Darktrace / EMAIL offers flexible deployment options, seamlessly integrating with Microsoft 365 and other native providers to protect against advanced threats across email and collaboration channels. Gartner analysts recommend API-based integrations for modern email security and customers consistently rate these approaches highly on Gartner Peer Insights.
But not all API integrations are equal. This blog explores an option uniquely offered by Darktrace: API + Journaling, and why it matters for speed, reliability, and resilience.
API + Journaling: What it is and why it’s different
Most Integrated Cloud Email Security (ICES) solutions rely on API-only ingestion, which:
- Subscribes to Microsoft Graph change notifications
- Fetches and analyzes messages after delivery
- Quarantines or retracts malicious messages post-inbox
This works, but introduces notification latency. Microsoft Graph aims for near-real-time delivery, but practical delays can range from seconds to minutes, especially under load or retry conditions. Even a one-second delay matters when email is your most critical communication channel.
API + Journaling solves this.
By adding journaling in Microsoft 365, Darktrace receives a copy of the raw email while it’s still in the transport pipeline – before it hits the inbox. That means:
- Analysis runs in parallel with Microsoft’s native defenses
- Detection decisions happen pre-delivery, not after
- Latency is dramatically reduced, and long-tail delays are eliminated
A modern, security-relevant approach
While journaling was originally introduced in Microsoft Exchange for compliance and archiving, it has evolved into a mature, well-documented feature that is widely used for both compliance and security monitoring. Microsoft’s own documentation recognizes journaling as a supported, secure, and configurable mechanism for message capture. In modern ICES deployments, journaling is leveraged not just for archiving, but for real-time, pre-delivery analysis, enabling faster detection and response to threats.
What I appreciate most is the simplicity of setting it up and configuring it."
Latency advantage: Measured in real environments
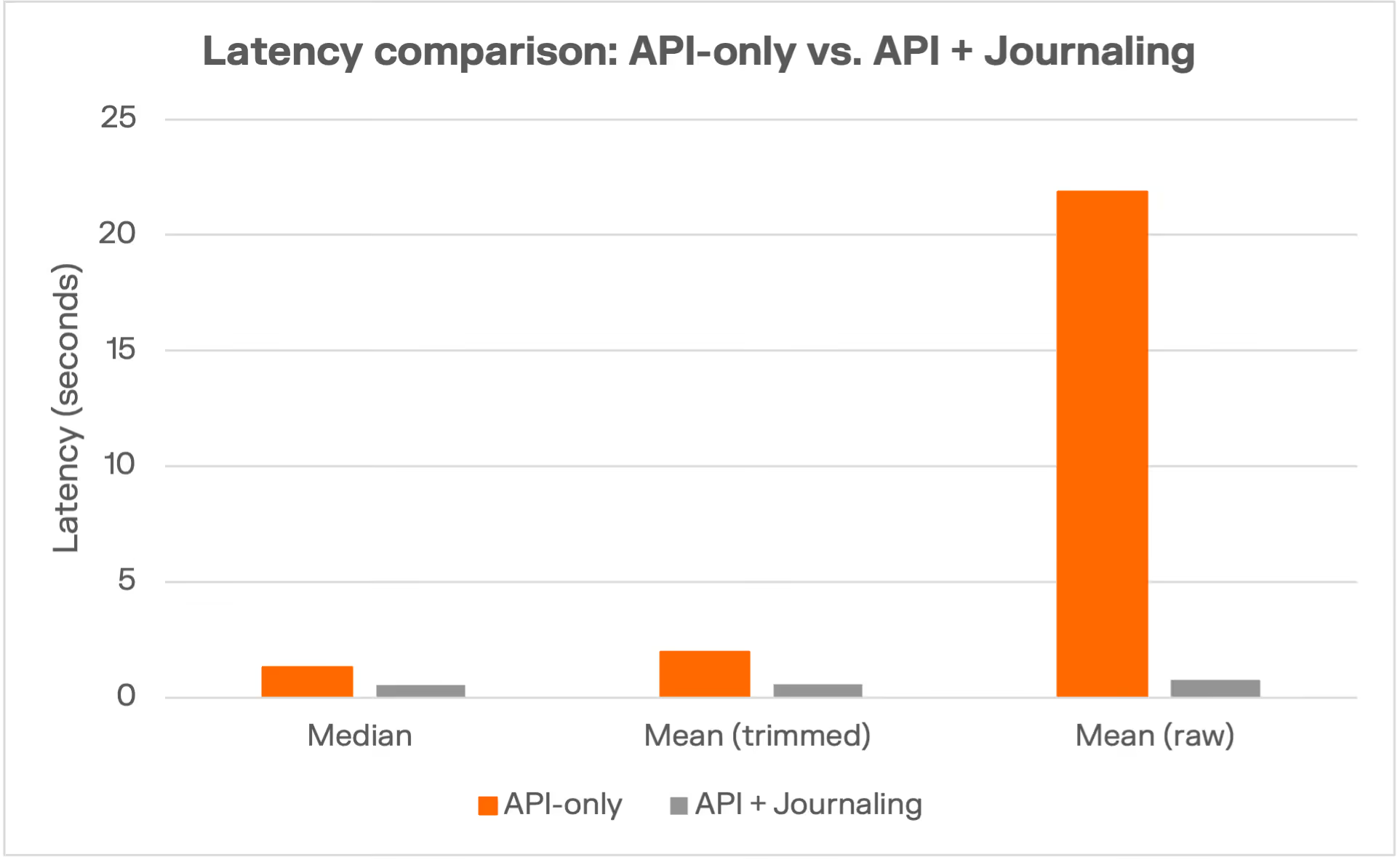
Our measurements across real customer deployments confirm the performance gap between API-only and API + Journaling deployments when evaluating the time taken to receive a single email:
The bottom line?
