Why Black Friday Drives a Surge in Phishing Attacks
In recent years, Black Friday has shifted from a single day of online retail sales and discounts to an extended ‘Black Friday Week’, often preceded by weeks of online hype. During this period, consumers are inundated with promotional emails and marketing campaigns as legitimate retailers compete for attention.
Unsurprisingly, this surge in legitimate communications creates an ideal environment for threat actors to launch targeted phishing campaigns designed to mimic legitimate retail emails. These campaigns often employ social engineering techniques that exploit urgency, exclusivity, and consumer trust in well-known brands, tactics designed to entice recipients into opening emails and clicking on malicious links.
Additionally, given the seasonal nature of Black Friday and the ever-changing habits of consumers, attackers adopt new tactics and register fresh domains each year, rather than reusing domains previously flagged as spam or phishing endpoints. While this may pose a challenge for traditional email security tools, it presents no such difficulty for Darktrace / EMAIL and its anomaly-based approach.
In the days and weeks leading up to ‘Black Friday’, Darktrace observed a spike in sophisticated phishing campaigns targeting consumers, demonstrating how attackers combine phycological manipulation with technical evasion to bypass basic security checks during this high-traffic period. This blog showcases several notable examples of highly convincing phishing emails detected and contained by Darktrace / EMAIL in mid to late November 2025.
Darktrace’s Black Friday Detections
Brand Impersonation: Deal Watchdogs’ Amazon Deals
The impersonation major online retailers has become a common tactic in retail-focused attacks, none more so than Amazon, which ranked as the fourth most impersonated brand in 2024, only behind Microsoft, Apple, Google, and Facebook [1]. Darktrace’s own research found Amazon to be the most mimicked brand, making up 80% of phishing attacks in its analysis of global consumer brands.
When faced with an email that appears to come from a trusted sender like Amazon, recipients are far more likely to engage, increasing the success rate of these phishing campaigns.
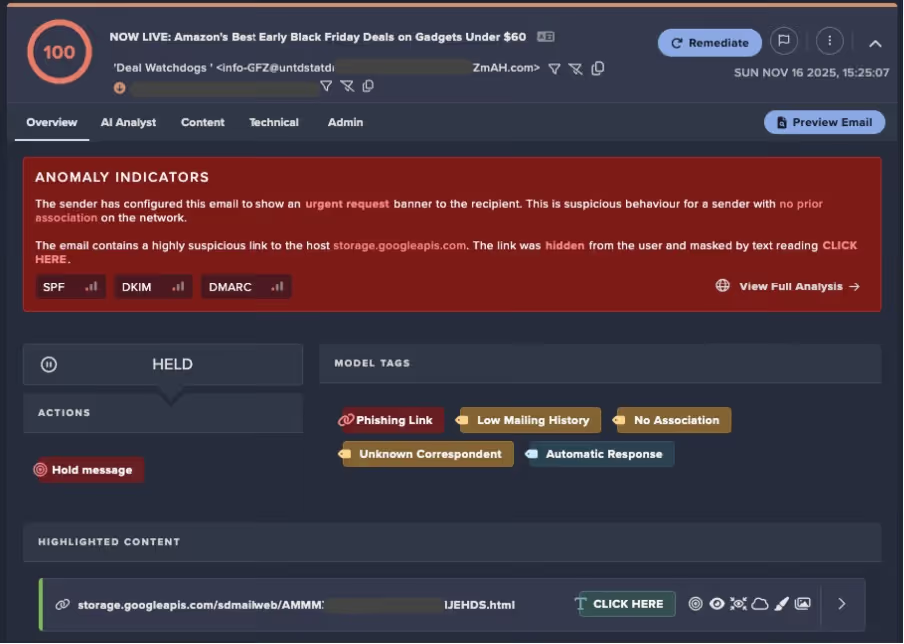
In one case observed on November 16, Darktrace detected an email with the subject line “NOW LIVE: Amazon’s Best Early Black Friday Deals on Gadgets Under $60”. The email was sent to a customer by the sender ‘Deal Watchdogs’, in what appeared to be an attempt to masquerade as a legitimate discount-finding platform. No evidence indicated that the company was legitimate. In fact, the threat actor made no attempt to create a convincing name, and the domain appeared to be generated by a domain generation algorithm (DGA), as shown in Figure 2.
Although the email was sent by ‘Deal Watchdogs’, it attempted to impersonate Amazon by featuring realistic branding, including the Amazon logo and a shade of orange similar to that used by them for the ‘CLICK HERE’ button and headline text.

