Between June 2021 and June 2022, crypto-currency platforms around the world lost an estimated 44 billion USD to cyber criminals, whose modus operandi range from stealing passwords and account recovery phrases, to cryptojacking and directly targeting crypto-currency transactions.
There has been a recent rise in cases of cyber criminals’ using information stealer malware to gather and exfiltrate sensitive crypto-currency wallet details, ultimately leading to the theft of significant sums of digital currency. Having an autonomous decision maker able to detect and respond to potential compromises is crucial to safeguard crypto wallets and transactions against would-be attackers.
In late 2022, Darktrace observed several threat actors employing a novel attack method to target crypto-currency users across its customer base, specifically the latest version of the Laplas Clipper malware. Using Self-Learning AI, Darktrace DETECT/Network™ and Darktrace RESPOND/Network™ were able to uncover and mitigate Laplas Clipper activity and intervene to prevent the theft of large sums of digital currency.
Laplas Clipper Background
Laplas Clipper is a variant of information stealing malware which operates by diverting crypto-currency transactions from victims’ crypto wallets into the wallets of threat actors [1]. Laplas Clipper is a Malware-as-a-Service (MaaS) offering available for purchase and use by a variety of threat actors. It has been observed in the wild since October 2022, when 180 samples were identified and linked with another malware strain, namely SmokeLoader [2]. This loader has itself been observed since at least 2011 and acts as a delivery mechanism for popular malware strains [3].
SmokeLoader is typically distributed via malicious attachments sent in spam emails or targeted phishing campaigns but can also be downloaded directly by users from file hosting pages or spoofed websites. SmokeLoader is known to specifically deliver Laplas Clipper onto compromised devices via a BatLoader script downloaded as a Microsoft Word document or a PDF file attached to a phishing email. These examples of social engineering are relatively low effort methods intended to convince users to download the malware, which subsequently injects malicious code into the explorer.exe process and downloads Laplas Clipper.
Laplas Clipper activity observed across Darktrace’s customer base generally began with SmokeLoader making HTTP GET requests to Laplas Clipper command and control (C2) infrastructure. Once downloaded, the clipper loads a ‘build[.]exe’ module and begins monitoring the victim’s clipboard for crypto-currency wallet addresses. If a wallet address is identified, the infected device connects to a server associated with Laplas Clipper and downloads wallet addresses belonging to the threat actor. The actor’s addresses are typically spoofed to appear similar to those they replace in order to evade detection. The malware continues to update clipboard activity and replaces the user’s wallet addresses with a spoofed address each time one is copied for a for crypto-currency transactions.
Darktrace Coverage of Laplas Clipper and its Delivery Methods
In October and November 2022, Darktrace observed a significant increase in suspicious activity associated with Laplas Clipper across several customer networks. The activity consisted largely of:
- User devices connecting to a suspicious endpoint.
- User devices making HTTP GET requests to an endpoint associated with the SmokeLoader loader malware, which was installed on the user’s device.
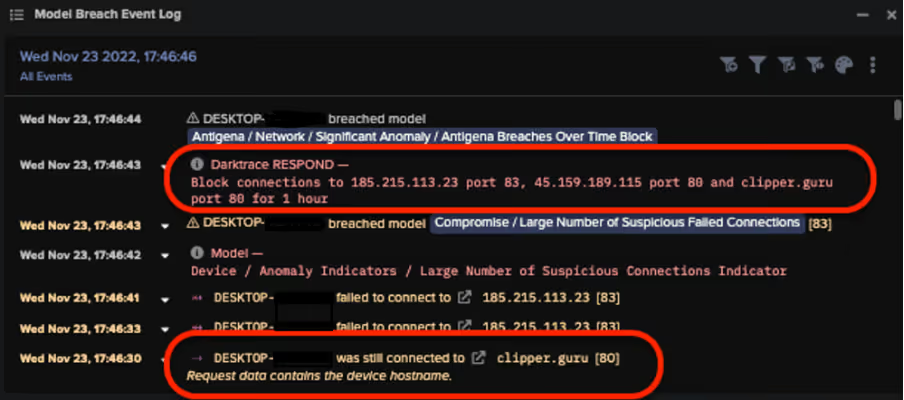
- User devices making HTTP connections to the Laplas Clipper download server “clipper[.]guru”, from which it downloads spoofed wallet addresses to divert crypto-currency payments.
