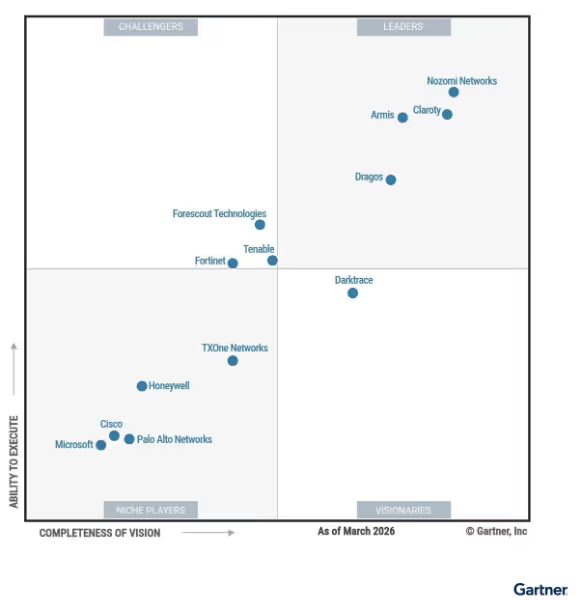
Gartner® Magic Quadrant™ for CPS Protection Platformsは、この急激に変化する市場を形成するベンダーについての独立した見解を提供するものであり、各プロバイダーがますます接続の進むOT(Operational Technology)およびサイバーフィジカル環境に関連するサイバーセキュリティリスクの解決をどのように支援しているかを評価するものです。セキュリティおよびリスク管理のリーダー達はこの調査結果を使用してベンダーの位置づけを理解し、CPS(Cyber Physical System)セキュリティ戦略の最新化に向けた判断の参考にしています。CPSセキュリティプラットフォームを評価されている組織の方はレポート全体をレビューし、この市場についての包括的な視点を得られることをお勧めします。
ダークトレースが2回連続して唯一のVisionaryに位置付けられたことは、CPSセキュリティに対する当社のイノベーション、製品展開および長期戦略の強みを裏付けていると捉えています。
Darktrace / OTは現代の産業環境の防御、そしてIT、OT、およびIoTが統合された環境の保護の現実に対処するために構築されており、自己学習型AIを適用して既知、未知、および新手の脅威を検知し、調査を加速するとともに運用上の影響に基づいてリスクの優先付けを行います。この独自のアプローチが重要インフラを担う複雑な組織が必要とする柔軟な展開モデルを支えています。
CPSセキュリティでDarktrace/ OTが傑出している理由
産業用環境と企業インフラの統合が引き続き進むなかで、セキュリティリーダーは従来のセキュリティアプローチではアップタイム、安全性、規制要件への対応が難しいシステムのサイバーリスクの削減を求められています。セキュリティチームは環境内でどのようにリスクが発生するかを理解し、より迅速かつ明確性を持って脅威を調査し、運用への影響に基づいて対処を優先付けなければなりません。
Darktrace / OTはその課題のために設計されています。クロスドメインの可視性、検知、調査を、自己学習型AI、CVEを超えた専用のリスク管理、そしてセキュリティの成果とオペレーションのレジリエンスを両立させる、OTのためのワークフローを組み合わせたソリューションです。
統合されたCPS環境全体に一元的な可視性
重要インフラは従来のOTネットワークを超えて拡大し、エンジニアリングワークステーション、HMI、リモートアクセス、企業システム、クラウドにリンクされたアーキテクチャも含まれるようになっており、セキュリティチームはアセット間の関係、依存関係がどこに存在しているか、そして複数のドメインにわたり露出がどのように生じるかを理解する必要があります。
Darktrace / OTはOT、IT、IoT、IoMTにわたる一元的な可視性を提供し、コネクテッド環境内のサイバーリスクに対する理解を助けます。Operational Overview,、OTワークフロー、プロトコルに対する深いレベルの検査等の機能を通じてテレメトリーを組み合わせることにより、Darktraceはエンジニアとセキュリティチームが共通のコンテキストを使用し、防御する環境についてのよりOTに即した理解に基づいて作業することを可能にします。
自己学習型AIにより強化された脅威検知、調査、対応
シグネチャは既知の脅威に対しては依然として価値を提供しますが、内部関係者による不正使用、ゼロデイエクスプロイト、および標的を絞った作戦のためにカスタム構築されたマルウェアには対応できません。Darktrace / OTは自己学習型AIを使用して、既知のマルウェアよりも異常な通信、正当なアクセスの誤用、または疑わしいデバイスの挙動を通じて脅威が現れることが多い産業用環境全体において、正常な行動からの微妙な逸脱を検出します。インシデント調査を強化するために、DarktraceのCyber AI Analystは自動的にアクティビティを相関付け、コンテキストに基づくサマリーを生成して人手によるトリアージ作業を削減し、チームはアラートの発生からインシデントの理解へ、より迅速に進むことができます。
Darktrace / OTは、NEXTfor OTを通じた拡張テレメトリーにより調査と対応をさらに強化し、エンジニアリングワークステーションやHMIなどの運用エンドポイントへの可視性を拡大して、より深い根本原因分析をサポートします。自己学習型AIを活用することで、Darktraceは異常なアクティビティをピンポイントで封じ込めつつ産業プロセスの正常な稼働を維持する、自律遮断も可能にしています。対応アクションはデバイス、デバイス種別、またはネットワークセグメントごとにカスタマイズでき、完全に自律的なアクションの実行や、人間の確認を含むワークフローなどのオプションを選択可能です。これにより、セキュリティチームはオペレーションの中断を削減すると同時に、対応の判断に対するコントロールを維持できます。
オペレーションへの影響に基づく、コンテキストを考慮した優先付け
セキュリティチームが受け身の防御からセキュリティ体制についての積極的な思考へシフトするには適切なツールが必要です。しかしほとんどのOTチームは産業用システムを理解していないIT中心型のツールに縛られ、静的なCVEリストに常に圧倒されています。そしてこれらのツールはOT専用のプロトコルへの理解が欠けています。
