Introduction
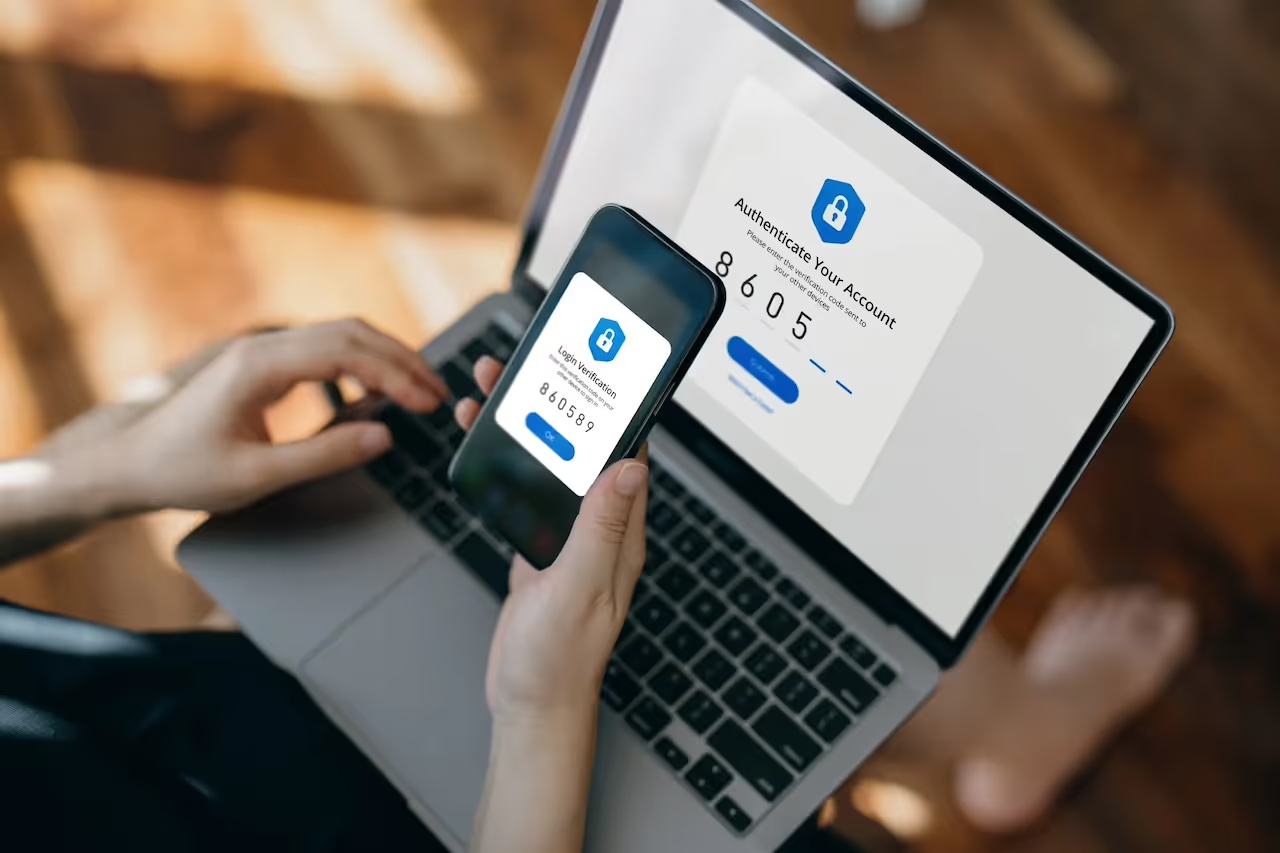
As malicious actors across the threat landscape continue to take advantage of the widespread adoption of Software-as-a-Service (SaaS) platforms and multi-factor authentication (MFA) services to gain unauthorized access to organizations’ networks, it is crucial to have appropriate security tools in place to defend against account compromise at the earliest stage.
One method frequently employed by attackers is account takeover. Account takeovers occur when a threat actor exploits credentials to login to a SaaS account, often from an unusual location where the genuine actor does not usually login from.
Access to these accounts can be caused by harvesting credentials through phishing emails and password spray attacks, or by exploiting insecure cloud safety practices such as not having MFA enabled on user accounts, requiring only user credentials for authentication. Once the integrity of the account is compromised, the threat actor can conduct further activity, such as delivering malware, reading and exfiltrating sensitive data, and sending out phishing emails to harvest further internal and external user credentials, repeating the attack cycle [1,2].
In early 2023, Darktrace detected a large-scale account takeover and phishing attack on the network of a customer in the education sector that affected hundreds of accounts and resulted in thousands of emails being forwarded outside of the network. The exceptional degree of visibility provided by Darktrace DETECT™ allowed for the detection of adversarial activity at every stage of the kill chain, and direct support from the Darktrace Analyst team via the Ask the Expert (ATE) service ensured the customer was fully informed and equipped to implement remedial action.
Details of Attack Chain
Darktrace observed the same pattern of activity on all hijacked accounts on the customer’s network; login from unfamiliar locations, enablement of a mail forwarding rule that forwards all incoming emails to malicious email addresses, and the sending of phishing emails followed by their deletion.

