What is a VPS and how are they abused?
A Virtual Private Server (VPS) is a virtualized server that provides dedicated resources and control to users on a shared physical device. VPS providers, long used by developers and businesses, are increasingly misused by threat actors to launch stealthy, scalable attacks. While not a novel tactic, VPS abuse is has seen an increase in Software-as-a-Service (SaaS)-targeted campaigns as it enables attackers to bypass geolocation-based defenses by mimicking local traffic, evade IP reputation checks with clean, newly provisioned infrastructure, and blend into legitimate behavior [3].
VPS providers like Hyonix and Host Universal offer rapid setup and minimal open-source intelligence (OSINT) footprint, making detection difficult [1][2]. These services are not only fast to deploy but also affordable, making them attractive to attackers seeking anonymous, low-cost infrastructure for scalable campaigns. Such attacks tend to be targeted and persistent, often timed to coincide with legitimate user activity, a tactic that renders traditional security tools largely ineffective.
Darktrace’s investigation into Hyonix VPS abuse
In May 2025, Darktrace’s Threat Research team investigated a series of incidents across its customer base involving VPS-associated infrastructure. The investigation began with a fleet-wide review of alerts linked to Hyonix (ASN AS931), revealing a noticeable spike in anomalous behavior from this ASN in March 2025. The alerts included brute-force attempts, anomalous logins, and phishing campaign-related inbox rule creation.
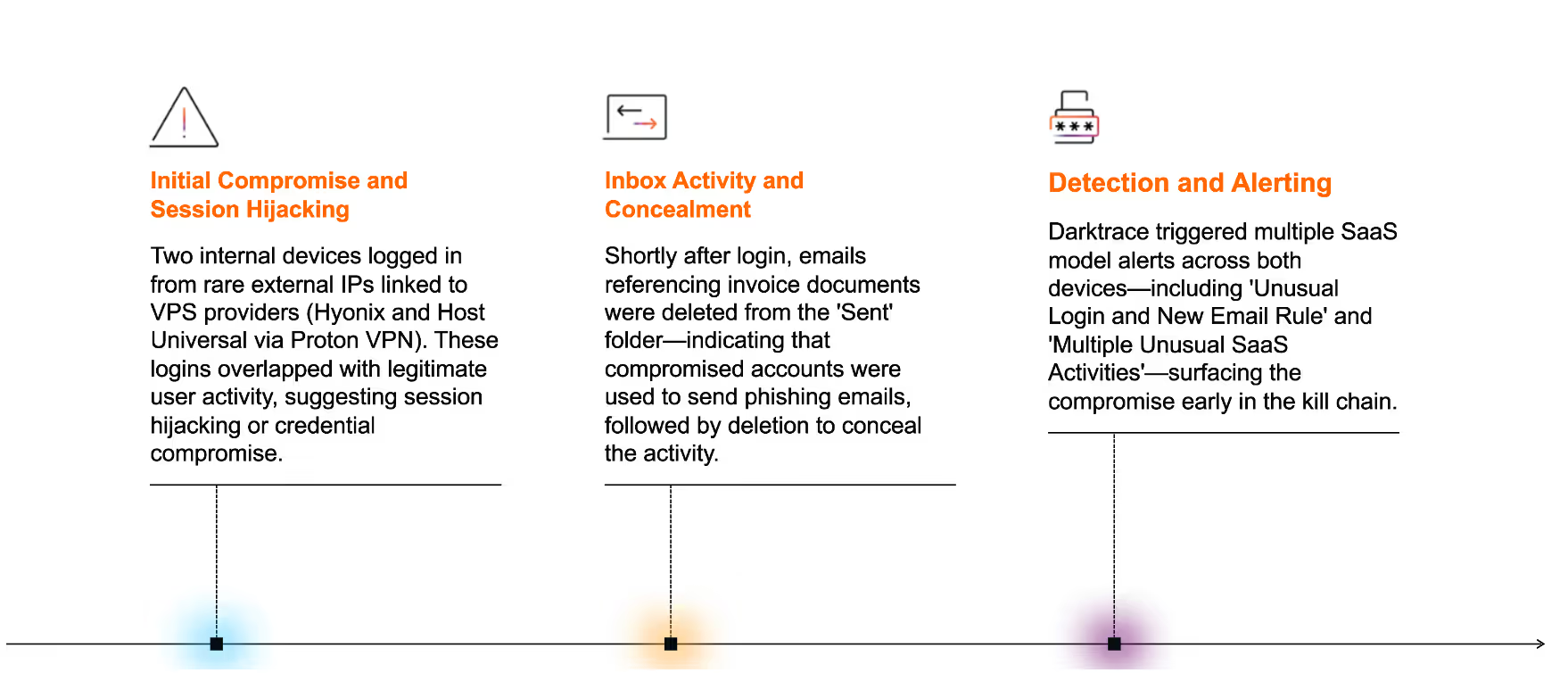
Darktrace identified suspicious activity across multiple customer environments around this time, but two networks stood out. In one instance, two internal devices exhibited mirrored patterns of compromise, including logins from rare endpoints, manipulation of inbox rules, and the deletion of emails likely used in phishing attacks. Darktrace traced the activity back to IP addresses associated with Hyonix, suggesting a deliberate use of VPS infrastructure to facilitate the attack.
