Why Cloud Investigations Fail Today
Cloud investigations have become one of the hardest problems in modern cybersecurity. Traditional DFIR tools were built for static, on-prem environments, rather than dynamic and highly scalable cloud environments, containing ephemeral workloads that disappear in minutes. SOC analysts are flooded with cloud security alerts with one-third lacking actionable data to confirm or dismiss a threat[1], while DFIR teams waste 3-5 days requesting access and performing manual collection, or relying on external responders.
These delays leave organizations vulnerable. Research shows that nearly 90% of organizations suffer some level of damage before they can fully investigate and contain a cloud incident [2]. The result is a broken model: alerts are closed without a complete understanding of the threat due to a lack of visibility and control, investigations drag on, and attackers retain the upper hand.
For SOC teams, the challenge is scale and clarity. Analysts are inundated with alerts but lack the forensic depth to quickly distinguish real threats from noise. Manual triage wastes valuable time, creates alert fatigue, and often forces teams to escalate or dismiss incidents without confidence — leaving adversaries with room to maneuver.
For DFIR teams, the challenge is depth and speed. Traditional forensics tools were built for static, on-premises environments and cannot keep pace with ephemeral workloads that vanish in minutes. Investigators are left chasing snapshots, requesting access from cloud teams, or depending on external responders, leading to blind spots and delayed response.
That’s why we built Darktrace / Forensic Acquisition & Investigation, the first automated forensic solution designed specifically for the speed, scale, and complexities of the cloud. It addresses both sets of challenges by combining automated forensic evidence capture, attacker timeline reconstruction, and cross-cloud scale. The solution empowers SOC analysts with instant clarity and DFIR teams with forensic depth, all in minutes, not days. By leveraging the very nature of the cloud, Darktrace makes these advanced capabilities accessible to security teams of all sizes, regardless of expertise or resources.
Introducing Automated Forensics at the Speed and Scale of Cloud
Darktrace / Forensic Acquisition & Investigation transforms cloud investigations by capturing, processing, and analyzing forensic evidence of cloud workloads, instantly, even from time-restricted ephemeral resources. Triggered by a detection from any cloud security tool, the entire process is automated, providing accurate root cause analysis and deep insights into attacker behavior in minutes rather than days or weeks. SOC and DFIR teams no longer have to rely on manual processes, snapshots, or external responders, they can now leverage the scale and elasticity of the cloud to accelerate triage and investigations.
Seamless Integration with Existing Detection Tools
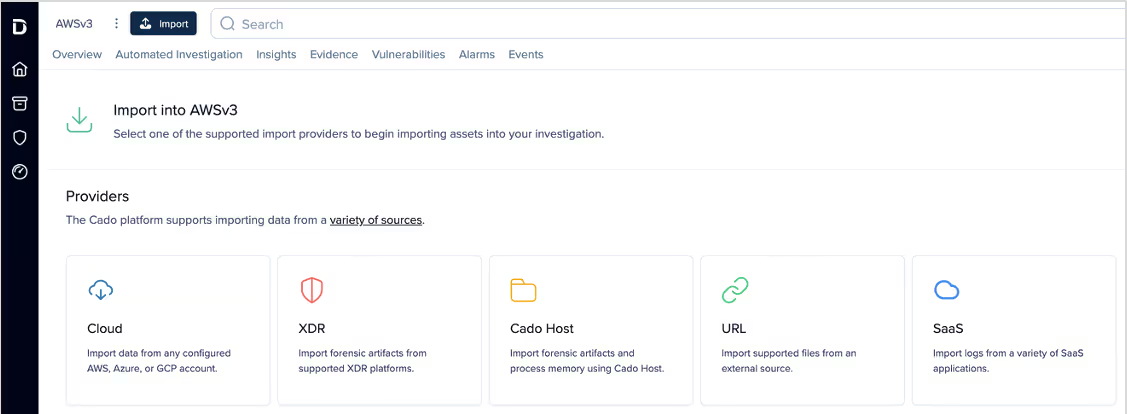
Darktrace / Forensic Acquisition & Investigation does not require customers to replace their detection stack. Instead, it integrates with cloud-native providers, XDR platforms, and SIEM/SOAR tools, automatically initiating forensic capture whenever an alert is raised. This means teams can continue leveraging their existing investments while gaining the forensic depth required to validate alerts, confirm root cause, and accelerate response.
