In January 2021, it was lauded that an international collaborative law enforcement operation had successfully dismantled Emotet’s infrastructure. This was one of the most prolific malware and banking Trojans which led to sensitive data loss, significant financial loss and reputational damage for its victims since early deployment in 2014.1
However, since November 2021, there have been signs of Emotet’s resurgence. Emotet has supposedly leveraged its former partner operators such as Trickbot, also discussed in another Darktrace blog, to rebuild its infrastructure by using already infected machines to download the new Emotet binary.2
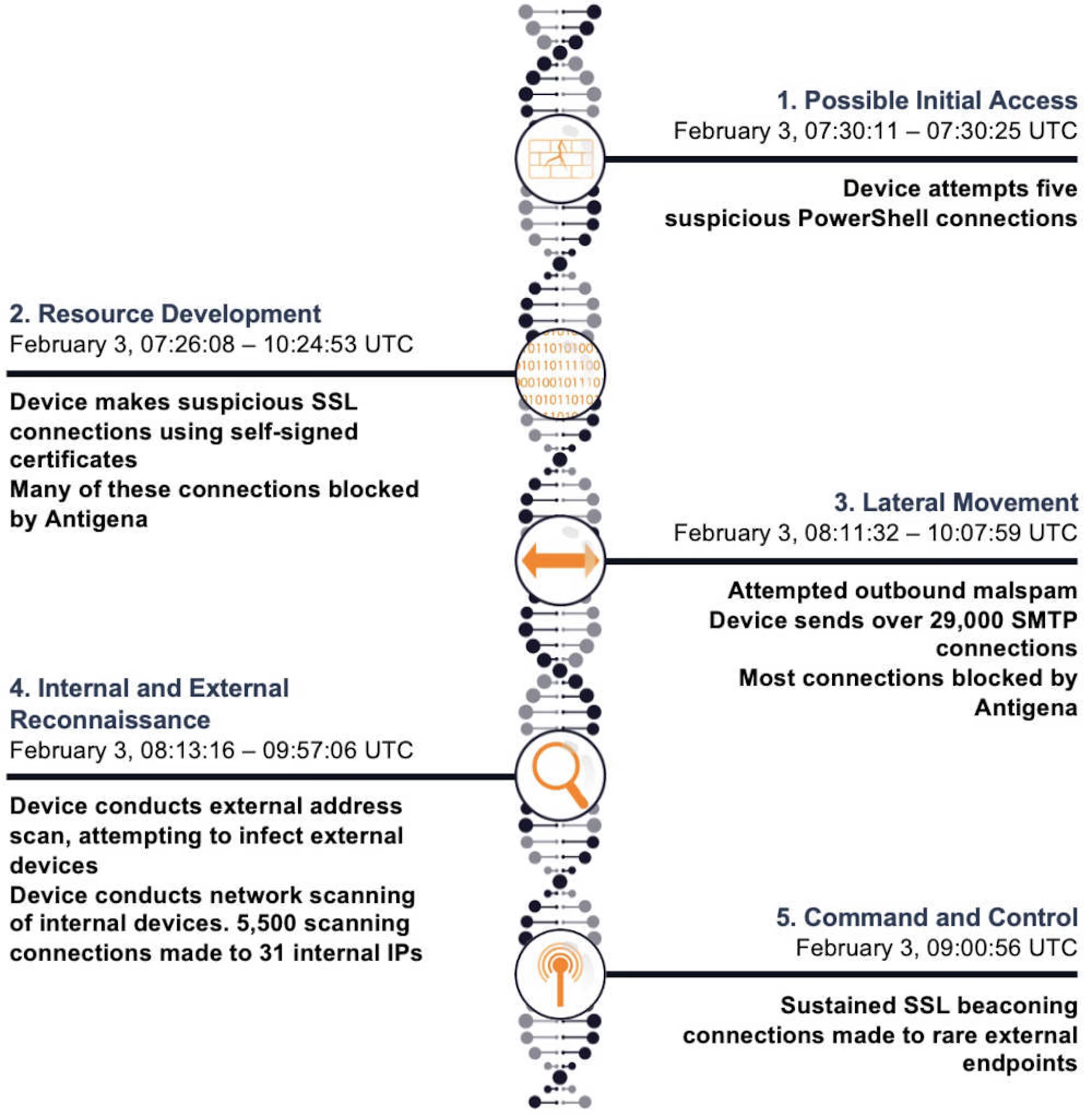
Early signs of Emotet’s return appear to be synonymous with its original kill chain and attack vectors. Malware is deployed, compromising a device as a zombie machine. This device is then used to send outbound malspam campaigns. These campaigns can be masked as application installer packages or fake reply email chains to give the spam credibility. Once the malware spreads through this spam, it then attempts to infect other devices – both internally and outbound in other networks.3
In February 2022, Darktrace detected elements of this kill chain in a customer’s environment, notably observing the large volume of SMTP connections which are characteristic of an outbound spam campaign.
