What is Medusa Ransomware in 2025?
In 2025, the Medusa Ransomware-as-a-Service (RaaS) emerged as one of the top 10 most active ransomware threat actors [1]. Its growing impact prompted a joint advisory from the US Cybersecurity and Infrastructure Security Agency (CISA) and the Federal Bureau of Investigation (FBI) [3]. As of January 2026, more than 500 organizations have fallen victim to Medusa ransomware [2].
Darktrace previously investigated Medusa in a 2024 blog, but the group’s rapid expansion and new intelligence released in late 2025 has lead Darktrace’s Threat Research team to investigate further. Recent findings include Microsoft’s research on Medusa actors exploiting a vulnerability in Fortra’s GoAnywhere MFT License Servlet (CVE-2025-10035)[4] and Zencec’s report on Medusa’s abuse of flaws in SimpleHelp’s remote support software (CVE-2024-57726, CVE-2024-57727, CVE-2024-57728) [5].
Reports vary on when Medusa first appeared in the wild. Some sources mention June 2021 as the earliest sightings, while others point to late 2022, when its developers transitioned to the RaaS model, as the true beginning of its operation [3][11].
Medusa Ransomware history and background
The group behind Medusa is known by several aliases, including Storm-1175 and Spearwing [4] [7]. Like its mythological namesake, Medusa has many “heads,” collaborating with initial access brokers (IABs) and, according to some evidence, affiliating with Big Game Hunting (BGH) groups such as Frozen Spider, as well as the cybercriminal group UNC7885 [3][6][13].
Use of Cyrillic in its scripts, activity on Russian-language cybercrime forums, slang unique to Russian criminal subcultures, and avoidance of targets in Commonwealth of Independent States (CIS) countries suggest that Medusa operates from Russia or an allied state [11][12].
Medusa ransomware should not be confused with other similarly named malware, such as the Medusa Android Banking Trojan, the Medusa Botnet/Medusa Stealer, or MedusaLocker ransomware. It is easily distinguishable from these variants because it appends the extension .MEDUSA to encrypted files and drops the ransom note !!!READ_ME_MEDUSA!!!.txt on compromised systems [8].
Who does Medusa Ransomware target?
The group appears to show little restraint, indiscriminately attacking organizations across all sectors, including healthcare, and is known to employ triple extortion tactics whereby sensitive data is encrypted, victims are threatened with data leaks, and additional pressure is applied through DDoS attacks or contacting the victim’s customers, rather than the more common double extortion model [13].
Medusa Ransomware TTPs
To attain initial access, Medusa actors typically purchase access to already compromised devices or accounts via IABs that employ phishing, credential stuffing, or brute-force attacks, and also target vulnerable or misconfigured Internet-facing systems.
In addition to the GoAnywhere MFT and SimpleHelp RMM flaws, other vulnerabilities exploited in Medusa attacks include ConnectWise ScreenConnect RMM (CVE-2024-1709), Microsoft Exchange Server (CVE-2021-34473, also known as ProxyShell), and Fortinet Enterprise Management Servers (CVE-2023-48788) [18][19][20][21][24][25].
Darktrace’s Coverage of Medusa Ransomware
Between December 2023 and November 2025, Darktrace observed multiple cases of file encryption related to Medusa ransomware across its customer base. When enabled, Darktrace’s Autonomous Response capability intervened early in the attack chain, blocking malicious activity before file encryption could begin.
Some of the affected were based in Europe, the Middle East and Africa (EMEA), others in the Americas (AMS), and the remainder in the Asia-Pacific and Japan region. The most impacted sectors were financial services and the automotive industry, followed by healthcare, and finally organizations in arts, entertainment and recreation, ICT, and manufacturing.
Remote Monitoring and Management (RMM) tool abuse
In most customer environments where Medusa file encryption attempts were observed, and in one case where the compromise was contained before encryption, unusual external HTTP connections associated with JWrapper were also detected. JWrapper is a legitimate tool designed to simplify the packaging, distribution, and management of Java applications, enabling the creation of executables that run across different operating systems. Many of the destination IP addresses involved in this activity were linked to SimpleHelp servers or associated with Atera.
