Introduction: Exploiting SAP platforms
Global enterprises depend extensively on SAP platforms, such as SAP NetWeaver and Visual Composer, to run critical business processes worldwide. These systems; however, are increasingly appealing targets for well-resourced adversaries:
- In March 2025, CISA issued an alert confirming active exploitation of a 2017 SAP NetWeaver vulnerability (CVE‑2017‑12637), enabling attackers to perform directory traversal and exfiltrate sensitive files, including credentials, from internet-facing systems
- In April–May 2025, public reporting revealed that a high‑severity zero-day in SAP Visual Composer (CVE‑2025‑31324, CVSS 10.0) has been used in the wild by threat actors deploying web‑shells and achieving full system compromise
- Moreover, CISA has added both NetWeaver and Visual Composer flaws to its Known Exploited Vulnerabilities (KEV) catalog, marking them as verified active threats due to widespread abuse
What is CVE-2025-31324?
CVE-2025-31324 affects SAP’s NetWeaver Visual Composer, a web-based software modeling tool. SAP NetWeaver is an application server and development platform that runs and connects SAP and non-SAP applications across different technologies [2]. It is commonly used by process specialists to develop application components without coding in government agencies, large enterprises, and by critical infrastructure operators [4].
CVE-2025-31324 affects SAP’s Netweaver Visual Composer Framework 7.1x (all SPS) and above [4]. The vulnerability in a Java Servlet (/irj/servlet_jsp) would enable an unauthorized actor to upload arbitrary files to the /developmentserver/metadatauploader endpoint, potentially resulting in remote code execution (RCE) and full system compromise [3]. The issue stems from an improper authentication and authorization check in the SAP NetWeaver Application Server Java systems [4].
What is the severity rating of CVE-2025-31324?
The vulnerability, first disclosed on April 24, 2025, carries the highest severity rating (CVSS v3 score: 10.0) and could allow remote attackers to upload malicious files without requiring authentication [1][5]. Although SAP released a workaround on April 8, many organizations are hesitant to take their business-critical SAP NetWeaver systems offline, leaving them exposed to potential exploitation [2].
How is CVE-2025-31324 exploited?
The vulnerability is exploitable by sending specifically crafted GET, POST, or HEAD HTTP requests to the /developmentserver/metadatauploader URL using either HTTP or HTTPS. Attackers have been seen uploading malicious files (.jsp, .java, or .class files to paths containing “\irj\servlet_jsp\irj\”), most of them being web shells, to publicly accessible SAP NetWeaver systems.
External researchers observed reconnaissance activity targeting this vulnerability in late January 2025, followed by a surge in exploitation attempts in February. The first confirmed compromise was reported in March [4].
Multiple threat actors have reportedly targeted the vulnerability, including Chinese Advanced Persistent Threats (APTs) groups Chaya_004 [7], UNC5221, UNC5174, and CL-STA-0048 [8], as well as ransomware groups like RansomEXX, also known as Storm-2460, BianLian [4] or Qilin [6] (the latter two share the same indicators of compromise (IoCs)).
Following the initial workaround published on April 8, SAP released a security update addressing CVE-2025-31324 and subsequently issued a patch on May 13 (Security Note 3604119) to resolve the root cause of the vulnerability [4].
Darktrace’s coverage of CVE-2025-31324 exploitation
Darktrace has observed activity indicative of threat actors exploiting CVE-2025-31324, including one instance detected before the vulnerability was publicly disclosed.
In April 2025, the Darktrace Threat Research team investigated activity related to the CVE-2025-31324 on SAP devices and identified two cases suggesting active exploitation of the vulnerability. One case was detected prior to the public disclosure of the vulnerability, and the other just two days after it was published.