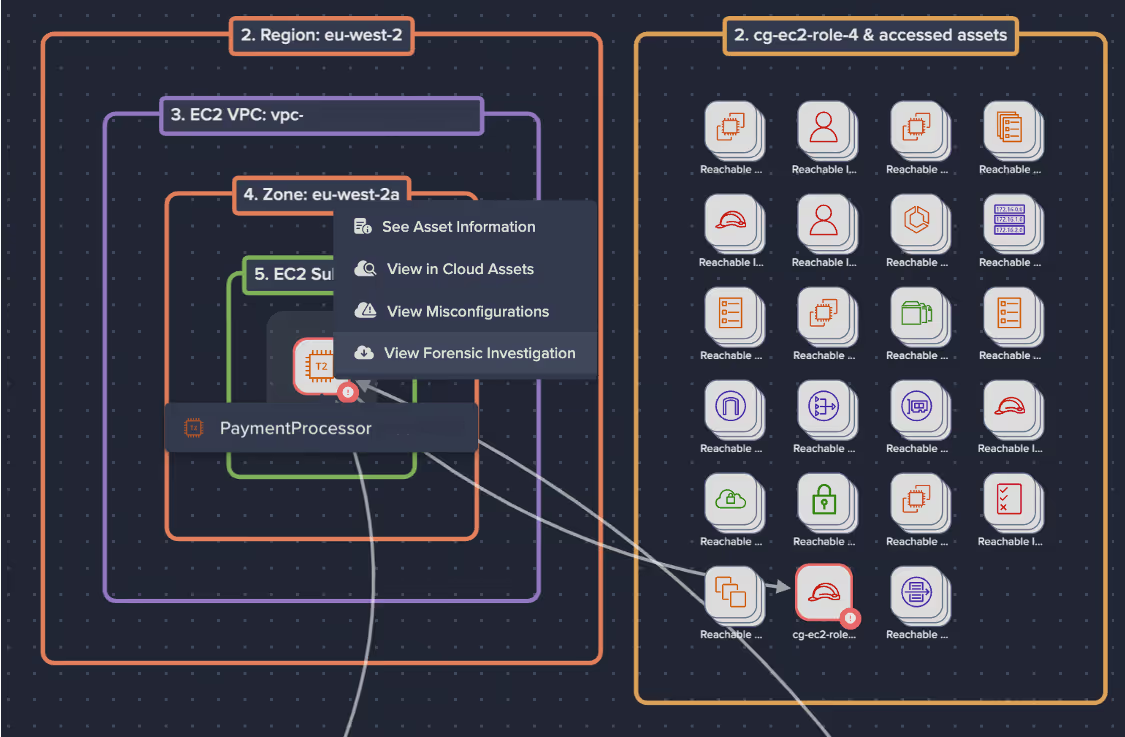
Most importantly, the solution is natively integrated with Darktrace / CLOUD, turning real-time detections of novel attacker behaviors into full forensic investigations instantly. When Darktrace / CLOUD identifies suspicious activity such as lateral movement, privilege escalation, or abnormal usage of compute resources, Darktrace / Forensic Acquisition & Investigation automatically preserves the underlying forensic evidence before it disappears. This seamless workflow unites detection, response, and investigation in a way that eliminates gaps, accelerates triage, and gives teams confidence that every critical cloud alert can be investigated to completion.
