IT-OT統合へのシフト
近年、産業環境は相互接続が進み外部との連携により依存するようになりました。その結果、真にエアギャップされたOTシステムの現実味は薄れています。特に、OEMが管理するアセットを使用している、レガシー装置に対してリモート診断が必要となる、あるいは第三者のインテグレーターが頻繁に接続するケースなどでは難しいでしょう。
こうした連携は、デジタル変革戦略に基づくもの、あるいは運用効率目標のため、いずれの場合においてもOT環境をより接続された、より自動化された、よりITシステムと絡み合ったものにしつつあります。このような統合により新たな可能性が開かれますが、同時にOT環境は、従来のOTアーキテクチャが耐えるように設計されていないような、さまざまなリスクにさらされることになります。
最新化により生まれるギャップと可視性だけでは不十分な理由
最新化への取り組みにより新たなテクノロジーが産業環境にも導入され、IT環境とOT環境の統合とともに、可視性の欠如も生まれました。しかし、可視性を取り戻すことはスタート地点にすぎません。可視性は何が接続されているかを教えてくれるだけで、アクセスをどのように管理すべきかを教えてはくれません。そしてここがITとOTの分断が避けられなくなるポイントです。
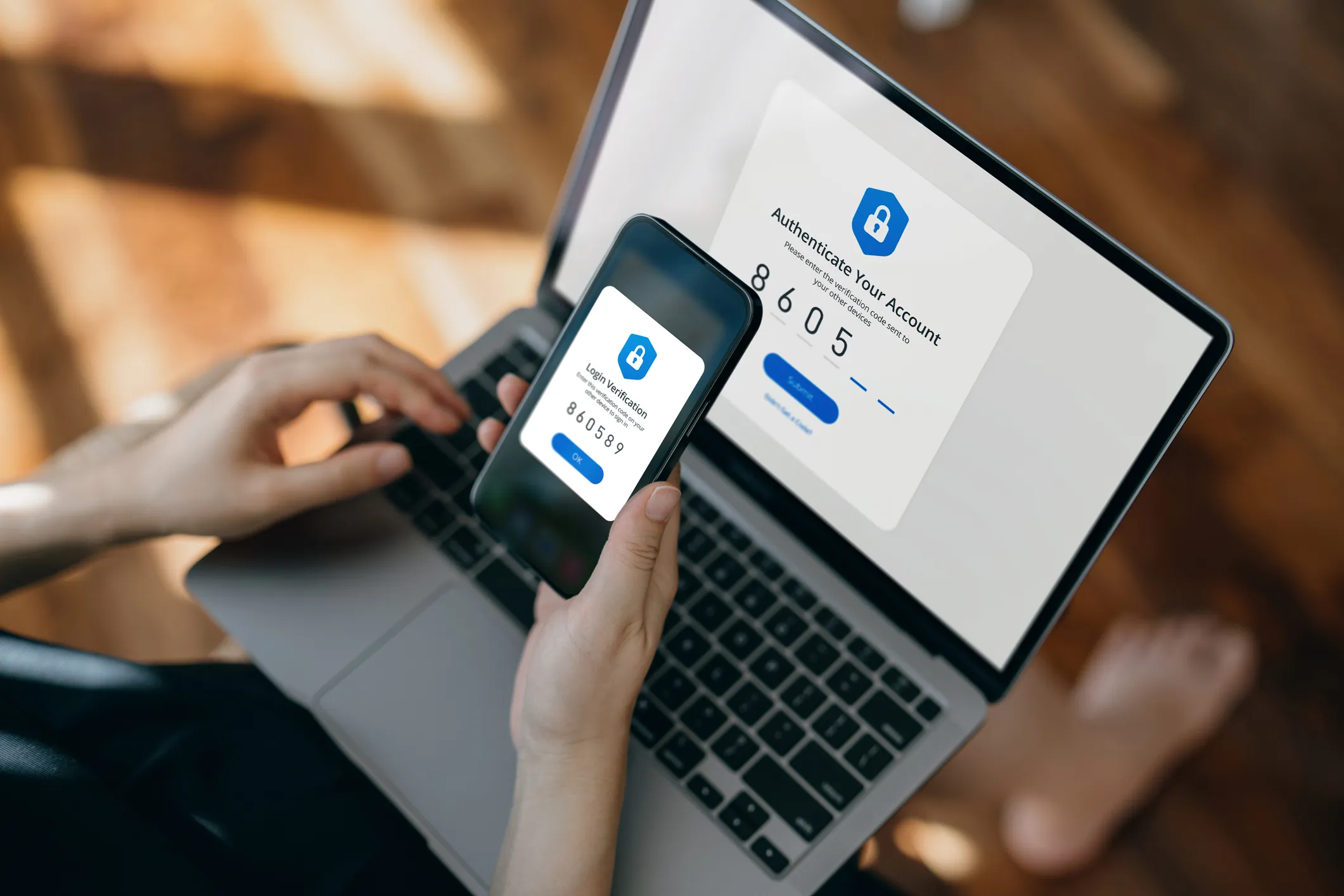
ITではうまく機能するセキュリティ戦略もOTではしばしば不十分なことがあります。OT環境ではわずかな失敗が環境への危険性、安全に関する事故、あるいは多大なコストを伴う稼働の停止などにつながるからです。さらに、安全なアクセス、分割の徹底、説明責任などを求める法規制の高まりからの圧力が加わると、可視性だけではもはや不十分であるということが明確になります。産業環境に今必要なのは、精密性です。そこではコントロールが必要です。そして、オペレーションを中断させることなくその両方を実現する必要があります。それには、アイデンティティベースのアクセス制御、リアルタイムのセッション監視、そして継続的なビヘイビア検知が必要となります。
監視されていないリモートアクセスによるリスク
このリスクは、アセットの故障をトラブルシューティングするためにOEMが緊急にアクセスを必要とする場合など、重大なタイミングで現れます。
限られた時間というプレッシャーのなかで、アクセス権限はしばしば最小限の検証ですばやく付与され、決められたプロセスが省略されることがあります。一旦中に入れば、コマンドの実行、設定の変更、あるいはネットワーク内で水平移動するなど、ユーザーのアクションに対するリアルタイムの監視はないケースがほとんどです。こうしたアクションは多くの場合記録されず、あるいは何かが壊れるまで気づかれません。問題が起こると、チームは断片的なログをつなぎ合わせる作業やインシデント後のフォレンジック作業に追われますが、説明責任の経路は明確ではありません。
アップタイムが決定的に重要であり安全性が譲れない環境においてこのレベルの不透明性では、まったく持続可能ではありません。