Medusa actors appear to favor RMM tools such as SimpleHelp. Unpatched or misconfigured SimpleHelp RMM servers can serve as an initial access vector to the victims’ infrastructure. After gaining access to SimpleHelp management servers, the threat actors edit server configuration files to redirect existing SimpleHelp RMM agents to communicate with unauthorized servers under their control.
The SimpleHelp tool is not only used for command-and-control (C2) and enabling persistence but is also observed during lateral movement within the network, downloading additional attack tools, data exfiltration, and even ransomware binary execution. Other legitimate remote access tools abused by Medusa in a similar manner to evade detection include Atera, AnyDesk, ScreenConnect, eHorus, N-able, PDQ Deploy/Inventory, Splashtop, TeamViewer, NinjaOne, Navicat, and MeshAgent [4][5][15][16][17].
Data exfiltration
Another correlation among Darktrace customers affected by Medusa was observed during the data exfiltration phase. In several environments, data was exfiltrated to the endpoints erp.ranasons[.]com or pruebas.pintacuario[.]mx (143.110.243[.]154, 144.217.181[.]205) over ports 443, 445, and 80. erp.ranasons[.]com was seemingly active between November 2024 and September 2025, while pruebas.pintacuario[.]mx was seen from November 2024 to March 2025. Evidence suggests that pruebas.pintacuario[.]mx previously hosted a SimpleHelp server [22][23].
Apart from RMM tools, Medusa is also known to use Rclone and Robocopy for data exfiltration [3][19]. During one Medusa compromise detected in mid-2024, the customer’s data was exfiltrated to external destinations associated with the Ngrok proxy service using an SSH-2.0-rclone client.
Medusa Compromise Leveraging SimpleHelp
In Q4 2025, Darktrace assisted a European company impacted by Medusa ransomware. The organization had partial Darktrace / NETWORK coverage and had configured Darktrace’s Autonomous Response capability to require manual confirmation for all actions. Despite these constraints, data received through the customer’s security integration with CrowdStrike Falcon enabled Darktrace analysts to reconstruct the attack chain, although the initial access vector remains unclear due to limited visibility.
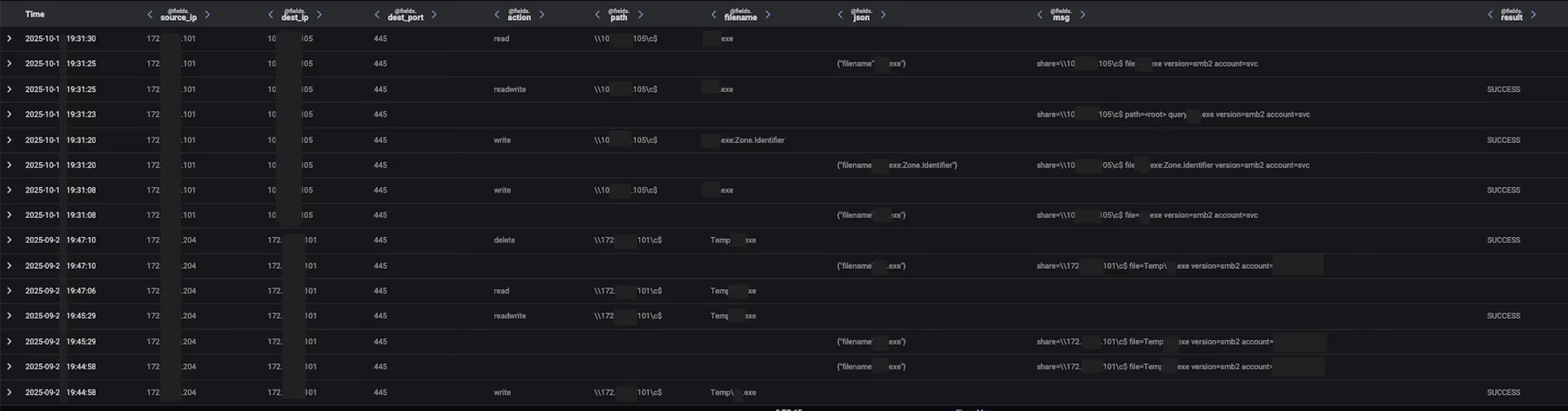
In late September 2025, a device out of the scope of Darktrace's visibility began scanning the network and using RDP, NTLM/SMB, DCE_RPC, and PowerShell for lateral movement.