Early detection of CVE 2025-31324 by Darktrace
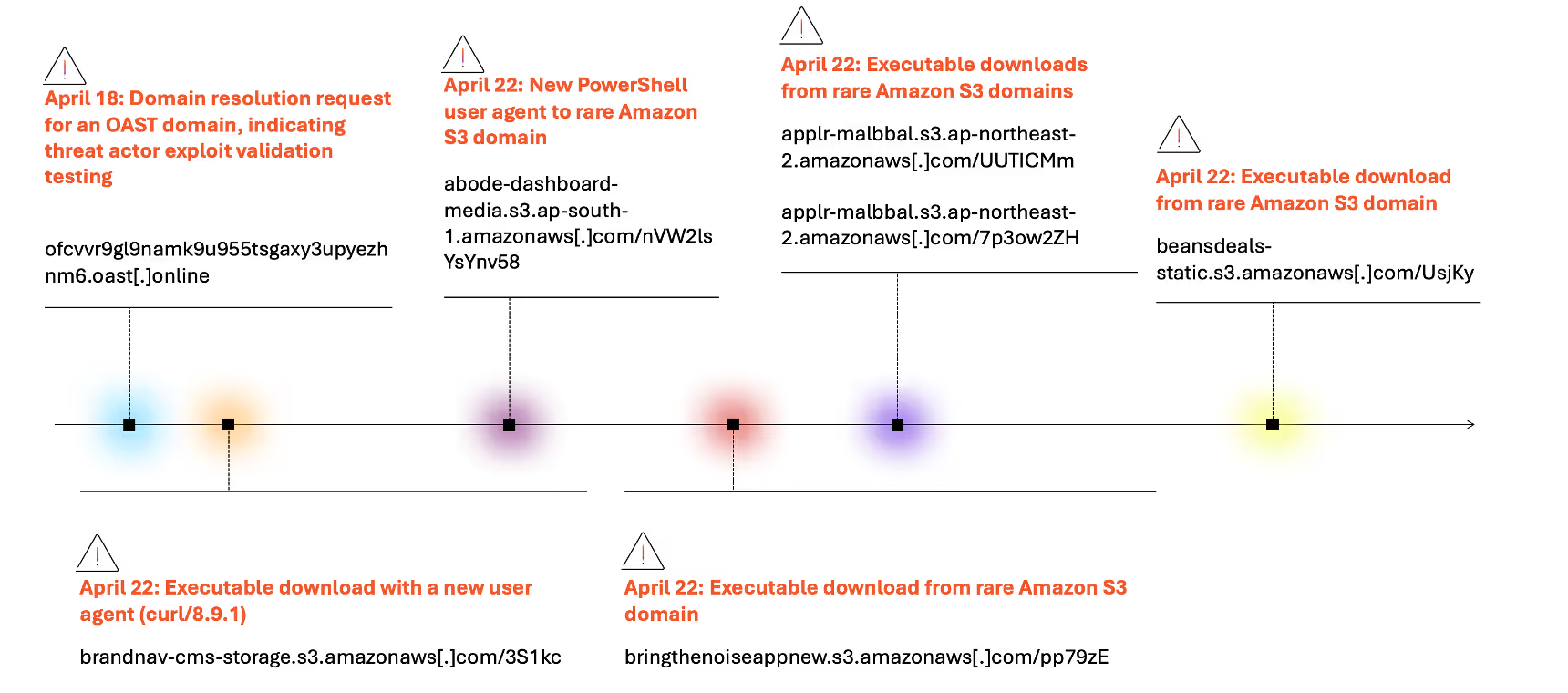
On April 18, six days prior to the public disclosure of CVE-2025-31324, Darktrace began to detect unusual activity on a device belonging to a logistics organization in the Europe, the Middle East and Africa (EMEA) region. Multiple IoCs observed during this incident have since been linked via OSINT to the exploitation of CVE-2025-31324. Notably, however, this reporting was not available at the time of detection, highlighting Darktrace’s ability to detect threats agnostically, without relying on threat intelligence.
The device was observed making domain name resolution request for the Out-of-Band Application Security Testing (OAST) domain cvvr9gl9namk9u955tsgaxy3upyezhnm6.oast[.]online. OAST is often used by security teams to test if exploitable vulnerabilities exist in a web application but can similarly be used by threat actors for the same purpose [9].
Four days later, on April 22, Darktrace observed the same device, an internet-facing system believed to be a SAP device, downloading multiple executable (.exe) files from several Amazon Simple Storage Service (S3). Darktrace’s Threat Research team later found these files to be associated with the KrustyLoader malware [23][24][25].
KrustyLoader is known to be associated with the Chinese threat actor UNC5221, also known as UTA0178, which has been reported to aggressively target devices exposed to the internet [10] [14] [15]. It is an initial-stage malware which downloads and launches a second-stage payload – Sliver C2. Sliver is a similar tool to Cobalt Strike (an open-source post-exploitation toolkit). It is used for command-and-control (C2) connections [11][12]13]. After its successful download, KrustyLoader deletes itself to evade detection. It has been reported that multiple Chinese APT groups have deployed KrustyLoader on SAP Netweaver systems post-compromise [8].
