AI SOC
Security operations centers face unprecedented pressure as cyber-threats grow more sophisticated and frequent, driven by AI, cloud adoption, and complex supply chains. Organizations now process an average of 960 alerts daily, with large enterprises handling over 3,000 alerts from dozens of security tools. This overwhelming volume leaves nearly half of the potential threats uninvestigated.
AI offers a path forward, enabling security teams to detect novel threats, automate routine investigations, and respond at machine speed. This article explores how an Artificial Intelligence Security Operations Center (AI SOC) transforms security operations and what organizations should consider when pursuing this evolution.
What is an AI SOC?
An AI SOC is a security operations center that leverages artificial intelligence and machine learning to detect, investigate, and respond to cyber-threats at machine speed and scale.
Unlike traditional SOCs that rely on manual processes and signature-based detection, an AI-powered SOC makes decisions autonomously by understanding the context of events in real time. The primary purpose is to augment human analysts, acting as a force multiplier that handles high-volume data analysis so security professionals can focus on strategic remediation and proactive security posture.
An AI-driven SOC continuously learns from organizational data, identifying anomalous behavior that indicates compromise without requiring predefined attack signatures or threat intelligence updates.
Traditional SOC vs. AI SOC
The traditional SOC model faces fundamental limitations that hinder effective threat detection and response:
- Reliance on signatures and rules that identify only known threats, leaving organizations vulnerable to novel attacks not yet cataloged in threat intelligence feeds
- Alert fatigue from false positives and thousands of daily notifications that lack sufficient context, forcing analysts to spend hours on manual correlation and investigation
- Inability to detect zero-day attacks and targeted threats that evade pattern-matching tools designed to recognize previously observed malicious behavior
- A widening skills gap that leaves security teams understaffed, with 90% of organizations reporting having one or more skills gaps within their security teams
The AI-powered SOC takes a different approach. Where legacy systems ask, “Is this bad?”, an AI SOC asks, "Is this abnormal for this environment?" This behavioral analysis enables the detection of zero-day exploits, insider threats, and targeted attacks that signature-based tools would miss entirely.
AI capabilities with SOC use cases
Different AI techniques support distinct functions within security operations. Understanding which capabilities address specific SOC challenges helps organizations prioritize investments and set realistic expectations for outcomes.
Core capabilities of an AI-driven SOC
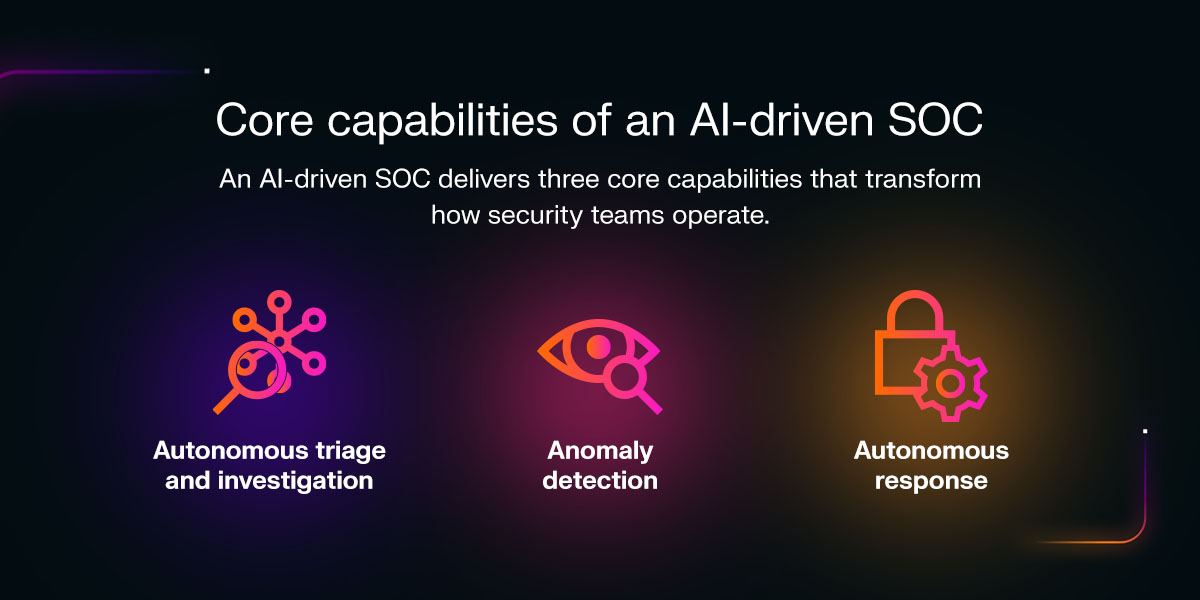
An AI-driven SOC delivers three core capabilities that transform how security teams operate.