Automated Evidence Collection Across Hybrid and Multi-Cloud
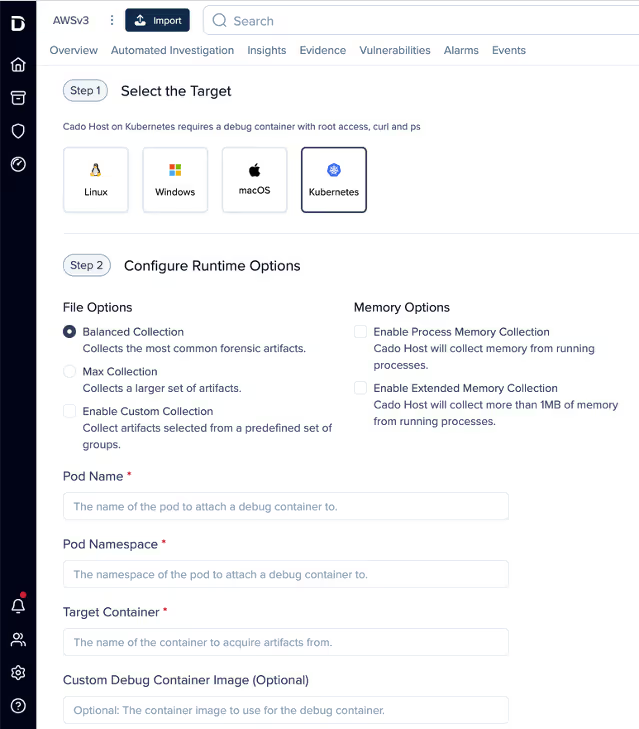
The solution provides automated forensic acquisition across AWS, Microsoft Azure, GCP, and on-prem environments. It supports both full volume capture, creating a bit-by-bit copy of an entire storage device for the most comprehensive preservation of evidence, and triage collection, which prioritizes speed by gathering only the most essential forensic artifacts such as process data, logs, network connections, and open file contents. This flexibility allows teams to strike the right balance between speed and depth depending on the investigation at hand.
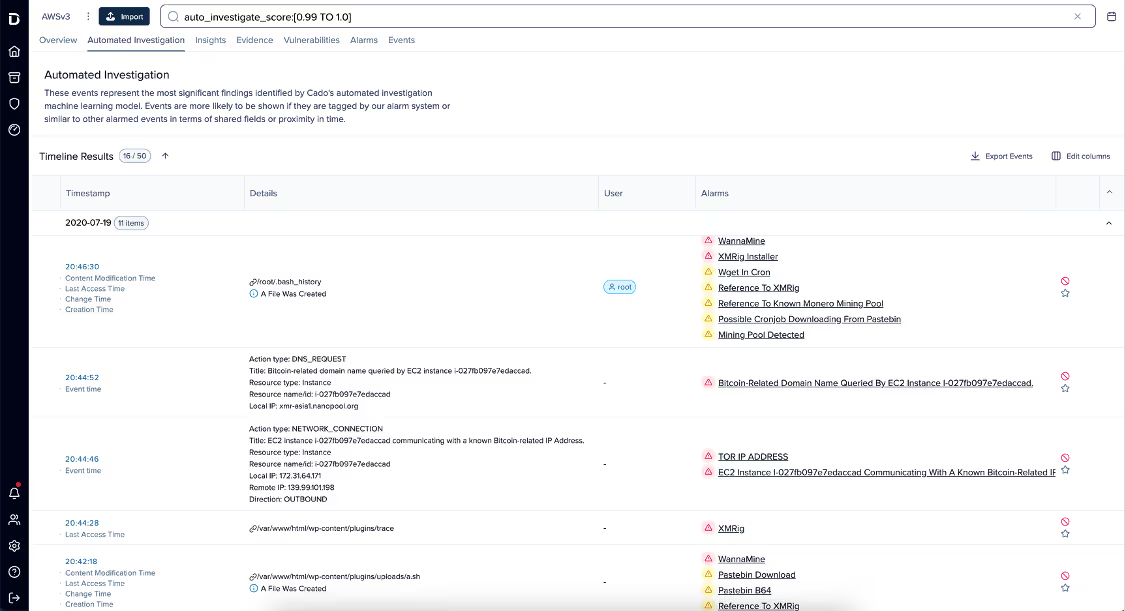
Automated Investigations, Root Cause Analysis and Attacker Timelines
Once evidence is collected, Darktrace applies automation to reconstruct attacker activity into a unified timeline. This includes correlating commands, files, lateral movement, and network activity into a single investigative view enriched with custom threat intelligence such as IOCs. Detailed investigation reporting including an investigation summary, an overview of the attacker timeline, and key events. Analysts can pivot into detailed views such as the filesystem view, traversing directories or inspecting file content, or filter and search using faceted options to quickly narrow the scope of an investigation.
