First observed in 2015, LeChiffre ransomware works by encrypting files and changing their extensions to .lechiffre (translated as ‘cipher’ in French). Unlike other variants of malware, hackers must run LeChiffre manually on a compromised system. Cyber-criminals automatically scan networks in search of poorly secured desktops, and then log in remotely and manually run an instance of the virus.
To profit from the current wave — and success — of ransomware, many low-level threat groups are using mutations of known ransomware. Despite the multiple recovery tools available online, LeChiffre remains a persistent and highly disruptive threat across all industries, with new mutations enabling it to bypass many legacy security solutions.
Recent activity in a Darktrace customer environment
Darktrace recently discovered a resurgence of LeChiffre ransomware whilst deployed in the network of a wholesale distributor in the US.
Over the course of a week, several devices were seen making HTTP requests for Mimikatz Powershell script, then authenticating with administrative credentials for the first time. The infected devices then exhibited network scanning activity on port 445. Shortly after, the devices began writing multiple files (svcctl, PsExec) over SMB to hidden file shares on multiple other devices.
The activity took place early on a Sunday morning, when the security team wasn’t closely monitoring the network and didn’t have eyes on the activity. However, Darktrace’s AI detected the highly suspicious activity in real time, monitoring 19.7k of SMB move successes, with .LEV62C_LeChiffre extension and almost 38.8k of SMB write successes with LEV62C_LeChiffre_ReadMe.txt — the ransom note.
This threatening activity escaped detection from the rest of the organization’s security stack, likely due to the fact that the download of the Mimikatz Powershell script was from a redirected, legitimate domain - githubusercontent[.]com. The use of this legitimate domain allowed it to go unnoticed by firewall and endpoint detection, while this particular variant of the LeChiffre malware was not yet recognized by signature-based tools.
However, with a continuously updating understanding of what constitutes ‘normal’ behavior for every network and device in an organization, Darktrace’s AI quickly detected the unusual activity and flagged it as highly threatening. The Cyber AI Analyst then fully investigated the attack, autonomously connecting the dots and surfacing the five stages of the attack chain ready for incident review. This greatly reduced the incident response time for the security team, who were able to isolate the infected devices and quickly take them offline.
A sample of the AI Analyst report of the SMB file encryption is shown below.