In one particular instance, a compromised device was observed connecting to endpoints associated with SmokeLoader shortly before connecting to a Laplas Clipper download server. In other instances, devices were detected connecting to other anomalous endpoints including the domains shonalanital[.]com, transfer[.]sh, and pc-world[.]uk, which appears to be mimicking the legitimate endpoint thepcworld[.]com.
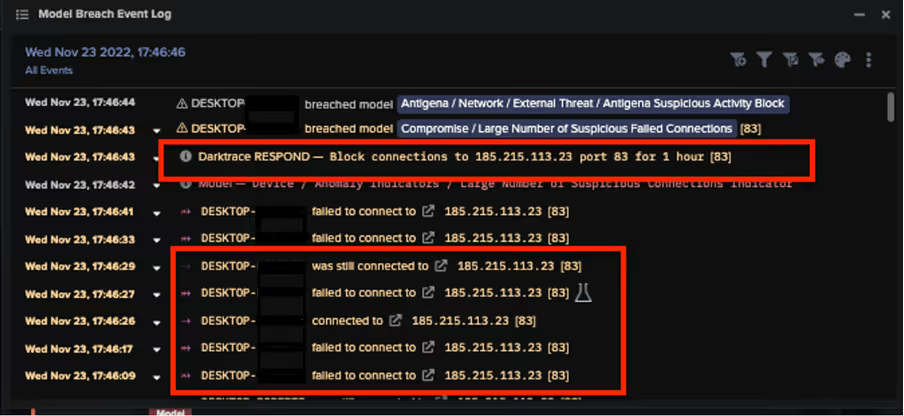
Additionally, some compromised devices were observed attempting to connect malicious IP addresses including 193.169.255[.]78 and 185.215.113[.]23, which are associated with the RedLine stealer malware. Additionally, Darktrace observed connections to the IP addresses 195.178.120[.]154 and 195.178.120[.]154, which are associated with SmokeLoader, and 5.61.62[.]241, which open-source intelligence has associated with Cobalt Strike.
The following DETECT/Network models breached in response to these connections:
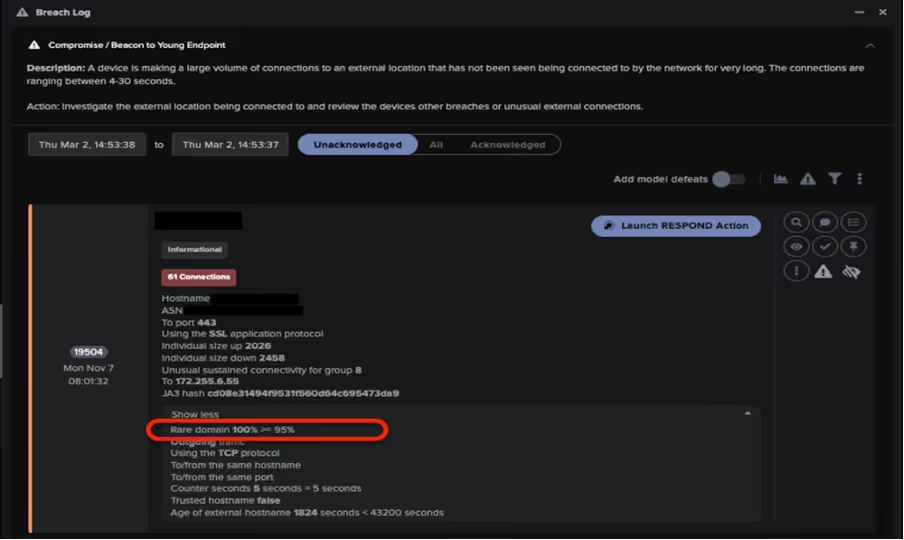
- Compromise / Beacon to Young Endpoint
- Compromise / Slow Beaconing Activity to External Rare
- Compromise / Beacon for 4 Days
- Compromise / Beaconing Activity to External Rare
- Compromise / Sustained TCP Beaconing Activity to Rare Endpoint
- Anomalous Connection / Multiple Failed Connections to Rare Endpoints
- Compromise / Large Number of Suspicious Failed Connections
- Compromise / HTTP Beaconing to Rare Destination
- Compromise / Post and Beacon to Rare External
- Anomalous Connection / Callback on Web Facing Device
DETECT/Network is able to identify such activity as its models operate based on a device’s usual pattern of behavior, rather than a static list of indicators of compromise (IOCs). As such, Darktrace can quickly identify compromised devices that deviate for their expected pattern of behavior by connecting to newly created malicious endpoints or C2 infrastructure, thereby triggering an alert.
