ダークトレースは、中国系グループの活動と一致する動きを特定しました。これは、主にアジア太平洋および日本(APJ)地域の顧客環境を標的としたTwill Typhoonに関連するキャンペーンです。
2025年9月下旬から、影響を受けた複数のホストが、YahooやApple関連のサービスを装ったインフラを含む、コンテンツ配信ネットワーク(CDN)を偽装したドメインへのリクエストを行っていることが観察されました。これらの事例において、ダークトレースは一貫した動作のパターンを特定しました。それは、正当なバイナリと悪意あるダイナミックリンクライブラリ(DLL)を同時に取得し、モジュラー型の.NETベースのリモートアクセス型トロイの木馬(RAT)フレームワークのサイドローディングと実行を可能にするものでした。
これらはダークトレースが先日発表した中国系オペレーションについてのレポート、 Crimson Echoで説明されているパターンとも一致しています。このケースでは、正規のソフトウェア上にモジュラー型の侵入チェーンが構築され、ステージングされたペイロードの投下が見られました。脅威アクターは正当なバイナリをコンフィギュレーションファイルや悪意あるDLLとともに取得することにより、.NETベースのRATのサイドローディングを可能にしました。
キャンペーンの確認
これらのケースには同じ順序のシーケンスが現れています:(1) 正規の実行可能ファイルの取得、(2) 対応する .config ファイルの取得、(3) 悪意あるDLLの取得、(4) DLLの繰り返しダウンロード、(5) コマンド&コントロール(C2)通信。 正規のバイナリは正規のプロセスを提供しますが、.config ファイルは悪意あるバイナリを取得します。
ダークトレースは、この活動が公に報告されているTwill Typhoonの手法と一致していると中程度の確信を持って評価しています。FDMTPの使用、DLLサイドローディング、および重複するインフラストラクチャが観察されたことは、以前に見られた作戦と一致していますが、これは特定の単一のアクターに固有のものではありません。アトリビューションには可視性による制限があります。初期アクセスは直接確認されませんでしたが、侵入のパターンは同様の作戦で報告されている既知のフィッシングによる侵入手法と一致しています。
Darktraceによる観測
2025年9月下旬より、Darktraceは複数の顧客環境において良く知られたプラットフォームの“CDN”エンドポイントと称するインフラ(YahooやAppleを偽装したものを含む)に対してHTTP GETリクエストが行われていることを観測しました。これらのケースでは、影響を受けたホストは正当な実行形式、対応する.configファイル(同じベース名)、そしてサイドローディング用DLLを取得しています。正当なバイナリ+コンフィギュレーション+DLLのシーケンスは中国系の攻撃キャンペーンで見られているものです。
いくつかのケースでは、ホストはさらに/GetClusterエンドポイントへのアウトバウンドリクエストを発行しており、protocol=Dotnet-Tcpdmtpパラメータも含まれていました。このアクティビティの後繰り返しDLLコンテンツの取得が行われ、その後これが正当なプロセス内でサーチオーダー杯ジャッキングに使われました。
2025年9月~10月に見られた多くのケースで、Darktraceのアラートは初期段階の登録およびC2セットアップ動作を識別しました。その後同じ外部ホストからのDLL(Client.dll等)取得(一部のケースでは複数日に渡って繰り返し)が続き、これは実行チェーンの確立と維持を示すものでした。2026年4月、金融セクターの顧客のエンドポイントがyahoo-cdn[.]it[.]comに対して一連のGETリクエストを開始し、最初に正当なバイナリ(vshost.exeおよびdfsvc.exeを含む)を取得し、その後11日間にわたり関連するコンフィギュレーションファイルおよびDLLコンポーネント(dfsvc.exe.configおよびdnscfg.dllを含む)を繰り返し取得しました。Visual Studio ホスティングと OneClick(dfsvc.exe)のパスの使用はどちらも、マルウェアをターゲット環境で実行できるようにするためのものです。
技術分析
初期ステージングおよび実行
最初のアクセスはわかっていませんが、ダークトレースの研究者はマルウェアを含む複数のアーカイブを特定しました。
代表的なサンプルには以下を含むZIPアーカイブ(“test.zip”)が含まれていました:
- 正規の実行形式:biz_render.exe(Sogou Pinyin IME)
- 悪意あるDLL: browser_host.dll
"test.zip" という名前のzipアーカイブには、正規のバイナリ"biz_render.exe" が含まれており、これは人気のある中国語IMEであるSogou Pinyinです。
正規のバイナリと共に ”browser_host.dll” という悪意のあるDLLがあります。</x1>この正規のバイナリは ”browser_host.dll”という正規のDLLを、LoadLibraryExWを介して読み込みますが、悪意のあるDLLにも同じ名前がつけられることにより、biz_render.exeに悪意のあるDLLをサイドロードします。同名の悪意あるDLLを提供することで、攻撃者は実行フローを乗っ取り、信頼されたプロセス内でペイロードを実行することができます。