The actors behind KrustyLoader have also been associated with the exploitation of zero-day vulnerabilities in other enterprise systems, including Ivanti devices [12]. Notably, in this case, one of the Amazon S3 domains observed (abode-dashboard-media.s3.ap-south-1.amazonaws[.]com ) had previously been investigated by Darktrace’s Threat Research team as part of their investigation into Ivanti Connect Secure (CS) and Policy Secure (PS) appliances.
In addition to the download of known malicious files, Darktrace also detected new IoCs, including several executable files that could not be attributed to any known malware families or previous attacks, and for which no corresponding OSINT reporting was available.
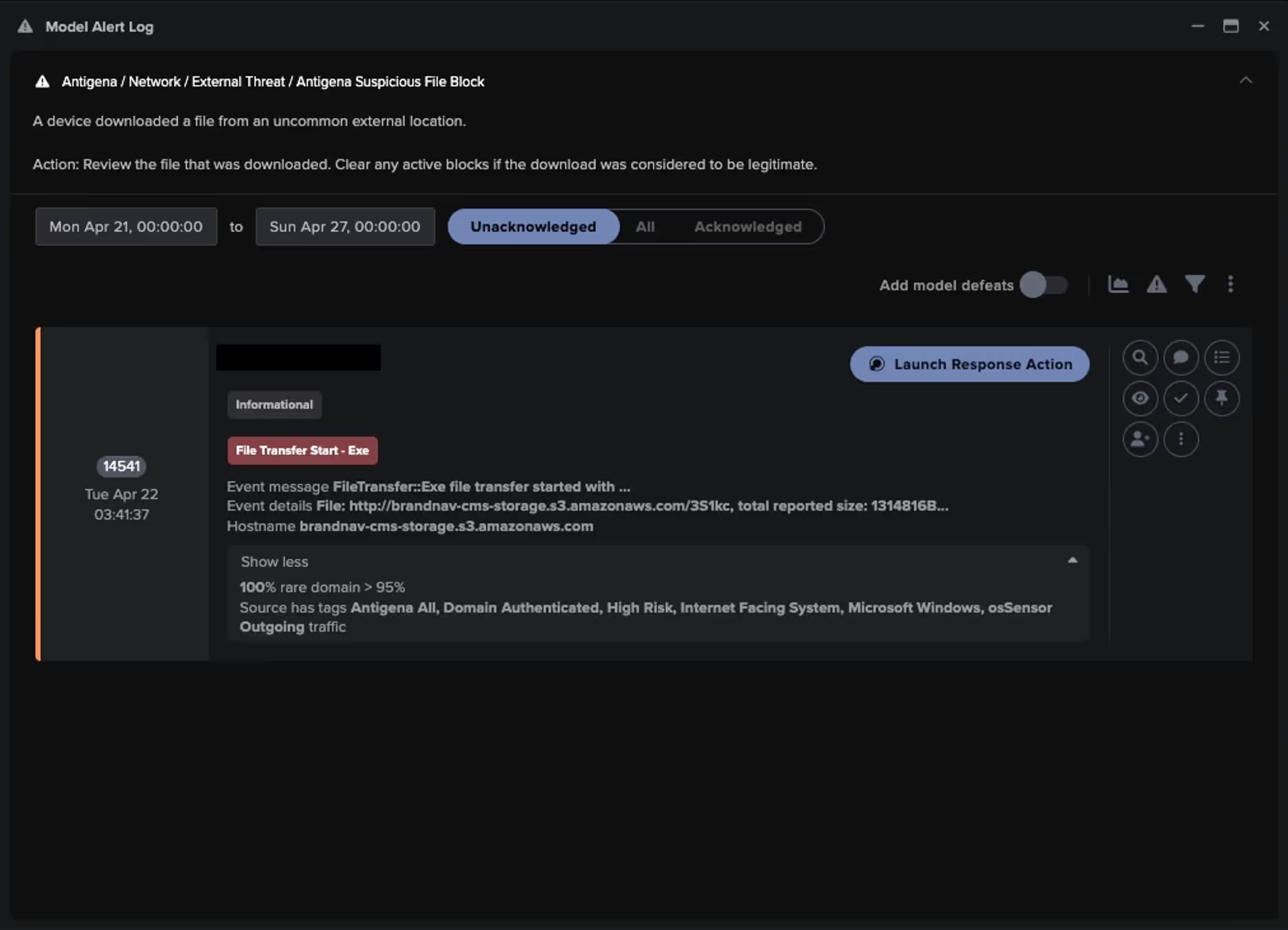
*The model alert was recreated in a demo environment using real incident metadata, as the original customer environment was no longer accessible.
