Investigating cloud attacks with Darktrace/ Forensic Acquisition & Investigation
Darktrace / Forensic Acquisition & Investigation™ is the industry’s first truly automated forensic solution purpose-built for the cloud. This blog will demonstrate how an investigation can be carried out against a compromised cloud server in minutes, rather than hours or days.
The compromised server investigated in this case originates from Darktrace’s Cloudypots system, a global honeypot network designed to observe adversary activity in real time across a wide range of cloud services. Whenever an attacker successfully compromises one of these honeypots, a forensic copy of the virtual server's disk is preserved for later analysis. Using Forensic Acquisition & Investigation, analysts can then investigate further and obtain detailed insights into the compromise including complete attacker timelines and root cause analysis.
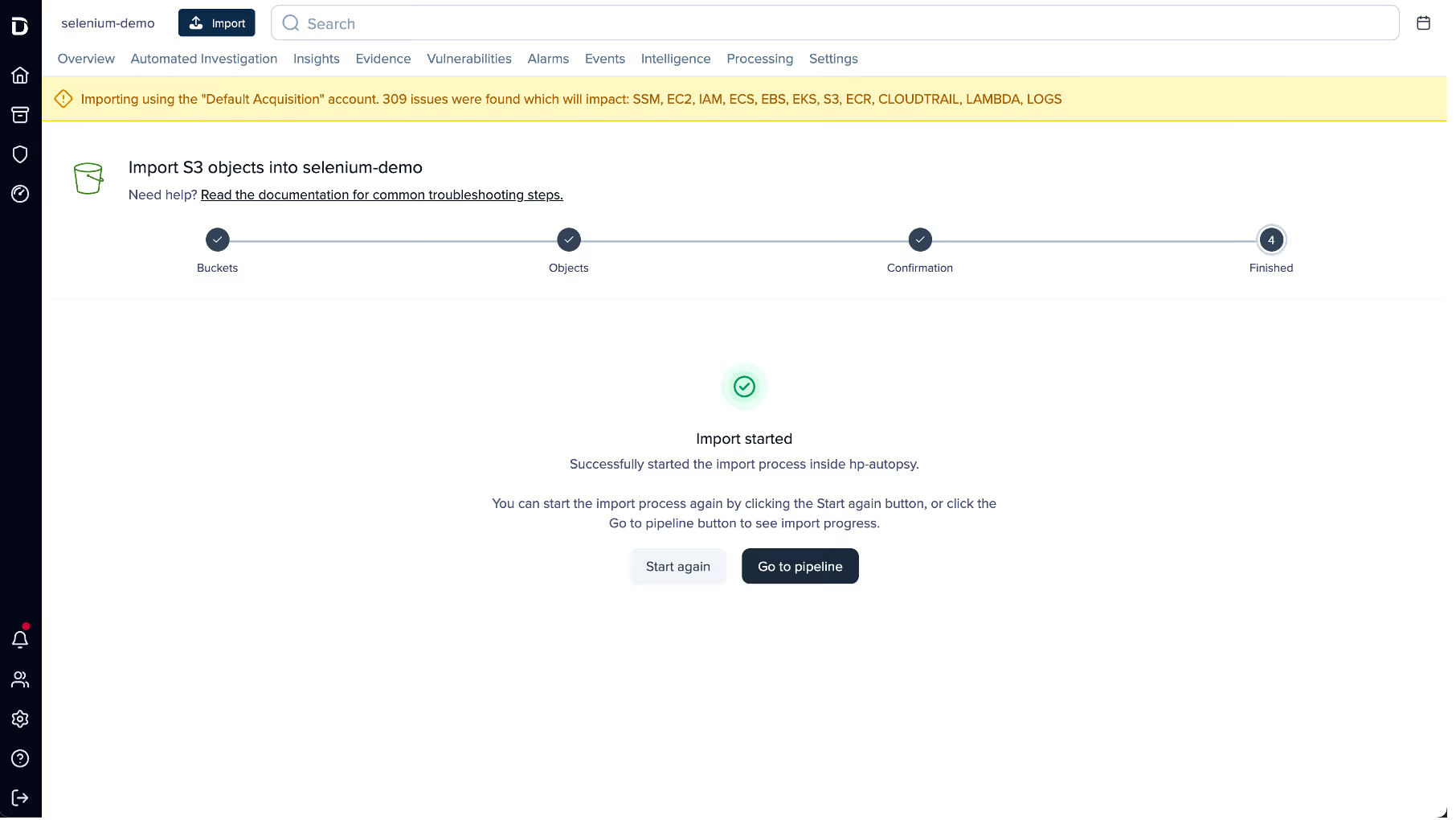
Forensic Acquisition & Investigation supports importing artifacts from a variety of sources, including EC2 instances, ECS, S3 buckets, and more. The Cloudypots system produces a raw disk image whenever an attack is detected and stores it in an S3 bucket. This allows the image to be directly imported into Forensic Acquisition & Investigation using the S3 bucket import option.