In one example, RESPOND/Network autonomously intercepted a compromised device attempting to connect to the Laplas Clipper C2 server, preventing it from downloading SmokeLoader and subsequently, Laplas Clipper itself.
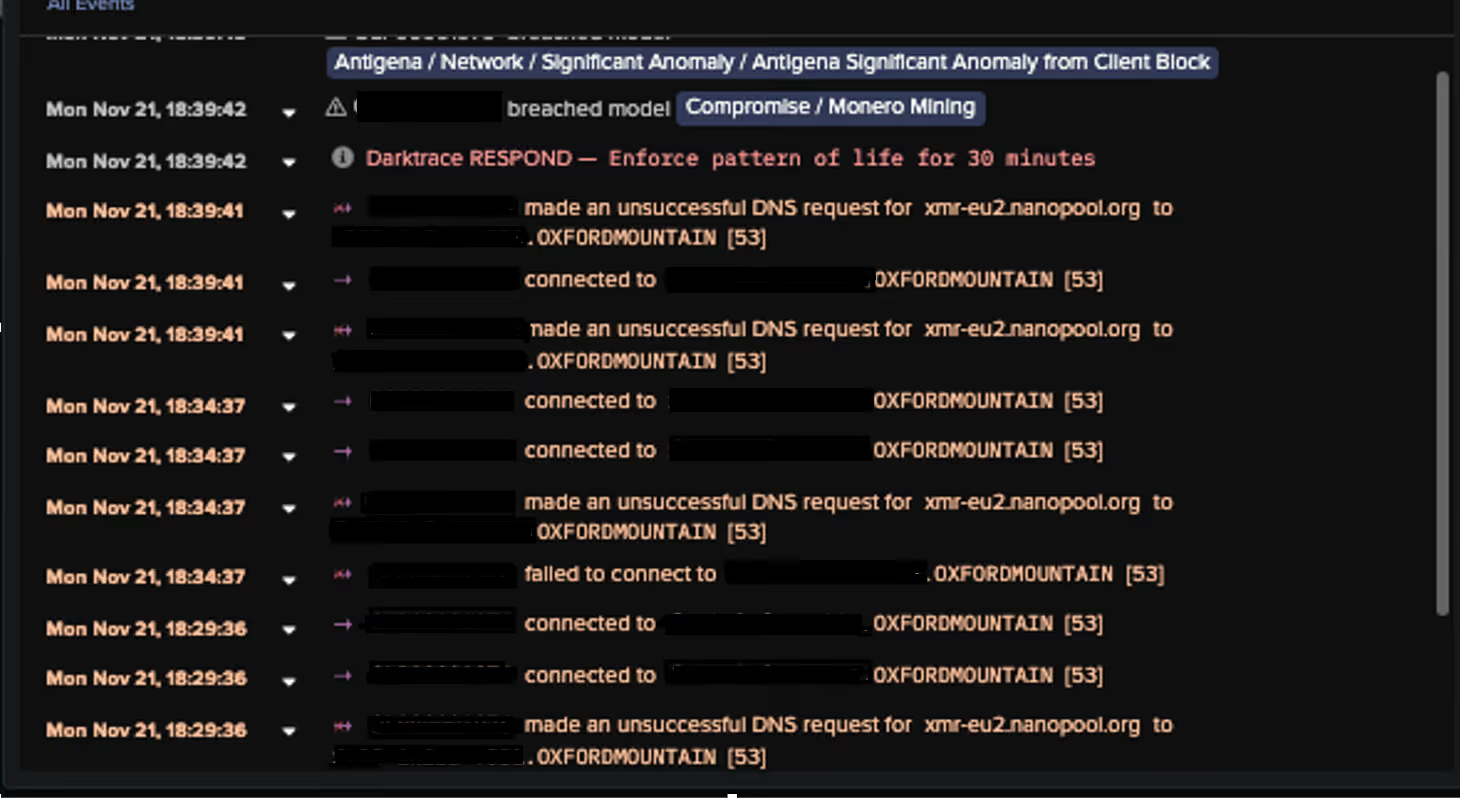
In another example, DETECT/Network observed an infected device attempting to perform numerous DNS Requests to a crypto-currency mining pool associated with the Monero digital currency.