Darktrace / OTはオペレーションのコンテキストに基づいてサイバーリスクを優先付けることにより、静的な脆弱性リストを超えた防御を可能にします。アセットの重要性、ネットワークの関係、エクスプロイト可能性についてのインテリジェンス、動作のテレメトリー、攻撃経路分析を取り込むことにより、Darktrace / OTはどの露出がオペレーションに現実的に影響を与える可能性があるかを理解するのに役立ちます。CVE深刻度、KEVデータ、MITREテクニック、ビジネスへの影響を相関付けることにより、Darktraceはオペレーションのレジリエンス、ガバナンス、そしてIEC-62443等のコンプライアンスの取り組みを支持する、より焦点を絞った修正の判断を可能にします。
現実の環境と企業システムとの整合性を考えた設計
Darktrace / OTは、産業用環境の現実、つまり、オンプレミス、ハイブリッド、分散、エアギャップを含むさまざまな、オペレーションに重要な影響を与えるネットワークへの柔軟な展開が欠かせない産業用環境のために設計されています。Darktrace / OTはSIEM、SOAR、CMDB、ファイアウォール、およびガバナンスツールを含むエンタープライズセキュリティエコシステムとも統合が可能で、幅広いセキュリティワークフローをサポートしています。これにより産業用環境の制約も尊重しつつOTセキュリティをエンタープライズプログラムと整合させ、セキュリティチームとエンジニアリングチーム間のコラボレーションを促進することができます。
お客様の評価とプラットフォームの認知
過去12か月間に、Darktrace / OTはGartner Peer Insights*において4.8/5の評価(37 Reviewsに基づく)を受け、このことは重要インフラおよび産業用環境におけるお客様のこのプラットフォームに対する強い支持を裏付けているものと確信しています。
この評価に加え、ダークトレースは Network Detection and Response (NDR) およびEmail Security Platforms,部門でのLeaderの評価を含むGartner Magic Quadrantsの複数の部門において評価を受けており、このことはダークトレースの ActiveAI Security Platformの幅広さを表しています。

CPSセキュリティの未来を拓く
ダークトレースが2年連続して唯一のVisionaryに位置付けられたことは、当社の明確な方向性を反映していると考えます:つまりCPSセキュリティプラットフォームはお客様が可視性を調査につなげ、調査を優先付けにつなげ、優先付けを実際の運用上の成果につなげるのを支援する必要があるということです。
このことは引き続き Darktrace / OT の目標です。
産業用環境がより接続され、より複雑化し、よりビジネスにとって決定的なものとなるなかで、ダークトレースはこれからもお客様が不確実性を解消し、レジリエンスを強化し、稼働を維持しつづけるシステムを保護するのに役立つ機能に投資を続けます。
- Gartner Magic Quadrant for CPS Protection Platformsレポート全文をダウンロード
- デモを予約してDarktrace / OTの実際の動作をご覧ください
Gartner, Magic Quadrant for CPS Protection Platforms, Katell Thielemann,Ruggero Contu, Wam Voster, Sumit Rajput, 3 March 2026
Gartner®, Peer Insights™, Darktrace in CPS Protection Platforms, as of March 26, 2026
https://www.gartner.com/reviews/product/darktraceot
Gartner免責事項
GARTNER, MAGIC QUADRANTおよびPEER INSIGHTSは、Gartner Inc.または関連会社の米国およびその他の国における登録商標およびサービスマークであり、同社の許可に基づいて使用しています。All rights reserved.
Gartnerは、Gartnerリサーチの発行物に掲載された特定のベンダー、製品またはサービスを推奨するものではありません。また、最高のレーティング又はその他の評価を得たベンダーのみを選択するようにテクノロジーユーザーに助言するものではありません。Gartnerリサーチの発行物は、Gartnerリサーチの見解を表したものであり、事実を表現したものではありません。Gartnerは、明示または黙示を問わず、本リサーチの商品性や特定目的への適合性を含め、一切の責任を負うものではありません。
Gartner Peer Insightsのコンテンツは、個々のエンドユーザー自身の経験による主観的な意見が集約されたものであり、Gartnerまたはその関連会社の見解を表すものではありません。Gartnerは、Gartner Peer Insightsに掲載された特定のベンダー、製品またはサービスを推奨するものではありません。Gartnerは、商品性または特定目的への適合性の保証を含む、その正確性または完全性について、本コンテンツの内容に関する一切の責任を、明示または黙示を問わず負うものではありません。
この図表は、Gartner, Inc.がリサーチの一部として公開したものであり、文書全体のコンテクストにおいて評価されるべきものです。オリジナルのGartnerドキュメントは、リクエストによりDarktraceからご提供することが可能です。



