On the second customer network, the attack was marked by coordinated logins from rare IPs linked to multiple VPS providers, including Hyonix. This was followed by the creation of inbox rules with obfuscated names and attempts to modify account recovery settings, indicating a broader campaign that leveraged shared infrastructure and techniques.
Darktrace’s Autonomous Response capability was not enabled in either customer environment during these attacks. As a result, no automated containment actions were triggered, allowing the attack to escalate without interruption. Had Autonomous Response been active, Darktrace would have automatically blocked connections from the unusual VPS endpoints upon detection, effectively halting the compromise in its early stages.
Case 1
Initial Intrusion
On May 19, 2025, Darktrace observed two internal devices on one customer environment initiating logins from rare external IPs associated with VPS providers, namely Hyonix and Host Universal (via Proton VPN). Darktrace recognized that these logins had occurred within minutes of legitimate user activity from distant geolocations, indicating improbable travel and reinforcing the likelihood of session hijacking. This triggered Darktrace / IDENTITY model “Login From Rare Endpoint While User Is Active”, which highlights potential credential misuse when simultaneous logins occur from both familiar and rare sources.
Shortly after these logins, Darktrace observed the threat actor deleting emails referring to invoice documents from the user’s “Sent Items” folder, suggesting an attempt to hide phishing emails that had been sent from the now-compromised account. Though not directly observed, initial access in this case was likely achieved through a similar phishing or account hijacking method.

Case 2
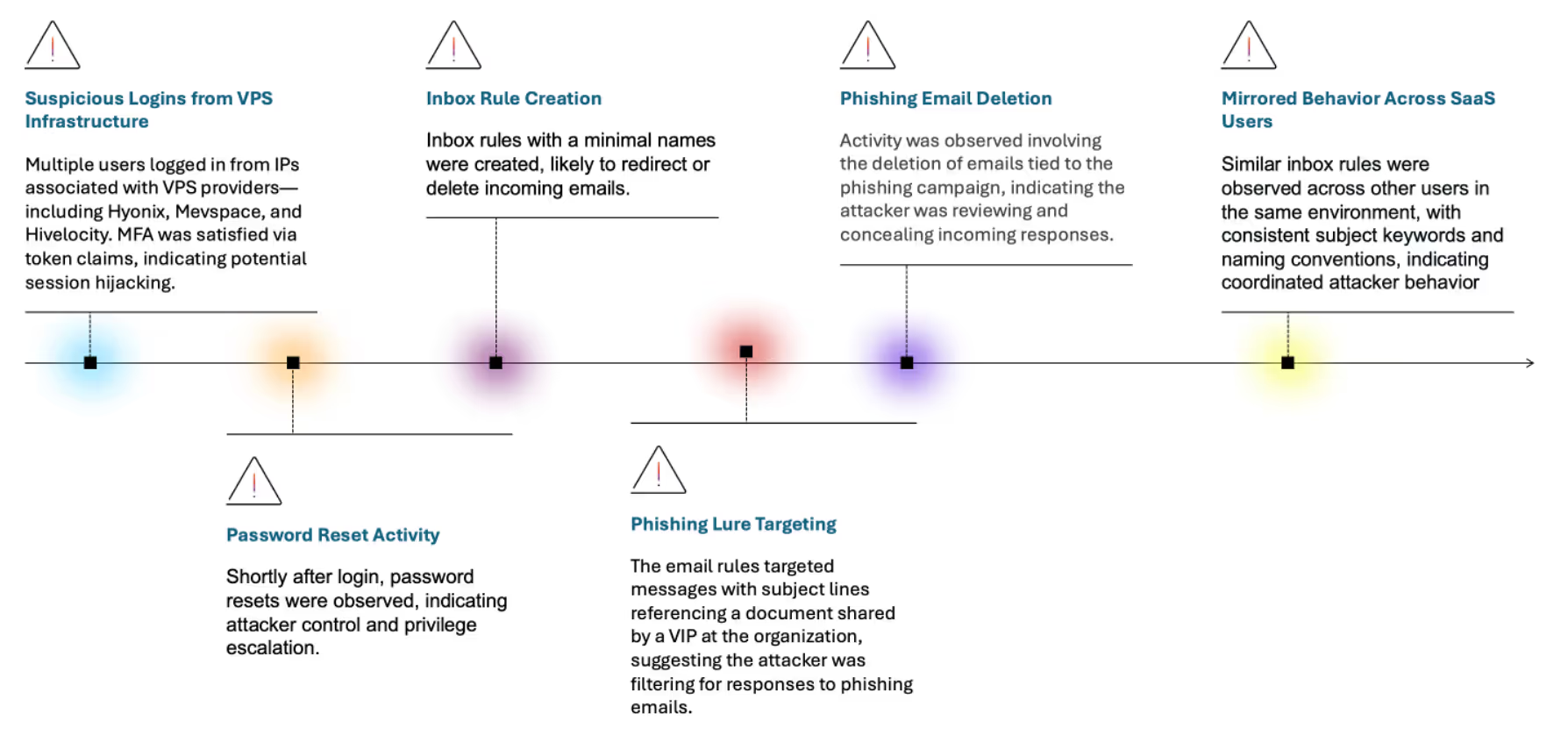
In the second customer environment, Darktrace observed similar login activity originating from Hyonix, as well as other VPS providers like Mevspace and Hivelocity. Multiple users logged in from rare endpoints, with Multi-Factor Authentication (MFA) satisfied via token claims, further indicating session hijacking.
Establishing control and maintaining persistence
Following the initial access, Darktrace observed a series of suspicious SaaS activities, including the creation of new email rules. These rules were given minimal or obfuscated names, a tactic often used by attackers to avoid drawing attention during casual mailbox reviews by the SaaS account owner or automated audits. By keeping rule names vague or generic, attackers reduce the likelihood of detection while quietly redirecting or deleting incoming emails to maintain access and conceal their activity.