Initial Access
Darktrace DETECT first detected anomalous SaaS activity on the customer environment on January 14, 2023, and then again on February 3, when multiple SaaS accounts were observed logging in from atypical locations with rare IP addresses and geographically impossible travel timings, or logging in whilst the account owner was active elsewhere. Subsequent investigation using open-source intelligence (OSINT) sources revealed one of the IP addressed had recently been associated with brute-force or password spray attempt.
This pattern of unusual login behavior persisted throughout the timeframe of the attack, with more unique accounts generating model breaches each day for similarly anomalous logins. As MFA authentication was not enforced for these user logins, the initial intrusion process was enabled by requiring only credentials for authentication.
Sending Emails
The compromised accounts were also seen sending out emails with the subject ‘Email HELP DESK’ to external and internal recipients. This was likely represented a threat actor employing social engineering tactics to gain the trust of the recipient by posing as an internal help desk.
Mail Forwarding
Following the successful logins, compromised accounts began creating email rules to forward mail to external email addresses, some of which were associated with domains that had hits for malicious activity according to OSINT sources [3].
- chotunai[.]com
- bymercy[.]com
- breazeim[.]com
- brandoza[.]com
Forwarding mail is a commonly observed tactic during SaaS compromises to control lines of communication. Malicious actors often attempt to insert themselves into ongoing correspondence for illicit purposes, such as exfiltrating sensitive information, gaining persistent access to the compromised email or redirecting invoice payments.
Email Deletions
Shortly after the mail forwarding activity, compromised accounts were detected performing anomalous email deletions en masse. Further investigation revealed that these accounts had previously sent a large volume of phishing emails and this mass deletion likely represented an attempt to conceal these activities by deleting them from their outboxes.
On February 10, the customer applied a mass password reset on all accounts that Darktrace had identified as compromised and provisioned, privileged accounts with MFA. They have indicated that those measures successfully halted the compromise, addressing the initial point of entry.
Darktrace Coverage
Using its Self-Learning AI, Darktrace effectively demonstrated its ability to detect unusual SaaS activity that could indicate that an account has been hijacked by malicious actors. Rather than relying on a traditional rules and signature-based approach, Darktrace models develop an understanding of the network itself and can instantly recognize when a compromised deviates from its expected pattern of life.

Initial Access
Initial access was detected by the following models:
- Security Integration / High Severity Integration Detection
- SaaS / Unusual Activity / Activity from Multiple Unusual IPs
- SaaS / Access / Unusual External Source for SaaS Credential Use
- SaaS / Compromise / Login From Rare Endpoint While User Is Active
Initial access was also detected by the following Cyber AI Analyst Incidents:
- Possible Hijack of Office365 Account
The model breaches and AI Analyst incidents detected logins from 100% rare external IP addresses in conjunction with a lack of MFA usage, as depicted in Figure 3.


Mail Forwarding
Mail forwarding was detected by the following models:
- SaaS / Admin / Mail Forwarding Enabled
Compromised accounts were largely detected configuring mail forwarding rules to external email addresses, ostensibly to establish persistence on the network and exfiltrate sensitive correspondence.

Mass Email Deletion
Mass email deletion was detected by the following models:
- SaaS / Compromise / Suspicious Login and Mass Email Deletes
- SaaS / Resource / Mass Email Deletes from Rare Location

