Salt Typhoonとは?
Salt Typhoonは、現在世界のインフラを狙っている最も執拗かつ巧妙なサイバー脅威の1つです。国家が支援する中国のアクターとされるこのAPT(Advanced Persistent Threat)グループは、主に米国の通信プロバイダー、エネルギーネットワーク、政府システムを標的とした、ー連のインパクトの大きいキャンペーンを実行しています。
少なくとも2019年から活動しており、Earth Estries、GhostEmperor、UNC2286としても記録されているこのグループは、エッジデバイスのエクスプロイトに高度な能力を示し、深い永続性を維持しつつ80か国以上において機密性の高いデータの抜き出しを行っています。公になっている被害の報告はほとんど米国の標的に集中していますが、Salt TyphoonのオペレーションはEMEA(ヨーロッパ、中東、アフリカ)地域にも拡大し、通信、政府機関、テクノロジー企業等が標的とされています。カスタムマルウェアの使用、およびインパクトの大きい脆弱性のエクスプロイト(例: Ivanti、Fortinet、Cisco等)は、インテリジェンス収集と地政学的影響を組み合わせたこのグループの戦略的性質を表しています [1]。
ゼロデイエクスプロイト、難読化テクニック、水平移動戦術を駆使することにより、Salt Typhoonは検知を回避し機密性の高い環境に長期間のアクセスを維持することのできる、恐るべき能力を実証しています。このグループのオペレーションにより合法的傍受システムが露出し、数百万のユーザーのメタデータが漏洩、必要不可欠なサービスの中断を招き、世界中で情報機関と民間パートナーの協調した対応が促されました。組織が自社の脅威モデルを評価するなかで、Salt Typhoonは国家が支援するサイバーオペレーションの進化と、積極的な防御戦略が緊急に必要であることをはっきりと思い出させる存在です。
Darktraceのカバレッジ
Darktraceはヨーロッパの通信企業において、DLLサイドローディングと正規のソフトウェアの悪用によるステルス性維持と実行を含む、Salt Typhoonのものとして知られているTTP(戦術、技法、手順)を確認しました。
初期アクセス
侵入は2025年7月、CVE-2025-5777のエクスプロイトから始まりました。これはCitrix NetScaler Gatewayアプライアンスに影響する脆弱性です。脅威アクターはここから、クライアントのMCS(Machine Creation Services)サービス内の Citrix VDA(Virtual Delivery Agent)ホストに移動しました。この侵入の初期のアクセス活動はSoftEther VPNサービスと関連するとみられるエンドポイントから発生しており、最初からインフラ難読化が行われていたことがわかります。
ツール
Darktraceはその後、この脅威アクターが複数のCitrix VDAホストに対し、高い確率でSNAPPYBEE(Deed RATとしても知られる) [2][3] であるとみられるバックドアを設置したことを検知しました。このバックドアはこれらの内部エンドポイントに対して、Norton Antivirus、Bkav Antivirus、IObit Malware Fighterなどのアンチウイルスソフトウェアの正規の実行形式ファイルと共にDLLとして仕掛けられました。このアクティビティのパターンは、攻撃者が正規のアンチウイルスソフトウェアを使ったDLLサイドローディングによりペイロードを実行しようとしたことを示しています。Salt Typhoonおよび類似のグループは過去にもこのテクニックを使用してきており[4][5]、これにより信頼されるソフトウェアの陰でペイロードを実行し従来型のセキュリティコントロールを回避することを可能にしています。
コマンド&コントロール(C2)
この脅威アクターが設置したバックドアはLightNode VPSエンドポイントをC2に使用し、HTTPと不明なTCPベースのプロトコルの両方を使って通信していました。このように二重のチャネルを使っていることは、Salt Typhoonが非標準プロトコルを多層的に使用して検知を回避することで知られていることと一致しています。バックドアに表示されたHTTP通信には、Internet Explorerの User-Agentヘッダーを持つPOSTリクエストや“/17ABE7F017ABE7F0” のようなTarget URIパターンが含まれていました。侵害されたエンドポイントが接続したC2ホストの1つはaar.gandhibludtric[.]com (38.54.63[.]75)であり、最近Salt Typhoonとの関連が確認されたドメインです[6]。
検知のタイムライン
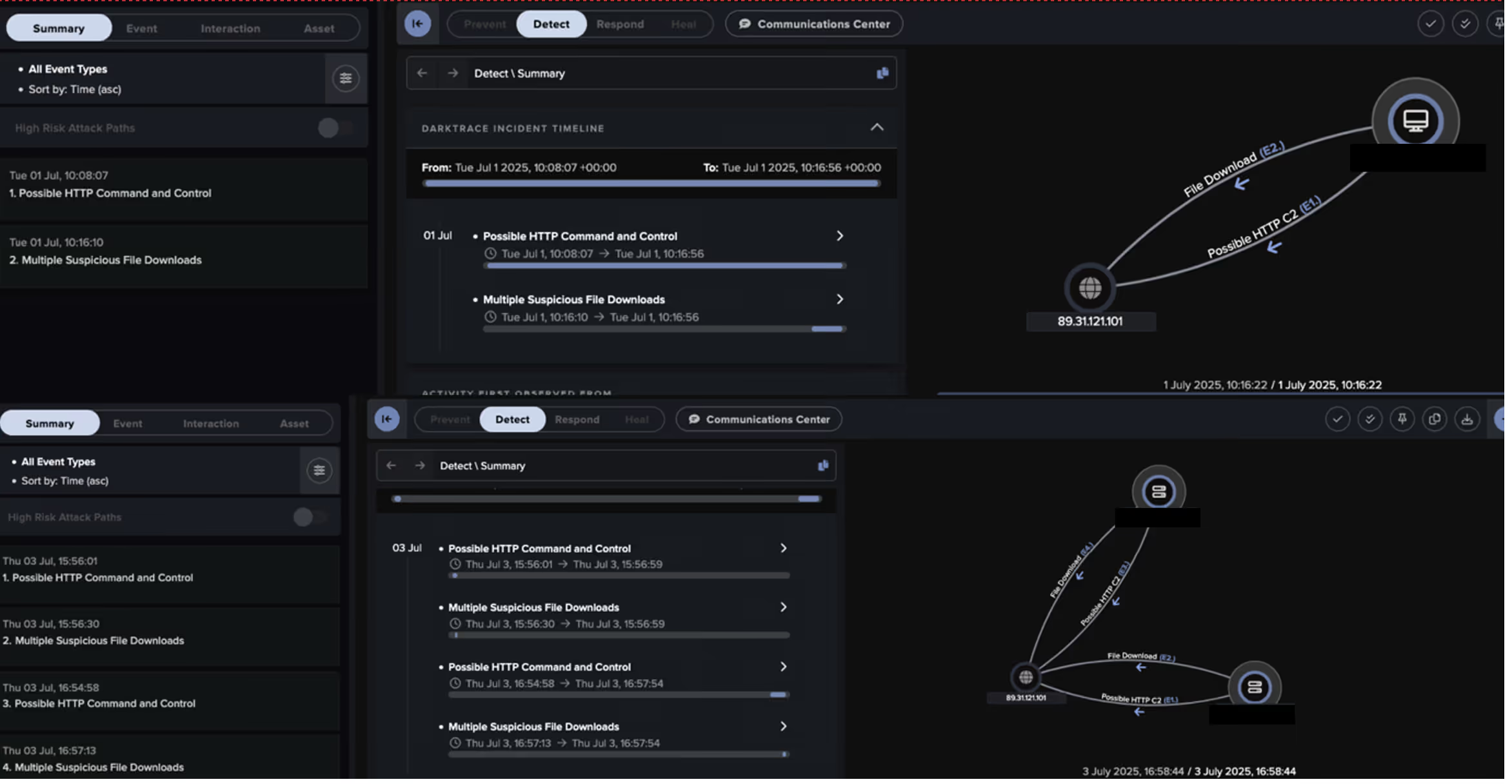
