Hybrid environments demand end-to-end visibility to stop modern attacks
Hybrid environments are a dominant trend in enterprise technology, but they continue to present unique issues to the defenders tasked with securing them. By 2026, Gartner predicts that 75% of organizations will adopt hybrid cloud strategies [1]. At the same time, only 23% of organizations report full visibility across cloud environments [2].
That means a strong majority of organizations do not have comprehensive visibility across both their on-premises and cloud networks. As a result, organizations are facing major challenges in achieving visibility and security in hybrid environments. These silos and fragmented security postures become a major problem when considering how attacks can move between different domains, exploiting the gaps.
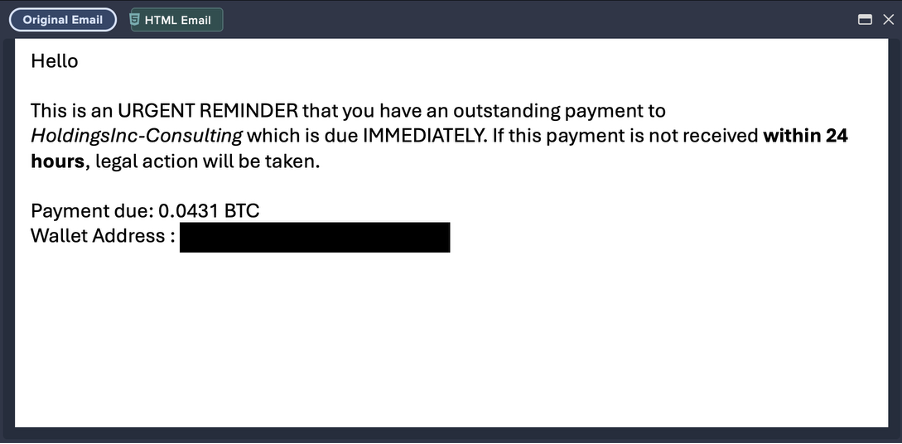
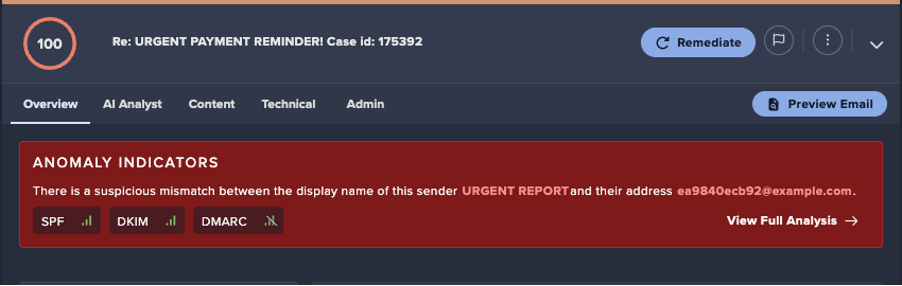
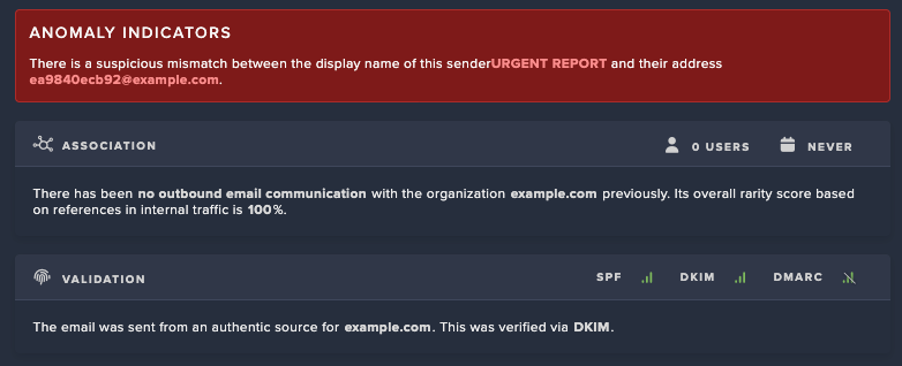
For example, an attack may start with a phishing email, leading to the compromise of a cloud-based application identity and then moving between the cloud and network to exfiltrate data. Some attack types inherently involve multiple domains, like lateral movement and supply chain attacks, which target both on-premises and cloud networks.
Given this, unified visibility is essential for security teams to reduce blind spots and detect threats across the entire attack surface.
