The challenge for CISOs
Despite continuous advances in security technologies, humans continue to be exploited by attackers. Credential abuse and social actions like phishing are major factors, accounting for around 60% of all breaches. These attacks rely less on technical vulnerabilities and more on exploiting human behavior and organizational processes.
From my perspective as a former CISO, protecting humans concentrates three of today’s most pressing challenges: the sheer volume of email-based threats, their increasing sophistication, and the limitations of traditional employee awareness programs in moving the needle on risk.
My personal experience of security awareness training as a CISO
With over 20 years’ experience as an ICT and Cybersecurity leader across various international organizations, I’ve seen security awareness training (SAT) in many guises. And while the cyber landscape is evolving in every direction, the effectiveness of SAT is reaching a plateau.
Most programs I’ve seen follow a familiar pattern. Training is delivered through a combination of eLearning modules and internal sessions designed to reinforce IT policies. Employees are typically required to complete a slide deck or video, followed by a multiple-choice quiz. Occasional phishing simulations are distributed throughout the year.
The content is often static and unpersonalized, based on known threats that may already be outdated. Every employee regardless of role or risk exposure receives the same training and the same simulated phishing templates, from front-desk staff to the CEO.
The problem with traditional SAT programs
The issue with the approach to SAT outlined above is that the distribution of power is imbalanced. Humans will always be fallible, particularly when faced with increasingly sophisticated attacks. Providing generic, low-context training risks creating false confidence rather than genuine resilience. Let’s look at some of the problems in detail.
Timing and delivery
Employees today operate under constant cognitive load, making lots of rapid decisions every day to reduce their email volumes. Yet if employees are completing training annually, or on an ad hoc basis, it becomes a standalone occurrence rather than a continuous habit.
As a result, retention is low. Employees often forget the lessons within weeks, a phenomenon known as the ‘Ebbinghaus Forgetting Curve.’
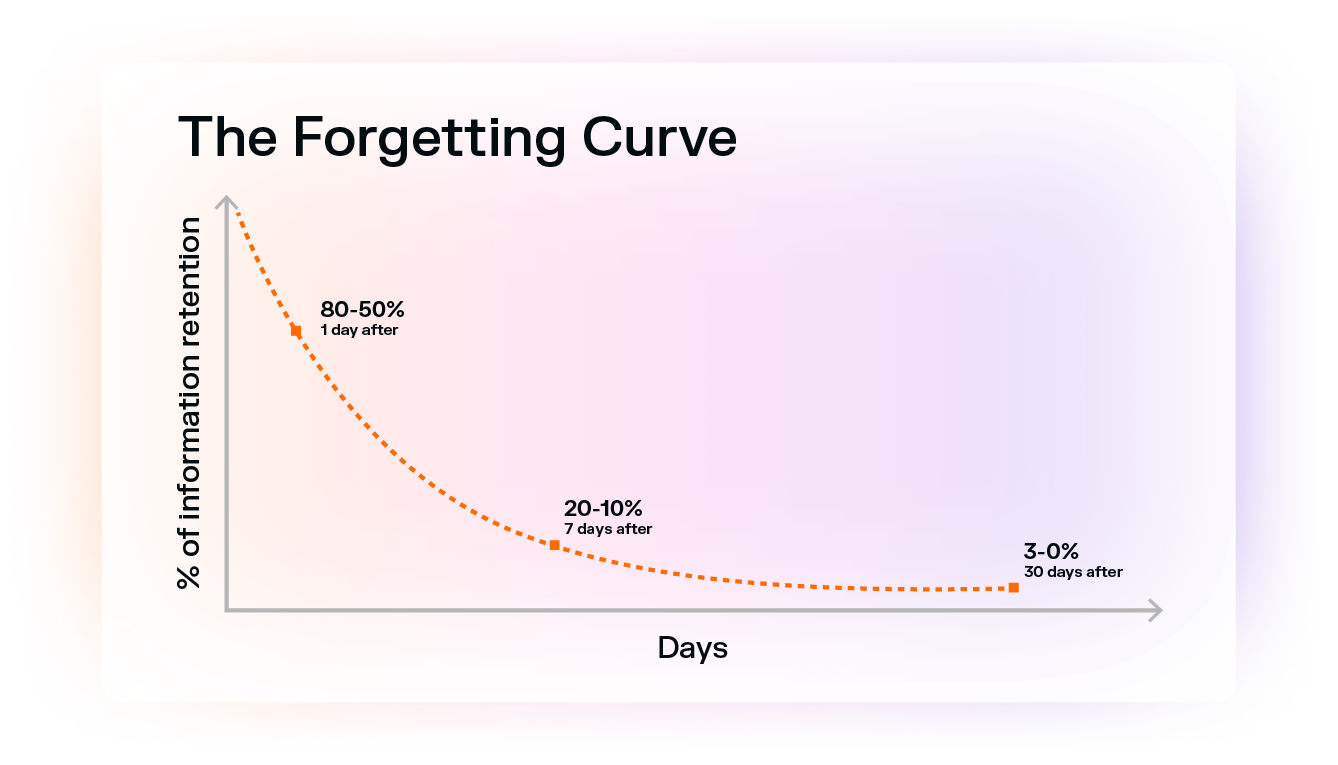
The graph illustrates that when you first learn something, the information disappears at an exponential rate without retention. In fact, according to the curve, you forget 50% of all new information within a day, and 90% of all new information within a week.
Simultaneously, most training is conducted within a separate interface. Because it takes place away from the actual moment of decision-making, the "teachable moment" is lost. There is a cognitive disconnect between the action (clicking a link in Outlook) and the education (watching a video in a browser).
People
In the context of professional risk management, the risks faced by different users are different. Static learning such as everyone receiving the same ‘Password Reset’ email doesn’t help users prepare for the specific threats they are likely to face. It also contributes to user fatigue, driven by repetitive training. And if users receive tests at the same time, news spreads among colleagues, hurting the efficacy of the test.
Staff turnover introduces further risk. In many organizations, new employees gain access to systems before receiving meaningful training, reducing onboarding to little more than policy acknowledgment.
Measuring success
In my experience, solutions are standalone, without any correlation to other tools in the security stack. In some cases, the programs are delivered by HR rather than the security team, creating a complete silo.
As a result, SAT is often perceived as a compliance exercise rather than a capability building function. The result is that poor-quality training does little to reduce the likelihood of compromise, regardless of completion rates or quiz performance.
What a modern SAT solution should look like
For today’s CISO, email represents the convergence point of high-volume, high-impact, and human-centric threats. Despite significant security investments, it remains one of the most difficult channels to secure effectively. Given these constraints, CISOs must evolve their approach to SAT.
Success lies in a balanced strategy one that combines advanced technology, attack surface reduction, and pragmatic user enablement, without over-relying on human vigilance as the final line of defense.
This means moving beyond traditional SAT toward continuous, contextual awareness, realistic simulations, and tight integration with security outcomes.
Three requirements for a modern SAT solution
- Invisible protection: The optimum security solution is one that assists users without impeding their experience. The objective is to enhance human capabilities, rather than simply delivering a lecture.
- Real-time feedback: Rather than a monthly quiz, the ideal system would provide a prompt or warning when a user is about to engage with something suspicious.
- Positive culture: Shifting the focus away from a "gotcha" culture, which is a contributing factor to a resentment, and instead empowers employees to serve as "sensors" for the company.
Discover how personalized security coaching can strengthen your human layer and make your email defenses more resilient. Explore Darktrace / Adaptive Human Defense.
































.jpg)