As Forensic Acquisition & Investigation runs cloud-natively, no additional configuration is required to add a specific S3 bucket. Analysts can browse and acquire forensic assets from any bucket that the configured IAM role is permitted to access. Operators can also add additional IAM credentials, including those from other cloud providers, to extend access across multiple cloud accounts and environments.

Forensic Acquisition & Investigation then retrieves a copy of the file and automatically begins running the analysis pipeline on the artifact. This pipeline performs a full forensic analysis of the disk and builds a timeline of the activity that took place on the compromised asset. By leveraging Forensic Acquisition & Investigation’s cloud-native analysis system, this process condenses hour of manual work into just minutes.
Once processing is complete, the preserved artifact is visible in the Evidence tab, along with a summary of key information obtained during analysis, such as the compromised asset’s hostname, operating system, cloud provider, and key event count.
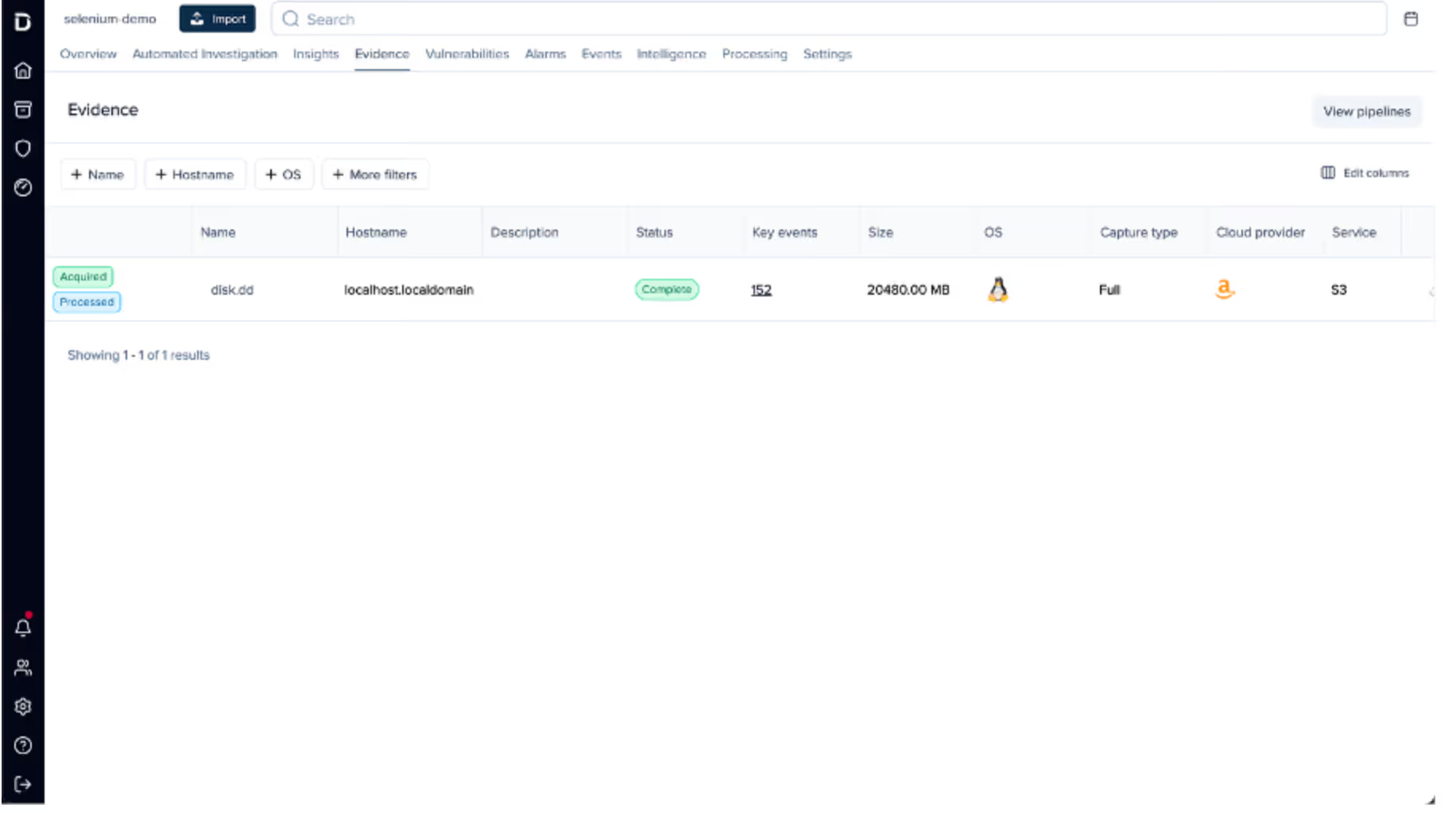
Clicking on the “Key events” field in the listing opens the timeline view, automatically filtered to show system- generated alarms.