Forensics for Containers and Ephemeral Assets
Investigating containers and serverless workloads has historically been one of the hardest challenges for DFIR teams, as these assets often disappear before evidence can be preserved. Darktrace / Forensic Acquisition & Investigation captures forensic evidence across managed Kubernetes cloud services, even from distroless or no-shell containers, AWS ECS and other environments, ensuring that ephemeral activity is no longer a blind spot. For hybrid organizations, this extends to on-premises Kubernetes and OpenShift deployments, bringing consistency across environments.
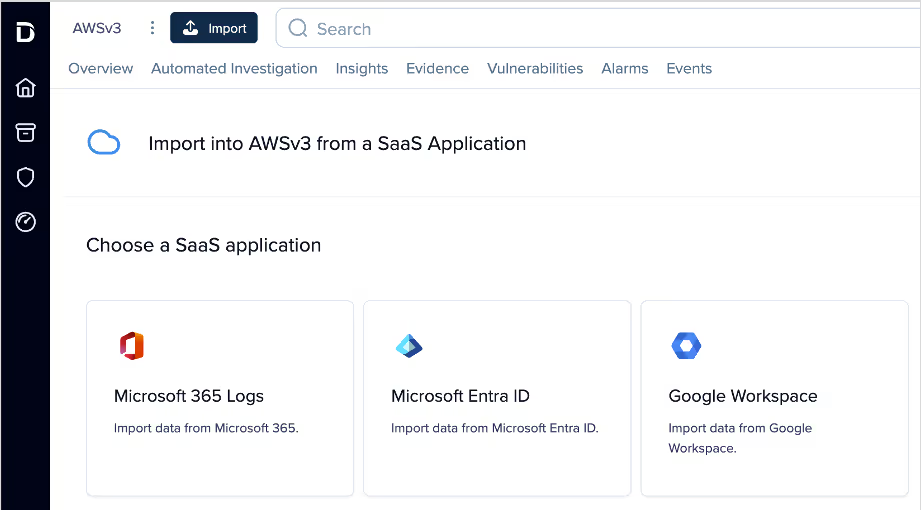
SaaS Log Collection for Modern Investigations
Beyond infrastructure-level data, the solution collects logs from SaaS providers such as Microsoft 365, Entra ID, and Google Workspace. This enables investigations into common attack types like business email compromise (BEC), account takeover (ATO), and insider threats — giving teams visibility into both infrastructure-level and SaaS-driven compromise from a single platform.
