Cloud Misconfigurations
Cloud misconfiguration
Cloud environments are secure by design, but implementation errors make them vulnerable. The complexity of managing multi-cloud environments creates visibility gaps where configuration drift occurs unnoticed, leaving security teams unaware of the exposure until it's exploited.
To maintain robust cloud security, it's essential to understand what cloud misconfiguration is, how it occurs within the Shared Responsibility Model, and how multi-layered AI-driven strategies provide better protection than traditional static checklists.
What is cloud misconfiguration?
Cloud misconfiguration occurs when security settings, access controls, or permissions in cloud environments are incorrectly configured, leaving data and resources vulnerable. Within the Shared Responsibility Model, cloud providers secure the underlying infrastructure while customers remain responsible for securing their data and applications. This division means that even when providers offer robust security features, improper customer configuration creates exploitable weaknesses.
These errors are not inherent flaws in cloud platforms. Rather, they represent mistakes in how organizations configure security settings, identity management, network controls, or storage permissions. A standard cyber-attack exploits vulnerabilities using sophisticated tools to breach systems. Cloud misconfiguration is opportunity-based, creating self-inflicted vulnerabilities that adversaries need no advanced techniques to exploit.
Cloud misconfigurations are not software bugs or zero-day exploits. They stem from human error in managing complexity across Infrastructure as a Service, Platform as a Service, and Software as a Service layers. Managing configurations across multiple cloud providers increases oversight challenges. These misconfigurations act as open doors, requiring no sophisticated hacking tools to exploit.
Why is preventing cloud misconfiguration important?
Cloud misconfiguration ranks as the leading cause of cloud data breaches, far outpacing external hacking attempts. Industry analysis shows the vast majority of cloud security failures stem from customer-side configuration errors.
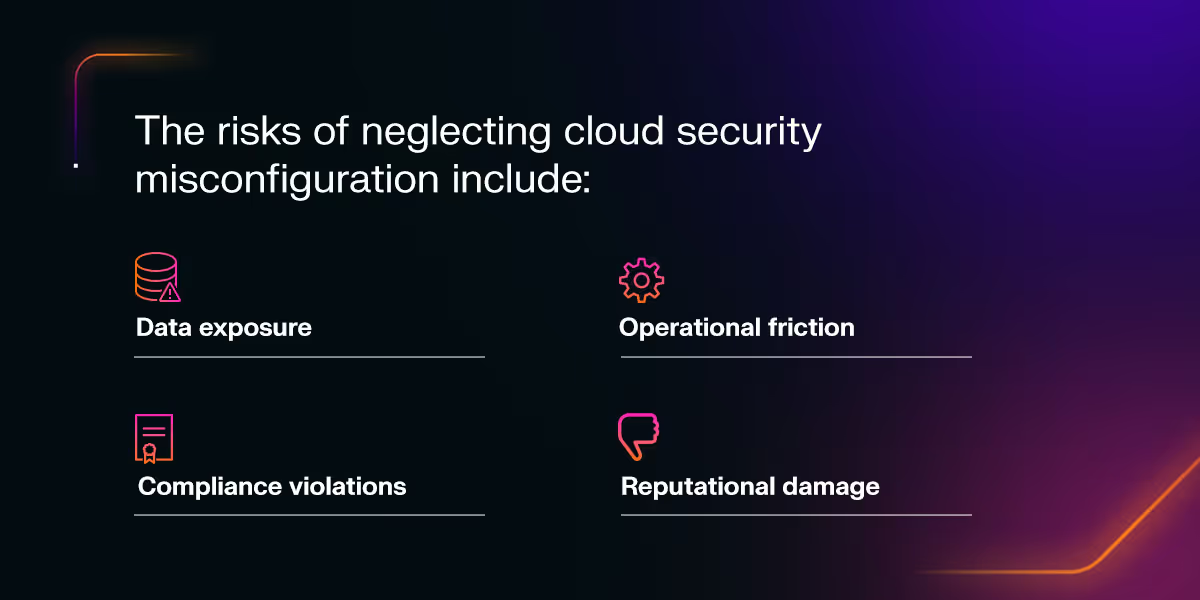
The risks of neglecting cloud security misconfiguration include:
- Data exposure: Cloud security misconfiguration creates direct pathways for data exfiltration, cryptojacking, ransomware deployment, and account takeovers without requiring sophisticated tools. A single misconfigured storage bucket or improperly secured API endpoint can expose terabytes of sensitive data. Adversaries scan for these openings, automating discovery and exploitation at scale.
- Compliance violations: Standards such as the General Data Protection Regulation, the Health Insurance Portability and Accountability Act, and System and Organization Controls 2 mandate specific security controls. When assets are publicly exposed due to misconfiguration, organizations face immediate compliance violations, triggering audits, fines, and the potential suspension of data processing activities.
- Operational friction: DevOps teams face pressure to release code fast to meet tight shipping deadlines. Security teams must maintain controls despite the speed. This pressure leads to configuration drift, where security settings deviate from baselines as developers prioritize speed over security reviews. Infrastructure deployed without proper validation accumulates risk.
- Reputational damage: Maintaining proper cloud hygiene enhances resilience and reduces the attack surface. When breaches occur due to preventable cloud misconfigurations, reputational damage often exceeds direct financial costs.