CrowdStrike “Defense Evasion: Disable or Modify Tools” alerts related to a suspicious driver (c:\windows\[0-9a-b]{4}.exe) and a PDQ Deploy executable (share=\\<device_hostname>\ADMIN$ file=AdminArsenal\PDQDeployRunner\service-1\exec\[0-9a-b]{4}.exe) suggest that the attackers used the Bring Your Own Vulnerable Driver (BYOVD) technique to terminate antivirus processes on network devices, leveraging tools such as KillAV or AbyssWorker along with the PDQ Software Deployment solution [19][26].
A few hours later, Darktrace observed the same device that had scanned the network writing Temp\[a-z]{2}.exe over SMB to another device on the same subnet. According to data from the CrowdStrike alert, this executable was linked to an RMM application located at C:\Users\<compromised_user>\Documents\[a-z]{2}.exe. The same compromised user account later triggered a CrowdStrike “Command and Control: Remote Access Tools” alert when accessing C:\ProgramData\JWrapper-Remote Access\JWrapper-Remote Access Bundle-[0-9]{11}\JWrapperTemp-[0-9]{10}-[0-9]{1}-app\bin\windowslauncher.exe [27].
Soon after, the destination device and multiple other network devices began establishing connections to 31.220.45[.]120 and 213.183.63[.]41, both of which hosted malicious SimpleHelp RMM servers. These C2 connections continued for more than 20 days after the initial compromise.
CrowdStrike integration alerts for the execution of robocopy . "c:\windows\\" /COPY:DT /E /XX /R:0 /W:0 /NP /XF RunFileCopy.cmd /IS /IT commands on several Windows servers, suggested that this utility was likely used to stage files in preparation for data exfiltration [19].
Around two hours later, Darktrace detected another device connecting to the attacker’s SimpleHelp RMM servers. This internal server had ‘doc’ in its hostname, indicating it was likely a file server. It was observed downloading documents from another internal server over SMB and uploading approximately 70 GiB of data to erp.ranasons[.]com (143.110.243[.]154:443).
![Data uploaded to erp.ranasons[.]com and the number of model alerts from the exfiltrating device, represented by yellow and orange dots.](https://cdn.prod.website-files.com/626ff4d25aca2edf4325ff97/69601f43842f8016c3898afd_Screenshot%202026-01-08%20at%201.18.52%E2%80%AFPM.avif)
Darktrace’s Cyber AI Analyst autonomously investigated the unusual connectivity, correlating the separate C2 and data exfiltration events into a single incident, providing greater visibility into the ongoing attack.