Post-CVE publication detection
Exploit Validation
Between April 27 and 29, Darktrace observed unusual activity from an SAP device on the network of a manufacturing customer in EMEA.
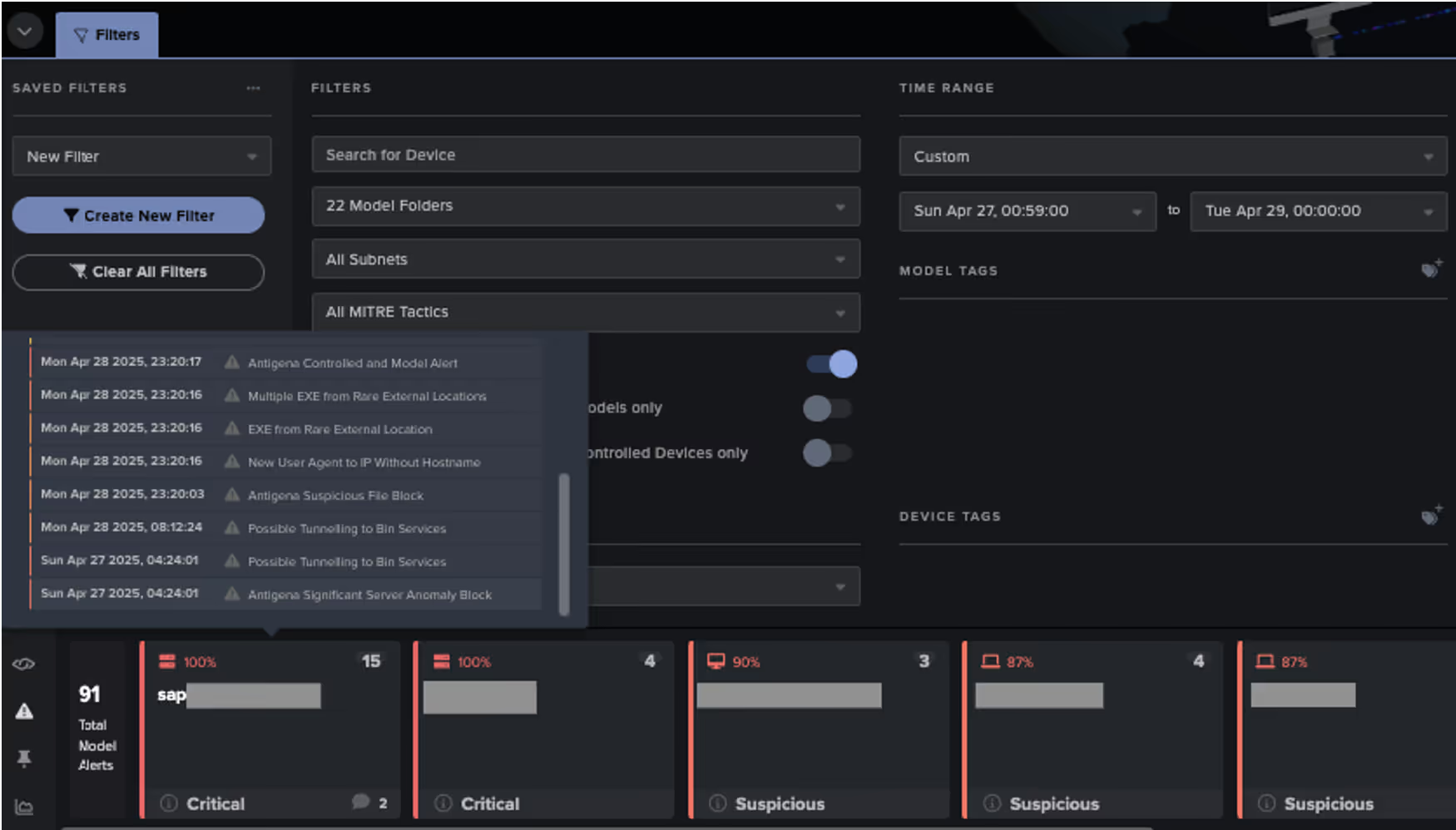
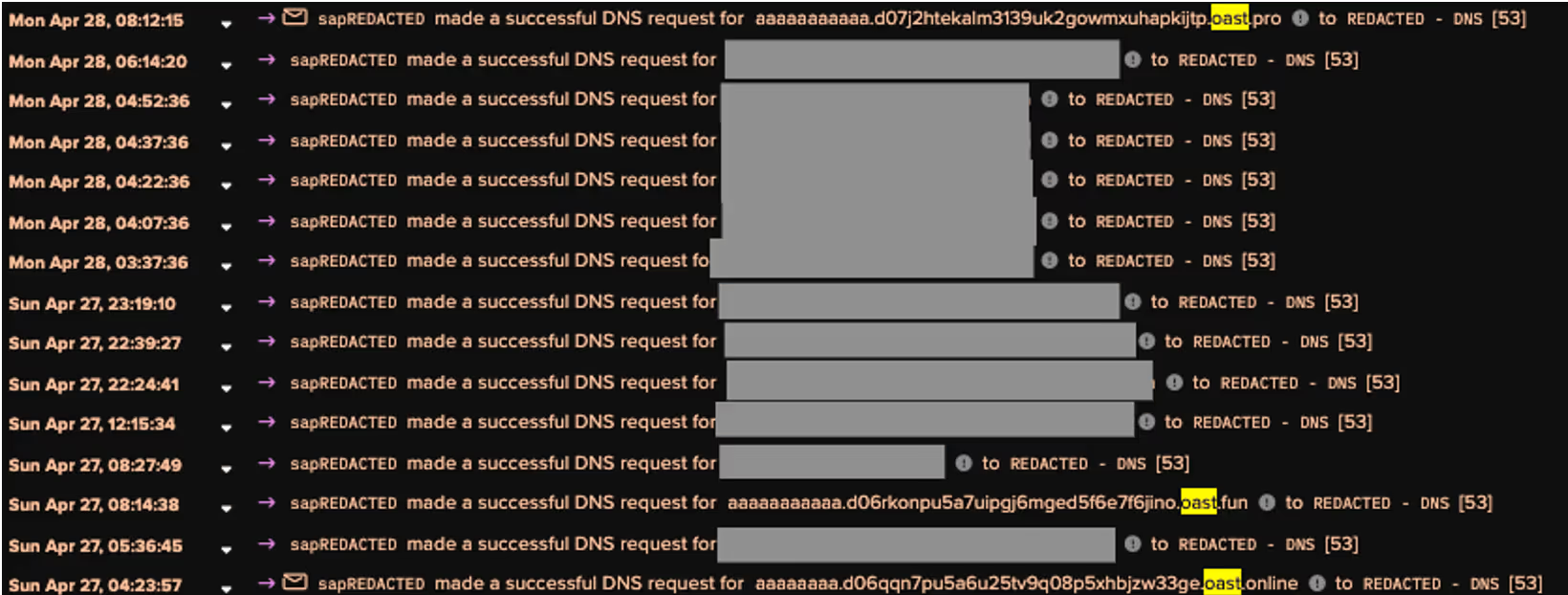
The device was observed making DNS requests for OAST domains (e.g. aaaaaaaa.d06qqn7pu5a6u25tv9q08p5xhbjzw33ge.oast[.]online and aaaaaaaaaaa.d07j2htekalm3139uk2gowmxuhapkijtp.oast[.]pro), suggesting that a threat actor was testing for exploit validation [9].