可視性のギャップ:誰が何を、いつ行っているか?
私たちが直面している根本的な問題は、誰がアクセス権を持っているかということと、そのアクセス権で何が行われているかという現実がつながっていないことです。
従来のアクセス管理ツールは認証情報を検証し、入り口を制限するかもしれませんが、セッション中のアクティビティについてリアルタイムの可視性を提供することは稀です。さらに、期待される振る舞いと、侵害、誤使用、設定間違いのかすかな兆候の違いを見分けられるものはさらに少ないでしょう。
その結果、OTチームとセキュリティチームはしばしば、問題の最も重要なカギとなる、意図と動作が見えない状況に置かれます。
ゼロトラストコントロールとAI駆動の検知でギャップを解消
OTでのリモートアクセスを管理することは、接続権限を付与するだけの問題ではもはやありません。厳密なアクセスパラメーターを徹底すると同時に、異常な振る舞いを継続的に監視することが必要です。これには、精密なアクセスコントロールと、インテリジェントかつリアルタイムの検知という2つの側面からのアプローチが必要です。
ゼロトラストアクセスコントロールが基盤となります。アイデンティティベースの、ジャストインタイム型のアクセス権を適用することにより、OT環境において、外部ベンダーやリモートユーザーが明示的に操作を承認されたシステムに対してのみ、そして必要な時間のみアクセスできるよう徹底できます。これらのコントロールのは、特定のデバイス、コマンド、あるいは機能へのアクセスに制限できるだけの細かさが必要です。これらの原則をPurdueモデル全体に一貫して適用することにより、OT環境を過剰なリスクにさらしてしまうキャッチオール式のVPNトンネル、ジャンプサーバー、そして脆いファイアウォール例外などへの依存を解消することができます。
アクセスコントロールは方程式の1部にすぎない
Darktrace / OT は継続的なAI駆動のビヘイビア検知でゼロトラストコントロールを補強します。静的なルールや事前定義済みのシグネチャに依存する代わりに、Darktraceは自己学習型AIを使用して、あらゆるデバイス、プロトコル、ユーザーに渡る環境全体で何が"正常”かについての、リアルタイムの、変化し続ける理解を構築します。これにより、微細な設定ミス、認証情報の間違った使用、あるいは水平移動を、後から知るのではなく発生と同時にリアルタイムに検知することができます。
ユーザーのアイデンティティとセッション内のアクティビティを、ビヘイビア分析と相関付けることによりDarktraceは全体像を明らかにし、誰がどのシステムにアクセスしたか、どのようなアクションを実行したか、それらのアクションはこれまでの通常状態と比較してどうか、そして逸脱が発生したかどうかを知ることができます。リモートアクセスセッションに関連する当て推量を取り除き、明確な、コンテキストを含めた情報を提供します。