![Cyber AI Analyst identified a file server making C2 connections to an attacker-controlled SimpleHelp server (213.183.63[.]41) and exfiltrating data to erp.ranasons[.]com.](https://cdn.prod.website-files.com/626ff4d25aca2edf4325ff97/69601f524d01b4d269313c38_Screenshot%202026-01-08%20at%201.19.06%E2%80%AFPM.avif)
![The same file server that connected to 213.183.63[.]41 and exfiltrated data to erp.ranasons[.]com was also observed attempting to connect to an IP address associated with Moscow, Russia (193.37.69[.]154:7070).](https://cdn.prod.website-files.com/626ff4d25aca2edf4325ff97/69601f6a598a3380572e284e_Screenshot%202026-01-08%20at%201.19.32%E2%80%AFPM.avif)
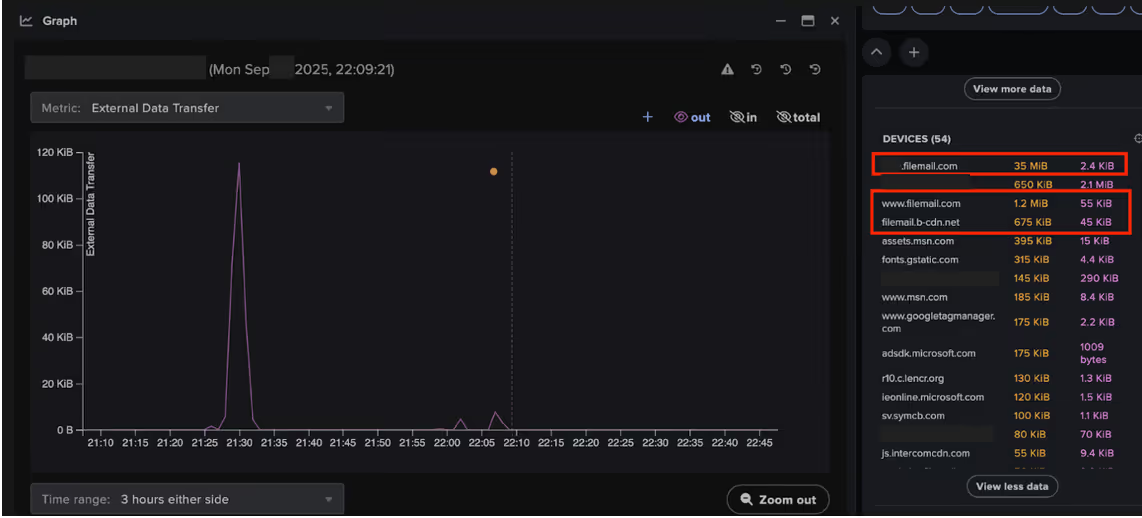
One of the devices connecting to the attacker's SimpleHelp RMM servers was also observed downloading 35 MiB from [0-9]{4}.filemail[.]com. Filemail, a legitimate file-sharing service, has reportedly been abused by Medusa actors to deliver additional malicious payloads [11].
Finally, integration alerts related to the ransomware binary, such as c:\windows\system32\gaze.exe and <device_hostname>\ADMIN$ file=AdminArsenal\PDQDeployRunner\service-1\exec\gaze.exe, along with “!!!READ_ME_MEDUSA!!!.txt” ransom notes were observed on network devices. This indicates that file encryption in this case was most likely carried out directly on the victim hosts rather than via the SMB protocol [3].
Conclusion
Threat actors, including nation-state actors and ransomware groups like Medusa, have long abused legitimate commercial RMM tools, typically used by system administrators for remote monitoring, software deployment, and device configuration, instead of relying on remote access trojans (RATs).
Attackers employ existing authorized RMM tools or install new remote administration software to enable persistence, lateral movement, data exfiltration, and ingress tool transfer. By mimicking legitimate administrative behavior, RMM abuse enables attackers to evade detection, as security software often implicitly trusts these tools, allowing attackers to bypass traditional security controls [28][29][30].
To mitigate such risks, organizations should promptly patch publicly exposed RMM servers and adopt anomaly-based detection solutions, like Darktrace / NETWORK, which can distinguish legitimate administrative activity from malicious behavior, applying rapid response measures through its Autonomous Response capability to stop attacks in their tracks.
Darktrace delivers comprehensive network visibility and Autonomous Response capabilities, enabling real-time detection of anomalous activity and rapid mitigation, even if an organization fall under Medusa’s gaze.