1. Autonomous triage and investigation
AI systematically investigates alerts at machine speed, weaving disparate data points from email, network, and cloud environments into unified security incidents. This process eliminates the manual correlation work that consumes analyst hours and ensures no alerts fall through the cracks.
2. Anomaly detection
AI-driven detection tools alert to abnormal activity indicative of a threat, allowing analysts to identify novel threats before they do damage. Rather than relying on historical attack patterns, behavioral AI understands what normal looks like for each user, device, and application within the organization.
3. Autonomous response
AI-powered SOC provides the ability to take precise, surgical action to stop a threat, such as interrupting a specific connection, without disrupting legitimate business operations. This capability moves beyond simple "block all" responses to intelligent containment that interrupts specific malicious connections while allowing normal work to continue uninterrupted.
Real-world AI SOC use cases
Understanding how AI performs in operational environments helps security leaders identify high-value deployment opportunities. The following use cases demonstrate how behavioral analysis and autonomous response address threats that traditional signature-based tools consistently miss.
Insider threat detection
Insider threats are one of the most challenging detection scenarios for traditional security tools. Legitimate users with valid credentials can access sensitive systems without triggering signature-based alerts.
AI excels in this domain by establishing behavioral baselines for each user and identifying subtle deviations that indicate potential compromise or malicious intent. Unusual data transfers, anomalous login times, access to systems outside normal job functions, and changes in communication patterns all become visible through behavioral analysis. These early warning signs allow security teams to investigate and intervene before data exfiltration occurs.
Ransomware speed
Today's ransomware operates at machine speed, with adversaries moving from initial access to encryption at unprecdented speeds. Human analysts struggle to respond fast enough when reaction time must be measured in seconds for success.
AI-powered detection identifies the behavioral signatures of ransomware deployment, including unusual file access patterns, lateral movement, and encryption activity, enabling autonomous response to contain the threat before it spreads across the network. This speed is essential for minimizing damage and maintaining business continuity.
Supply chain visibility
Third-party vendors and trusted partners are a vulnerability that traditional tools often overlook. Adversaries target supply chain relationships to gain access to well-defended organizations through less-secure partners.
AI provides visibility into unusual activity originating from trusted external connections, identifying when a vendor account behaves differently than expected or when data flows deviate from established patterns. This scrutiny addresses a critical gap in conventional security approaches that implicitly trust authenticated third-party access.
Key benefits for security teams
The AI-powered SOC delivers measurable advantages that address the core challenges facing security operations today:
- Dramatically reducing alert fatigue: By filtering out benign anomalies and grouping related events, the system refers analysts to actionable, high-fidelity incidents rather than showing thousands of disconnected notifications.
- Speed and efficiency: The global average time to contain a data breach is 60 days, and the total average breach life cycle is 241 days. AI SOC reduces investigation time to minutes through automated correlation and contextualization that eliminates manual log pivoting.
- Closing the skills gap: AI acts as an "always-on" Level 1 analyst, allowing junior staff to perform at a higher level and senior staff to focus on complex threat hunting rather than routine triage.
Implementing an AI SOC strategy
Transitioning to an AI-enhanced security operations model requires careful planning to maximize value while managing organizational change. The following principles help security teams avoid common pitfalls and build a foundation for sustainable success.
Focus on integration
View SOC transformation as an evolution rather than a wholesale replacement. AI integrates with existing tools like Security Information and Event Management (SIEM) and Endpoint Detection and Response (EDR) platforms to enhance their value. Organizations achieve faster time-to-value by layering AI capabilities onto established security infrastructure rather than attempting to rebuild from scratch.
Implement a human-AI loop
The ideal implementation establishes human-machine teaming where AI handles data processing, initial analysis, and routine response while humans provide strategic oversight and final decision-making on critical incidents. This partnership leverages the strengths of both artificial and human intelligence, combining machine speed and scale with human judgment and contextual understanding.
Use a phased, risk-based approach
Successful implementation follows a structured progression:
- Phase 1: Establishes strong governance with a risk taxonomy and oversight committee before any deployment begins
- Phase 2: Introduces a proof of concept in low-risk areas where the organization can validate AI performance and build confidence
- Phase 3: Expands automation to high-risk tasks as trust develops and the AI demonstrates consistent accuracy
This measured approach manages organizational change while building the foundation for long-term success.
Learn more about SOC transformation
The AI SOC transformation represents a fundamental shift in how organizations approach security operations, combining machine speed with human expertise to address the scale and sophistication of today's cyber-threats.
Darktrace has pioneered AI-powered cybersecurity since 2013, developing technology that learns from your unique business data rather than relying on historical attack patterns. To continue exploring how AI transforms security operations, read the "Reimagining Your SOC" blog series.