API + Journaling consistently cuts detection latency by 2–3x in typical scenarios and mitigates long-tail delays by up to ~30x – a critical advantage when every second counts. That could be the difference between actioning an email before a user sees it within their inbox or after, avoiding user confusion and erroneous email notifications that disappear by the time they go into Outlook.
Their Proof of Life, learning your environment and user behaviour and the things it has automatically noted were amazing. There has not been a single case of phishing in our organization since its deployment."
And speed isn’t the only benefit
API + Journaling doesn’t only benefit email users in terms of delivery speed. It also offers:
- Robustness backed by SLAs: Journaling leverages Microsoft 365’s Exchange Online transport pipeline, which operates under Microsoft’s financially backed 99.9% availability SLA. API notifications, by contrast, are best-effort and carry no latency guarantee
- Resilience against API throttling: Journaling avoids variability from Graph webhook delivery and retries
- Defense in depth: Parallel analysis with native security reduces exposure windows and strengthens posture
Flexible deployment, clear recommendation
Darktrace / EMAIL supports multiple integration patterns, including API-only for environments where journaling isn’t feasible. API-only deployments remain a flexible option for organizations with specific requirements or constraints. However, for those prioritizing speed, reliability, and SLA-backed assurance, API + Journaling is our recommended approach.
All integration styles have trade-offs, and the right choice depends on your organization’s needs and constraints. Darktrace’s integration with Microsoft 365 is fully supported and aligns with Microsoft’s best practices for ICES vendors. Our approach delivers both operational efficiency and enhanced detection, as validated by customer results and independent analyst recognition. We recommend API + journaling for organizations seeking the best balance of speed, clarity, and resilience.
Ready to accelerate your email threat detection? Contact us to get a demo and we’ll walk you through our deployment options.
Journaling Myths & Facts: FAQ
Q: Is journaling slow, outdated, or risky compared to API-only approaches?
A: No. Journaling is a mature, well-documented Microsoft feature, widely used for compliance and security monitoring. When implemented with proper controls, journaling is secure and compliant. Data is isolated, access-controlled, and never shared across customers. Importantly, journaling does not “move” the original email out of Microsoft 365; it simply creates a copy for analysis, leaving the original message flow intact. Pre-delivery journaling enables parallel analysis with native security, reducing risk, not increasing it.
Q: Is it true that Microsoft does not recommend using Journaling and/or post-delivery actions?
A: No, Microsoft clearly states that they do not recommend these methods for security benchmarking specifically. However, as a deployment method, it is a perfectly valid approach with more consistent delivery times than relying on APIs exclusively.
Q: Does API + Journaling create fragmented visibility or complicate investigations?
A: Other solutions may create duplicated visibility but Darktrace’s deployment ensures message IDs are preserved, maintaining operational clarity and traceability for SOC teams. Our integration is designed to avoid message duplication and supports unified investigation workflows. API + journaling is unique in providing both speed and clarity, with proven customer outcomes such as reducing malicious messages to zero in large enterprise environments.
Q: Is journaling secure and compliant?
A: Yes. Journaling data is isolated, access-controlled, and never shared across customers. Microsoft provides clear guidance on secure journaling configurations and compliance best practices.
Q: Does journaling mean there is no internal or lateral email monitoring?
A: Darktrace can be configured to capture internal, external, or all messages, ensuring full visibility for compliance and threat detection.
Q: What if my organization can’t use journaling?
A: Darktrace / EMAIL still supports API-only deployments, providing flexibility for organizations with unique requirements.
References
Microsoft Online Services SLA (Exchange Online)
Configure Journaling in Exchange Online
Microsoft Graph API Change Notifications
































.jpg)







%201.png)