Lessons learned from OT cyber attacks
Over the past decade, some of the most disruptive attacks on power utilities have shown the limits of signature-based detection and reshaped how defenders think about OT security. Each incident reinforced that signatures are too narrow and reactive to serve as the foundation of defense.
2015: BlackEnergy 3 in Ukraine
According to CISA, on December 23, 2015, Ukrainian power companies experienced unscheduled power outages affecting a large number of customers — public reports indicate that the BlackEnergy malware was discovered on the companies’ computer networks.
2016: Industroyer/CrashOverride
CISA describes CrashOverride malwareas an “extensible platform” reported to have been used against critical infrastructure in Ukraine in 2016. It was capable of targeting industrial control systems using protocols such as IEC‑101, IEC‑104, and IEC‑61850, and fundamentally abused legitimate control system functionality to deliver destructive effects. CISA emphasizes that “traditional methods of detection may not be sufficient to detect infections prior to the malware execution” and recommends behavioral analysis techniques to identify precursor activity to CrashOverride.
2017: TRITON Malware
The U.S. Department of the Treasury reports that the Triton malware, also known as TRISIS or HatMan, was “designed specifically to target and manipulate industrial safety systems” in a petrochemical facility in the Middle East. The malware was engineered to control Safety Instrumented System (SIS) controllers responsible for emergency shutdown procedures. During the attack, several SIS controllers entered a failed‑safe state, which prevented the malware from fully executing.
The broader lessons
These events revealed three enduring truths:
- Signatures have diminishing returns: BlackEnergy showed that while signatures can eventually identify adapted IT malware, they arrive too late to prevent OT disruption.
- Behavioral monitoring is essential: CrashOverride demonstrated that adversaries abuse legitimate industrial protocols, making behavioral and anomaly detection more effective than traditional signature methods.
- Critical safety systems are now targets: TRITON revealed that attackers are willing to compromise safety instrumented systems, elevating risks from operational disruption to potential physical harm.
The natural progression for utilities is clear. Static, file-based defenses are too fragile for the realities of OT.
These incidents showed that behavioral analytics and anomaly detection are far more effective at identifying suspicious activity across industrial systems, regardless of whether the malicious code has ever been seen before.
Strategic risks of overreliance on signatures
- False sense of security: Believing signatures will block advanced threats can delay investment in more effective detection methods.
- Resource drain: Constantly updating, tuning, and maintaining signature libraries consumes valuable staff resources without proportional benefit.
- Adversary advantage: Nation-state and advanced actors understand the reactive nature of signature defenses and design attacks to circumvent them from the start.
Recommended Alternatives (with real-world OT examples)
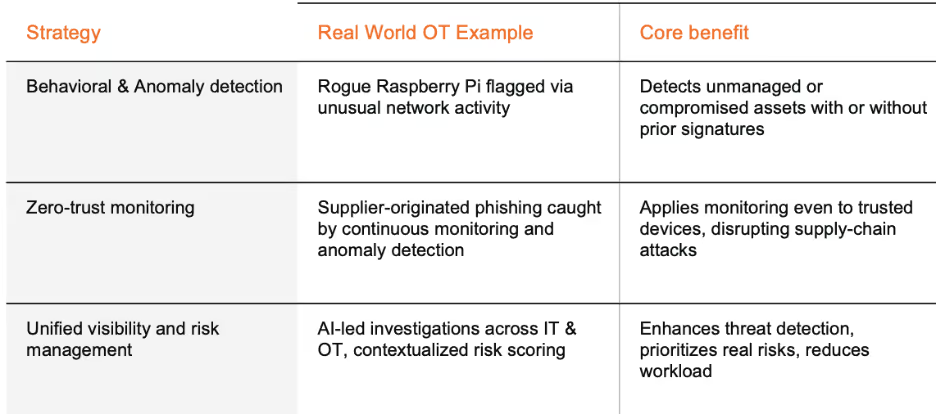
Behavioral and anomaly detection
Rather than relying on signatures, focusing on behavior enables detection of threats that have never been seen before—even trusted-looking devices.
Real-world insight:
In one OT setting, a vendor inadvertently left a Raspberry Pi on a customer’s ICS network. After deployment, Darktrace’s system flagged elastic anomalies in its HTTPS and DNS communication despite the absence of any known indicators of compromise. The alerting included sustained SSL increases, agent‑beacon activity, and DNS connections to unusual endpoints, revealing a possible supply‑chain or insider risk invisible to static tools.
Darktrace’s AI-driven threat detection aligns with the zero-trust principle of assuming the risk of a breach. By leveraging AI that learns an organization’s specific patterns of life, Darktrace provides a tailored security approach ideal for organizations with complex supply chains.
Threat intelligence sharing & building toward zero-trust philosophy
Frameworks such as MITRE ATT&CK for ICS provide a common language to map activity against known adversary tactics, helping teams prioritize detections and response strategies. Similarly, information-sharing communities like E-ISAC and regional ISACs give utilities visibility into the latest tactics, techniques, and procedures (TTPs) observed across the sector. This level of intel can help shift the focus away from chasing individual signatures and toward building resilience against how adversaries actually operate.
Real-world insight:
Darktrace’s AI embodies zero‑trust by assuming breach potential and continually evaluating all device behavior, even those deemed trusted. This approach allowed the detection of an anomalous SharePoint phishing attempt coming from a trusted supplier, intercepted by spotting subtle patterns rather than predefined rules. If a cloud account is compromised, unauthorized access to sensitive information could lead to extortion and lateral movement into mission-critical systems for more damaging attacks on critical-national infrastructure.
This reinforces the need to monitor behavioral deviations across the supply chain, not just known bad artifacts.
Defense-in-Depth with OT context & unified visibility
OT environments demand visibility that spans IT, OT, and IoT layers, supported by risk-based prioritization.
Real-world insight:
Darktrace / OT offers unified AI‑led investigations that break down silos between IT and OT. Smaller teams can see unusual outbound traffic or beaconing from unknown OT devices, swiftly investigate across domains, and get clear visibility into device behavior, even when they lack specialized OT security expertise.
Moreover, by integrating contextual risk scoring, considering real-world exploitability, device criticality, firewall misconfiguration, and legacy hardware exposure, utilities can focus on the vulnerabilities that genuinely threaten uptime and safety, rather than being overwhelmed by CVE noise.
Regulatory alignment and positive direction
Industry regulations are beginning to reflect this evolution in strategy. NERC CIP-015 requires internal network monitoring that detects anomalies, and the standard references anomalies 15 times. In contrast, signature-based detection is not mentioned once.
This regulatory direction shows that compliance bodies understand the limitations of static defenses and are encouraging utilities to invest in anomaly-based monitoring and analytics. Utilities that adopt these approaches will not only be strengthening their resilience but also positioning themselves for regulatory compliance and operational success.
Conclusion
Signature-based detection retains utility for common IT malware, but it cannot serve as the backbone of security for power utilities. History has shown that major OT attacks are rarely stopped by signatures, since each campaign targets specific systems with customized tools. The most dangerous adversaries, from insiders to nation-states, actively design their operations to avoid detection by signature-based tools.
A more effective strategy prioritizes behavioral analytics, anomaly detection, and community-driven intelligence sharing. These approaches not only catch known threats, but also uncover the subtle anomalies and novel attack techniques that characterize tomorrow’s incidents.














.png)









%201.png)