重要な点は、Darktraceがオペレーション内のノイズと本物のサイバー脅威に関連した異常を区別することです。CVEアラートから日常的なアクティビティまですべてを1つのストリームにまとめてしまう他のツールとは異なり、Darktraceは正しいリモートアクセス動作とミスや乱用の可能性を区別します。つまり、組織はコンプライアンスの観点からアクセスを監査できるとともに、セッションがもしエクスプロイトされていれば、その不正な使用は、高確度なサイバー脅威に関連したアラートとして確認できることを意味します。このアプローチはコントロールを補完するものとして利用することができ、もしアクセス権が過剰に拡大されている、あるいは間違って利用されている場合にも、その挙動を可視化し、それに対するアクションが可能です。
たとえば、セッションにおいて、普段とは異なるコマンドシーケンス、新たな水平移動経路、あるいはスケジュールされた時間帯以外のアクティビティが発生するなど、学習したベースラインを逸脱した場合、Darktraceは即座にフラグを立てることができます。これらの情報を基に、人手による調査を開始する、あるいはアクセス権のはく奪やセッション隔離などポリシーに応じて自動的にアクションをトリガーするなどが可能です。
この多層的なアプローチにより、リアルタイムの意思決定が可能になり、中断のないオペレーションが確保され、重要な作業を遅らせたりワークフローを中断したりすることなくあらゆるリモートアクティビティに対して完全な説明責任を担保することができます。
ゼロトラストアクセスとAI駆動の監視の組み合わせ:
- きめ細かいアクセス適用: ゼロトラスト原則に従いコンプライアンスの要件を満たす、ロールベースの、ジャストインタイムのアクセス。
- コンテキストを加えた脅威検知: 自己学習型AIが異常なOT動作をリアルタイムに検知し、脅威をアクセスイベントとユーザーアクティビティに結びつける。
- 自動化されたセッション管理: 動作の異常によってアラートや自動制御をトリガーすることができ、アップタイムを維持しつつ封じ込めまでの時間を短縮。
- Purdueレイヤー全体に渡る完全な可視性: 相関付けされたデータにより、IT、OTレイヤー全体にわたりリモートアクセスイベントをデバイスレベルの動作と結びつけることが可能。
- スケーラブルかつ受動的な監視: 動作を受動的に学習することによりレガシーシステムやエアギャップされた環境全体をカバーすることが可能、シグネチャやエージェント、侵入型スキャンは必要なし。
妥協のない完全なセキュリティ
オペレーションの敏捷性かそれともセキュリティコントロールか、あるいは可視性かそれとも簡潔性か、これらのどちらかを選ぶ必要はもうありません。ゼロトラストアプローチをリアルタイムのAI検知で強化することにより、権限と動作の両方を認識し、産業オペレーションの現実に即した、多様な環境にスケール可能な、安全なリモートアクセスを実現することができます。
重要インフラの保護において、検知を伴わないアクセスはリスクであり、アクセスコントロールを伴わない検知は不完全だからです。








%201.png)