Privilege escalation tool download attempt
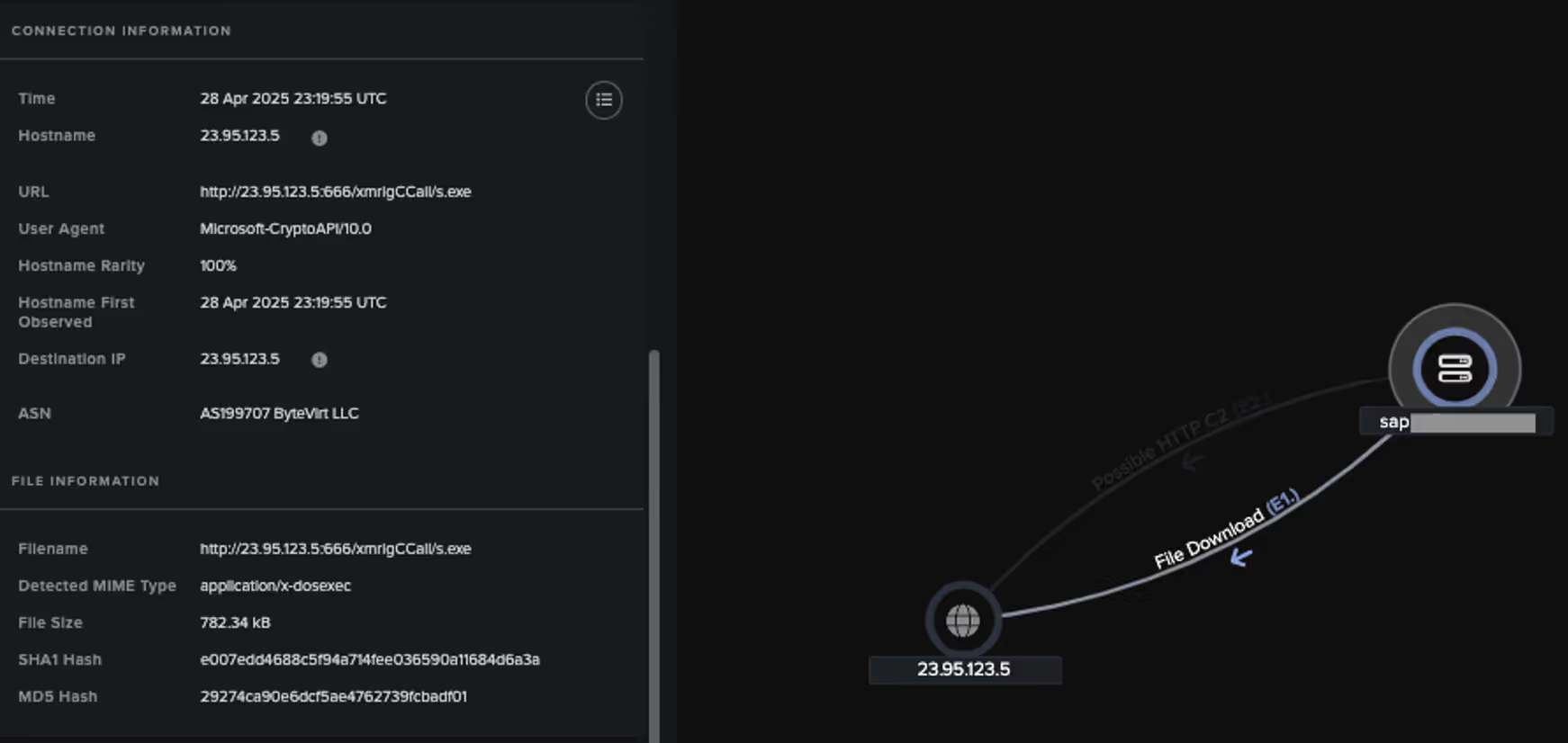
One day later, Darktrace observed the same device attempting to download an executable file from hxxp://23.95.123[.]5:666/xmrigCCall/s.exe (SHA-1 file hash: e007edd4688c5f94a714fee036590a11684d6a3a).
Darktrace / NETWORK identified the user agents Microsoft-CryptoAPI/10.0 and CertUtil URL Agent during the connections to 23.95.123[.]5. The connections were made over port 666, which is not typically used for HTTP connections.
Multiple open-source intelligence (OSINT) vendors have identified the executable file as either JuicyPotato or SweetPotato, both Windows privilege escalation tools[16][17][18][19]. The file hash and the unusual external endpoint have been associated with the Chinese APT group Gelsemium in the past, however, many threat actors are known to leverage this tool in their attacks [20] [21].
Darktrace deemed this activity highly suspicious and triggered an Enhanced Monitoring model alert, a high-priority security model designed to detect activity likely indicative of compromise. As the customer was subscribed to the Managed Threat Detection service, Darktrace’s Security Operations Centre (SOC) promptly investigated the alert and notified the customer for swift remediation. Additionally, Darktrace’s Autonomous Response capability automatically blocked connections to the suspicious IP, 23.95.123[.]5, effectively containing the compromise in its early stages.