Common types of cloud misconfigurations
Cloud misconfigurations occur during rapid lift-and-shift migrations when organizations move on-premises workloads to the cloud without adapting security controls. Shadow IT compounds this problem by allowing developers to bypass security reviews, creating ungoverned assets.
Storage and database exposure
Unsecured storage buckets are among the most prevalent cloud misconfigurations. Storage buckets such as Amazon S3 buckets, Azure Blob Storage, and Google Cloud Storage containers are frequently left accessible to the public internet. Databases also suffer from exposure when administrators fail to restrict access to specific IP ranges or require authentication.
Identity and Access Management (IAM) mistakes
Overly permissive access violates the Least Privilege principle, granting users or services more privileges than necessary. The absence of Multi-Factor Authentication on privileged accounts compounds IAM risks, enabling adversaries who obtain credentials through phishing to immediately access cloud resources.
Network configuration errors
Unrestricted inbound and outbound ports create direct access points. Leaving SSH port 22 or RDP port 3389 open to the internet invites brute-force attacks. Improper network segmentation allows lateral movement once adversaries establish an initial foothold.
Logging and monitoring gaps
Disabling or misrouting logs prevents security teams from detecting suspicious activity. When organizations fail to enable logging capabilities or route logs to centralized systems, cloud misconfigurations go unnoticed, and attacks remain undetected. This visibility gap prevents forensic investigations.
Secrets management failures
Hard-coded API keys or credentials left in public code repositories create immediate security risks. Developers often embed authentication tokens in application code, then accidentally commit this sensitive information to GitHub. Automated scanners continuously search public repositories for these credentials and exploit them within minutes.
Unencrypted data
Storing data at rest or in transit without encryption exposes sensitive information. Cloud providers offer encryption services, but organizations must enable and configure these protections. Data transmitted without Transport Layer Security encryption can be intercepted, while unencrypted storage volumes remain readable if compromised.
Approaches to misconfiguration management
Effective misconfiguration management requires a comprehensive approach that combines proactive detection with rapid remediation. Organizations must identify configuration errors before they reach production while continuously monitoring live systems for drift. Today's strategies leverage automation and artificial intelligence (AI) to maintain security across dynamic, multi-cloud infrastructures.
Detection methods
Identifying misconfigurations requires layered detection strategies that operate across the development and production life cycle. Organizations benefit from catching errors early while maintaining vigilance in live environments where configurations change constantly.
- Static analysis: Scanning Infrastructure-as-Code templates before deployment catches configuration errors early. This shift-left approach reviews Terraform configurations, Kubernetes manifests, and CloudFormation templates against security baselines before resources are provisioned.
- Continuous monitoring: Real-time scanning in live environments remains essential for catching configuration drift after initial deployment. Cloud environments change constantly as teams modify permissions, deploy services, and adjust network rules. Continuous monitoring detects changes as they happen.
Remediation strategies
Once misconfigurations are detected, organizations must remediate them quickly to minimize exposure. The approach to remediation impacts an organization's ability to maintain security posture at scale:
- Manual versus automated remediation: Manual audits struggle to keep pace with dynamic cloud environments where hundreds of changes occur daily. Automated remediation tools detect policy violations and either alert administrators or automatically correct misconfigurations, reducing the exposure window.
- Cloud Security Posture Management (CSPM): CSPM tools assess cloud configurations against industry best practices and compliance frameworks. They benchmark deployments against CIS standards, provide risk scoring, and prioritize remediation based on potential impact.
- Integration challenges: Achieving comprehensive visibility across disparate cloud providers and containerized environments is challenging. Security solutions must integrate with multiple APIs and data sources to provide unified visibility.
The AI advantage
Multi-layered AI transforms cloud misconfiguration management by understanding context rather than applying static rules. This approach addresses the limitations of traditional tools that generate excessive false positives or miss sophisticated threats:
- Context over checklists: Unlike static tools that flag every open port, multi-layered AI understands behavioral context. It distinguishes between a port open to a known partner IP address and a port opened to a suspicious IP address. AI learns what constitutes normal behavior for each specific environment, reducing false positives.
- Attack path modeling: AI visualizes how adversaries would actually exploit discovered misconfigurations, chaining together multiple low-severity issues that create high-risk attack paths. This capability prioritizes the small percentage of misconfigurations that pose genuine threats.
- Continuous visibility: Real-time monitoring that adapts instantly when new containers or instances are spun up ensures security coverage never lags behind infrastructure changes. AI-driven solutions maintain continuous awareness of the entire cloud estate.
- Autonomous response: AI can contain breaches resulting from misconfigurations without disrupting legitimate business operations. When detecting data exfiltration from an exposed storage bucket, autonomous response mechanisms block the malicious connection while preserving access for authorized users.
Learn more Darktrace / CLOUD
Cloud misconfiguration is inevitable in complex, human-led IT environments where perfect configuration remains a moving target. As organizations scale their cloud infrastructure across multiple providers and services, maintaining visibility and control becomes challenging.
Darktrace / CLOUD provides a unified view of your entire cloud estate, using multi-layered AI to detect misconfigurations and respond to the attacks that exploit them in real time.
Explore how Darktrace strengthens cloud security by reading "Combatting the Top Three Sources of Risk in the Cloud" and “Most Common Cloud Security Threats.”