Darktrace detected accounts performing highly anomalous mass email deletions from rare locations. The actors deleted the email “Email HELP DESK” which was later confirmed as being the primary phishing email used in the attack. Deletions were observed on compromised accounts’ outboxes, presumably to conceal the malicious activity.
Darktrace also detected this linked pattern of activity in sequential models such as:
- SaaS / Compromise / Unusual Login, Sent Mail, Deleted Sent
- SaaS / Compromise / Suspicious Login and Mass Email Deletes
Ask the Expert
The customer used the ATE service to request more technical information and support concerning the attack. Darktrace’s 24/7 team of analysts were able to offer expert assistance and further details to assist in the subsequent investigations and remediation steps.
Further Detection and Response
Unfortunately, the customer did not have Darktrace/Email™ enabled at the time of the attack. Darktrace/Email has visibility over inbound and outbound mail-flow which provides an oversight on potential data loss incidents. In this case, Darktrace DETECT/Email would have been able to provide full visibility over the phishing emails sent by the compromised accounts, as well as the attackers attempts to spoof an internal helpdesk. Further to this, the new Analysis Outlook integration helps employees understand why an email is suspicious and enables them report emails directly to the security team, which helps to continuously build user awareness of phishing attacks.
Darktrace/Email also enhances Darktrace/Network™ detections by triggering ‘Email Nexus’ models within Darktrace/Network, where malicious activity is detected across the digital estate, correlating moving from SaaS compromised logins to mass email spam being sent out by compromised users.

Darktrace RESPOND™ was not enabled on the customer environment at the time of the attack; if it were, Darktrace would have been able to autonomously take action against the SaaS model breaches detecting across multiple of the kill chain. RESPOND would have disabled the hijacked accounts or force them to log out for a period of time, whilst also disabling the inbox rules that had been established by malicious actors. This would have given the customer’s security team valuable time to analyze the incident and mitigate the situation, preventing the attack from escalating any further.
Conclusion
Ultimately, Darktrace demonstrated its unparalleled visibility over customer networks which allowed for the detection of this large-scale targeted SaaS account takeover, and the subsequent phishing attack. It underscores the importance of defense in depth; critically, MFA was not enforced for this environment which likely made the targeted organization far more susceptible to compromise via credential theft. The phishing activity detected by Darktrace following this account compromise also highlights the need for email protection in any security stack.
Darktrace’s visibility meant allowed it to detect the attack at a high degree of granularity, including the account logins, email forwarding rule creations, outbound mail, and the mass deletions of phishing emails. Darktrace’s anomaly-based detection means it does not have to rely on signatures, rules or known indicators of compromise (IoCs) when identifying an emerging threat, instead placing the emphasis on recognizing a user’s deviation from its normal behavior.
However, without the presence of an autonomous response technology able to instantly intervene and stop ongoing attacks, organizations will always be reacting to attacks once the damage is done. Darktrace RESPOND is uniquely placed to take action against suspicious activity as soon as it is detected, preventing attacks from escalating and saving customers from significant disruption to their business.
Credit to: Zoe Tilsiter, Cyber Analyst, Gernice Lee, Cyber Analyst.
Appendices
Models Breached
SaaS / Access / Unusual External Source for SaaS Credential Use
SaaS / Admin / Mail Forwarding Enabled
SaaS / Compliance / Microsoft Cloud App Security Alert Detected
SaaS / Compromise / SaaS Anomaly Following Anomalous Login
SaaS / Compromise / Unusual Login, Sent Mail, Deleted Sent
SaaS / Compromise / Suspicious Login and Mass Email Deletes
SaaS / Resource / Mass Email Deletes from Rare Location
SaaS / Unusual Activity / Multiple Unusual External Sources For SaaS Credential
SaaS / Unusual Activity / Activity from Multiple Unusual IPs
SaaS / Unusual Activity / Multiple Unusual SaaS Activities
Security Integration / Low Severity Integration Detection
Security Integration / High Severity Integration Detection
List of IoCs
brandoza[.]com - domain - probable domain of forwarded email address
breazeim[.]com - domain - probable domain of forwarded email address
bymercy[.]com - domain - probable domain of forwarded email address
chotunai[.]com - domain - probable domain of forwarded email address
MITRE ATT&CK Mapping
Tactic: INITIAL ACCESS, PERSISTENCE, PRIVILEGE ESCILATION, DEFENSE EVASION
Technique: T1078.004 – Cloud Accounts
Tactic: COLLECTION
Technique: T1114- Email Collection
Tactic:COLLECTION
Technique: T1114.003- Email Forwarding Rule
Tactic: IMPACT
Technique: T1485- Data Destruction
Tactic: DEFENSE EVASION
Technique: T1578.003 – Delete Cloud Instance
References
[1] Darktrace, 2022, Cloud Application Security_ Protect your SaaS with Self-Learning AI.pdf
[2] https://www.cloudflare.com/en-gb/learning/access-management/account-takeover/




























%201.png)