![Actions taken by Darktrace’s Autonomous Response to block connections to the suspicious external endpoint 23.95.123[.]5. This event log shows that the connections to 23.95.123[.]5 were made over a rare destination port for the HTTP protocol and that new user agents were used during the connections.](https://cdn.prod.website-files.com/626ff4d25aca2edf4325ff97/685195a1592b0029efa4fd53_Screenshot%202025-06-17%20at%209.19.36%E2%80%AFAM.avif)
Conclusion
The exploitation of CVE-2025-31324 to compromise SAP NetWeaver systems highlights the persistent threat posed by vulnerabilities in public-facing assets. In this case, threat actors leveraged the flaw to gain an initial foothold, followed by attempts to deploy malware linked to groups affiliated with China [8][20].
Crucially, Darktrace demonstrated its ability to detect and respond to emerging threats even before they are publicly disclosed. Six days prior to the public disclosure of CVE-2025-31324, Darktrace detected unusual activity on a device believed to be a SAP system, which ultimately represented an early detection of the CVE. This detection was made possible through Darktrace’s behavioral analysis and anomaly detection, allowing it to recognize unexpected deviations in device behavior without relying on signatures, rules or known IoCs. Combined with its Autonomous Response capability, this allowed for immediate containment of suspicious activity, giving security teams valuable time to investigate and mitigate the threat.
Credit to Signe Zaharka (Principal Cyber Analyst), Emily Megan Lim, (Senior Cyber Analyst) and Ryan Traill (Analyst Content Lead)
Appendices
List of IoCs
23.95.123[.]5:666/xmrigCCall/s.exe - URL- JuicyPotato/SweetPotato - high confidence
29274ca90e6dcf5ae4762739fcbadf01- MD5 file hash - JuicyPotato/SweetPotato - high confidence
e007edd4688c5f94a714fee036590a11684d6a3a - SHA-1 file hash - JuicyPotato/SweetPotato -high confidence
3268f269371a81dbdce8c4eedffd8817c1ec2eadec9ba4ab043cb779c2f8a5d2 - SHA-256 file hash - JuicyPotato/SweetPotato -high confidence
abode-dashboard-media.s3.ap-south-1.amazonaws[.]com/nVW2lsYsYnv58 - URL- high confidence
applr-malbbal.s3.ap-northeast-2.amazonaws[.]com/7p3ow2ZH - URL- high confidence
applr-malbbal.s3.ap-northeast-2.amazonaws[.]com/UUTICMm - URL- KrustyLoader - high confidence
beansdeals-static.s3.amazonaws[.]com/UsjKy - URL- high confidence
brandnav-cms-storage.s3.amazonaws[.]com/3S1kc - URL- KrustyLoader - high confidence
bringthenoiseappnew.s3.amazonaws[.]com/pp79zE - URL- KrustyLoader - high confidence
f662135bdd8bf792a941ea222e8a1330 - MD5 file hash- KrustyLoader - high confidence
fa645f33c0e3a98436a0161b19342f78683dbd9d - SHA-1 file hash- KrustyLoader - high confidence
1d26fff4232bc64f9ab3c2b09281d932dd6afb84a24f32d772d3f7bc23d99c60 - SHA-256 file hash- KrustyLoader - high confidence
6900e844f887321f22dd606a6f2925ef - MD5 file hash- KrustyLoader - high confidence
da23dab4851df3ef7f6e5952a2fc9a6a57ab6983 - SHA-1 file hash- KrustyLoader - high confidence
1544d9392eedf7ae4205dd45ad54ec67e5ce831d2c61875806ce4c86412a4344 - SHA-256 file hash- KrustyLoader - high confidence
83a797e5b47ce6e89440c47f6e33fa08 - MD5 file hash - high confidence
a29e8f030db8990c432020441c91e4b74d4a4e16 - SHA-1 file hash - high confidence
72afde58a1bed7697c0aa7fa8b4e3b03 - MD5 file hash- high confidence
fe931adc0531fd1cb600af0c01f307da3314c5c9 - SHA-1 file hash- high confidence
b8e56de3792dbd0f4239b54cfaad7ece3bd42affa4fbbdd7668492de548b5df8 - SHA-256 file hash- KrustyLoader - high confidence
17d65a9d8d40375b5b939b60f21eb06eb17054fc - SHA-1 file hash- KrustyLoader - high confidence
8c8681e805e0ae7a7d1a609efc000c84 - MD5 file hash- KrustyLoader - high confidence