Bypassing the rest of the security stack
The attack used Living-off-the-Land techniques by making PowerShell connections via pre-existing user agents within the network. As PowerShell connections can be used for legitimate reasons, this activity appeared to bypass the rest of the customer’s security stack and was likely seen as approved by their tools. However, Darktrace detected that the device was using the PowerShell user agent to connect to an external location. This is rare in comparison to wider network behavior.
The customer’s pre-existing security did not block the outgoing SMTP connections made by the compromised device on unusual ports. However, Darktrace Antigena blocked 71% of outgoing connections on mail ports 25 and 587, significantly reducing the scale of the spam dissemination.
Darktrace insights and services
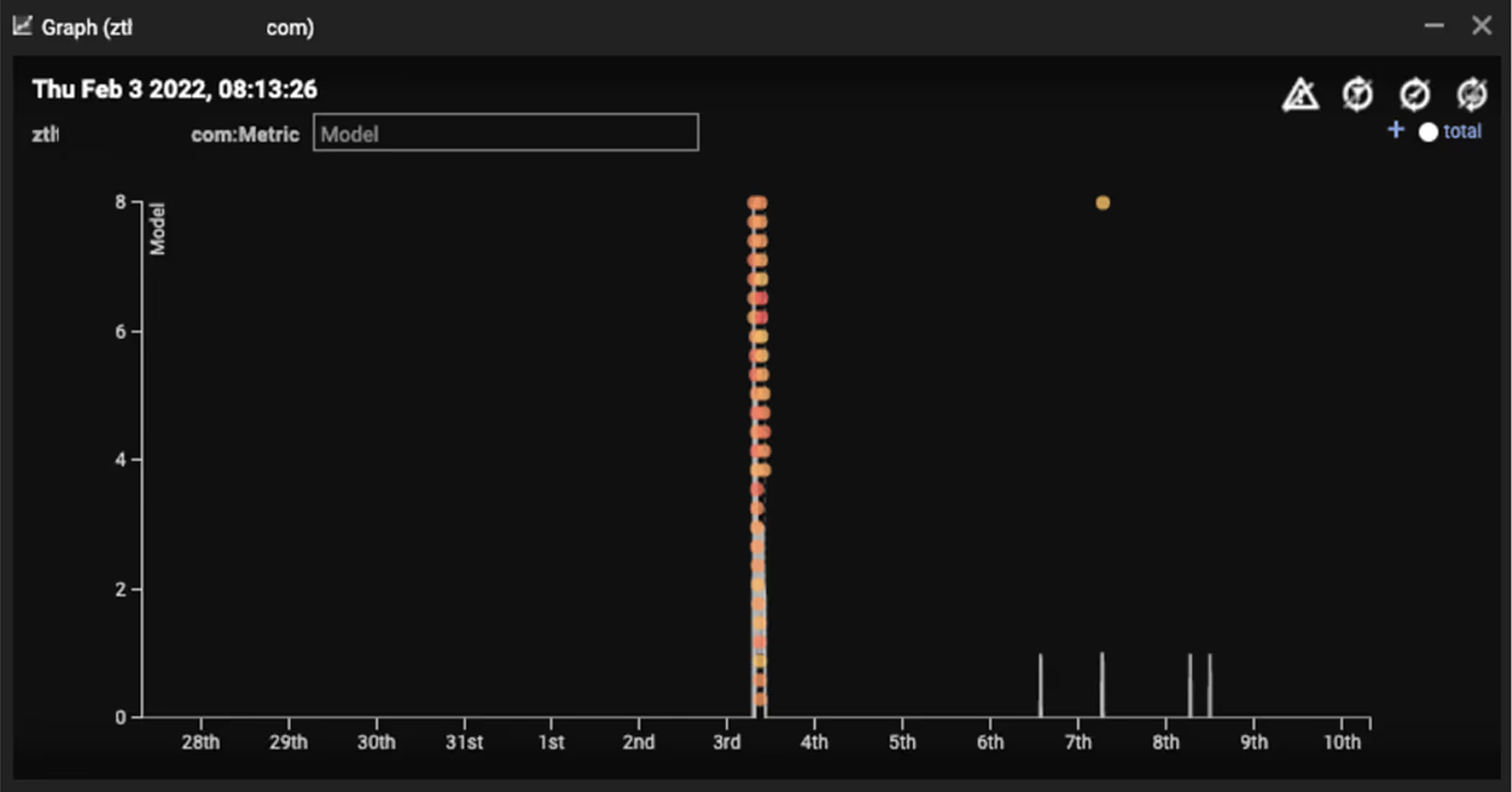
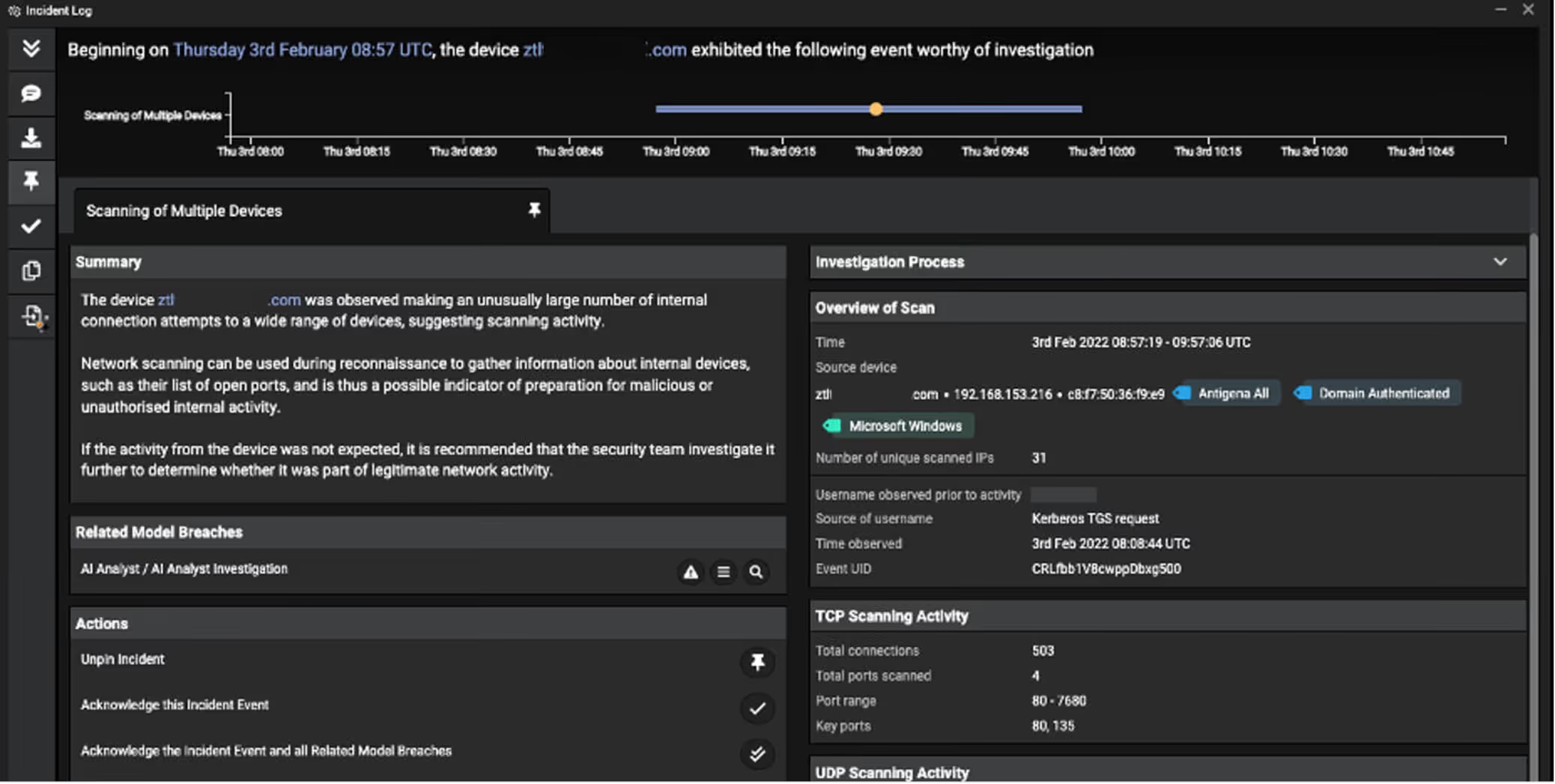
Darktrace quickly detected a range of anomalous behaviors from the new PowerShell use, uptake in C2 beaconing activity and spam. This can be highlighted via the spike in model breaches (Figure 3). Darktrace’s Cyber AI Analyst also launched an investigation into the device’s suspicious network scanning activity. This was essential for generating an incident summary which outlined the investigation process and technical details needed for the organization’s security team to act quickly (Figure 4).