Darktraceは侵入の初期段階に対して高確度の検知結果を生成しました。初期のツール使用とC2アクティビティは、Darktrace Cyber AI AnalystTMによる調査と、Darktraceのモデルの両方によって明確にカバーされていました。脅威アクターが高度であったにもかかわらず、侵入アクティビティはこれらの攻撃の初期段階から先へ進展する前に識別され、修正されました。Darktraceのタイムリーかつ高確度の検知が脅威の無害化に重要な役割を果たしたものと思われます。
Cyber AI Analystの知見
Darktrace Cyber AI Analyst は侵入の初期段階においてDarktraceが検知したモデルアラートを自律的に調査しました。この調査を通じ、Cyber AI Analystは初期のツール使用とC2イベントを突き止め、これらをつなぎ合わせて攻撃の進行を表す1つのインシデントにまとめました。
まとめ
TTPやステージングパターン、インフラ、マルウェアの共通点に基づき、ダークトレースは一定の確信を持って観察されたアクティビティがSalt Typhoon/Earth Estries (ALA GhostEmperor/UNC2286)と一致していると評価しました。Salt Typhoonは引き続きそのステルス性、永続性、正規ツールの悪用によって防御者を悩ませています。攻撃者が通常のオペレーションに紛れ込もうとする傾向が高まるなかで、かすかな逸脱を識別し分散したシグナルを相関付けるには、動作の異常を検知することが不可欠となります。Salt Typhoonの特徴である変化する手法、そして信頼されるソフトウェアやインフラを別の目的に使用する能力により、従来の手法だけでは今後も検知が難しいことが確実です。この侵入インシデントは積極的な防御の重要性を示しており、そこではシグネチャの照合だけにとどまらない異常ベースの検知が、初期段階のアクティビティを明らかにする上で決定的な役割を果たします。
本稿の執筆には Nathaniel Jones (VP, Security & AI Strategy, FCISO)、Sam Lister(Specialist Security Researcher)、Emma Foulger(Global Threat Research Operations Lead)、Adam Potter(Senior Cyber Analystが協力しました。
編集:Ryan Traill(Analyst Content Lead)
付録
侵害インジケータ(IoC)
IoC-タイプ-説明 + 確度
89.31.121[.]101 – IP Address – Possible C2 server
hxxp://89.31.121[.]101:443/WINMM.dll - URI – Likely SNAPPYBEE download
b5367820cd32640a2d5e4c3a3c1ceedbbb715be2 - SHA1 – Likely SNAPPYBEE download
hxxp://89.31.121[.]101:443/NortonLog.txt - URI - Likely DLL side-loading activity
hxxp://89.31.121[.]101:443/123.txt - URI - Possible DLL side-loading activity
hxxp://89.31.121[.]101:443/123.tar - URI - Possible DLL side-loading activity
hxxp://89.31.121[.]101:443/pdc.exe - URI - Possible DLL side-loading activity
hxxp://89.31.121[.]101:443//Dialog.dat - URI - Possible DLL side-loading activity
hxxp://89.31.121[.]101:443/fltLib.dll - URI - Possible DLL side-loading activity
hxxp://89.31.121[.]101:443/DisplayDialog.exe - URI - Possible DLL side-loading activity
hxxp://89.31.121[.]101:443/DgApi.dll - URI - Likely DLL side-loading activity
hxxp://89.31.121[.]101:443/dbindex.dat - URI - Likely DLL side-loading activity
hxxp://89.31.121[.]101:443/1.txt - URI - Possible DLL side-loading activity
hxxp://89.31.121[.]101:443/imfsbDll.dll – Likely DLL side-loading activity
hxxp://89.31.121[.]101:443/imfsbSvc.exe - URI – Likely DLL side-loading activity