Darktrace identified that the email, marked as urgent by the sender, contained a suspicious link to a Google storage endpoint (storage.googleapis[.]com), which had been hidden by the text “CLICK HERE”. If clicked, the link could have led to a credential harvester or served as a delivery vector for a malicious payload hosted on the Google storage platform.
Fortunately, Darktrace immediately identified the suspicious nature of this email and held it before delivery, preventing recipients from ever receiving or interacting with the malicious content.
Around the same time, Darktrace detected a similar email attempting to spoof Amazon on another customer’s network with the subject line “Our 10 Favorite Deals on Amazon That Started Today”, also sent by ‘Deal Watchdogs,’ suggesting a broader campaign.
Analysis revealed that this email originated from the domain petplatz[.]com, a fake marketing domain previously linked to spam activity according to open-source intelligence (OSINT) [2].
Brand Impersonation: Louis Vuitton
A few days later, on November 20, Darktrace / EMAIL detected a phishing email attempting to impersonate the luxury fashion brand Louis Vuitton. At first glance, the email, sent under the name ‘Louis Vuitton’ and titled “[Black Friday 2025] Discover Your New Favorite Louis Vuitton Bag – Elegance Starts Here”, appeared to be a legitimate Black Friday promotion. However, Darktrace’s analysis uncovered several red flags indicating a elaborate brand impersonation attempt.
The email was not sent by Louis Vuitton but by rskkqxyu@bookaaatop[.]ru, a Russia-based domain never before observed on the customer’s network. Darktrace flagged this as suspicious, noting that .ru domains were highly unusual for this recipient’s environment, further reinforcing the likelihood of malicious intent. Subsequent analysis revealed that the domain had only recently registered and was flagged as malicious by multiple OSINT sources [3].
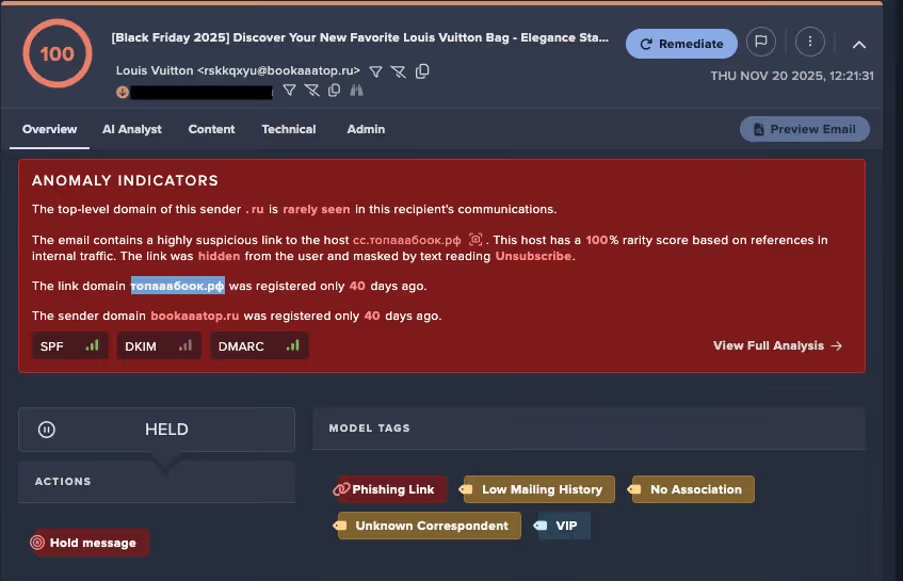
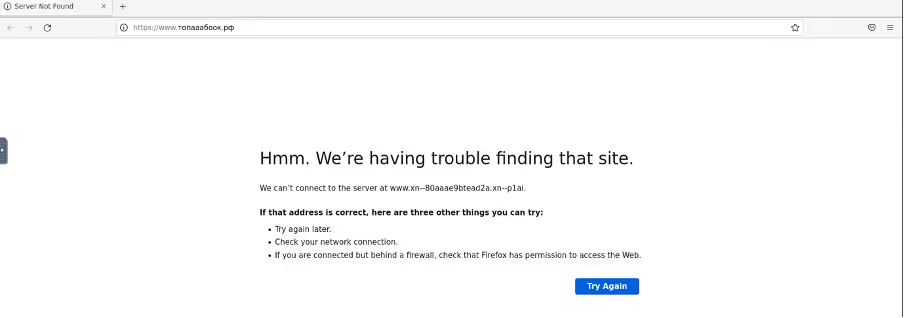
Darktrace further noted that the email contained a highly suspicious link hidden behind the text “View Collection” and “Unsubscribe,” ensuring that any interaction, whether visiting the supposed ‘handbag store’ or attempting to opt out of marketing emails, would direct recipients to the same endpoint. The link resolved to xn--80aaae9btead2a[.]xn--p1ai (топааабоок[.]рф), a domain confirmed as malicious by multiple OSINT sources [4]. At the time of analysis, the domain was inaccessible, likely due to takedown efforts or the short-lived nature of the campaign.