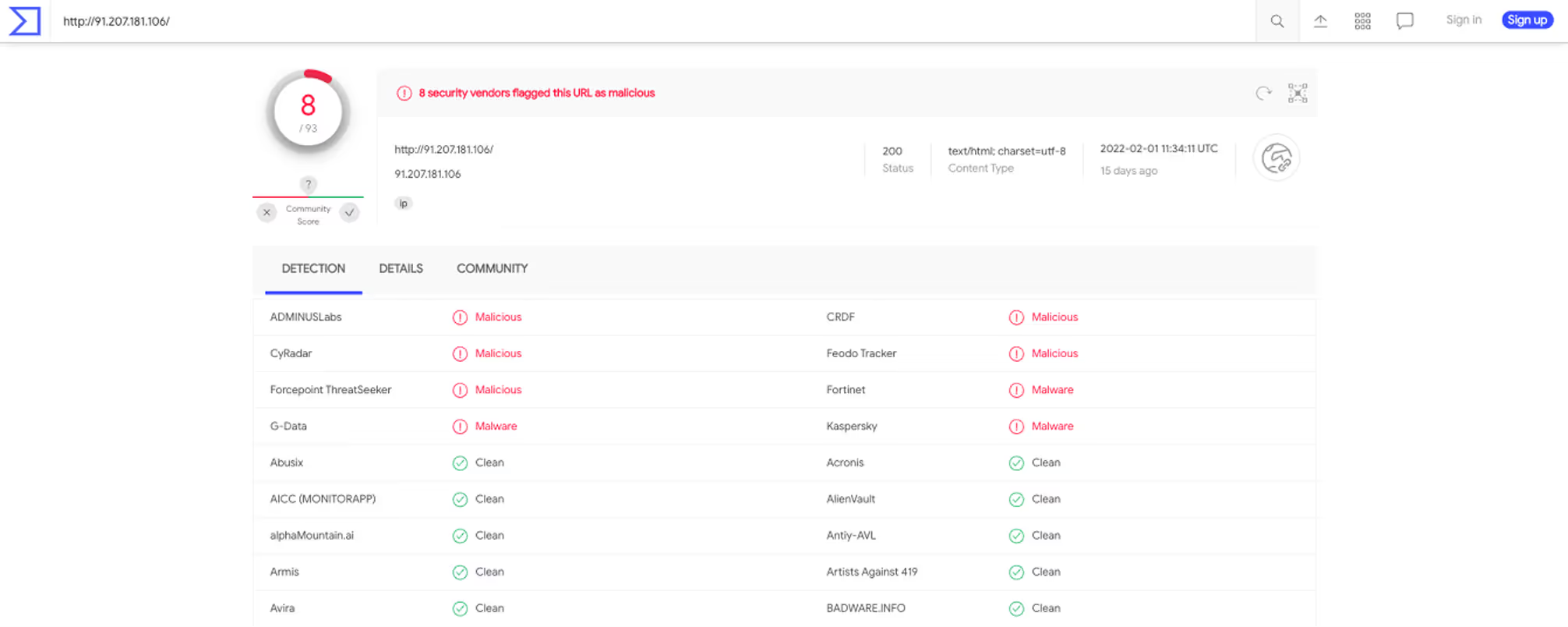
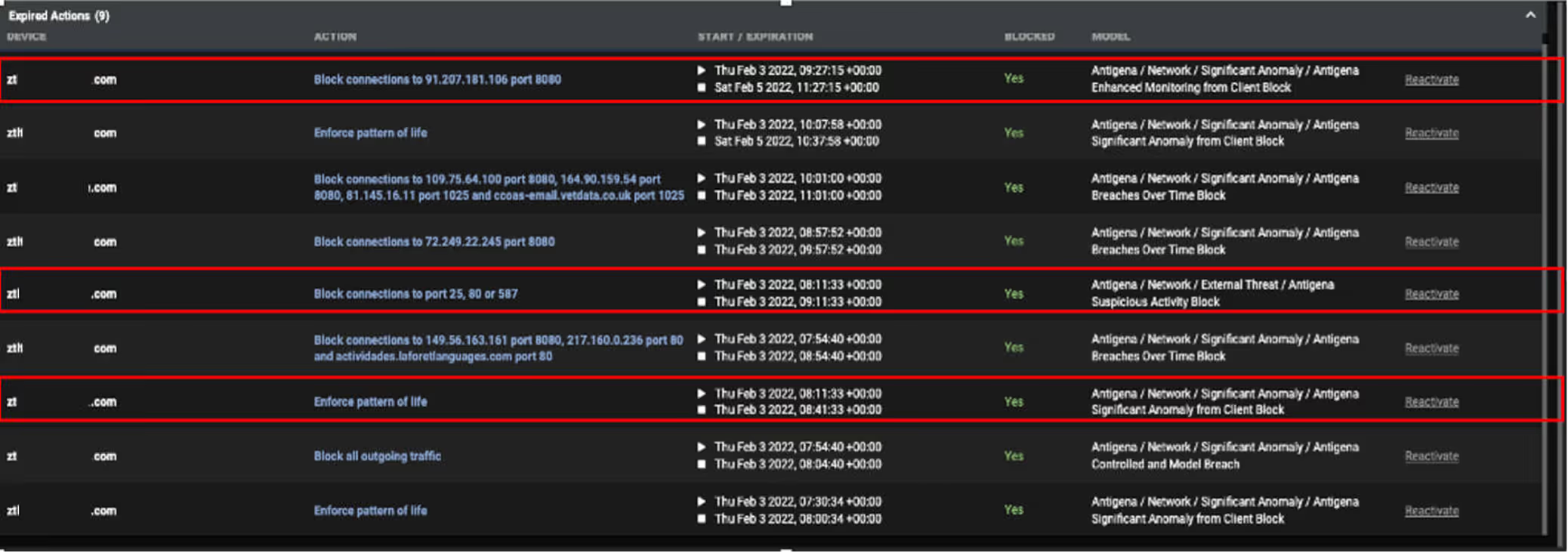
Throughout the incident, Antigena autonomously responded to the initial breach device to enforce its ‘pattern of life’ without interrupting business processes. This significantly reduced the scope of the compromise by halting further lateral movement. In response to the malicious outbound email spam, Antigena enforced the device’s usual ‘pattern of life’ for thirty minutes and blocked connections to ports 25, 80 and 587 for one hour (Figure 5). Against the command-and-control activity, connections to 91.207.181[.]106 via port 8080 were also blocked for three hours.
The customer’s subscription to Darktrace’s Proactive Threat Notification (PTN) and Ask the Expert (ATE) services meant that this compromise was assisted by additional triage and alerting. PTN ensured that the Darktrace SOC team were quickly alerted to the breach, enabling analysts to perform a detailed investigation alongside the customer’s own security team. Simultaneously, the ATE service ensured the customer was provided with additional information to ensure the threat was less likely to happen again. This equipped the team with the vital information needed for them to act, and to restore quickly and precisely.
The resurgence of Emotet shows how email continues to act as a crucial attack vector and source of compromise. In particular, widespread malspam campaigns remain adaptable and effective. The incident in this blog is yet another example highlighting the alarming mutability and networked