This activity caused the following DETECT/Network models to breach:
- Compromise / Monero Mining
- Compromise / High Priority Crypto Currency Mining
RESPOND/Network quickly intervened, enforcing a previously established pattern of life on the device, ensuring it could not perform any unexpected activity, and blocking the connections to the endpoint in question for an hour. These actions carried out by Darktrace’s autonomous response technology prevented the infected device from carrying out crypto-mining activity, and ensured the threat actor could not perform any additional malicious activity.
Finally, in instances when RESPOND/Network was not activated, external connections to the Laplas Clipper C2 server were nevertheless monitored by DETECT/Network, and the customer’s security team were notified of the incident.
Conclusion
The rise of information stealing malware variants such as Laplas Clipper highlights the importance of crypto-currency and crypto-mining in the malware ecosystem and more broadly as a significant cyber security concern. Crypto-mining is often discounted as background noise for security teams or compliance issues that can be left untriaged; however, malware strains like Laplas Clipper demonstrate the real security risks posed to digital estates from threat actors focused on crypto-currency.
Leveraging its Self-Learning AI, DETECT/Network and RESPOND/Network are able to work in tandem to quickly identify connections to suspicious endpoints and block them before any malicious software can be downloaded, safeguarding customers.
Appendices
List of IOCs
a720efe2b3ef7735efd77de698a5576b36068d07 - SHA1 Filehash - Laplas Malware Download
conhost.exe - URI - Laplas Malware Download
185.223.93.133 - IP Address - Laplas C2 Endpoint
185.223.93.251 - IP Address - Laplas C2 Endpoint
45.159.189.115 - IP Address - Laplas C2 Endpoint
79.137.204.208 - IP Address - Laplas C2 Endpoint
5.61.62.241 - IP Address - Laplas C2 Endpoint
clipper.guru - URI - Laplas C2 URI
/bot/online?guid= - URI - Laplas C2 URI
/bot/regex?key= - URI - Laplas C2 URI
/bot/get?address - URI - Laplas C2 URI
Mitre Attack and Mapping
Initial Access:
T1189 – Drive By Compromise
T1566/002 - Spearphishing
Resource Development:
T1588 / 001 - Malware
Ingress Tool Transfer:
T1105 – Ingress Tool Transfer
Command and Control:
T1071/001 – Web Protocols
T1071 – Application Layer Protocol
T1008 – Fallback Channels
T1104 – Multi-Stage Channels
T1571 – Non-Standard Port
T1102/003 – One-Way Communication
T1573 – Encrypted Channel
Persistence:
T1176 – Browser Extensions
Collection:
T1185 – Man in the Browser
Exfiltration:
T1041 – Exfiltration over C2 Channel
References
[1] https://blog.cyble.com/2022/11/02/new-laplas-clipper-distributed-by-smokeloader/
[2] https://thehackernews.com/2022/11/new-laplas-clipper-malware-targeting.html




