Darktrace / EMAIL blocked this email before it reached customer inboxes, preventing recipients from interacting with the malicious content and averting any disruption.
Too good to be true?
Aside from spoofing well-known brands, threat actors frequently lure consumers with “too good to be true” luxury offers, a trend Darktrace observed in multiple cases throughout November.
In one instance, Darktrace identified an email with the subject line “[Black Friday 2025] Luxury Watches Starting at $250.” Emails contained a malicious phishing link, hidden behind text like “Rolex Starting from $250”, “Shop Now”, and “Unsubscribe”.
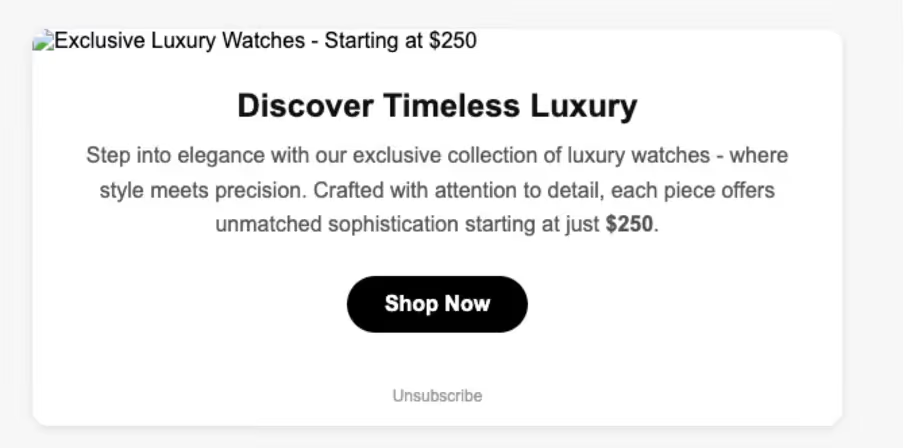
Similarly to the Louis Vuitton email campaign described above, this malicious link led to a .ru domain (hxxps://x.wwwtopsalebooks[.]ru/.../d65fg4er[.]html), which had been flagged as malicious by multiple sources [5].
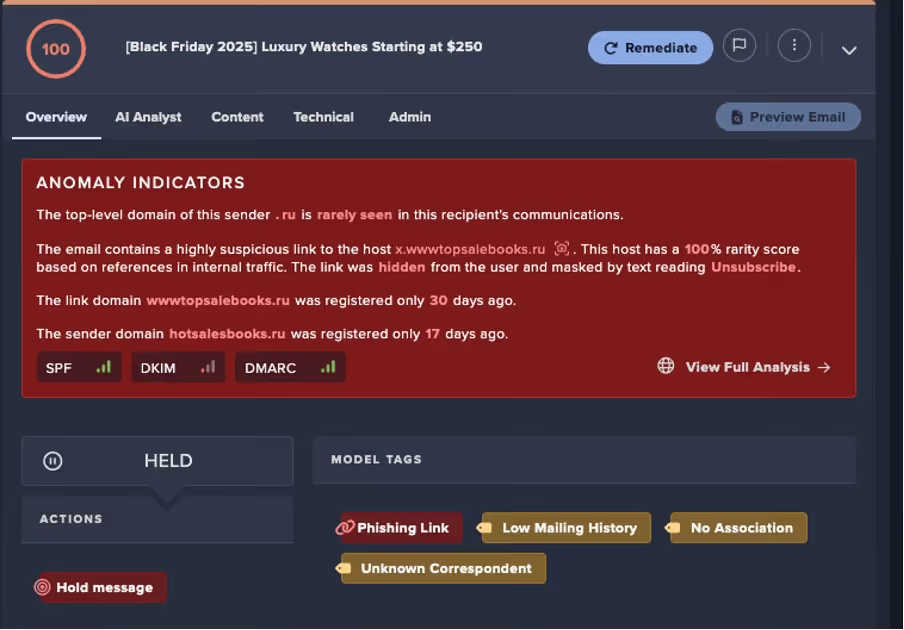
If accessed, this domain would redirect users to luxy-rox[.]com, a recently created domain (15 days old at the time of writing) that has also been flagged as malicious by OSINT sources [6]. When visited, the redirect domain displayed a convincing storefront advertising high-end watches at heavily discounted prices.