Credit to Signe Zaharka (Principal Cyber Analyst) and Emma Foulger (Global Threat Research Operations Lead
Edited by Ryan Traill (Analyst Content Lead)
Appendices
List of Indicators of Compromise (IoCs)
IoC - Type - Description + Confidence + Time Observed
185.108.129[.]62 IP address Malicious SimpleHelp server observed during Medusa attacks (High confidence) - March 7, 2023
185.126.238[.]119 IP address Malicious SimpleHelp server observed during Medusa attacks (High confidence) - November 26-27, 2024
213.183.63[.]41 IP address Malicious SimpleHelp server observed during Medusa attacks (High confidence) - November 28, 2024 - Sep 30, 2025
213.183.63[.]42 IP address Malicious SimpleHelp server observed during Medusa attacks (High confidence) - July 4 -9 , 2024
31.220.45[.]120 IP address Malicious SimpleHelp server observed during Medusa attacks (High confidence) - September 12 - Oct 20 , 2025
91.92.246[.]110 IP address Malicious SimpleHelp server observed during Medusa attacks (High confidence) - May 24, 2024
45.9.149[.]112:15330 IP address Malicious SimpleHelp server observed during Medusa attacks (High confidence) - June 21, 2024
89.36.161[.]12 IP address Malicious SimpleHelp server observed during Medusa attacks (High confidence) - June 26-28, 2024
193.37.69[.]154:7070 IP address Suspicious RU IP seen on a device being controlled via SimpleHelp and exfiltrating data to a Medusa related endpoint - September 30 - October 20, 2025
erp.ranasons[.]com·143.110.243[.]154 Hostname Data exfiltration destination - November 27, 2024 - September 30, 2025
pruebas.pintacuario[.]mx·144.217.181[.]205 - Hostname Data exfiltration destination - November 27, 2024 - March 26, 2025
lirdel[.]com · 44.235.83[.]125/a.msi (1b9869a2e862f1e6a59f5d88398463d3962abe51e19a59) File & hash Atera related file downloaded with PowerShell - June 20, 2024
wizarr.manate[.]ch/108.215.180[.]161:8585/$/1dIL5 File Suspicious file observed on one of the devices exhibiting unusual activity during a Medusa compromise - February 28, 2024
!!!READ_ME_MEDUSA!!!.txt" File - Ransom note
*.MEDUSA - File extension File extension added to encrypted files
gaze.exe – File - Ransomware binary
Darktrace Model Coverage
Darktrace / NETWORK model detections triggered during connections to attacker controlled SimpleHelp servers:
Anomalous Connection/Anomalous SSL without SNI to New External
Anomalous Connection/Multiple Connections to New External UDP Port
Anomalous Connection/New User Agent to IP Without Hostname
Anomalous Connection/Rare External SSL Self-Signed
Anomalous Connection/Suspicious Self-Signed SSL
Anomalous File/EXE from Rare External Location
Anomalous Server Activity/Anomalous External Activity from Critical Network Device
Anomalous Server Activity/New User Agent from Internet Facing System
Anomalous Server Activity/Outgoing from Server
Anomalous Server Activity/Rare External from Server
Compromise/High Volume of Connections with Beacon Score
Compromise/Large Number of Suspicious Failed Connections
Compromise/Ransomware/High Risk File and Unusual SMB
Device/New User Agent
Unusual Activity/Unusual External Data to New Endpoint
Unusual Activity/Unusual External Data Transfer
Darktrace / NETWORK Model Detections during the September/October 2025 Medusa attack:
Anomalous Connection / Data Sent to Rare Domain
Anomalous Connection / Download and Upload
Anomalous Connection / Low and Slow Exfiltration
Anomalous Connection / New User Agent to IP Without Hostname
Anomalous Connection / Uncommon 1 GiB Outbound
Anomalous Connection / Unusual Admin RDP Session
Anomalous Connection / Unusual Incoming Long Remote Desktop Session
Anomalous Connection / Unusual Long SSH Session
Anomalous File / EXE from Rare External Location
Anomalous File / Internal/Unusual Internal EXE File Transfer