The timeline provides a chronological record of every event that occurred on the system, derived from multiple sources, including:
- Parsed log files such as the systemd journal, audit logs, application specific logs, and others.
- Parsed history files such as .bash_history, allowing executed commands to be shown on the timeline.
- File-specific events, such as files being created, accessed, modified, or executables being run, etc.
This approach allows timestamped information and events from multiple sources to be aggregated and parsed into a single, concise view, greatly simplifying the data review process.
Alarms are created for specific timeline events that match either a built-in system rule, curated by Darktrace’s Threat Research team or an operator-defined rule created at the project level. These alarms help quickly filter out noise and highlight on events of interest, such as the creation of a file containing known malware, access to sensitive files like Amazon Web Service (AWS) credentials, suspicious arguments or commands, and more.
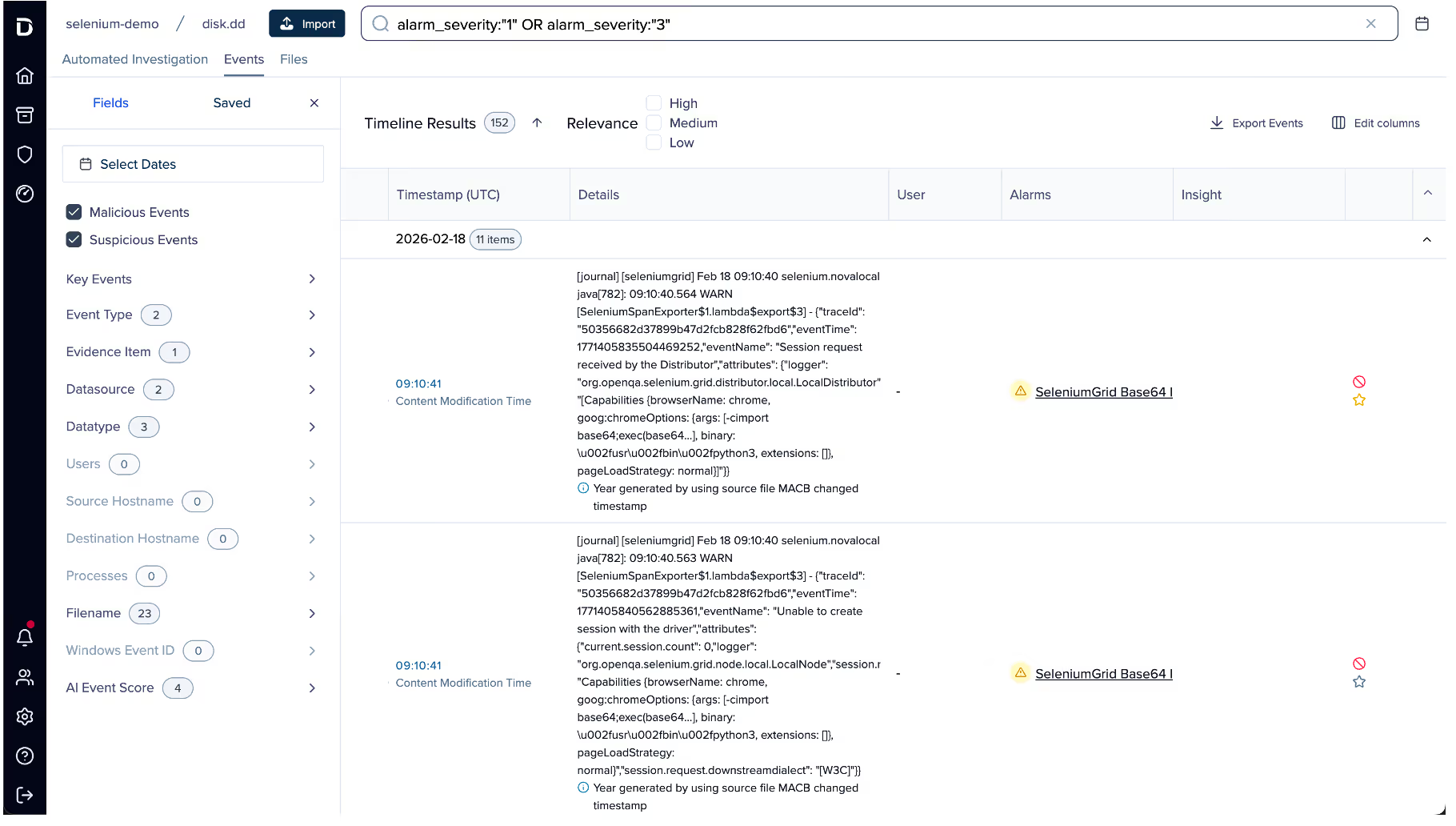
In this case, several alarms were generated for suspicious Base64 arguments being passed to Selenium. Examining the event data, it appears the attacker spawned a Selenium Grid session with the following payload:
"request.payload": "[Capabilities {browserName: chrome, goog:chromeOptions: {args: [-cimport base64;exec(base64...], binary: /usr/bin/python3, extensions: []}, pageLoadStrategy: normal}]"
This is a common attack vector for Selenium Grid. The chromeOptions object is intended to specify arguments for how Google Chrome should be launched; however, in this case the attacker has abused the binary field to execute the Python3 binary instead of Chrome. Combined with the option to specify command-line arguments, the attacker can use Python3’s -c option to execute arbitrary Python code, in this instance, decoding and executing a Base64 payload.
