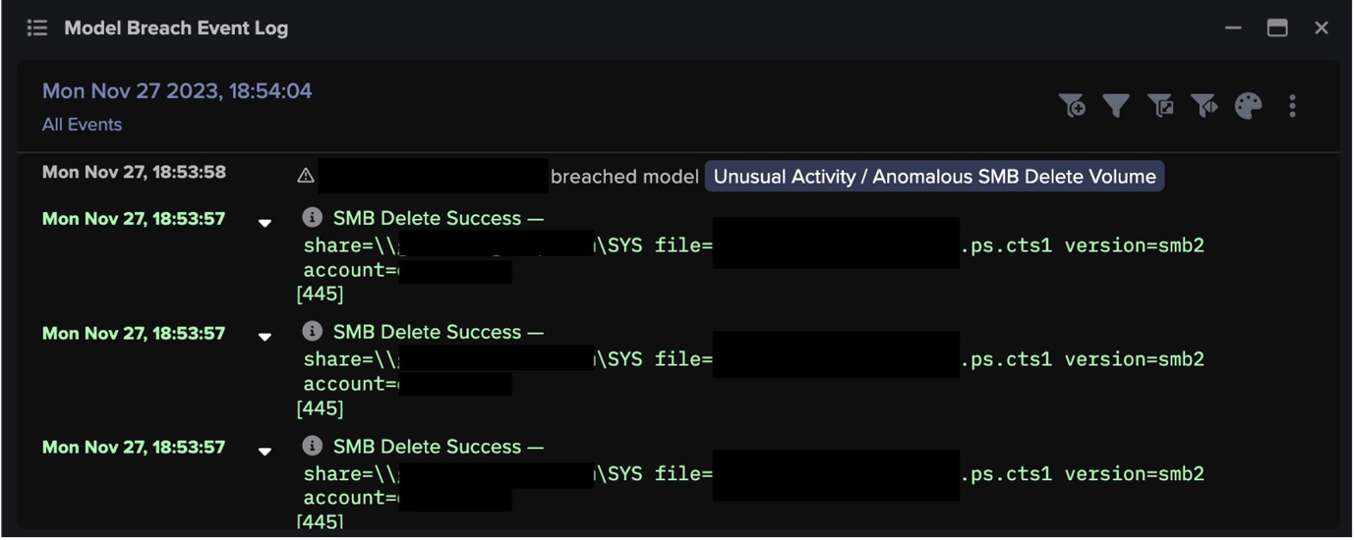
The Raspberry Pi then scanned a large number of devices on SMB port 445 and engaged in suspicious use of the outdated SMB version 1 protocol, suggesting more in-depth reconnaissance to find exploitable vulnerabilities.
Reacting to the scanning activity alongside the insecure protocol SMBv1, Antigena blocked connections from the source device to the destination IPs for one hour.
Four minutes later, the device engaged in connections to the open-source vulnerability scanner, Nmap. Nmap can be used legitimately for vulnerability scanning and so often is not alerted to by traditional security tools. However, Darktrace’s AI detected that the use of the tool was highly anomalous, and so blocked all outgoing traffic for ten minutes.
July 15, 22:03 — Final reconnaissance
Three hours later, the Raspberry Pi initiated another network scan across six unique external IPs – this was in preparation for the final data exfiltration. Antigena responded with instant, specific blocks to the external IPs which the device was attempting to connect to – before any data could be exfiltrated.
