Why cloud investigation and response needs to evolve
As organizations accelerate their move to the cloud, they’re confronting two interrelated pressures: a rapidly expanding attack surface and rising regulatory scrutiny. The dual pressure is forcing security practitioners to evolve their strategies in the cloud, particularly around investigation and response, where we see analysts spending the most time. This work is especially difficult in the cloud, often requiring experienced analysts to manually stitch together evidence across fragmented systems, unfamiliar platforms, and short-lived assets.
However, adapting isn’t easy. Many teams are operating with limited budgets and face a shortage of cloud-specific security talent. That’s why more organizations are now prioritizing tools that not only deliver deep visibility and rapid response in the cloud, but also help upskill their analysts to keep pace with threats and compliance demands.
Our 2024 survey report highlights just how organizations are recognizing gaps in their cloud security, feeling the heat from regulators, and making significant investments to bolster their cloud investigation capabilities.
In this blog post, we’ll explore the current challenges, approaches, and strategies organizations are employing to enhance their cloud investigation and incident response.
Recognizing the gaps in current cloud investigation and response methods
Complex environments & static tools
Due to the dynamic nature of cloud infrastructure, ephemeral assets, autoscaling environments, and multi-cloud complexity, traditional investigation and response methods which rely on static snapshots and point-in-time data, are fundamentally mismatched. And with Cloud environment APIs needing deep provider knowledge and scripting skills to extract much needed evidence its unrealistic for one person to master all aspects of cloud incident response.
Analysts are still stitching together logs from fragmented systems, manually correlating events, and relying on post-incident forensics that often arrive too late to drive meaningful response. These approaches were built for environments that rarely changed. In the cloud, where assets may only exist for minutes and attacker movement can span regions or accounts in seconds, point-in-time visibility simply can’t keep up. As a result, critical evidence is missed, timelines are incomplete, and investigations drag on longer than they should.
Even some modern approaches still depend heavily on static configurations, delayed snapshots, or siloed visibility that can’t keep pace with real-time attacker movement.
There is even the problem of identifying what cloud data sources hold the valuable information needed to investigate in the first place. With AWS alone having over 200 products, each with its own security practices and data sources.It can be challenging to identify where you need to be looking.
To truly secure the cloud, investigation and response must be continuous, automated, and context-rich. Tools should be able to surface the signal from the noise and support analysts at every step, even without deep forensics expertise.
Increasing compliance pressure
With the rise of data privacy regulations and incident reporting mandates worldwide, organizations face heightened scrutiny. Noncompliance can lead to severe penalties, making it crucial to have robust cloud investigation and response mechanisms in place. 74% of organizations surveyed reported that data privacy regulations complicate incident response, underscoring the urgency to adapt to regulatory requirements.
In addition, a majority of organizations surveyed (89%) acknowledged that they suffer damage before they can fully contain and investigate incidents, particularly in cloud environments, highlighting the need for enhanced cloud capabilities.
Enhancing cloud investigation and response
To address these challenges, organizations are actively growing their capabilities to perform investigations in the cloud. Key steps include:
Allocating and increasing budgets:
Recognizing the importance of cloud-specific investigation tools, many organizations have started to allocate dedicated budgets for cloud forensics. 83% of organizations have budgeted for cloud forensics, with 77% expecting this budget to increase. This reflects a strong commitment to improving cloud security.
Implementing automation that understands cloud behavior
Automation isn’t just about speeding up tasks. While modern threats require speed and efficiency from defenders, automation aims to achieve this by enabling consistent decision making across unique and dynamic environments. Traditional SOAR platforms, often designed for static on-prem environments, struggle to keep pace with the dynamic and ephemeral nature of the cloud, where resources can disappear before a human analyst even has a chance to look at them. Cloud-native automation, designed to act on transient infrastructure and integrate seamlessly with cloud APIs, is rapidly emerging as the more effective approach for real-time investigation and response. Automation can cover collection, processing, and storage of incident evidence without ever needing to wait for human intervention and the evidence is ready and waiting all in once place, regardless of if the evidence is cloud-provider logs, disk images, or memory dumps. With the right automation tools you can even go further and automate the full process from end to end covering acquisition, processing, analysis, and response.