aar.gandhibludtric[.]com – Hostname – Likely C2 server
38.54.63[.]75 – IP – Likely C2 server
156.244.28[.]153 – IP – Possible C2 server
hxxp://156.244.28[.]153/17ABE7F017ABE7F0 - URI – Possible C2 activity
MITRE TTP
テクニック | 説明
T1190 | Exploit Public-Facing Application - Citrix NetScaler Gateway compromise
T1105 | Ingress Tool Transfer – Delivery of backdoor to internal hosts
T1665 | Hide Infrastructure – Use of SoftEther VPN for C2
T1574.001 | Hijack Execution Flow: DLL – Execution of backdoor through DLL side-loading
T1095 | Non-Application Layer Protocol – Unidentified application-layer protocol for C2 traffic
T1071.001| Web Protocols – HTTP-based C2 traffic
T1571| Non-Standard Port – Port 443 for unencrypted HTTP traffic
侵入時のDarktraceモデルアラート
Anomalous File::Internal::Script from Rare Internal Location
Anomalous File::EXE from Rare External Location
Anomalous File::Multiple EXE from Rare External Locations
Anomalous Connection::Possible Callback URL
Antigena::Network::External Threat::Antigena Suspicious File Block
Antigena::Network::Significant Anomaly::Antigena Significant Server Anomaly Block
Antigena::Network::Significant Anomaly::Antigena Controlled and Model Alert
Antigena::Network::Significant Anomaly::Antigena Alerts Over Time Block
Antigena::Network::External Threat::Antigena File then New Outbound Block
参考文献
[1] https://www.cisa.gov/news-events/cybersecurity-advisories/aa25-239a
[2] https://www.trendmicro.com/en_gb/research/24/k/earth-estries.html
[5] https://lab52.io/blog/deedrat-backdoor-enhanced-by-chinese-apts-with-advanced-capabilities/
[6] https://www.silentpush.com/blog/salt-typhoon-2025/
このブログで提供されるコンテンツはダークトレースが一般的な情報提供の目的でのみ公開するものであり、サイバーセキュリティに関するトピック、傾向、インシデント、出来事についての、公開の時点における当社の理解を反映したものです。当社は内容の正確性と重要性の担保に努めていますが、情報は明示的暗黙的を問わず、何らの表明あるいは保証も伴わわない「そのまま」の状態で提供されるものです。ダークトレースは本書に含まれる情報の完全性、正確性、信頼性、適時性について何らの責任も負わず、すべての保証を明示的に否認します。
本ブログに含まれるいかなる内容も法的、技術的、技術的助言を構成するものではなく、読者は本書に含まれる情報に基づいて行動する前に資格を持った専門家に相談されることをお勧めします。第三者の組織、技術、脅威アクター、インシデントに対する言及は情報目的のみであり、提携、承認、推奨を暗に意味するものではありません。
ダークトレース、その関連会社、従業員、あるいは代理人は、本ブログの情報の使用またはこれに対する信頼により生じた、いかなる損失、損害、危害についても責任を負いません。
サイバーセキュリティを取り巻く環境は急激に変化しており、ブログの内容は古くなるあるいは新しいものに代替される可能性があります。当社は任意のコンテンツを更新、変更、あるいは削除する権利を留保します。


