正規のバイナリは、サイドロードされた"browser_host.dll"から関数GetBrowserManagerInstanceを呼び出し、その後、埋め込まれた文字列に対してXORベースの復号化(キー 0x90)を実行して、mscoree.dllを解決し動的にロードします。
このDLLは、ネイティブバイナリのみに依存するのではなく、Windowsの共通言語ランタイム(CLR)を使用することにより、プロセス内で管理された.NETコードを実行します。実行中、ローダーはペイロードを.NETアセンブリとして直接メモリにロードし、メモリ内での実行を可能にします。
C2 登録
GETリクエストが以下に対して実行されます:
GET /GetCluster?protocol=DotNet-TcpDmtp&tag={0}&uid={1}
カスタムヘッダ:
Verify_Token: Dmtp
これは、後の通信に使用されるIPアドレスをbase64でエンコードし、gzipで圧縮したものを返します。

ステージングされたペイロードの取得
その後のアクティビティには、yahoo-cdn.it[.]comからの複数のコンポーネントの取得が含まれます。以下のGETリクエストが行われます:
/dfsvc.exe
/dnscfg.dll
/dfsvc.exe.config
/vhost.exe
/Microsoft.VisualStudio.HostingProcess.Utilities.Sync.dll
/config.etl
ClickOnceおよびAppDomainのハイジャッキング
Dfsvc.exeは正当なWindowsのClickOnceエンジンであり、ClickOnceアプリケーションの更新に使用される.NETフレームワークの一部です。付随するdfsvc.exeには、アプリケーションのコンフィギュレーションデータを保存するために使用されるdfsvc.exe.configファイルが含まれています。しかし、このケースではマルウェアが正規のdfsvc.exe.configをC:\Windows\Microsoft.NET\Framework64\v4.0.30319のサーバーから取得したものと置き換えます。
さらに、正当なVisual Studioホスティングプロセスであるvhost.exeがサーバーから取得され、それとともに”Microsoft.VisualStudio.HostingProcess.Utilities.Sync.dll”と”config.etl”も取得されます。このDLLは、config.etl内のAESで暗号化されたペイロードを復号してロードするために使用されます。暗号化されたペイロードはdnscfg.dllであり、これはdfsvcの代わりにvshostにロードすることができ、環境が.NETをサポートしていない場合に使用することができます。

悪意あるコンフィギュレーションはログ記録を無効にし、アプリケーションがリモートサーバーからdnscfg.dllを読み込むようにし、カスタムのAppDomainManagerを使用してdfsvc.exeの初期化時にDLLが実行されるようにします。永続性を確保するために、%APPDATA%\Local\Microsoft\WindowsApps\dfsvc.exeのスケジュールされたタスクが追加されます。
コアペイロード
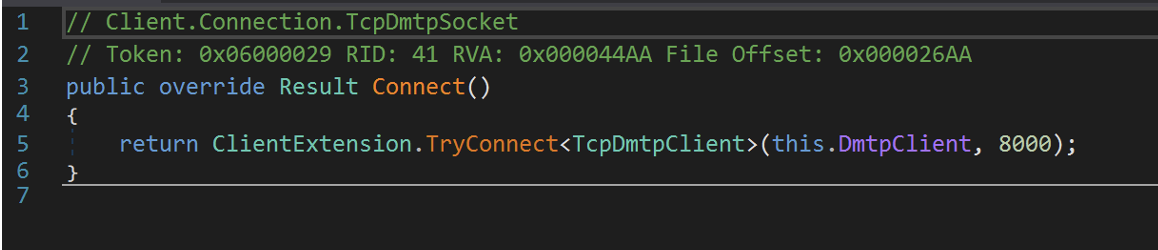
DLL dnscfg.dll は、カスタムTCPベースのプロトコルであるDMTP(Duplex Message Transport Protocol)を使用して通信する、著しく難読化された.NET RAT(Client.TcpDmtp.dll) です。 観察された特徴から、これはFDMTPフレームワーク(v3.2.5.1)の更新版であると思われます。