nature of malware organizations. This allows them to return, even long after their dismantling. Fortunately, in this incident, Autonomous Response enabled this Emotet compromise to be minimized, while PTN and ATE services alerted and further supported the security team throughout.
Appendix
Darktrace model breaches
· Device / Multiple Lateral Movement Model Breaches
· Device / Large Number of Model Breaches
· Device / Suspicious Network Scan Activity
· Device / Network Scan
· Device / External Address Scan
· Device / Multiple C2 Model Breaches
· Device / Large Number of Connections to New Endpoints
· Device / Increased External Connectivity
· Device / New User Agent and New IP
· Device / New PowerShell User Agent
· Compromise / Suspicious Beaconing Behavior
· Compromise / Beacon to Young Endpoint
· Compromise / Agent Beacon to New Endpoint
· Compromise / Sustained SSL or HTTP Increase
· Compromise / Suspicious Spam Activity
· Anomalous Connection / Possible Outbound Spam
· Anomalous Connection / Suspicious Expired SSL
· Anomalous Connection / Rare External SSL Self-Signed
· Anomalous Connection / Suspicious Self-Signed SSL
· Anomalous Connection / Anomalous SSL without SNI to New External
· Anomalous Connection / PowerShell to Rare External
· AI Analyst / AI Analyst Investigation
· Unusual Activity / Unusual External Activity
IoCs

MITRE ATT&CK Techniques Observed

Footnotes
1. https://www.cisa.gov/uscert/ncas/alerts/TA18-201A
3. https://www.kaspersky.com/resource-center/threats/emotet



























%201.png)