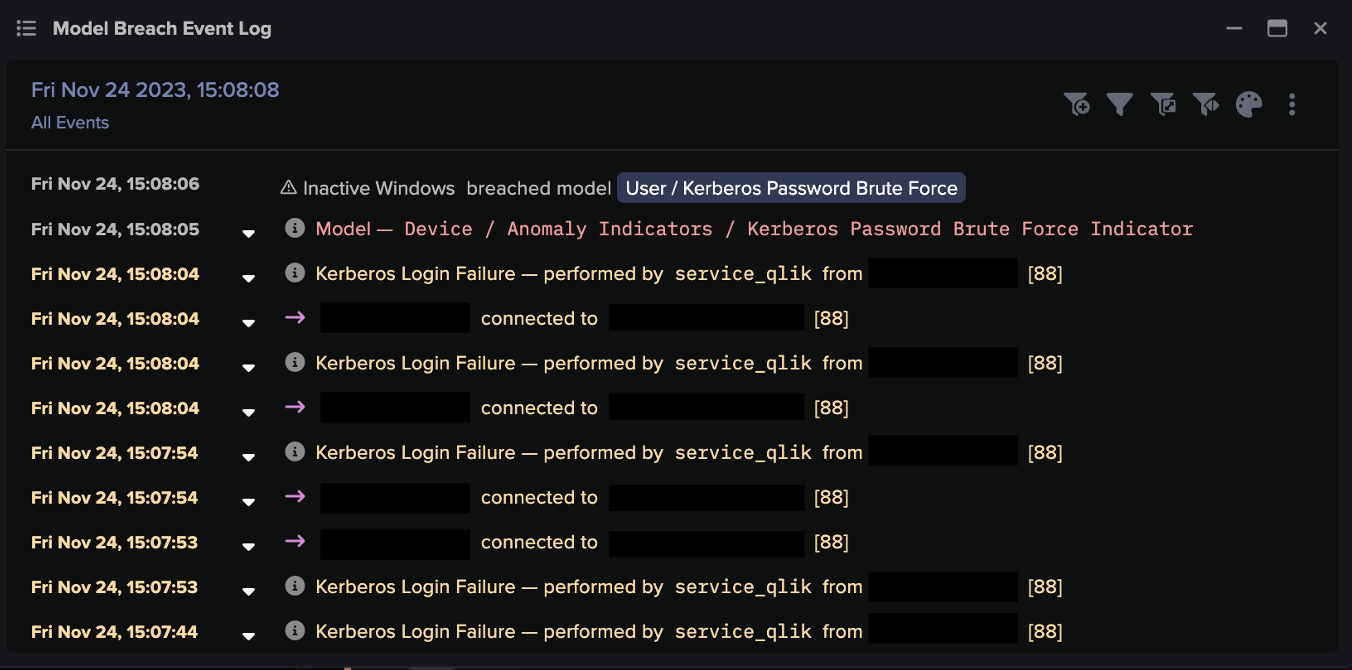
After 30 minutes, Darktrace detected bruteforcing activity from the Raspberry Pi using the SMB and NTLM authentication protocols. The device made a large number of failed login attempts to a single internal device using over 100 unique user accounts. Antigena blocked the activity, successfully stopping another wave of attempted SMB lateral movement.
By this stage, Antigena had bought the security team enough time to respond. The team applied an Antigena quarantine rule (the most severe action Antigena can take) to the Raspberry Pi, until they were able to find the physical location of the device and unplug it from the network.
How AI Analyst stitched together the incident
Cyber AI Analyst autonomously reported on three key moments of the attack:
- Unusual External Data Transfer
- Possible HTTP Command and Control
- TCP Scanning of Multiple Devices (the attempted data exfiltration)
It tied together activities over the span of multiple days, which could have been easily missed by human analysis. The AI provided crucial pieces of information, including the extent of the scanning activity. Such insights are time-consuming to calculate manually.

Figure 3: A screenshot from Cyber AI Analyst summarizing potential C2 activity.
Autonomous Response
Antigena took targeted action throughout to neutralize the suspicious behavior, while allowing normal business operations to continue unhindered.
Rather than widespread blocking, Antigena implemented a range of nuanced responses depending on the situation, always taking the smallest action necessary to deal with the threat.

Figure 4: Darktrace’s UI reveals the attempted network reconnaissance, and Antigena actions a targeted response. All IP addresses have been randomized.
Raspberry Pi: IoT threats
In an event involving 206 countries and 11,000 athletes, facing attacks from hacktivists, criminal groups, and nation states, with many broadcasters working remotely and millions watching from home, organizations involved in the Olympics needed a security solution which could rise to the occasion.
Even with the largest affairs, threats can come from the smallest places. The ability to detect unauthorized IoT devices and maintain visibility over all activity in your digital estate is essential.
Autonomous Response protects against the unexpected, stopping malicious activity at machine speed without any user input. This is necessary for rapid response and remediation, especially for resource-stretched internal security teams. When it comes to defending systems and outpacing attackers, AI always wins the race.
Thanks to Darktrace analysts Emma Foulger and Greg Chapman for their insights on the above threat find.