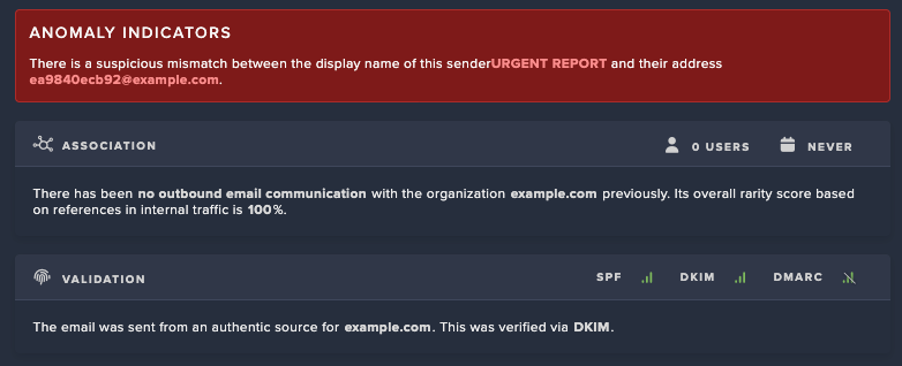
Artificial Intelligence (AI) that augments analysts’ intuition not just adds speed
While many vendors tout AI’s ability to “analyze large volumes of data,” that’s table stakes. The real differentiator is how AI understands the narrative of an incident, surfacing high-fidelity alerts, correlating attacker movement across cloud and hybrid environments, and presenting findings in a way that upskills rather than overwhelms analysts.
In this space, AI isn’t just accelerating investigations, it’s democratizing them by reducing the reliance on highly specialized forensic expertise.
Strategies for effective cloud investigation and response
Organizations are also exploring various strategies to optimize their cloud investigation and response capabilities:
Enhancing visibility and control:
- Unified platforms: Implementing platforms that provide a unified view across multiple cloud environments can help organizations achieve better visibility and control. This consolidation reduces the complexity of managing disparate tools and data sources.
- Improved integration: Ensuring that all security tools and platforms are seamlessly integrated is critical. This integration facilitates better data sharing and cohesive incident management.
- Cloud specific expertise: Training and Recruitment: Investing in training programs to develop cloud-specific skills among existing staff and recruiting experts with cloud security knowledge can bridge the skill gap.
- Continuous learning: Given the constantly evolving nature of cloud threats, continuous learning and adaptation are essential for maintaining effective security measures.
Leveraging automation and AI:
- Automation solutions: Automation solutions for cloud environments can significantly speed up and simplify incident response efficiency. These solutions can handle repetitive tasks, allowing security teams to focus on more complex issues.
- AI powered analysis: AI can assist in rapidly analyzing incident data, identifying anomalies, and predicting potential threats. This proactive approach can help prevent incidents before they escalate.
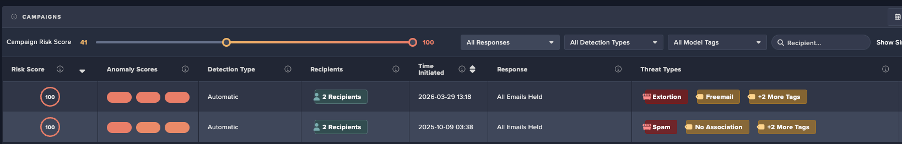
Cloud investigation and response with Darktrace
Darktrace’s forensic acquisition & investigation capabilities helps organizations address the complexities of cloud investigations and incident response with ease. The product seamlessly integrates with AWS, GCP, and Azure, consolidating data from multiple cloud environments into one unified platform. This integration enhances visibility and control, making it easier to manage and respond to incidents across diverse cloud infrastructures.
By leveraging machine learning and automation, Forensic Acquisition & Investigation accelerates the investigation process by quickly analyzing vast amounts of data, identifying patterns, and providing actionable insights. Automation reduces manual effort and response times, allowing your security team to focus on the most pressing issues.
Forensic Acquisition & Investigation can help you stay ahead of threats whilst also meeting regulatory requirements, helping you to maintain a robust cloud security position.







%201.png)












.jpg)