One of the newly created inbox rules targeted emails with subject lines referencing a document shared by a VIP at the customer’s organization. These emails would be automatically deleted, suggesting an attempt to conceal malicious mailbox activity from legitimate users.
Mirrored activity across environments
While no direct lateral movement was observed, mirrored activity across multiple user devices suggested a coordinated campaign. Notably, three users had near identical similar inbox rules created, while another user had a different rule related to fake invoices, reinforcing the likelihood of a shared infrastructure and technique set.
Privilege escalation and broader impact
On one account, Darktrace observed “User registered security info” activity was shortly after anomalous logins, indicating attempts to modify account recovery settings. On another, the user reset passwords or updated security information from rare external IPs. In both cases, the attacker’s actions—including creating inbox rules, deleting emails, and maintaining login persistence—suggested an intent to remain undetected while potentially setting the stage for data exfiltration or spam distribution.
On a separate account, outbound spam was observed, featuring generic finance-related subject lines such as 'INV#. EMITTANCE-1'. At the network level, Darktrace / NETWORK detected DNS requests from a device to a suspicious domain, which began prior the observed email compromise. The domain showed signs of domain fluxing, a tactic involving frequent changes in IP resolution, commonly used by threat actors to maintain resilient infrastructure and evade static blocklists. Around the same time, Darktrace detected another device writing a file named 'SplashtopStreamer.exe', associated with the remote access tool Splashtop, to a domain controller. While typically used in IT support scenarios, its presence here may suggest that the attacker leveraged it to establish persistent remote access or facilitate lateral movement within the customer’s network.
Conclusion
This investigation highlights the growing abuse of VPS infrastructure in SaaS compromise campaigns. Threat actors are increasingly leveraging these affordable and anonymous hosting services to hijack accounts, launch phishing attacks, and manipulate mailbox configurations, often bypassing traditional security controls.
Despite the stealthy nature of this campaign, Darktrace detected the malicious activity early in the kill chain through its Self-Learning AI. By continuously learning what is normal for each user and device, Darktrace surfaced subtle anomalies, such as rare login sources, inbox rule manipulation, and concurrent session activity, that likely evade traditional static, rule-based systems.