29274ca90e6dcf5ae4762739fcbadf01 - MD5 file hash- KrustyLoader - high confidence
Darktrace Model Detections
Anomalous Connection / CertUtil Requesting Non Certificate
Anomalous Connection / CertUtil to Rare Destination
Anomalous Connection / Powershell to Rare External
Anomalous File / EXE from Rare External Location
Anomalous File / Multiple EXE from Rare External Locations
Anomalous File / Internet Facing System File Download
Anomalous File / Masqueraded File Transfer (Enhanced Monitoring)
Anomalous Server Activity / New User Agent from Internet Facing System
Compliance / CertUtil External Connection
Compromise / High Priority Tunnelling to Bin Services (Enhanced Monitoring)
Compromise / Possible Tunnelling to Bin Services
Device / Initial Attack Chain Activity (Enhanced Monitoring)
Device / Suspicious Domain
Device / Internet Facing Device with High Priority Alert
Device / Large Number of Model Alerts
Device / Large Number of Model Alerts from Critical Network Device (Enhanced Monitoring)
Device / New PowerShell User Agent
Device / New User Agent
Autonomous Response Model Alerts
Antigena / Network / External Threat / Antigena Suspicious File Block
Antigena / Network / Significant Anomaly / Antigena Controlled and Model Alert
Antigena / Network / Significant Anomaly / Antigena Enhanced Monitoring from Server Block
Antigena / Network / Significant Anomaly / Antigena Significant Server Anomaly Block
Antigena/ Network / External Threat / Antigena Suspicious File Block
Antigena/ Network / External Threat / Antigena Suspicious File Pattern of Life Block
Antigena/ Network / Significant Anomaly / Antigena Alerts Over Time Block
Antigena/ Network / Significant Anomaly / Antigena Controlled and Model Alert
Antigena/ Network / Significant Anomaly / Antigena Enhanced Monitoring from Server Block
Antigena/ Network / Significant Anomaly / Antigena Significant Server Anomaly Block
Cyber AI Analyst Incidents
Possible HTTP Command and Control
Suspicious File Download
MITRE ATT&CK Mapping
Malware - RESOURCE DEVELOPMENT - T1588.001
PowerShell - EXECUTION - T1059.001
Drive-by Compromise - INITIAL ACCESS - T1189
Ingress Tool Transfer - COMMAND AND CONTROL - T1105
Application Layer Protocol - COMMAND AND CONTROL - T1071
Exploitation of Remote Services - LATERAL MOVEMENT - T1210
Exfiltration Over Unencrypted/Obfuscated Non-C2 Protocol - EXFILTRATION - T1048.003
References
1. https://nvd.nist.gov/vuln/detail/CVE-2025-31324
4. https://onapsis.com/blog/active-exploitation-of-sap-vulnerability-cve-2025-31324/
6. https://op-c.net/blog/sap-cve-2025-31324-qilin-breach/
9. https://portswigger.net/burp/application-security-testing/oast
10. https://www.picussecurity.com/resource/blog/unc5221-cve-2025-22457-ivanti-connect-secure
11. https://malpedia.caad.fkie.fraunhofer.de/details/elf.krustyloader
12. https://www.broadcom.com/support/security-center/protection-bulletin/krustyloader-backdoor
13. https://labs.withsecure.com/publications/new-krustyloader-variant-dropped-via-screenconnect-exploit
15. https://thehackernews.com/2024/01/chinese-hackers-exploiting-critical-vpn.html
16. https://www.virustotal.com/gui/file/3268f269371a81dbdce8c4eedffd8817c1ec2eadec9ba4ab043cb779c2f8a5d2
17. https://bazaar.abuse.ch/sample/3268f269371a81dbdce8c4eedffd8817c1ec2eadec9ba4ab043cb779c2f8a5d2/
19. https://www.manageengine.com/log-management/correlation-rules/detecting-sweetpotato.html
20. https://unit42.paloaltonetworks.com/rare-possible-gelsemium-attack-targets-se-asia/
21. https://assets.kpmg.com/content/dam/kpmg/in/pdf/2023/10/kpmg-ctip-gelsemium-apt-31-oct-2023.pdf
23. https://www.virustotal.com/gui/file/b8e56de3792dbd0f4239b54cfaad7ece3bd42affa4fbbdd7668492de548b5df8

















%201.png)