Anomalous Server Activity / Anomalous External Activity from Critical Network Device
Anomalous Server Activity / Outgoing from Server
Anomalous Server Activity / Rare External from Server
Compliance / Default Credential Usage
Compliance / High Priority Compliance Model Alert
Compliance / Outgoing NTLM Request from DC
Compliance / Possible Unencrypted Password File On Server
Compliance / Remote Management Tool On Server
Compromise / Large Number of Suspicious Failed Connections
Compromise / Large Number of Suspicious Successful Connections
Compromise / Ransomware/High Risk File and Unusual SMB
Compromise / Suspicious Beaconing Behaviour
Compromise / Suspicious HTTP and Anomalous Activity
Compromise / Sustained SSL or HTTP Increase
Compromise / Sustained TCP Beaconing Activity To Rare Endpoint
Device / ICMP Address Scan
Device / Increase in New RPC Services
Device / Initial Attack Chain Activity
Device / Large Number of Model Alert
Device / Large Number of Model Alerts from Critical Network Device
Device / Lateral Movement and C2 Activity
Device / Multiple C2 Model Alert
Device / Network Scan
Device / Possible SMB/NTLM Reconnaissance
Device / Spike in LDAP Activity
Device / Suspicious Network Scan Activity
Device / Suspicious SMB Scanning Activity
Security Integration / High Severity Integration Incident
Security Integration / Low Severity Integration Incident
Unusual Activity / Enhanced Unusual External Data Transfer
Unusual Activity / Internal Data Transfer
Unusual Activity / Unusual External Activity
Unusual Activity / Unusual External Data to New Endpoint
Unusual Activity / Unusual External Data Transfer
User / New Admin Credentials on Server
Autonomous Response Actions
Antigena / Network/External Threat/Antigena File then New Outbound Block
Antigena / Network/External Threat/Antigena Ransomware Block
Antigena / Network/External Threat/Antigena Suspicious Activity Block
Antigena / Network/External Threat/Antigena Suspicious File Block
Antigena / Network/Insider Threat/Antigena Internal Anomalous File Activity
Antigena / Network/Insider Threat/Antigena Internal Data Transfer Block
Antigena / Network/Insider Threat/Antigena Large Data Volume Outbound Block
Antigena / Network/Insider Threat/Antigena Network Scan Block
Antigena / Network/Insider Threat/Antigena Unusual Privileged User Activities Block
Antigena / Network/Significant Anomaly/Antigena Alerts Over Time Block
Antigena / Network/Significant Anomaly/Antigena Controlled and Model Alert
Antigena / Network/Significant Anomaly/Antigena Enhanced Monitoring from Server Block
Antigena / Network/Significant Anomaly/Antigena Significant Server Anomaly Block
Antigena / Network/Significant Anomaly/Repeated Antigena Alerts
MITRE ATT&CK Mapping
Technique Name, Tactic, ID, Sub-Technique
Application Layer Protocol , COMMAND AND CONTROL , T1071
Automated Collection , COLLECTION , T1119
Automated Exfiltration , EXFILTRATION , T1020
Brute Force , CREDENTIAL ACCESS , T1110
Client Configurations , RECONNAISSANCE , T1592.004 , T1592
Cloud Accounts , DEFENSE EVASION , PERSISTENCE , PRIVILEGE ESCALATION , INITIAL ACCESS , T1078.004 , T1078
Command-Line Interface , EXECUTION ICS , T0807
Credential Stuffing , CREDENTIAL ACCESS , T1110.004 , T1110
Data Encrypted for Impact , IMPACT , T1486
Data from Network Shared Drive , COLLECTION , T1039
Data Obfuscation , COMMAND AND CONTROL , T1001
Data Staged , COLLECTION , T1074
Data Transfer Size Limits , EXFILTRATION , T1030
Default Accounts , DEFENSE EVASION , PERSISTENCE , PRIVILEGE ESCALATION , INITIAL ACCESS , T1078.001 , T1078
Default Credentials , LATERAL MOVEMENT ICS , T0812
Distributed Component Object Model , LATERAL MOVEMENT , T1021.003 , T1021
Drive-by Compromise , INITIAL ACCESS ICS , T0817
Drive-by Compromise , INITIAL ACCESS , T1189
Email Collection , COLLECTION , T1114
