Tracking CVEs isn’t enough: Why context is critical
Vulnerabilities are weaknesses in a system that can be exploited by malicious actors to gain unauthorized access or to disrupt normal operations. Common Vulnerabilities and Exposures (or CVEs) are a list of publicly disclosed cybersecurity vulnerabilities that can be tracked and mitigated by the security community.
When a vulnerability is discovered, the standard practice is to report it to the vendor or the responsible organization, allowing them to develop and distribute a patch or fix before the details are made public. This is known as responsible disclosure.
With a record-breaking 40,000 CVEs reported for 2024 and a predicted higher number for 2025 by the Forum for Incident Response and Security Teams (FIRST) [1], anomaly-detection is essential for identifying these potential risks. The gap between exploitation of a zero-day and disclosure of the vulnerability can sometimes be considerable, and retroactively attempting to identify successful exploitation on your network can be challenging, particularly if taking a signature-based approach.
Detecting threats without relying on CVE disclosure
Abnormal behaviors in networks or systems, such as unusual login patterns or data transfers, can indicate attempted cyber-attacks, insider threats, or compromised systems. Since Darktrace does not rely on rules or signatures, it can detect malicious activity that is anomalous even without full context of the specific device or asset in question.
For example, during the Fortinet exploitation late last year, the Darktrace Threat Research team were investigating a different Fortinet vulnerability, namely CVE 2024-23113, for exploitation when Mandiant released a security advisory around CVE 2024-47575, which aligned closely with Darktrace’s findings.
Retrospective analysis like this is used by Darktrace’s threat researchers to better understand detections across the threat landscape and to add additional context.
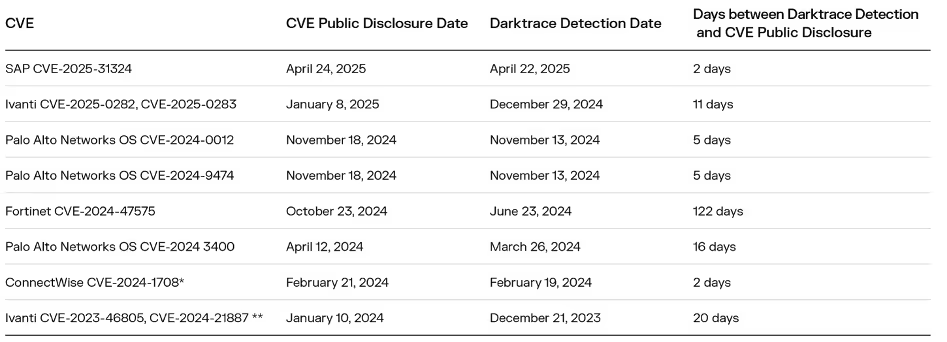
Below are ten examples from the past year where Darktrace detected malicious activity days or even weeks before a vulnerability was publicly disclosed.
Trends in pre-CVE exploitation
Often, the disclosure of an exploited vulnerability can be off the back of an incident response investigation related to a compromise by an advanced threat actor using a zero-day. Once the vulnerability is registered and publicly disclosed as having been exploited, it can kick off a race between the attacker and defender: attack vs patch.
Nation-state actors, highly skilled with significant resources, are known to use a range of capabilities to achieve their target, including zero-day use. Often, pre-CVE activity is “low and slow”, last for months with high operational security. After CVE disclosure, the barriers to entry lower, allowing less skilled and less resourced attackers, like some ransomware gangs, to exploit the vulnerability and cause harm. This is why two distinct types of activity are often seen: pre and post disclosure of an exploited vulnerability.
Darktrace saw this consistent story line play out during several of the Fortinet and PAN OS threat actor campaigns highlighted above last year, where nation-state actors were seen exploiting vulnerabilities first, followed by ransomware gangs impacting organizations [2].
The same applies with the recent SAP Netweaver exploitations being tied to a China based threat actor earlier this spring with subsequent ransomware incidents being observed [3].
Autonomous response
Anomaly-based detection offers the benefit of identifying malicious activity even before a CVE is disclosed; however, security teams still need to quickly contain and isolate the activity.
For example, during the Ivanti chaining exploitation in the early part of 2025, a customer had Darktrace’s Autonomous Response capability enabled on their network. As a result, Darktrace was able to contain the compromise and shut down any ongoing suspicious connectivity by blocking internal connections and enforcing a “pattern of life” on the affected device.
This pre-CVE detection and response by Darktrace occurred 11 days before any public disclosure, demonstrating the value of an anomaly-based approach.
In some cases, customers have even reported that Darktrace stopped malicious exploitation of devices several days before a public disclosure of a vulnerability.
For example, During the ConnectWise exploitation, a customer informed the team that Darktrace had detected malicious software being installed via remote access. Upon further investigation, four servers were found to be impacted, while Autonomous Response had blocked outbound connections and enforced patterns of life on impacted devices.
Beyond signatures: Spotting anomalies before CVEs
By continuously analyzing behavioral patterns, systems can spot unusual activities and patterns from users, systems, and networks to detect anomalies that could signify a security breach.
Through ongoing monitoring and learning from these behaviors, anomaly-based security systems can detect threats that traditional signature-based solutions might miss, while also providing detailed insights into threat tactics, techniques, and procedures (TTPs). This type of behavioral intelligence supports pre-CVE detection, allows for a more adaptive security posture, and enables systems to evolve with the ever-changing threat landscape.
Darktrace's Self-Learning AI Approach
As leaders in cybersecurity AI for over a decade, Darktrace has the expertise to effectively integrate the right AI for optimal results. Darktrace’s Self-Learning AI uses a multi-layered AI approach, learning your unique organization to detect and respond to malicious activity before vulnerabilities are publicly known, often days or even weeks in advance.
By strategically integrating a diverse set of AI techniques, such as machine learning, deep learning, LLMs, and natural language processing, both sequentially and hierarchically, Darktrace's multi-layered AI approach provides a robust defense mechanism that is unique to your organization and adapts to the evolving threat landscape.
Techniques such as Bayesian learning and behavioral clustering allow Darktrace to evaluate different models adaptively, ensuring an accurate understanding of entity behavior. This layer applies behavioral analysis to detect patterns across similar entities and helps predict behaviors, even with sparse data from specific devices or systems. The AI continuously adjusts its frame of reference to remain effective in dynamic environments.
To learn more about Darktrace's AI, read our AI Arsenal White Paper where we break down the different applications of AI in cybersecurity.
[related-resource]
References and further reading:
- https://www.first.org/blog/20250607-Vulnerability-Forecast-for-2025
- https://cloud.google.com/blog/topics/threat-intelligence/fortimanager-zero-day-exploitation-cve-2024-47575
- https://thehackernews.com/2025/05/china-linked-hackers-exploit-sap-and.html
Related Darktrace blogs:
- SAP CVE 2025 31324
- Ivanti CVE-2025-0282 CVE-2025-0283
- Palo Alto OS CVE 2024-0012 & CVE 2024-9474
- Fortinet CVE 2024-47575
- Palo Alto Networks OS– CVE 2024 3400
- ConnectWise CVE-2024-1708
- Ivanti CVE-2023-46805, CVE-2024-21887
*Self-reported by customer, confirmed afterwards.
**Updated January 2024 blog now reflects current findings
This report explores the latest trends shaping the cybersecurity landscape and what defenders need to know in 2026.
This report explores the latest trends shaping the cybersecurity landscape and what defenders need to know in 2026.
.png)






































.avif)




