As Industrial Control Systems (ICS) and traditional IT networks converge, the number of cyber-attacks that start in the corporate network before spreading to operational technology has increased dramatically in the last 12 months. From North Korean hackers targeting a nuclear power plant in India to ransomware shutting down operations at a US gas facility, and across Honda’s manufacturing sites, 2020 has been the year OT attacks have become mainstream.
Darktrace recently detected a simulation of a state-of-the-art attack at an international airport, identifying ICS reconnaissance, lateral movement, vulnerability scanning and protocol fuzzing – a technique in which the attacker sends nonsensical commands over an ICS communication channel in order to confuse the target device, causing it to fail or reboot.
Darktrace’s Industrial Immune System detected every stage of the sophisticated attack, using AI-powered anomaly detection to identify ICS attack vectors without a list of known exploits, company assets, or firmware versions. The attacker leveraged tools at every stage of the ICS kill chain, including ICS-specific attack techniques.
Any unusual attempts to read or reprogram single coils, objects, or other data blocks were detected by Cyber AI, and Darktrace’s Cyber AI Analyst also automatically identified the activity and created summary reports detailing the key actions taken.
The attack spanned multiple days and targeted the Building Management System (BMS) and the Baggage Reclaim network, with attackers utilizing two common ICS protocols (BacNet and S7Comm) and leveraging legitimate tools (such as ICS reprogramming commands and connections through SMB service pipes) to evade traditional, signature-based security tools.
Attack details

Figure 1: Timeline of the attack
In the first stage of the attack, a new device was introduced to the network, using ARP spoofing to evade detection from traditional security tools. At 11.40am, the attacker scanned a target device and attempted to bruteforce open services. Once the target device had been hijacked, the attacker then sought to establish an external connection to the Internet. External connections should not be possible in ICS networks, but attackers often seek to bypass firewalls and network segregation rules in order to create a command and control (C2) channel.

Figure 2: Darktrace Threat Tray 15 minutes after the pentest commenced. High level model breaches have already alerted the analyst team to the attack device.
The hijacked device then began performing ICS reconnaissance using Discover and Read commands. Darktrace identified new objects and data blocks being targeted as part of this reconnaissance, and detected ICS devices targeted with unusual BacNet and Siemens S7Comm protocol commands.
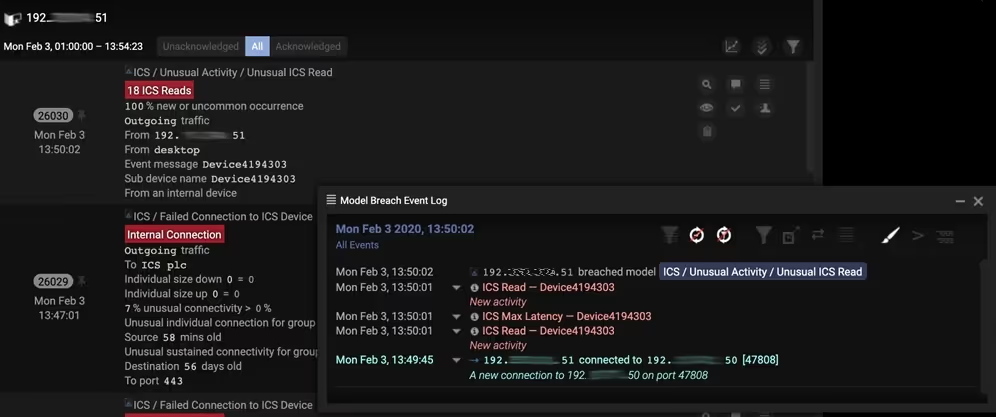
Figure 3: Model alerts associated with ICS reconnaissance over BacNet. Machine learning at the ICS command level detected new and unusual BacNet objects being targeted by the attacker.
The attacker enumerated through multiple ICS devices in order to perform lateral movement throughout the ICS system. Once they had learned device settings and configurations, they used ICS Reprogram and Write commands to reconfigure machines. The attacker attempted to use known vulnerabilities to exploit the target devices, such as the use of SMB, SMBv1, HTTP, RDP, and ICS protocol fuzzing.

Figure 4: Visualization of the device enumeration performed by the attacker against multiple ICS controllers. The attacker used ICS Discover commands as part of the initial reconnaissance.
The attacker took deliberate actions to evade the airport’s cyber security stack, including making connections using ICS protocols commonly used on the network to devices which commonly use those protocols. While legacy security tools failed to pick up on this activity, Darktrace’s deep packet inspection was able to identify unusual commands used by the attacker within those ‘normal’ connections.
The attacker used ARP spoofing to slow any investigation using asset management-based security tools – including two other solutions being trialed by the airport at the time of the attack. They also used multiple devices throughout the intrusion to throw defense teams off the scent.
Darktrace’s AI technology also launched an automated investigation into the incident. The Cyber AI Analyst identified all of the attack devices and produced summary reports for each, showcasing its ability to not only save crucial time for security teams, but bridge the skills gap between IT teams and ICS engineers.

Figure 5: The Cyber AI Analyst threat tray at the end of day 1. Both devices used by the attacker have been identified.
The Cyber AI Analyst immediately began investigating after the first model breach, and continued to stitch together disparate events across the network to produce a natural language summary of the incident, including recommendations for action.

Figure 6: AIA incident summary at the end of day 2, detailing the use of SMB exploits as part of the attack chain against one of the ICS devices.
Potential ramifications
Had the attack been allowed to continue, the attackers – potentially activist groups, terrorist organizations, and organized criminals – could have caused significant operational disruption to the airport. For example, the BMS is likely to manage temperature settings, the sprinkler system, fire alarms and fire exits, lighting, and doors in and out of secure access areas. Meddling with any one of these could cause severe disruption at an airport, with significant financial and reputational effects. Similarly, access to baggage reclaim networks could be used by criminals seeking to smuggle illegal goods or steal valuable cargo.
This simulation showcases the possibilities for an advanced cyber-criminal looking to compromise integrated IT and OT networks. The majority of leading ICS ‘security’ vendors are signature-based, and fail to pick up on novel techniques and utilization of common protocols to pursue malicious ends – this is why ICS attacks have continued to hit the headlines this year.
The incident showcases the extent of Cyber AI’s detections in a real-world ICS environment, and the level of detail Darktrace can provide following an attack. As Industrial Control Systems become increasingly integrated with the wider IT network, the importance of securing these critical systems is paramount. Darktrace provides a unified security umbrella with visibility and detection across the entire digital environment.
Thanks to Darktrace analyst Oakley Cox for his insights on the above investigation.
Learn more about the Industrial Immune System
Darktrace model detections:
- ICS / Unusual ICS Commands
- ICS / Multiple New Reprograms
- ICS / Multiple New Discover Commands
- ICS / Rare External from OT Device
- ICS / Uncommon ICS Protocol Warning
- ICS / Multiple Failed Connections to ICS Device
- ICS / Anomalous IT to ICS Connection



