Risks of fragmented visibility
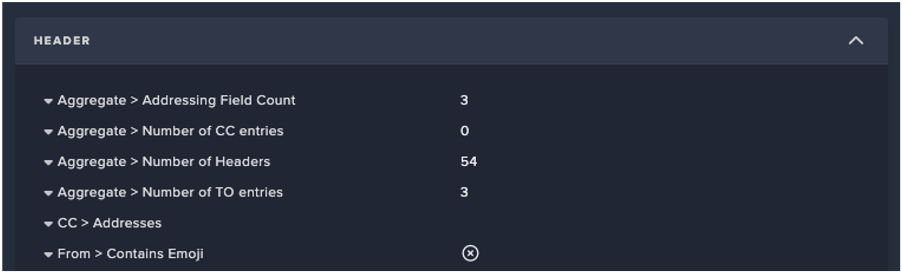
Silos arise due to separate teams and tools managing on-premises and cloud environments. Many teams have a hand in cloud security, with some common ones including security, infrastructure, DevOps, compliance, and end users, and these teams can all use different tools. This fragmentation increases the likelihood of inconsistent policies, duplicate alerts, and missed threats. And that’s just within the cloud, not even considering the additional defenses involved with network security.
Without a unified security strategy, gaps between these infrastructures and the teams which manage them can leave organizations vulnerable to cyber-attacks. The lack of visibility between on-premises and cloud environments contributes to missed threats and delayed incident response. In fact, breaches involving stolen or compromised credentials take an average of 292 to identify and contain [3]. That’s almost ten months.
The risk of fragmented visibility runs especially high as companies undergo cloud migrations. As organizations transition to cloud environments, they still have much of their data in on-premises networks, meaning that maintaining visibility across both on-premises and cloud environments is essential for securing critical assets and ensuring seamless operations.
Unified visibility is the solution
Unified visibility is achieved by having a single-pane-of-glass view to monitor both on-premises and cloud environments. This type of view brings many benefits, including streamlined detection, faster response times, and reduced complexity.
This can only be accomplished through integrations or interactions between the teams and tools involved with both on-premises security and cloud security.
AI-driven platforms, like Darktrace, are especially well equipped to enable the real-time monitoring and insights needed to sustain unified visibility. This is because they can handle the large amounts of data and data types.
Darktrace accomplishes this by plugging into an organization’s infrastructure so the AI can ingest and analyze data and its interactions within the environment to form an understanding of the organization’s normal behavior, right down to the granular details of specific users and devices. The system continually revises its understanding about what is normal based on evolving evidence.
This dynamic understanding of normal means that the AI engine can identify, with a high degree of precision, events or behaviors that are both anomalous and unlikely to be benign. This helps reduce noise while surfacing real threats, across cloud and on-prem environments without manual tuning.
In this way, given its versatile AI-based, platform approach, Darktrace empowers security teams with real-time monitoring and insights across both the network and cloud.
Unified visibility in the modern threat landscape
As part of the Darktrace ActiveAI Security Platform™, Darktrace / CLOUD works continuously across public, private, hybrid, and multi-cloud deployments. With real-time Cloud Asset Enumeration and Dynamic Architecture Modeling, Darktrace / CLOUD generates up-to-date architecture diagrams, giving SecOps and DevOps teams a unified view of cloud infrastructures.
It is always on the lookout for changes, driven by user and service activity. For example, unusual user activity can significantly raise the asset’s score, prompting Darktrace’s AI to update its architectural view and keep a living record of the cloud’s ever-changing landscape, providing near real-time insights into what’s happening.
This continuous architectural awareness ensures that security teams have a real-time understanding of cloud behavior and not just a static snapshot.