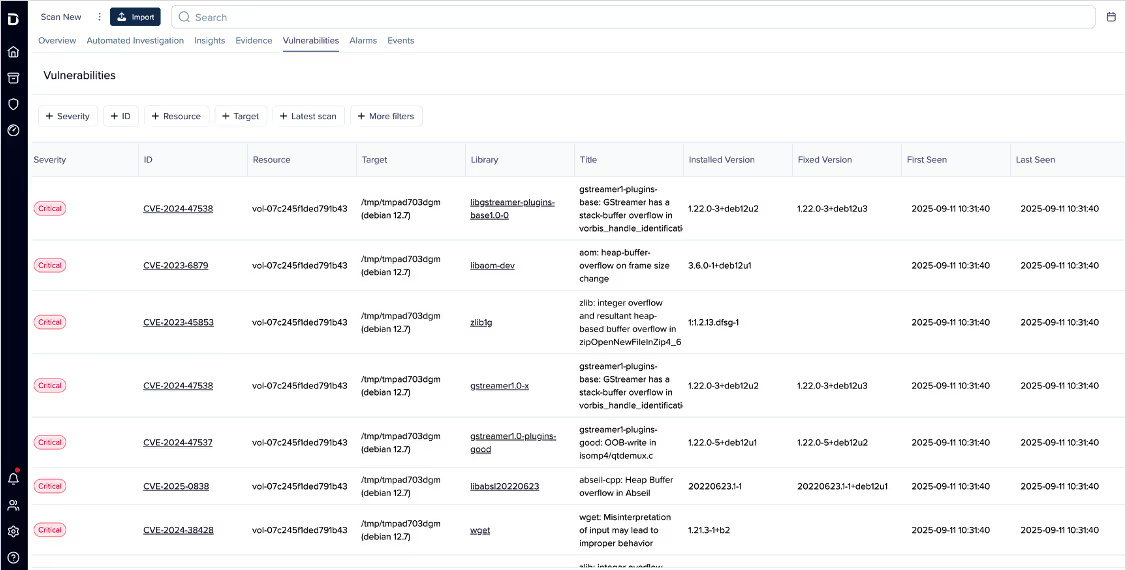
Proactive Vulnerability and Malware Discovery
Finally, the solution surfaces risk proactively with vulnerability and malware discovery for Linux-based cloud resources. Vulnerabilities are presented in a searchable table and correlated with the attacker timeline, enabling teams to quickly understand not just which packages are exposed, but whether they have been targeted or exploited in the context of an incident.
Cloud-Native Scale and Performance
Darktrace / Forensic Acquisition & Investigation uses a cloud-native parallel processing architecture that spins up compute resources on demand, ensuring that investigations run at scale without bottlenecks. Detailed reporting and summaries are automatically generated, giving teams a clear record of the investigation process and supporting compliance, litigation readiness, and executive reporting needs.
Scalable and Flexible Deployment Options
Every organization has different requirements for speed, control, and integration. Darktrace / Forensic Acquisition & Investigation is designed to meet those needs with two flexible deployment models.
- Self-Hosted Virtual Appliance delivers deep integration and control across hybrid environments, preserving forensic data for compliance and litigation while scaling to the largest enterprise investigations.
- SaaS-Delivered Deployment provides fast time-to-value out of the box, enabling automated forensic response without requiring deep cloud expertise or heavy setup.
Both models are built to scale across regions and accounts, ensuring organizations of any size can achieve rapid value and adapt the solution to their unique operational and compliance needs. This flexibility makes advanced cloud forensics accessible to every security team — whether they are optimizing for speed, integration depth, or regulatory alignment
Delivering Advanced Cloud Forensics for Every Team
Until now, forensic investigations were slow, manual, and reserved for only the largest organizations with specialized DFIR expertise. Darktrace / Forensic Acquisition & Investigation changes that by leveraging the scale and elasticity of the cloud itself to automate the entire investigation process. From capturing full disk and memory at detection to reconstructing attacker timelines in minutes, the solution turns fragmented workflows into streamlined investigations available to every team.
Whether deployed as a SaaS-delivered service for fast time-to-value or as a self-hosted appliance for deep integration, Darktrace / Forensic Acquisition & Investigation provides the features that matter most: automated evidence capture, cross-cloud investigations, forensic depth for ephemeral assets, and root cause clarity without manual effort.
With Darktrace / Forensic Acquisition & Investigation, what once took days now takes minutes. Now, forensic investigations in the cloud are faster, more scalable, and finally accessible to every security team, no matter their size or expertise.
[related-resource]
Sources: [1], [2] Darktrace Report: Organizations Require a New Approach to Handle Investigations in the Cloud
Additional Resources
Darktrace Innovation Launch: Automated Cloud Forensics
Discover the industry's first truly automated cloud forensics solution in this live broadcast with experts from AWS and Forrester.


































%201.png)