ペイロードは:
- クラスタベースの解決を使用 (GetHostFromCluster)
- トークン検証を実装
- 永続的な実行ループに入る (LoopMessage)
- DMTPを介した構造化されたリモートタスキングをサポート
接続が確立されると、マルウェアは永続的なループ(LoopMessage)に入り、リモートサーバーからのコマンドを受信できるようになります。
値は直接参照するのではなく、実行時に解決されるコンテナを通じて取得されます。文字列値は暗号化されたバイト配列(_0)に格納され、カスタムのXORベースの文字列復号ルーチン(dcsoft)によって復号されます。キーの下位16ビットは0xA61D(42525)とXORされて初期のXORキーが導出され、それに続くビットは文字列の長さと暗号化されたバイト配列へのオフセットを定義します。各文字は2つの暗号化されたバイトから再構成され、増加するキー値とXORされて、ペイロードで使用される平文文字列が生成されます。

リソースセクションには複数の圧縮されたバイナリが埋め込まれており、その大多数はライブラリファイルです。

モジュラー型フレームワークとプラグイン
ペイロードには以下を含む複数の圧縮ライブラリが埋め込まれています:
client.core.dllclient.dmtpframe.dll
Client.core.dllは、システムプロファイリング、C2通信、およびプラグイン実行に使用されるコアライブラリです。インプラントは、アンチウイルス製品、ドメイン名、HWID、CLRバージョン、管理者権限、ハードウェアの詳細、ネットワークの詳細、オペレーティングシステム、およびユーザーを含む情報を取得する機能を備えています。

さらに、このコンポーネントはプラグインの読み込みを担当しており、バイナリおよびJSONベースのプラグイン実行の両方をサポートしています。これにより、プラグインは実行されるタスクに応じて異なる形式のコマンドやパラメータを受け取ることができます。
このフレームワークがプラグインのハッシュ、メソッド名、タスク識別子、呼び出し元追跡、引数の処理などの詳細を管理し、プラグインを環境内で一貫して実行することができます。実行管理に加えて、このライブラリはログ記録、通信、プロセス処理などの共通のランタイム機能へのアクセスをプラグインに提供します。

client.dmtpframe.dllは次を処理します:
- DMTP通信
- ハートビートおよび再接続
- レジストリを通じたプラグイン永続化:
HKCU\Software\Microsoft\IME\{id}
Client.dmtpframe.dllはTouchSocket DMTPネットワーキングライブラリ上に構築されており、リモートプラグインの管理を行います。このDLLは、ハートビートの維持、再接続処理、RPCスタイルのメッセージング、SSLサポート、およびトークンベースの認証を含むリモート通信機能を実装しています。このDLLは、永続化のためにHKCU/Software/Microsoft/IME/{id} のレジストリにプラグインを追加する機能も備えています。
観測されたプラグイン
使用されたすべてのプラグインは判明していませんが、研究者たちは以下の4つを確認することができました:
- Persist.WpTask.dll - リモートでスケジュールされたWindowsタスクを作成、削除、トリガーするために使用されます。
- Persist.registry.dll - レジストリの永続性を管理するために使用され、レジストリ値の作成および削除、隠し永続化キーの操作が可能です。
- Persist.extra.dll - メインフレームワークの読み込みと永続化に使用されます。
- Assist.dll - リモートでファイルやコマンドを取得したり、システムプロセスを操作したりするために使用されます。


Persist.extra.dll は、スクリプト"setup.log"を、読み込みメインフレームワークをロードおよび永続化するために使用されるモジュールです。バイナリのリソースセクションに格納されている難読化されたスクリプトは、.NET COMオブジェクトを作成し、永続化のためにレジストリキーHKCU\Software\Classes\TypeLib\ {9E175B61-F52A-11D8-B9A5-505054503030}\1.0\1\Win64 に追加します。このスクリプトの難読化を解除すると、"WindowsBase.dll”という別のDLLが明らかになります。