Exfiltration Over Alternative Protocol , EXFILTRATION , T1048
Exfiltration Over C2 Channel , EXFILTRATION , T1041
Exfiltration to Cloud Storage , EXFILTRATION , T1567.002 , T1567
Exploit Public-Facing Application , INITIAL ACCESS , T1190
Exploitation for Privilege Escalation , PRIVILEGE ESCALATION , T0890
Exploitation of Remote Services , LATERAL MOVEMENT , T1210
Exploits , RESOURCE DEVELOPMENT , T1588.005 , T1588
File and Directory Discovery , DISCOVERY , T1083
File Deletion , DEFENSE EVASION , T1070.004 , T1070
Graphical User Interface , EXECUTION ICS , T0823
Ingress Tool Transfer , COMMAND AND CONTROL , T1105
Lateral Tool Transfer , LATERAL MOVEMENT , T1570
LLMNR/NBT-NS Poisoning and SMB Relay , CREDENTIAL ACCESS , COLLECTION , T1557.001 , T1557
Malware , RESOURCE DEVELOPMENT , T1588.001 , T1588
Network Service Scanning , DISCOVERY , T1046
Network Share Discovery , DISCOVERY , T1135
Non-Application Layer Protocol , COMMAND AND CONTROL , T1095
Non-Standard Port , COMMAND AND CONTROL , T1571
One-Way Communication , COMMAND AND CONTROL , T1102.003 , T1102
Pass the Hash , DEFENSE EVASION , LATERAL MOVEMENT , T1550.002 , T1550
Password Cracking , CREDENTIAL ACCESS , T1110.002 , T1110
Password Guessing , CREDENTIAL ACCESS , T1110.001 , T1110
Password Spraying , CREDENTIAL ACCESS , T1110.003 , T1110
Program Download , LATERAL MOVEMENT ICS , T0843
Program Upload , COLLECTION ICS , T0845
Remote Access Software , COMMAND AND CONTROL , T1219
Remote Desktop Protocol , LATERAL MOVEMENT , T1021.001 , T1021
Remote System Discovery , DISCOVERY , T1018
Scanning IP Blocks , RECONNAISSANCE , T1595.001 , T1595
Scheduled Transfer , EXFILTRATION , T1029
Spearphishing Attachment , INITIAL ACCESS ICS , T0865
Standard Application Layer Protocol , COMMAND AND CONTROL ICS , T0869
Supply Chain Compromise , INITIAL ACCESS ICS , T0862
User Execution , EXECUTION ICS , T0863
Valid Accounts , DEFENSE EVASION , PERSISTENCE , PRIVILEGE ESCALATION , INITIAL ACCESS , T1078
Valid Accounts , PERSISTENCE ICS , LATERAL MOVEMENT ICS , T0859
Vulnerabilities , RESOURCE DEVELOPMENT , T1588.006 , T1588
Vulnerability Scanning , RECONNAISSANCE , T1595.002 , T1595
Web Protocols , COMMAND AND CONTROL , T1071.001 , T1071
References
1. https://www.intel471.com/blog/threat-hunting-case-study-medusa-ransomware
2. https://www.ransomware.live/group/medusa
3. https://www.cisa.gov/news-events/cybersecurity-advisories/aa25-071a
5. https://zensec.co.uk/blog/how-rmm-abuse-fuelled-medusa-dragonforce-attacks/
6. https://www.checkpoint.com/cyber-hub/threat-prevention/ransomware/medusa-ransomware-group/
7. https://cyberpress.org/medusa-ransomware-attacks-spike-42/
8. https://blog.barracuda.com/2025/02/25/medusa-ransomware-and-its-cybercrime-ecosystem
11. https://unit42.paloaltonetworks.com/medusa-ransomware-escalation-new-leak-site/
13. https://redpiranha.net/news/medusa-ransomware-everything-you-need-know
14. https://www.theregister.com/2025/03/13/medusa_ransomware_infects_300_critical/
16. https://nagomisecurity.com/medusa-ransomware-us-cert-alert
19. https://thehackernews.com/2025/03/medusa-ransomware-hits-40-victims-in.html
21. https://brandefense.io/blog/stone-gaze-in-depth-analysis-of-medusa-ransomware/
22. https://www.darktrace.com/ja/blog/2025-cyber-threat-landscape-darktraces-mid-year-review
23. https://www.joesandbox.com/analysis/1576447/0/html
24. https://blog.barracuda.com/2025/02/25/medusa-ransomware-and-its-cybercrime-ecosystem
25. https://shassit.mit.edu/news/medusa-ransomware-attacks-on-gmail/
26. https://thehackernews.com/2025/03/medusa-ransomware-uses-malicious-driver.html
27. https://www.cisa.gov/news-events/cybersecurity-advisories/aa25-163a
28. https://www.catonetworks.com/blog/cato-ctrl-investigation-of-rmm-tools/
29. https://redcanary.com/threat-detection-report/trends/rmm-tools/

















%201.png)