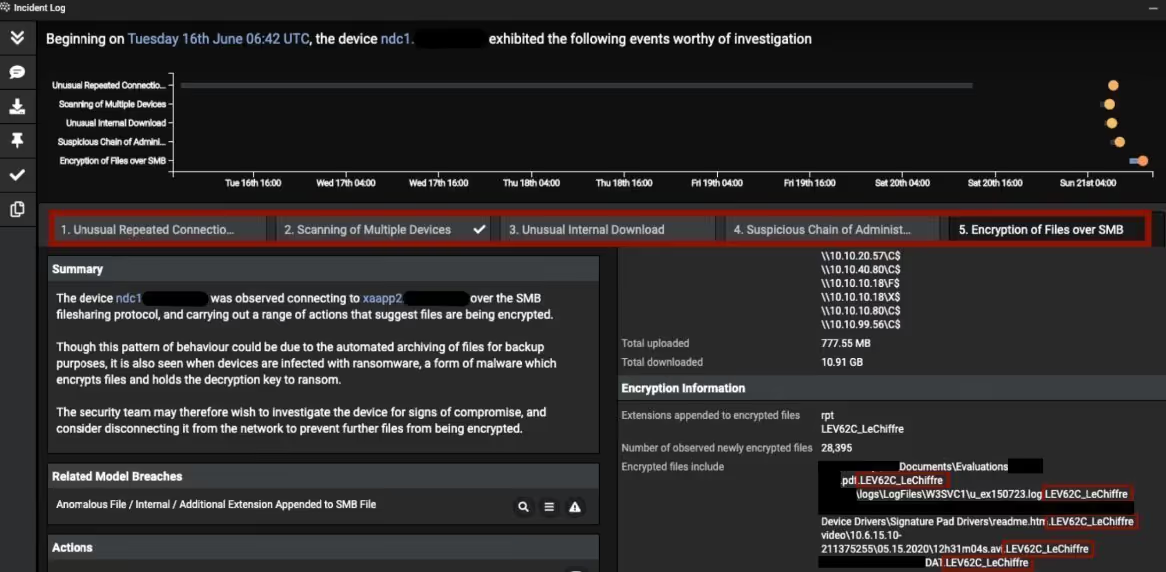
Figure 1: Darktrace’s Cyber AI Analyst autonomously investigates the attack
Overview of infected device
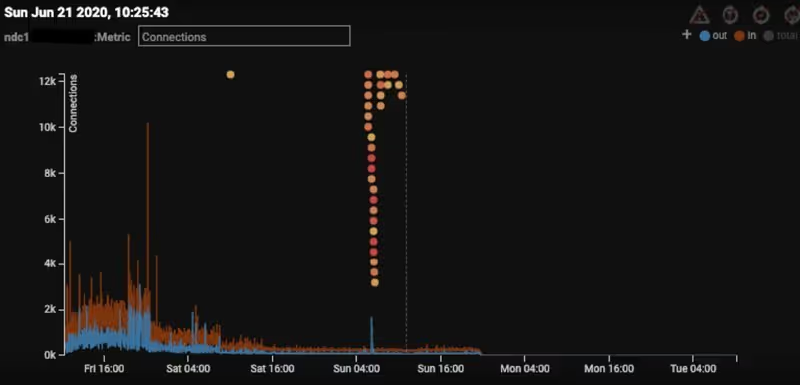
Figure 2: The graph showing the Darktrace detections cluster on June 21
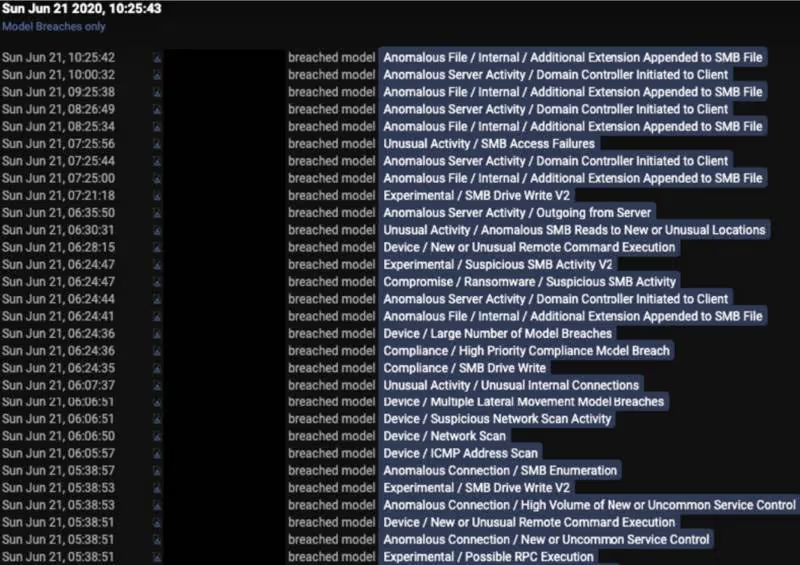
Figure 3: The device event log showing the list of model breaches on June 21
Machine-speed attacks require machine-speed response
This incident happened while the customer was participating in Darktrace’s free 30-day Proof of Value. Had Darktrace’s Autonomous Response technology, Antigena, been enabled, the AI would have responded immediately, taking action when the malware attempted lateral movement to prevent the breach device from carrying out encryption. Even without Antigena, Darktrace’s real-time detection and AI-powered investigation enabled the security team to quickly de-escalate the compromise.
The barrier to entry has been significantly lowered by the commoditization of malware. Many forms of ransomware are easily available to low-level threat actors via Darknet purchases, and minor changes made by cyber-criminals can easily enable the attacks to go undetected by most security tools. Now even low-skilled threat actors have the potential to cause significant damage and evade the traditional security stack.
The events described above demonstrate that ransomware continues to present a very real threat across multiple industries. And with ransomware capable of encrypting files across hundreds of devices in minutes, the need for machine-speed response is more important than ever. Darktrace Antigena enables security teams to get ahead of a threat by autonomously responding to threatening activity, taking devices offline or enforcing their ‘pattern of life’ to keep businesses operational.
Thanks to Darktrace analyst Fiona Goh for her insights on the above threat find.
Learn more about Autonomous Response
IoCs:
IoCCommentLEV62C_LeChiffre_ReadMe.txtRansom note.LEV62C_LeChiffreSuccessful SMB move with LeChiffre encryption extension
Darktrace model detections:
- Compromise / Ransomware / Suspicious SMB Activity
- Device / Multiple Lateral Movement Model Breaches
- Device / Large Number of Model Breaches
- Anomalous File / Internal / Additional Extension Appended to SMB File
- Device / New or Unusual Remote Command Execution
- Anomalous Connection / High Volume of New or Uncommon Service Control
- Anomalous Connection / SMB Enumeration
- Device / Suspicious Network Scan Activity
- Device / Network Scan
- Compliance / SMB Drive Write
- Unusual Activity / SMB Access Failures
- Experimental / Default Credential Usage V3


