バイナリは5分ごとにicloud-cdn[.]netをチェックし、バージョン文字列を取得し、暗号化されたペイロードであるchecksum.binをダウンロードし、ローカルにC:\ProgramData\USOShared\Logs\checksum.etlとして保存し、ハードコードされたキーPOt_L[Bsh0=+@0a.を使用してAESで復号化し、Assembly.Load(byte[])を介して復号化されたアセンブリをメモリから直接ロードします。version.txtファイルは更新マーカーとして機能し、リモートのバージョンが変更された場合にのみ再ダウンロードされるようにします。また、ミューテックスは重複したインスタンスの起動を防ぎます。

Checksum.etlはAESで復号化され、メモリにロードされ、別の.NET DLLである"Client.dll"がロードされます。このバイナリは前述の"dnscfg.dll"と同じものであり、脅威アクターがバージョンに基づいてメインフレームワークを更新することを可能にします。
まとめ
これらの事例で一貫して観測されたシーケンスは以下の通りです:
- 正規の実行形式の取得
- サイドローディング用DLLの取得
- /GetClusterによるC2登録
侵入は単一の足場に依存しておらず、独立して更新、交換、再読み込みが可能なコンポーネントに分散されています。このアプローチは、中国系脅威アクターの手法と一致しています。Crimson Echoレポートで説明されているように、安定した特徴は技術的なものではなく、動作上の特徴です。インフラストラクチャは変化し、ペイロードも変わりますが、実行モデルは同じです。防御者にとって、その意味は明白です。それは個別の指標に基づく検知は急速に劣化するということです。動作のシーケンスや、アクセスがどのように構築され再確立されるかに基づく検知は、はるかに永続的です。
協力:Tara Gould (Malware Research Lead), Adam Potter (Senior Cyber Analyst), Emma Foulger (Global Threat Research Operations Lead), Nathaniel Jones (VP, Security & AI Strategy)
編集: Ryan Traill (Content Manager)
付録
検知モデルとトリガーされたインジケータのリストをIOCとともに提示します。
Indicators of Compromise (IoCs)
Test.zip - fc3959ebd35286a82c662dc81ca658cb
Dnscfg.dll - b2c8f1402d336963478f4c5bc36c961a
Client.TcpDmtp.dll - c52b4a16d93a44376f0407f1c06e0b
Browser_host.dll - c17f39d25def01d5c87615388925f45a
Client.DmtpFrame.dll - 482cc72e01dfa54f30efe4fefde5422d
Persist.Extra - 162F69FE29EB7DE12B684E979A446131
Persist.Registry - 067FBAD4D6905D6E13FDC19964C1EA52
Assist - 2CD781AB63A00CE5302ED844CFBECC27
Persist.WpTask - DF3437C88866C060B00468055E6FA146
Microsoft.VisualStudio.HostingProcess.Utilities.Sync.dll - c650a624455c5222906b60aac7e57d48
www.icloud-cdn[.]net
www.yahoo-cdn.it[.]com
154.223.58[.]142[AP8] [EF9]
MITRE ATT&CK テクニック
T1106 – ネイティブAPI
T1053.005 -スケジュールされたタスク
T1546.16 - コンポーネントオブジェクトモデルハイジャッキング
T1547.001 – レジストリ実行キー
T1511.001 -DLLインジェクション
T1622 – デバッガ回避
T1027 – ファイルおよび情報の難読化解除/復号化解除
T1574.001 - 実行フローハイジャック:DLL
T1620 – リフレクティブコードローディング
T1082 – システム情報探索
T1007 – システムサービス探索
T1030 – システムオーナー/ユーザー探索
T1071.001 - Webプロトコル
T1027.007 - 動的API解決
T1095 – 非アプリケーションレイヤプロトコル
Darktrace モデルアラート
· Compromise / Beaconing Activity To External Rare
· Compromise / HTTP Beaconing to Rare Destination
· Anomalous File / Script from Rare External Location
· Compromise / Sustained SSL or HTTP Increase
· Compromise / Agent Beacon to New Endpoint
· Anomalous File / EXE from Rare External Location
· Anomalous File / Multiple EXE from Rare External Locations
· Compromise / Quick and Regular Windows HTTP Beaconing
· Compromise / High Volume of Connections with Beacon Score
· Anomalous File / Anomalous Octet Stream (No User Agent)
· Compromise / Repeating Connections Over 4 Days
· Device / Large Number of Model Alerts
· Anomalous Connection / Multiple Connections to New External TCP Port
· Compromise / Large Number of Suspicious Failed Connections
· Anomalous Connection / Multiple Failed Connections to Rare Endpoint
· Device / Increased External Connectivity


