Learn how two rogue Raspberry Pi devices infected a healthcare provider
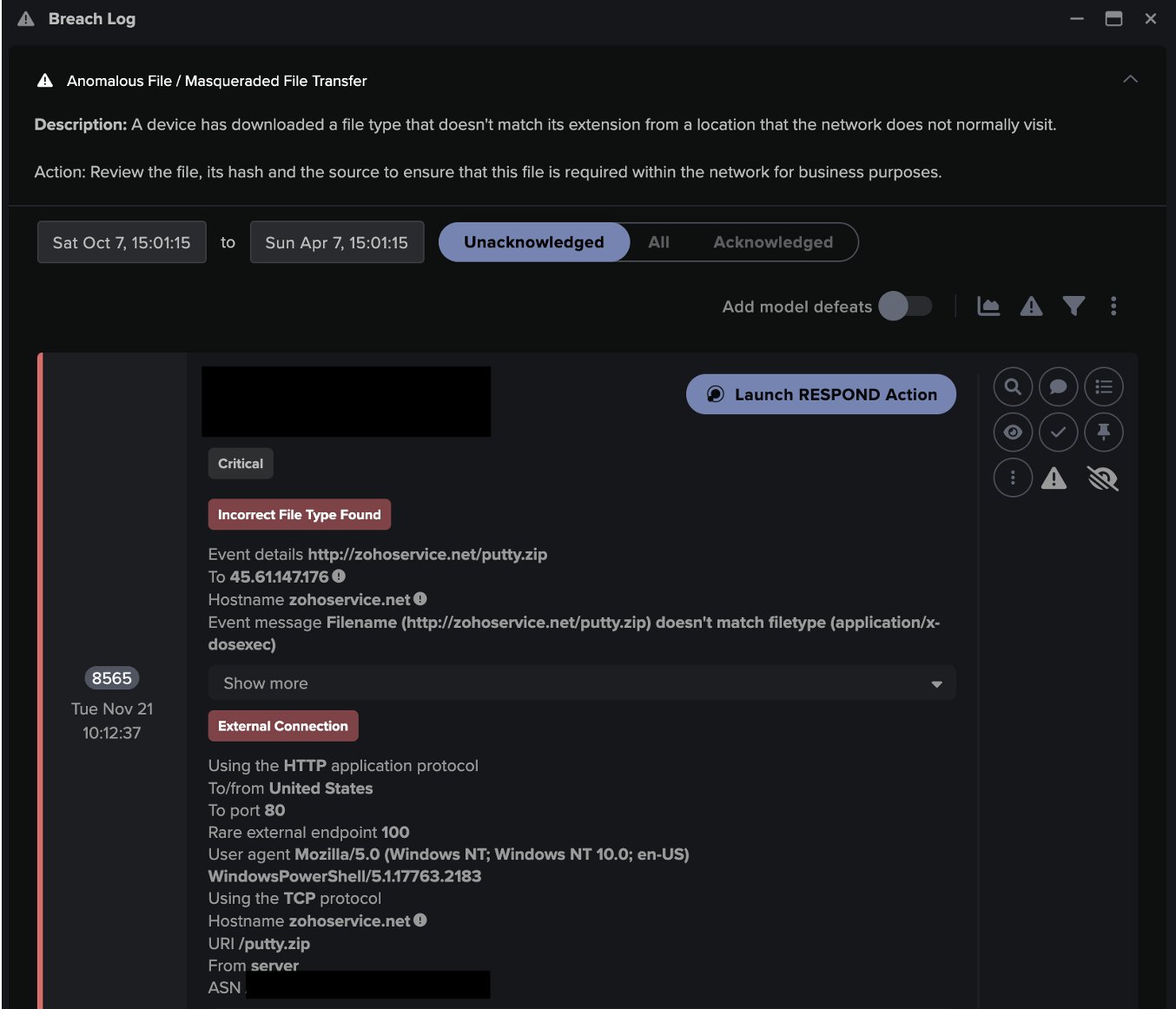
Darktrace model detections:
- Compromise / Ransomware / Suspicious SMB Activity
- Tags / New Raspberry Pi Device
- Device / Network Scan
- Unusual Activity / Unusual Raspberry Pi Activity
- Antigena / Network / Insider Threat / Antigena Network Scan Block
- Device / Suspicious Network Scan Activity
- Antigena / Network / Significant Anomaly / Antigena Significant Anomaly from Client Block
- Antigena / Network / Significant Anomaly / Antigena Controlled and Model Breach
- Device / Suspicious SMB Scanning Activity
- Antigena / Network / Significant Anomaly / Antigena Breaches Over Time Block
- Device / Attack and Recon Tools
- Device / New Device with Attack Tools
- Device / Anomalous Nmap Activity
- Device / External Network Scan
- Device / SMB Session Bruteforce
- Antigena / Network / Manual / Block All Outgoing Connections
































![Cyber AI Analyst Incident Log showing the offending device making over 1,000 connections to the suspicious hostname “zohoservice[.]net” over port 8383, within a specific period.](https://assets-global.website-files.com/626ff4d25aca2edf4325ff97/662971c1cf09890fd46729a1_Screenshot%202024-04-24%20at%201.55.10%20PM.png)