Selenium’s logs truncate the Arguments field automatically, so an alternate method is required to retrieve the full payload. To do this, the search bar can be used to find all events that occurred around the same time as this flagged event.
![Pivoting off the previous event by filtering the timeline to events within the same window using timestamp: [“2026-02-18T09:09:00Z” TO “2026-02-18T09:12:00Z”].](https://cdn.prod.website-files.com/626ff4d25aca2edf4325ff97/69a8a18526ca3e653316a596_Screenshot%202026-03-04%20at%201.17.50%E2%80%AFPM.avif)
Scrolling through the search results, an entry from Java’s systemd journal can be identified. This log contains the full, unaltered payload. GCHQ’s CyberChef can then be used to decode the Base64 data into the attacker’s script, which will ultimately be executed.

In this instance, the malware was identified as a variant of a campaign that has been previously documented in depth by Darktrace.
Investigating Perfctl Malware
This campaign deploys a malware sample known as ‘perfctl to the compromised host. The script executed by the attacker downloads a Go binary named “promocioni.php” from 200[.]4.115.1. Its functionality is consistent with previously documented perfctl samples, with only minor changes such as updated filenames and a new command-and-control (C2) domain.
Perfctl is a stealthy malware that has several systems designed to evade detection. The main binary is packed with UPX, with the header intentionally tampered with to prevent unpacking using regular tools. The binary also avoids executing any malicious code if it detects debugging or tracing activity, or if artifacts left by earlier stages are missing.
To further aid its evasive capabilities, perfctl features a usermode rootkit using an LD preload. This causes dynamically linked executables to load perfctl’s rootkit payload before other system modules, allowing it to override functions, such as intercepting calls to list files and hiding output from the returned list. Perfctl uses this to hide its own files, as well as other files like the ld.so.preload file, preventing users from identifying that a rootkit is present in the first place.
This also makes it difficult to dynamically analyze, as even analysts aware of the rootkit will struggle to get around it due to its aggressiveness in hiding its components. A useful trick is to use the busybox-static utilities, which are statically linked and therefore immune to LD preloading.
Perfctl will attempt to use sudo to escalate its permissions to root if the user it was executed as has the required privileges. Failing this, it will attempt to exploit the vulnerability CVE-2021-4034.
Ultimately, perfctl will attempt to establish a C2 link via Tor and spawn an XMRig miner to mine the Monero cryptocurrency. The traffic to the mining pool is encapsulated within Tor to limit network detection of the mining traffic.
Darktrace’s Cloudypots system has observed 1,959 infections of the perfctl campaign across its honeypot network in the past year, making it one of the most aggressive campaigns seen by Darktrace.
Key takeaways
This blog has shown how Darktrace / Forensic Acquisition & Investigation equips defenders in the face of a real-world attacker campaign. By using this solution, organizations can acquire forensic evidence and investigate intrusions across multiple cloud resources and providers, enabling defenders to see the full picture of an intrusion on day one. Forensic Acquisition & Investigation’s patented data-processing system takes advantage of the cloud’s scale to rapidly process large amounts of data, allowing triage to take minutes, not hours.
Darktrace / Forensic Acquisition & Investigation is available as Software-as-a-Service (SaaS), but can also be hosted within a customer's cloud environment, with the option to deploy in one Cloud Service Provider (CSP) while maintaining cross-cloud visibility, providing flexibility between convenience and data sovereignty to suit any use case.
Support for acquiring traditional compute instances like EC2, as well as more exotic and newly targeted platforms such as ECS and Lambda, ensures that attacks taking advantage of Living-off-the-Cloud (LOTC) strategies can be triaged quickly and easily as part of incident response. As attackers continue to develop new techniques, the ability to investigate how they use cloud services to persist and pivot throughout an environment is just as important to triage as a single compromised EC2 instance.
Credit to Nathaniel Bill (Malware Research Engineer)

































.png)





%201.png)