As attackers continue to exploit trusted infrastructure and mimic legitimate user behavior, organizations should adopt behavioral-based detection and response strategies. Proactively monitoring for indicators such as improbable travel, unusual login sources, and mailbox rule changes, and responding swiftly with autonomous actions, is critical to staying ahead of evolving threats.
Credit to Rajendra Rushanth (Cyber Analyst), Jen Beckett (Cyber Analyst) and Ryan Traill (Analyst Content Lead)
References
· 1: https://cybersecuritynews.com/threat-actors-leveraging-vps-hosting-providers/
· 2: https://threatfox.abuse.ch/asn/931/
· 3: https://www.cyfirma.com/research/vps-exploitation-by-threat-actors/
Appendices
Darktrace Model Detections
• SaaS / Compromise / Unusual Login, Sent Mail, Deleted Sent
• SaaS / Compromise / Suspicious Login and Mass Email Deletes
• SaaS / Resource / Mass Email Deletes from Rare Location
• SaaS / Compromise / Unusual Login and New Email Rule
• SaaS / Compliance / Anomalous New Email Rule
• SaaS / Resource / Possible Email Spam Activity
• SaaS / Unusual Activity / Multiple Unusual SaaS Activities
• SaaS / Unusual Activity / Multiple Unusual External Sources For SaaS Credential
• SaaS / Access / Unusual External Source for SaaS Credential Use
• SaaS / Compromise / High Priority Login From Rare Endpoint
• SaaS / Compromise / Login From Rare Endpoint While User Is Active
List of Indicators of Compromise (IoCs)
Format: IoC – Type – Description
• 38.240.42[.]160 – IP – Associated with Hyonix ASN (AS931)
• 103.75.11[.]134 – IP – Associated with Host Universal / Proton VPN
• 162.241.121[.]156 – IP – Rare IP associated with phishing
• 194.49.68[.]244 – IP – Associated with Hyonix ASN
• 193.32.248[.]242 – IP – Used in suspicious login activity / Mullvad VPN
• 50.229.155[.]2 – IP – Rare login IP / AS 7922 ( COMCAST-7922 )
• 104.168.194[.]248 – IP – Rare login IP / AS 54290 ( HOSTWINDS )
• 38.255.57[.]212 – IP – Hyonix IP used during MFA activity
• 103.131.131[.]44 – IP – Hyonix IP used in login and MFA activity
• 178.173.244[.]27 – IP – Hyonix IP
• 91.223.3[.]147 – IP – Mevspace Poland, used in multiple logins
• 2a02:748:4000:18:0:1:170b[:]2524 – IPv6 – Hivelocity VPS, used in multiple logins and MFA activity
• 51.36.233[.]224 – IP – Saudi ASN, used in suspicious login
• 103.211.53[.]84 – IP – Excitel Broadband India, used in security info update
MITRE ATT&CK Mapping
Tactic – Technique – Sub-Technique
• Initial Access – T1566 – Phishing
T1566.001 – Spearphishing Attachment
• Execution – T1078 – Valid Accounts
• Persistence – T1098 – Account Manipulation
T1098.002 – Exchange Email Rules
• Command and Control – T1071 – Application Layer Protocol
T1071.001 – Web Protocols
• Defense Evasion – T1036 – Masquerading
• Defense Evasion – T1562 – Impair Defenses
T1562.001 – Disable or Modify Tools
• Credential Access – T1556 – Modify Authentication Process
T1556.004 – MFA Bypass
• Discovery – T1087 – Account Discovery
• Impact – T1531 – Account Access Removal
The content provided in this blog is published by Darktrace for general informational purposes only and reflects our understanding of cybersecurity topics, trends, incidents, and developments at the time of publication. While we strive to ensure accuracy and relevance, the information is provided “as is” without any representations or warranties, express or implied. Darktrace makes no guarantees regarding the completeness, accuracy, reliability, or timeliness of any information presented and expressly disclaims all warranties.
Nothing in this blog constitutes legal, technical, or professional advice, and readers should consult qualified professionals before acting on any information contained herein. Any references to third-party organizations, technologies, threat actors, or incidents are for informational purposes only and do not imply affiliation, endorsement, or recommendation.
Darktrace, its affiliates, employees, or agents shall not be held liable for any loss, damage, or harm arising from the use of or reliance on the information in this blog.
The cybersecurity landscape evolves rapidly, and blog content may become outdated or superseded. We reserve the right to update, modify, or remove any content without notice.