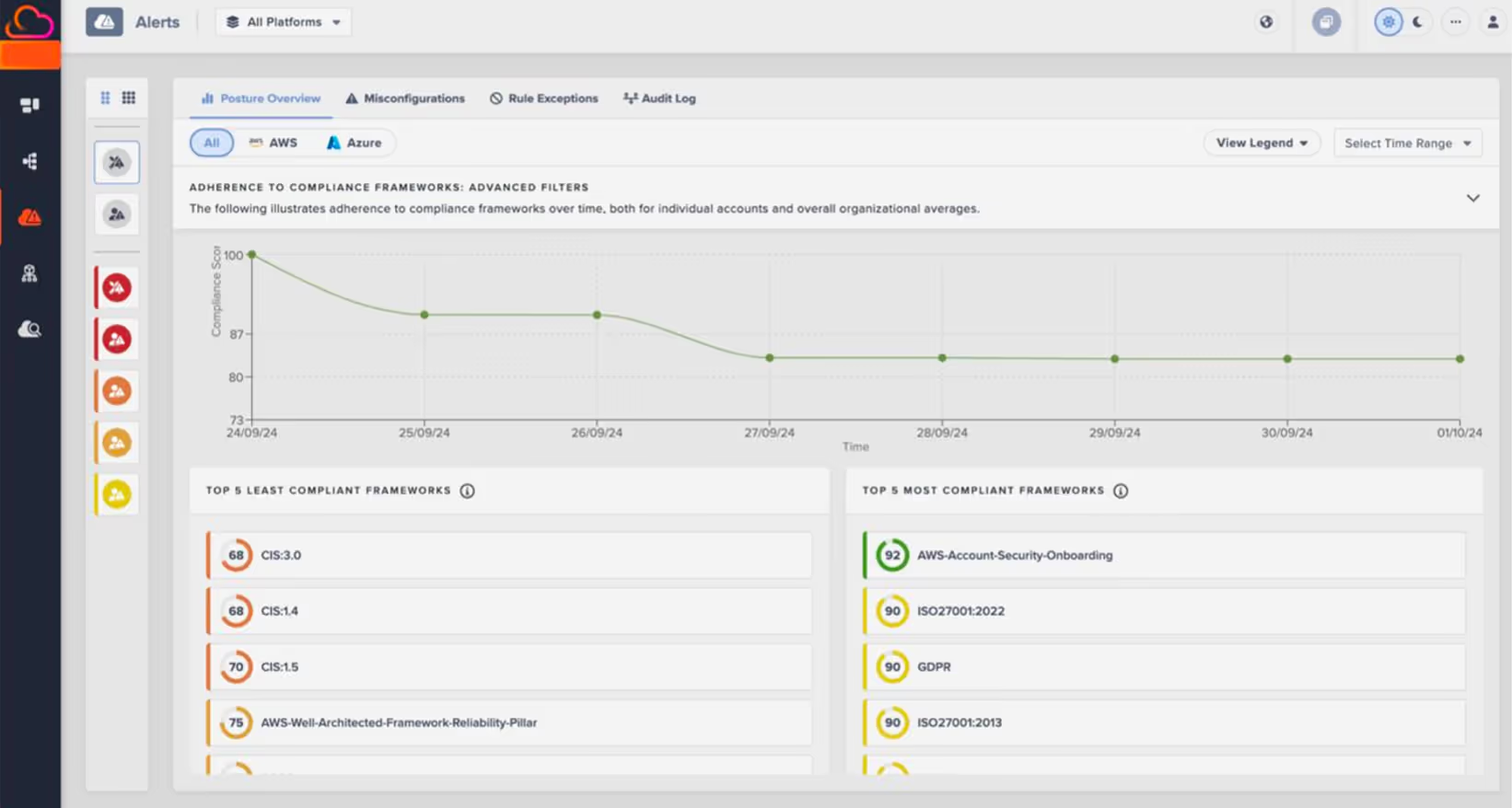
With this dynamic cloud visibility and monitoring, Darktrace / CLOUD can help unify and secure environments.
Real world example: Remote access supply chain attacks
Sectop Remote Access Trojan (RAT) malware, also known as ‘ArchClient2,’ is a .NET RAT that contains information stealing capabilities and allows threat actors to monitor and control targeted computers. It is commonly distributed through drive-by downloads of illegitimate software via malvertizing.
Darktrace has been able to detect and respond to Sectop RAT attacks using unified visibility and platform-wide coverage. In one such example, Darktrace observed one device making various suspicious connections to unusual endpoints, likely in an attempt to receive C2 information, perform beaconing activity, and exfiltrate data to the cloud.
This type of supply chain attack can jump from the network to the cloud, so a unified view of both environments helps shorten detection and response times, therefore mitigating potential impact. Darktrace’s ability to detect these cross-domain behaviors stems from its AI-driven, platform-native visibility.
Conclusion
Organizations need unified visibility to secure complex, hybrid environments effectively against threats and attacks. To achieve this type of comprehensive visibility, the gaps between legacy security tools across on-premises and cloud networks can be bridged with platform tools that use AI to boost data analysis for highly accurate behavioral prediction and anomaly detection.
Read more about the latest trends in cloud security in the blog “Protecting Your Hybrid Cloud: The Future of Cloud Security in 2025 and Beyond.”
References:
1. Gartner, May 22, 2023, “10 Strategic Data and Analytics Predictions Through 2028”
2. Cloud Security Alliance, February 14, 2024, “Cloud Security Alliance Survey Finds 77% of Respondents Feel Unprepared to Deal with Security Threats”
3. IBM, “Cost of a Data Breach Report 2024”
Darktrace / CLOUD Solution Brief
Discover how advanced AI solutions like Darktrace / CLOUD can help unify and secure your hybrid environment in the solution brief.
.avif)




















.avif)







.jpg)