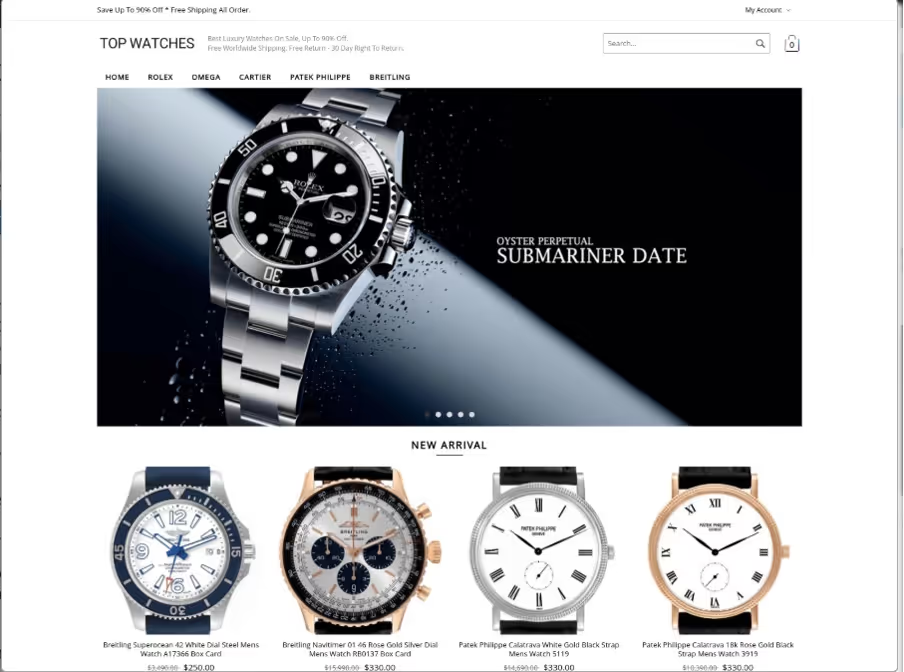
Although the true intent of this domain could not be confirmed, it was likely a scam site or a credential-harvesting operation, as users were required to create an account to complete a purchase. As of the time or writing, the domain in no longer accessible .
This email illustrates a layered evasion tactic: attackers employed multiple domains, rapid domain registration, and concealed redirects to bypass detection. By leveraging luxury branding and urgency-driven discounts, the campaign sought to exploit seasonal shopping behaviors and entice victims into clicking.
Staying Protected During Seasonal Retail Scams
The investigation into these Black Friday-themed phishing emails highlights a clear trend: attackers are exploiting seasonal shopping events with highly convincing campaigns. Common tactics observed include brand impersonation (Amazon, Louis Vuitton, luxury watch brands), urgency-driven subject lines, and hidden malicious links often hosted on newly registered domains or cloud services.
These campaigns frequently use redirect chains, short-lived infrastructure, and psychological hooks like exclusivity and luxury appeal to bypass user scepticism and security filters. Organizations should remain vigilant during retail-heavy periods, reinforcing user awareness training, link inspection practices, and anomaly-based detection to mitigate these evolving threats.
Credit to Ryan Traill (Analyst Content Lead) and Owen Finn (Cyber Analyst)
Appendices
References
1. https://keepnetlabs.com/blog/top-5-most-spoofed-brands-in-2024
2. https://www.virustotal.com/gui/domain/petplatz.com
3. https://www.virustotal.com/gui/domain/bookaaatop.ru
4. https://www.virustotal.com/gui/domain/xn--80aaae9btead2a.xn--p1ai
6. https://www.virustotal.com/gui/domain/luxy-rox.com
Indicators of Compromise (IoCs)
IoC – Type – Description + Confidence
petplatz[.]com – Hostname – Spam domain
bookaaatop[.]ru – Hostname – Malicious Domain
xn--80aaae9btead2a[.]xn--p1ai (топааабоок[.]рф) – Hostname - Malicious Domain
hxxps://x.wwwtopsalebooks[.]ru/.../d65fg4er[.]html) – URL – Malicious Domain
luxy-rox[.]com – Hostname - Malicious Domain
MITRE ATT&CK Mapping
Tactic – Technique – Sub-Technique
Initial Access - Phishing – (T1566)






























.jpg)







%201.png)